Machine learning: Trends,perspectives, and prospects
机器学习:趋势、观点和前景
Abstract
Machine learning addresses the question of how to build computers that improve automatically through experience. It is one of today’s most rapidly growing technical fields, lying at the intersection of computer science and statistics, and at the core of artificial intelligence and data science. Recent progress in machine learning has been driven both by the development of new learning algorithms and theory and by the ongoing explosion in the availability of online data and low-cost computation. The adoption of data-intensive machine-learning methods can be found throughout science, technology and commerce, leading to more evidence-based decision-making across many walks of life, including health care, manufacturing, education, financial modeling, policing, and marketing.摘要
机器学习解决了如何建立通过训练自动改进的计算机的问题。它是当今位于计算机科学和统计学的交叉点发展最快的技术领域之一,也是人工智能和数据科学的核心。机器学习的最新进展是由新的学习算法和理论的发展以及在线数据和低成本计算的持续爆炸所推动的。在科学、技术和商业中更多会使用数据密集型机器学习方法,从而导致在医疗保健、制造业、教育、金融建模、警察和市场营销等领域采取了更多基于证据的决策。
正文
Machine learning is a discipline focused on two interrelated questions: How can one construct computer systems that auto-matically improve through experience? and What are the fundamental statistical-computational-information-theoretic laws that govern all learning systems, including computers, humans, and organizations? The study of machine learning is important both for addressing these fundamental scientific and engineering questions and for the highly practical computer software it has produced and fielded across many applications.
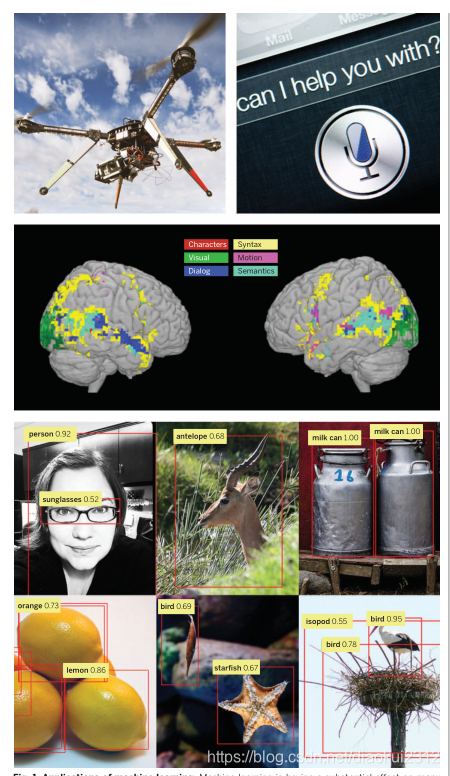
Machine learning has progressed dramatically over the past two decades, from laboratory curiosity to a practical technology in widespread commercial use. Within artificial intelligence (AI), machine learning has emerged as the method of choice for developing practical software for computer vision, speech recognition, natural language processing, robot control, and other applications. Many developers of AI systems now recognize that, for many applications, it can be far easier to train a system by showing it examples of desired input-output behavior than to program it manually by anticipating the desired response for all possible inputs. The effect of machine learning has also been felt broadly across computer science and across a range of industries concerned with data-intensive issues, such as consumer services, the diagnosis of faults in complex systems, and the control of logistics chains. There has been a similarly broad range of effects across empirical sciences, from biology to cosmology to social science, as machine-learning methods have been developed to analyze highthroughput experimental data in novel ways. See Fig. 1 for a depiction of some recent areas of application of machine learning.
机器学习是一门专注于两个相互关联的问题的学科:
一是如何构建一个通过经验自动改进的计算机系统?
二是统计计算信息理论的基本定律是什么,它是怎么支配着所有的学习系统,包括计算机、人类和组织的?
