一、系统环境
生成工具: OpenSSL 3.0.7 1 Nov 2022 (Library: OpenSSL 3.0.7 1 Nov 2022)
生成系统: Rocky Linux 9.2
web 服务:nginx/1.20.1
文件目录:/opt/certs/ 自己创建目录
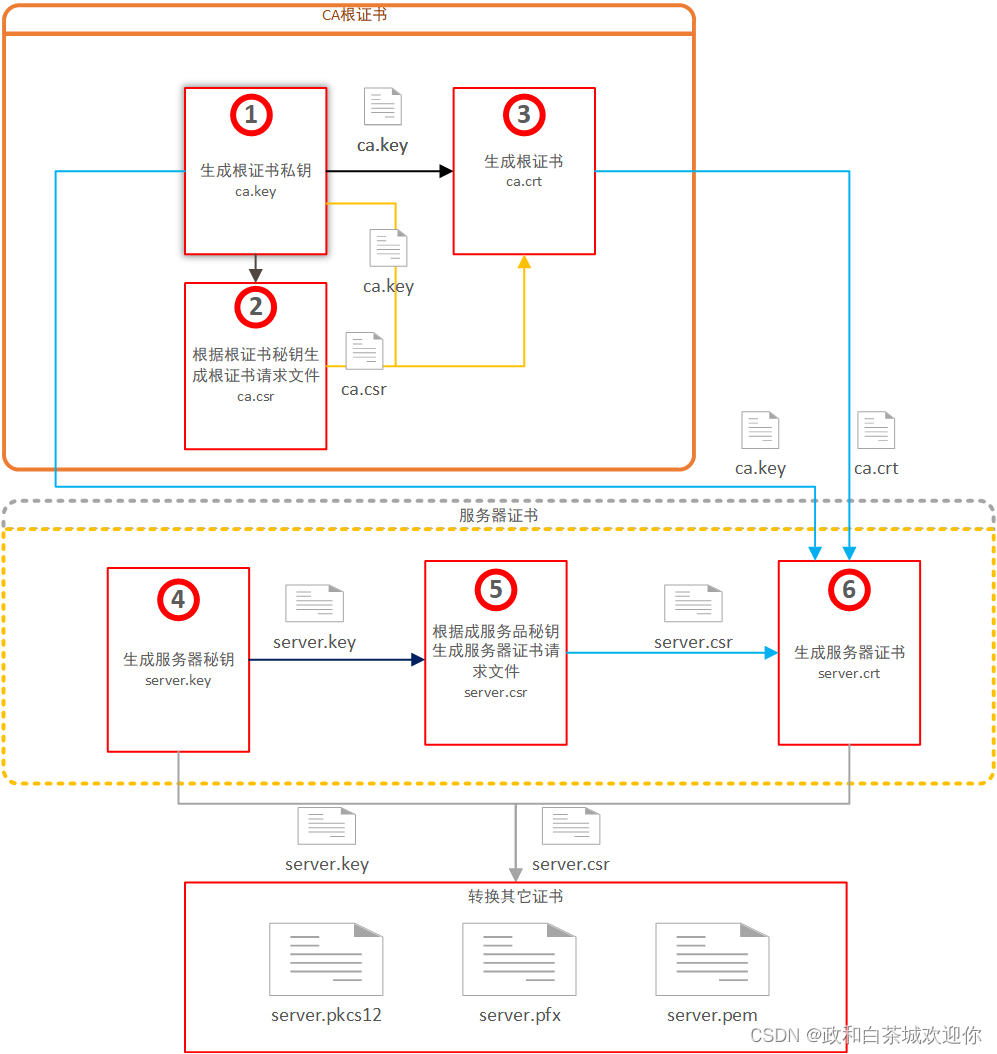
二、证书生成业务图
三 、生成根证书
生成根证书通过常分为几个步骤生成,生成私钥(.key)–>生成证书请求(.csr)–>用CA根证书签名得到证书(.crt)
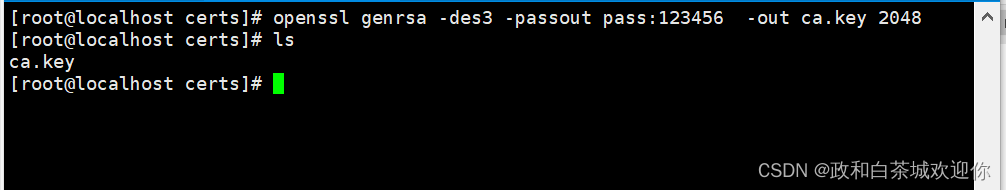
2.1生成根证书私钥
openssl genrsa -des3 -passout pass:123456 -out ca.key 2048genrsa::使用RSA算法产生私钥
-des3::使用des3的AES算法对私钥进行加密
-passout:私钥密码,注意参数格式pass:123456,没有这个参数,在生成私钥时会提示控制台输入
-out:输出文件的路径
2048:指定私钥长度
2.2生成根的请求证书
openssl req -passin pass:123456 -new -key ca.key -out ca.csr -subj "/C=CN/ST=Beijing/L=Beijing/O=Beijing CSSCA Technologies Co., Ltd./OU=R&D/CN=CSSCA Root Certificate Authority"req:执行证书签发命令
-passin:私钥的密码,参数格式pass:123456没有这个参数,控制台提示输入
-new:新证书签发请求
-key:指定私钥路径
-out:输出的csr文件的路径
-subj:证书相关的用户信息(subject的缩写)
subj子参数详解:
缩写 翻译 英文对照
C 国家名称缩写 Country Name (2 letter code)
ST 州或省名称 State or Province Name (full name)
L 城市或区域称 Locality Name (eg, city)
O 组织名(或公司名) Organization Name (eg, company)
OU 组织单位名称(或部门名) Organizational Unit Name (eg, section)
CN 服务器域名/证书拥有者名称 Common Name (e.g. server FQDN or YOUR name)
emailAddress 邮件地址 Email

2.3 自签名根证书
2.3.1创建配置文件
ca.ext是扩展的配置信息,这个很重要
[root@localhost certs]# touch ca.ext
[root@localhost certs]# echo -e "[ v3_ca ] \nsubjectKeyIdentifier=hash\nauthorityKeyIdentifier=keyid:always,issuer\nbasicConstraints = critical,CA:true" > ca.ext
[root@localhost certs]# cat ca.ext
[ v3_ca ]
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid:always,issuer
basicConstraints = critical,CA:true
[root@localhost certs]# 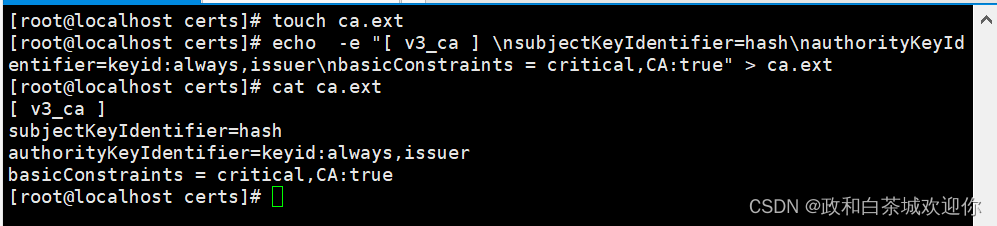 2.3.2 创建证书
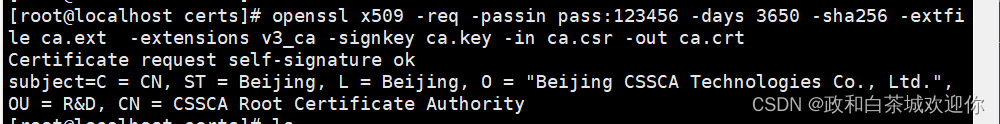
2.3.2 创建证书
ca要给自己签发证书