机器学习的研究对于解决这些基本的科学和工程问题以及它在许多应用中产生和应用的高度实用的计算机软件都很重要。
机器学习在过去的二十年里取得了巨大的进步,从实验室的好奇心到广泛商业应用的实用技术。在人工智能(AI)中,机器学习已经成为开发计算机视觉、语音识别、自然语言处理、机器人控制和其他应用的实用软件的首选方法。许多人工智能系统的开发人员现在认识到,对于许多应用来说,通过展示期望的输入-输出行为的例子来训练一个系统要比手动编程来预测所有可能输入的预期响应要容易得多。在计算机科学和涉及数据密集型问题的一系列行业也广泛地感受到了机器学习的效果,如消费者服务、复杂系统故障诊断和物流链控制。随着机器学习方法以新的方式分析高通量的实验数据,在生物学到宇宙学到社会科学的经验科学中也有类似广泛的影响。图1描述了有关机器学习的一些最新应用领域的描述。
A learning problem can be defined as the problem of improving some measure of performance when executing some task, through some type of training experience. For example, in learning to detect credit-card fraud, the task is to assign a label of “fraud” or“not fraud” to any given credit-card transaction. The performance metric to be improved might be the accuracy of this fraud classifier, and the training experience might consist of a collection of historical credit-card transactions, each labeled in retrospect as fraudulent or not. Alternatively, one might define a different performance metric that assigns a higher penalty when “fraud” is labeled “not fraud” than when “not fraud” is incorrectly labeled “fraud.” One might also define a different type of training experience—for example, by including unlabeled credit-card transactions along with labeled examples. A diverse array of machine-learning algorithms has been developed to cover the wide variety of data and problem types exhibited across different machine-learning problems (1, 2). Conceptually, machine-learning algorithms can be viewed as searching through a large space of candidate programs, guided by training experience, to find a program that optimizes the performance metric. Machine-learning algorithms vary greatly, in part by the way in which they represent candidate programs (e.g., decision trees, mathematical functions, and general programming languages) and in part by the way in which they search through this space of programs (e.g., optimization algorithms with well-understood convergence guarantees and evolutionary search methods that evaluate successive generations of randomly mutated programs). Here, we focus on approaches that have been particularly successful to date. Many algorithms focus on function approximation problems, where the task is embodied in a function (e.g., given an input transaction, output a “fraud” or “not fraud” label), and the learning problem is to improve the accuracy of that function, with experience consisting of a sample of known input-output pairs of the function. In some cases, the function is represented explicitly as a parameterized functional form; in other cases, the function is implicit and obtained via a search process, a factorization, an optimization procedure, or a simulation-based procedure. Even when implicit, the function generally depends on parameters or other tunable degrees of freedom, and training corresponds to finding values for these parameters that optimize the performance metric. Whatever the learning algorithm, a key scientific and practical goal is to theoretically characterize the capabilities of specific learning algorithms and the inherent difficulty of any given learning problem: How accurately can the algorithm learn from a particular type and volume of training data? How robust is the algorithm to errors in its modeling assumptions or to errors in the training data? Given a learning problem with a given volume of training data, is it possible to design a successful algorithm or is this learning problem fundamentally intractable? Such theoretical characterizations of machine-learning algorithms and problems typically make use of the familiar frameworks of statistical decision theory and computational complexity theory.In fact, attempts to characterize machine-learning algorithms theoretically have led to blends of statistical and computational theory in which the goal is to simultaneously characterize the sample complexity (how much data are required to learn accurately) and the computational complexity (how much computation is required) and to specify how these depend on features of the learning algorithm such as the representation it uses for what it learns (3–6). A specific form of computational analysis that has proved particularly useful in recent years has been that of optimization theory, with upper and lower bounds on rates of convergence of optimization procedures merging well with the formulation of machine-learning problems as the optimization of a performance metric (7, 8). As a field of study, machine learning sits at the crossroads of computer science, statistics and a variety of other disciplines concerned with automatic improvement over time, and inference and decision-making under uncertainty. Related disciplines include the psychological study of human learning, the study of evolution, adaptive control theory, the study of educational practices, neuroscience, organizational behavior, and economics. Although the past decade has seen increased crosstalk with these other fields, we are just beginning to tap the potential synergies and the diversity of formalisms and experimental methods used across these multiple fields for studying systems that improve with experience.
学习问题可以定义为在执行某项任务时,通过某种类型的训练经验来提高某种性能的问题。例如,在学习检测信用卡欺诈时,任务是给任何给定的信用卡交易判定一个“欺诈”或“不欺诈”的标签。需要改进的性能指标可能是该欺诈分类器的准确性,而训练经验可能包括一组历史信用卡交易,每一笔交易回顾起来都被标记为欺诈或不欺诈。或者,可以定义一个不同的性能指标,当“欺诈”被标记为“非欺诈”时,会比“不欺诈”被错误地标记为“欺诈”时分配更高的惩罚。还可以定义不同类型的训练经验,例如,通过训练经验中同时包括未标记的信用卡交易记录和有标签的信用卡交易记录。
人们已经开发了一系列不同的机器学习算法,以涉及不同机器学习问题(1,2)中显示的各种数据和问题类型。从概念上讲,机器学习算法可以看作是在训练经验的指导下,在大量候选程序空间中搜索,并找到一个优化性能指标的程序。机器学习算法内部有很多区别,部分原因在于它们表示候选程序(例如决策树、数学函数和通用编程语言)的方式,另一部分在于它们在程序空间中搜索的方式(例如,具有易于理解的收敛保证的优化算法和评估连续几代的随机变异程序的进化搜索方法)。在这里,我们将重点放在迄今为止特别成功的方法。
许多算法专注于函数逼近问题,其中任务体现在函数中(例如,给定一个输入事务,输出一个“欺诈”或“不欺诈”标签),学习问题是提高该函数的准确性,经验包括已知输入输出对(已打标数据)的样本。在某些情况下,此功能显式表示为参数化函数形式;在其他情况下,函数是隐式的,可以通过搜索过程、因子分解、优化过程或基于仿真的过程获得。即使是隐式的,函数通常也依赖于参数或其他可调自由度,而训练对应于为这些参数寻找优化性能指标的值。
无论学习算法是什么,一个重要的科学且实用的目标是从理论上描述特定学习算法的能力和任何给定学习问题的固有难题:
1.算法如何准确地从特定类型和数量的训练数据中学习?
2.该算法对其建模假设中的错误或对训练数据中的错误的鲁棒性如何?
3.给定一个学习问题,在给定的训练数据量下,是否有可能设计成功的算法,或者此学习问题从根本上是否是棘手的?
这种机器学习算法和问题的理论描述通常使用成熟的统计决策理论和计算复杂性的框架理论。实际上,从理论上描述机器学习算法的尝试促进了统计理论和计算理论的融合,其目标是同时描述样本复杂性(准确学习需要多少数据)和计算复杂性(需要多少计算),并指定这些内容与学习算法的关系,例如它所学内容的表示(3-6)。近年来被证明特别有效的计算分析的一种具体形式是优化理论,优化过程的收敛速度的上下界与机器学习问题的表述很好地结合在一起,作为性能优化的指标(7,8)。
作为一个研究领域,机器学习处于计算机科学、统计学和其他各种学科的十字路口,这些学科涉及随着时间的推移自动改进,以及在不确定性下的推理和决策。相关学科包括人类学习的心理学研究、进化研究、适应性控制理论、教育实践研究、神经科学、组织行为学和经济学。尽管在过去的十年中,我们已经看到了机器学习与这些其他领域的交流增加了,但我们才刚刚开始挖掘潜在的协同效应,以及在这些多个领域使用的形式和实验方法的多样性来研究随着经验而改进的系统。
Drivers of machine-learning progress
The past decade has seen rapid growth in the ability of networked and mobile computing systems to gather and transport vast amounts of data, a phenomenon often referred to as “Big Data.” The scientists and engineers who collect such data have often turned to machine learning for solutions to the problem of obtaining useful insights, predictions, and decisions from such data sets. Indeed, the sheer size of the data makes it essential to develop scalable procedures that blend computational and statistical considerations, but the issue is more than the mere size of modern data sets; it is the granular,personalized nature of much of these data. Mobile devices and embedded computing permit large amounts of data to be gathered about individual humans, and machine-learning algorithms can learn from these data to customize their services to the needs and circumstances of each individual. Moreover, these personalized services can be connected, so that an overall service emerges that takes advantage of the wealth and diversity of data from many individuals while still customizing to the needs and circumstances of each. Instances of this trend toward capturing and mining large quantities of data to improve services and productivity can be found across many fields of commerce, science, and government. Historical medical records are used to discover which patients will respond best to which treatments; historical traffic data are used to improve traffic control and reduce congestion; historical crime data are used to help allocate local police to specific locations at specific times; and large experimental data sets are captured and curated to accelerate progress in biology, astronomy, neuroscience, and other data intensive empirical sciences. We appear to be at the beginning of a decades-long trend toward increasingly data-intensive,evidence-based decision making across many aspects of science, commerce,and government.
With the increasing prominence of large-scale data in all areas of human endeavor has come awave of new demands on the underlying machine learning algorithms. For example, huge data sets require computationally tractable algorithms, highly personal data raise the need for algorithms that minimize privacy effects, and the availability of huge quantities of unlabeled data raises the challenge of designing learning algorithms to take advantage of it. The next sections survey some of the effects of these demands on recent work in machine-learning algorithms, theory, and practice.