openssl x509 -req -passin pass:123456 -days 3650 -sha256 -extfile ca.ext -extensions v3_ca -signkey ca.key -in ca.csr -out ca.crtx509:生成x509格式证书
-req:输入csr文件
-passin:私钥的密码,参数格式pass:123456没有这个参数,控制台提示输入
-days:证书的有效期(天)
-sha256:证书摘要采用sha256算法
-extfile: 扩展的文件配置
-extensions:扩展文件中配置的v3_ca项添加扩展
-signkey:签发证书的私钥
-in:要输入的csr文件
-out:输出的cer证书文件
(1)创建非根证书指定 -extensions v3_req,表示,在openssl.cnf中v3_req扩展属性为:
basicConstraints = CA:FALSE。
(2)创建根证书时,指定了-extensions v3_ca,basicConstraints = critical,CA:true
2.4 查看根证书
证书是否有下面这个配置项
X509v3 extensions:
X509v3 Subject Key Identifier:
27:F7:F9:AA:6D:F2:F2:25:3B:CA:1D:B3:82:98:99:BF:7D:C7:7C:46
X509v3 Authority Key Identifier:
27:F7:F9:AA:6D:F2:F2:25:3B:CA:1D:B3:82:98:99:BF:7D:C7:7C:46
X509v3 Basic Constraints: critical
CA:TRUE
[root@localhost certs]# openssl x509 -text -in ca.crt -noout
Certificate:
Data:
Version: 3 (0x2)
Serial Number:
73:c3:98:5d:fc:64:12:77:c6:16:95:e9:78:1b:8a:17:e1:f8:20:87
Signature Algorithm: sha256WithRSAEncryption
Issuer: C = CN, ST = Beijing, L = Beijing, O = "Beijing CSSCA Technologies Co., Ltd.", OU = R&D, CN = CSSCA Root Certificate Authority
Validity
Not Before: Nov 5 02:44:18 2023 GMT
Not After : Nov 2 02:44:18 2033 GMT
Subject: C = CN, ST = Beijing, L = Beijing, O = "Beijing CSSCA Technologies Co., Ltd.", OU = R&D, CN = CSSCA Root Certificate Authority
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (2048 bit)
Modulus:
00:f3:ad:94:d1:0c:a6:5b:26:62:93:b2:a3:01:e7:
32:d3:72:78:52:15:62:d2:be:26:f8:d3:83:5d:b0:
33:6d:56:57:c0:06:d1:f5:35:bc:a6:d9:c9:75:20:
03:88:47:87:64:13:64:a0:3c:bc:d2:6e:43:12:0f:
5b:ff:06:fe:39:c7:af:bd:47:66:87:97:9f:77:19:
64:ca:2e:16:f1:aa:4d:87:a2:aa:17:f7:af:bb:76:
c1:e1:2d:59:3f:c7:0d:a5:85:c6:7b:86:04:5e:da:
68:8b:36:8a:b3:78:b5:cf:25:98:c2:d9:56:aa:3a:
f0:be:a0:32:bf:6b:17:47:f4:46:6c:ac:e1:ce:b1:
bf:8c:3e:73:97:95:91:76:ed:13:c0:f8:43:45:4c:
b1:39:ae:73:e6:69:c6:96:98:9c:b6:71:de:b2:23:
8a:de:7e:80:27:fc:ea:62:45:96:b1:88:1c:e2:b0:
5e:85:42:41:e8:4c:65:f9:07:58:9c:cc:60:cc:69:
7e:18:87:ce:dd:d5:39:bb:6a:5b:46:f8:65:4d:ec:
b6:b4:68:03:0d:61:2b:74:a8:d2:dd:19:94:21:f1:
ec:89:24:21:a6:44:58:ff:e2:fb:a9:90:51:a3:d1:
03:0a:e4:97:06:2b:01:1e:a8:38:9d:c4:08:d4:d7:
a5:0f
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Subject Key Identifier:
27:F7:F9:AA:6D:F2:F2:25:3B:CA:1D:B3:82:98:99:BF:7D:C7:7C:46
X509v3 Authority Key Identifier:
27:F7:F9:AA:6D:F2:F2:25:3B:CA:1D:B3:82:98:99:BF:7D:C7:7C:46
X509v3 Basic Constraints: critical
CA:TRUE
Signature Algorithm: sha256WithRSAEncryption
Signature Value:
9f:0c:00:d2:1d:0a:c3:5a:5c:16:f7:3f:67:14:db:5f:28:df:
21:2f:98:eb:a3:52:41:d3:35:17:4f:3a:cd:ec:40:5b:04:7b:
93:c0:65:1b:0f:a0:d5:fa:b5:05:e7:f8:4b:17:c5:b2:b0:3b:
48:03:34:ae:2e:5c:7a:96:d3:ff:50:ea:2f:82:aa:3a:79:3b:
bf:ec:57:61:3c:a9:b4:2d:42:85:dd:2f:b6:9a:92:0c:72:ac:
05:6a:32:30:cb:d6:f0:a1:77:79:4d:7c:0b:06:5c:4d:ae:6a:
08:88:34:76:be:d5:2f:61:83:e3:6a:4f:d4:7d:f7:84:11:ad:
de:e1:00:75:31:42:66:04:47:73:a6:30:d7:0a:90:b4:e5:37:
a8:3b:8e:c4:a2:8f:39:ce:32:94:33:aa:08:89:24:19:0a:f0:
57:ca:5d:31:8f:74:7a:c1:91:49:60:4f:36:f7:b6:02:5c:7a:
f6:c2:36:93:d4:a1:56:38:b3:70:b7:09:d6:02:c9:89:b5:0d:
ae:67:93:a6:4f:1b:5e:01:87:d0:7d:54:86:91:d1:1b:db:80:
76:5d:05:24:7a:eb:9d:74:70:a6:87:d0:40:3a:46:5a:50:72:
0d:63:80:aa:8d:8e:34:72:40:87:a6:8c:5b:2e:58:08:51:e5:
00:23:a3:9d四、服务器证书生成
生成根证书通过常分为几个步骤生成,生成私钥(.key)–>生成证书请求(.csr)–>用CA私钥+CA根证书签名得到证书(.crt)
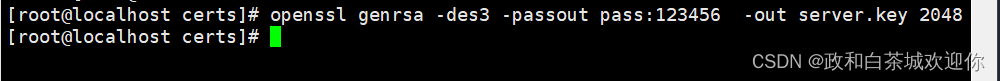
3.1 生成服务器私钥