推进机器学习进度的因素
在过去的十年里,网络和移动计算系统收集和传输大量数据的能力迅速增长,这种现象通常被称为“大数据”。收集这些数据的科学家和工程师经常使用机器学习在这些数据集的预测和决策上获取有用见解。确实,数据的巨大规模使得开发融合计算和统计考虑的可扩展程序变得至关重要,但问题不仅仅是现代数据集的大小,而是这些数据的细化、个性化特性。移动设备和嵌入式计算允许收集大量关于人类个体的数据,而机器学习算法可以从这些数据中学习,以根据每个人的需要和环境定制他们的服务。此外,这些个性化服务可以连接起来,这样就形成了一个整体服务,此服务利用了来自许多个人的丰富和多样的数据,同时仍然可以根据每个人的需要和情况进行定制。在商业、科学和政府的许多领域都可以找到收集和挖掘大量数据以提高服务和生产率的趋势。比如:历史医疗记录用于发现哪些患者对哪种治疗反应最好;历史交通数据用于改善交通管制和减少拥堵;历史犯罪数据用于帮助在特定时间将当地警察分配到特定地点;收集和整理大量的实验数据集,以加速生物学、天文学、神经科学和其他数据密集型经验科学的发展。在科学、商业和政府的许多方面,我们似乎正处于一个长达数十年的,越来越依赖于数据、基于证据决策的趋势的开端。
随着大规模数据在人类各个领域的日益突出,对底层机器学习算法提出了新的要求。例如,庞大的数据集需要计算上易于处理的算法,高度个性化的数据增加了对最小化隐私影响的算法的需求,大量未标记数据的可用性提出了设计学习算法来利用它的挑战。接下来的部分将介绍这些需求对机器学习算法、理论和实践的最新工作的一些影响。
Core methods and recent progress
The most widely used machine-learning methods are supervised learning methods. Supervised learning systems, including spam classifiers of e-mail, face recognizers over images, and medical diagnosis systems for patients, all exemplify the function approximation problem discussed earlier, where the training data take the form of a collection of (x, y) pairs and the goal is to produce a prediction y* in response to a query x*. The inputs x may be classical vectors or they may be more complex objects such as documents, images, DNA sequences, or graphs. Similarly, many different kinds of output y have been studied. Much progress has been made by focusing on the simple binary classification problem in which y takes on one of two values (for example, “spam” or “not spam”), but there has also been abundant research on problems such as multiclass classification (where y takes on one of K labels), multilabel classification (where y is labeled simultaneously by several of the K labels), ranking problems (where y provides a partial order on some set), and general structured prediction problems (where y is a combinatorial object such as a graph, whose components may be required to satisfy some set of constraints). An example of the latter problem is part-of-speech tagging, where the goal is to simultaneously label every word in an input sentence x as being a noun, verb, or some other part of speech. Supervised learning also includes cases in which y has realvalued components or a mixture of discrete and real-valued components.
Supervised learning systems generally form their predictions via a learned mapping f(x), which produces an output y for each input x (or a probability distribution over y given x). Many different forms of mapping f exist, including decision trees, decision forests, logistic regression, support vector machines, neural networks, kernel machines, and Bayesian classifiers. A variety of learning algorithms has been proposed to estimate these different types of mappings, and there are also generic procedures such as boosting and multiple kernel learning that combine the outputs of multiple learning algorithms. Procedures for learning f from data often make use of ideas from optimization theory or numerical analysis, with the specific form of machinelearning problems (e.g., that the objective function or function to be integrated is often the sum over a large number of terms) driving innovations. This diversity of learning architectures and algorithms reflects the diverse needs of applications, with different architectures capturing different kinds of mathematical structures, offering different levels of amenability to post-hoc visualization and explanation, and providing varying trade-offs between computational complexity, the amount of data, and performance.