openssl genrsa -des3 -passout pass:123456 -out server.key 2048
3.2 生成证书请求文件
openssl req -passin pass:123456 -new -key server.key -out server.csr -subj "/C=CN/L=Shanghai/O=Shanghai/OU=R&D/CN=fhh"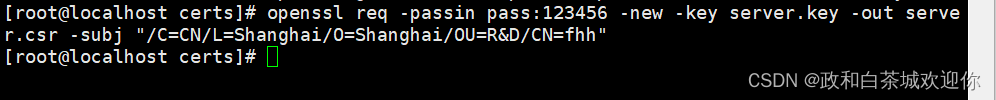
3.3 生成服务证签名证书
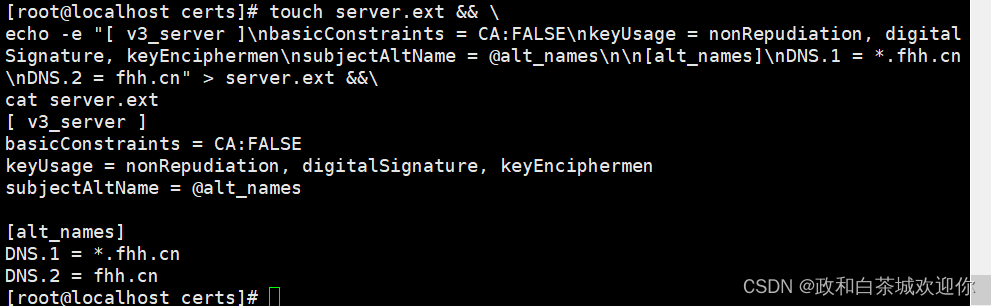
3.3.1 创建配置文件
创建扩展文件server.ext,添加配置项目,这个很重要,特别是域名配置
touch server.ext && \
echo -e "[ v3_server ]\nbasicConstraints = CA:FALSE\nkeyUsage = nonRepudiation, digitalSignature, keyEncipherment\nsubjectAltName = @alt_names\n\n[alt_names]\nDNS.1 = *.fhh.cn\nDNS.2 = fhh.cn" > server.ext &&\
cat server.ext
3.3.2 创建序列号文件并设置序号
需要创建一个文件serial,用来保存生成证书序号,从00开始,在签名时要配置项目-CAserial serial
touch serial && echo 00 > serial
3.3.3 服务器证书签名
服务器签名
openssl x509 -req -passin pass:123456 -extfile server.ext -extensions v3_server -days 3650 -sha256 -CA ca.crt -CAkey ca.key -CAserial serial -in server.csr -out server.crt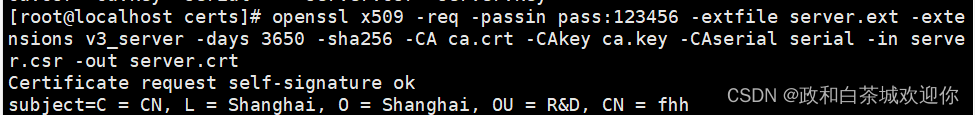