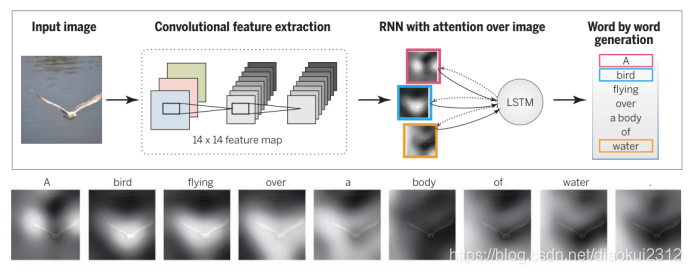
One high-impact area of progress in supervised learning in recent years involves deep networks, which are multilayer networks of threshold units, each of which computes some simple parameterized function of its inputs(9, 10). Deep learning systems make use of gradient-based optimization algorithms to adjust parameters throughout such a multilayered network based on errors at its output. Exploiting modern parallel computing architectures, such as graphics processing units originally developed for video gaming, it has been possible to build deep learning systems that contain billions of parameters and that can be trained on the very large collections of images, videos, and speech samples available on the Internet. Such large-scale deep learning systems have had a major effect in recent years in computer vision (11) and speech recognition (12), where they have yielded major improvements in performance over previous approaches (see Fig. 2). Deep network methods are being actively pursued in a variety of additional applications from natural language translation to collaborative filtering.
核心方法和最新进展
最广泛使用的机器学习方法是监督学习方法。有监督的学习系统,包括电子邮件的垃圾邮件分类器、图像上的人脸识别器和针对患者的医疗诊断系统,都是前面讨论过的函数逼近问题的例子,其中训练数据采用(x,y)对的集合形式,目标是生成对查询x的预测y。输入x可以是经典向量,也可以是更复杂的对象,例如文档、图像、DNA序列或图形。类似地,研究了许多不同种类的输出y。在简单的二元分类问题中,y取两个值中的一个(例如,“垃圾邮件”或“非垃圾邮件”)已经取得了很大的进展,但是对于诸如多类分类(y取K个标签中的一个)的问题也有大量的研究,多标签分类(其中y由多个K标签同时标记)、排名问题(其中y在某个集合上提供偏序)和一般结构化预测问题(其中y是组合对象(例如图),其组件可能需要满足某些约束集)。后一个问题的一个例子是词性标注,目标是同时将输入句子x中的每个单词标记为名词、动词或其他词性。监督学习还包括y具有实值分量或离散分量与实值分量的混合的情况。
有监督学习系统通常通过学习映射f(x)形成预测,f(x)为每个输入x产生一个输出y(或给定x在y上的概率分布)。存在许多不同形式的映射,包括决策树、随机森林、logistic回归、支持向量机、神经网络、内核机和贝叶斯分类器。人们已经提出了各种学习算法来估计这些不同类型的映射,还有一些结合了多种学习算法的输出的通的过程,如boosting和多核学习。从数据中学习f的过程通常利用最优化理论或数值分析的思想,以及机器学习问题的特定形式(例如,目标函数或待集成的函数通常是大量项的总和)推动创新。学习体系结构和算法的多样性反映了应用程序的不同需求,不同的体系结构是使用了了不同种类的数学结构,为事后可视化和解释提供了不同程度的适应性,并在计算复杂度、数据量和性能之间提供了不同的权衡。
近年来,监督学习的一个重要进展领域涉及深度网络,它是由阈值单元组成的多层网络,每个阈值单元都计算其输入的一些简单参数化函数(9,10)。深度学习系统利用基于梯度的优化算法,根据输出的误差调整多层网络中的参数。利用现代并行计算体系结构,如最初为视频游戏开发的图形处理单元,可以构建包含数十亿个参数的深度学习系统,这些系统可以根据互联网上提供的大量图像、视频和语音样本进行训练。这种大规模的深度学习系统在计算机视觉(11)和语音识别(12)方面产生了重大影响,与以前的方法相比,它们在性能方面取得了重大改进(见图2)。从自然语言翻译到协同过滤,深层网络方法正被广泛应用。
The internal layers of deep networks can be viewed as providing learned representations of the input data. While much of the practical success in deep learning has come from supervised learning methods for discovering such representations, efforts have also been made to develop deep learning algorithms that discover useful representations of the input without the need for labeled training data (13). The general problem is referred to as unsupervised learning, a second paradigm in machine-learning research (2).