3.3.4 用根证书验证签名的服务器证书
openssl verify -CAfile ca.crt server.crt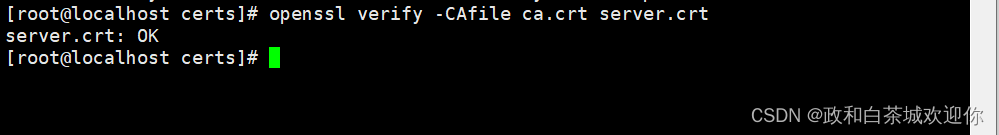
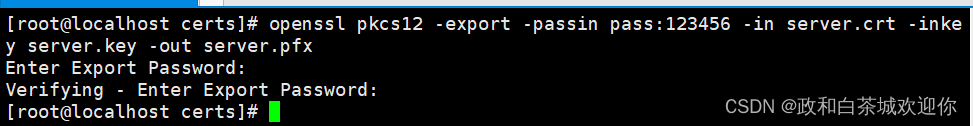
3.3.5 服务证书转pfx
Tomca配置是pfx格式,所以生成的证书要转换下,生成时需要输入pfx密码
openssl pkcs12 -export -passin pass:123456 -in server.crt -inkey server.key -out server.pfx
3.3.6 服务器私钥脱密
因为Nginx配置server.key 不能是带密码
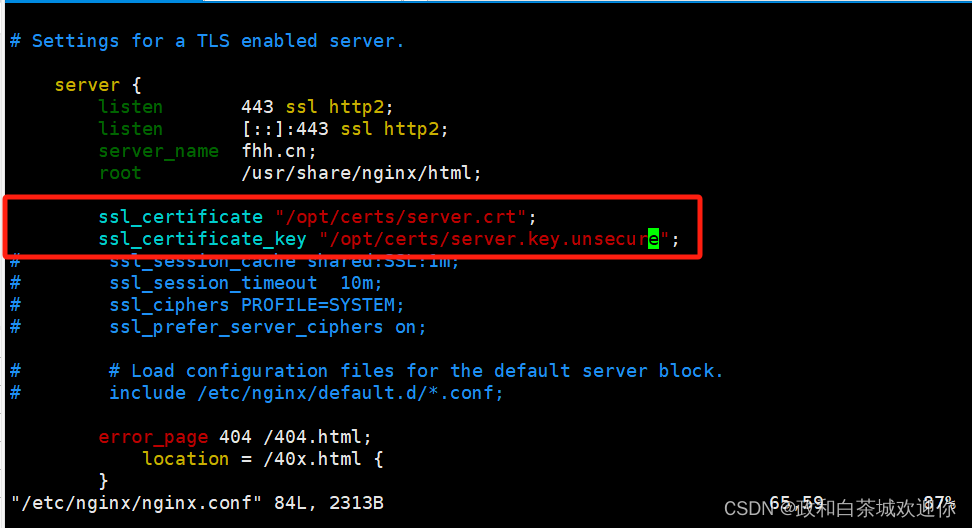
openssl rsa -in server.key -out server.key.unsecure 五、配置Nginx
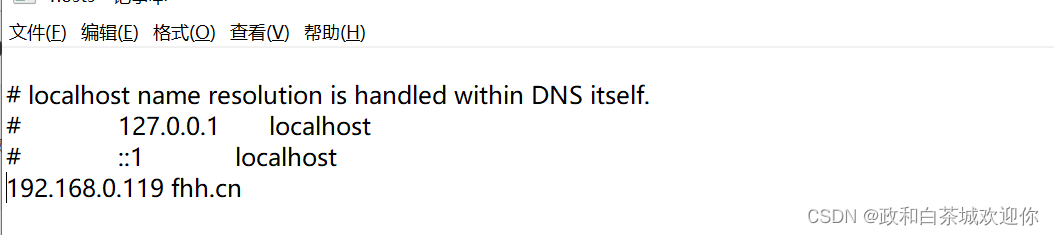
六、配置域名
在C:\Windows\System32\drivers\etc\hosts进行配置
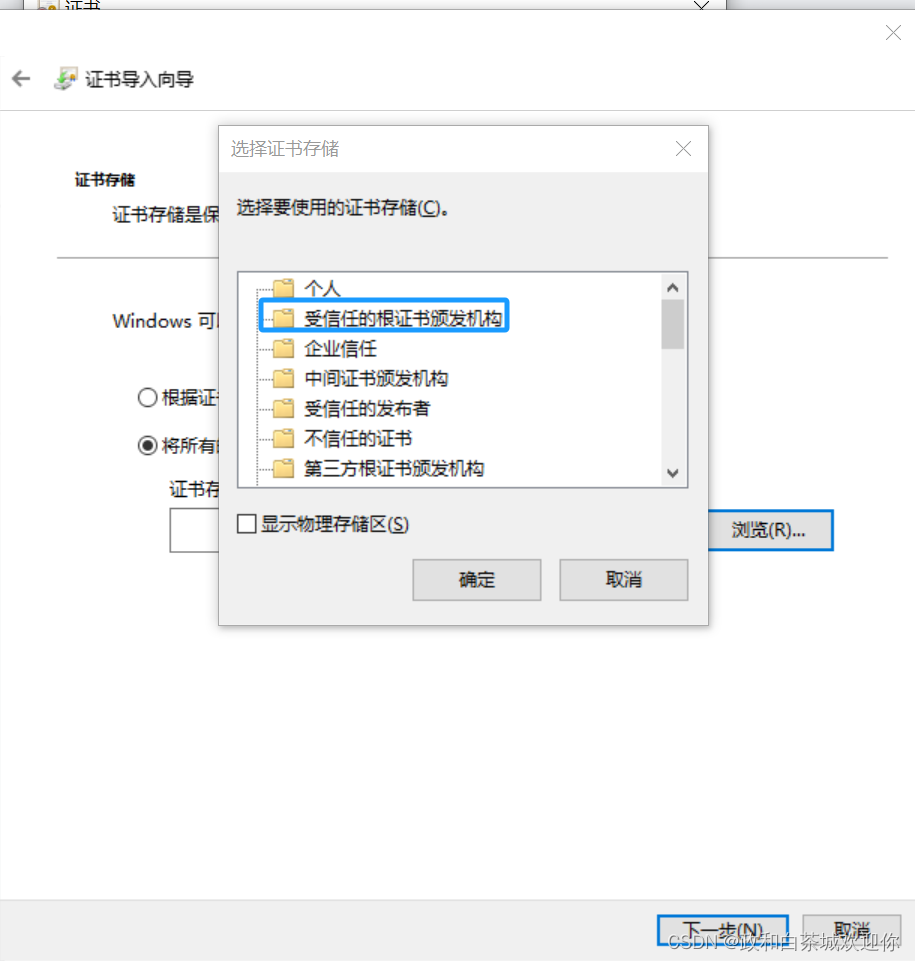
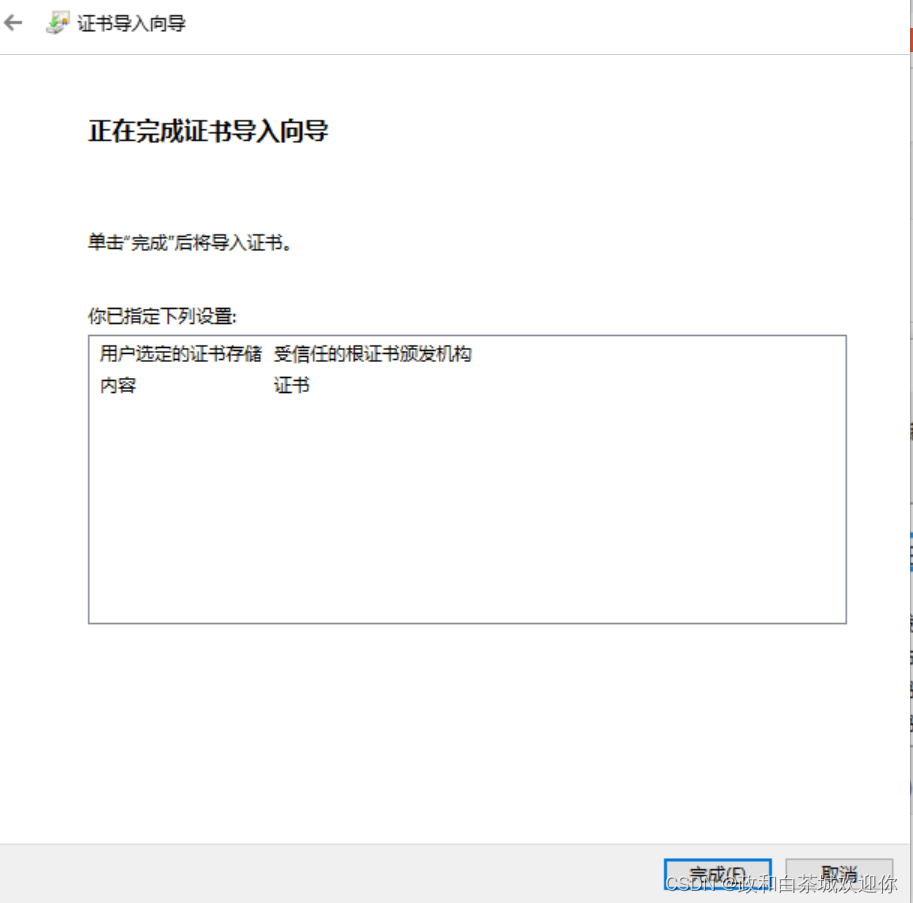
七、浏览器导入证书
把ca.crt证书导入到系统中


八、访问浏览器
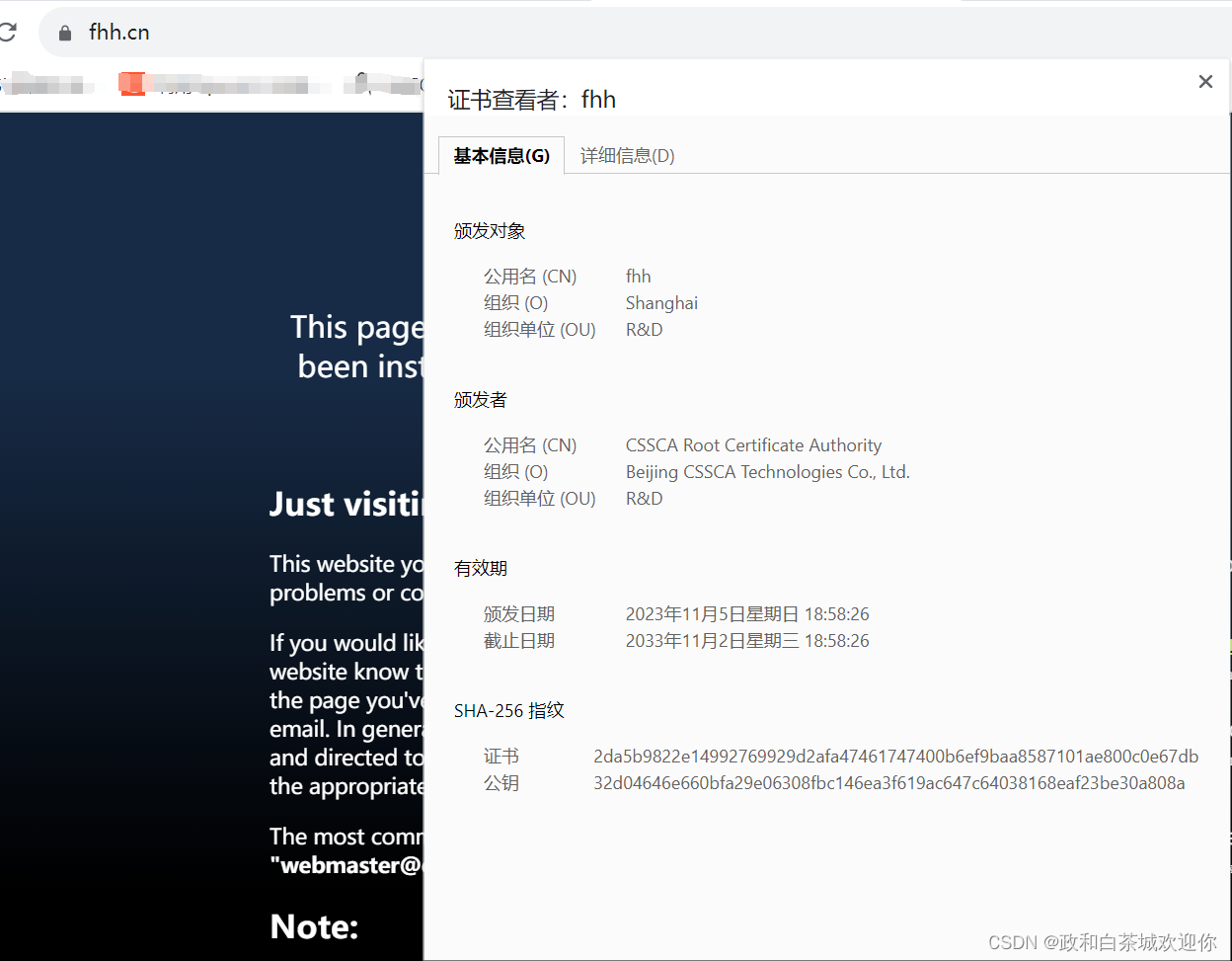








 https://fhh.cn/
https://fhh.cn/















 909
909

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