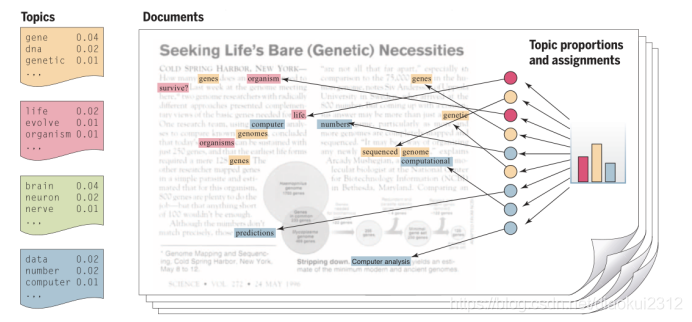
Broadly, unsupervised learning generally involves the analysis of unlabeled data under assumptions about structural properties of the data (e.g., algebraic, combinatorial, or probabilistic). For example, one can assume that data lie on a low-dimensional manifold and aim to identify that manifold explicitly from data. Dimension reduction methods—including principal components analysis, manifold learning, factor analysis, random projections, and autoencoders (1, 2)—make different specific assumptions regarding the underlying manifold (e.g., that it is a linear subspace, a smooth nonlinear manifold, or a collection of submanifolds). Another example of dimension reduction is the topic modeling framework depicted in Fig. 3. A criterion function is defined that embodies these assumptions—often making use of general statistical principles such as maximum likelihood, the method of moments, or Bayesian integration—and optimization or sampling algorithms are developed to optimize the criterion. As another example, clustering is the problem of finding a partition of the observed data (and a rule for predicting future data) in the absence of explicit labels indicating a desired partition. A wide range of clustering procedures has been developed, all based on specific assumptions regarding the nature of a “cluster.” In both clustering and dimension reduction, the concern with computational complexity is paramount, given that the goal is to exploit the particularly large data sets that are available if one dispenses with supervised labels.
可以将深度网络的内部层视为提供学习的输入数据表示形式。虽然深度学习的很多实际成功来自于发现此类表示的监督学习方法,但人们仍在努力开发深度学习算法,这些算法可从无标记训练数据中发现输入的有用表示(13)。一般这种问题被称为无监督学习,这是机器学习研究中的第二个大类型(2)。
广义地讲,无监督学习通常涉及在有关数据的结构特性(例如代数,组合或概率)的假设下对未标记数据进行分析。例如,可以假设数据位于低维流形上,并且目的是从数据中明确标识该流形。这种将数据固定假设在低维的思想需要用到降维方法,包括主成分分析,流形学习,因子分析,随机投影和自动编码器(1,2),同时对基础流形做出了不同的特定假设(例如,它是线性子空间,平滑非线性流形,或子流形的集合)。降维的另一个示例是图3中描述的主题建模框架。定义了一个标准函数来体现这些假设(通常利用常见的统计原理,例如最大似然,矩方法或贝叶斯积分)以及优化或开发了采样算法以优化标准。作为另一示例,聚类是在缺少指示期望分区的显式标签的情况下找到观测数据的分区(以及用于预测未来数据的规则)的问题。根据有关“集群”性质的特定假设,已经开发了各种各样的集群程序。在聚类和降维方面,考虑到目标是要利用特别大的数据集(如果人们放弃了监督标签的话),那么对计算复杂性的关注是至关重要的。
A third major machine-learning paradigm is reinforcement learning (14, 15). Here, the information available in the training data is intermediate between supervised and unsupervised learning. Instead of training examples that indicate the correct output for a given input, the training data in reinforcement learning are assumed to provide only an indication as to whether an action is correct or not; if an action is incorrect, there remains the problem of finding the correct action. More generally, in the setting of sequences of inputs, it is assumed that reward signals refer to the entire sequence; the assignment of credit or blame to individual actions in the sequence is not directly provided. Indeed, although simplified versions of reinforcement learning known as bandit problems are studied, where it is assumed that rewards are provided after each action, reinforcement learning problems typically involve a general control-theoretic setting in which the learning task is to learn a control strategy (a “policy”) for an agent acting in an unknown dynamical environment, where that learned strategy is trained to chose actions for any given state, with the objective of maximizing its expected reward over time. The ties to research in control theory and operations research have increased over the years, with formulations such as Markov decision processes and partially observed Markov decision processes providing points of contact (15, 16). Reinforcement-learning algorithms generally make use of ideas that are familiar from the control-theory literature, such as policy iteration, value iteration, rollouts, and variance reduction, with innovations arising to address the specific needs of machine learning (e.g., largescale problems, few assumptions about the unknown dynamical environment, and the use of supervised learning architectures to represent policies). It is also worth noting the strong ties between reinforcement learning and many decades of work on learning in psychology and neuroscience, one notable example being the use of reinforcement learning algorithms to predict the response of dopaminergic neurons in monkeys learning to associate a stimulus light with subsequent sugar reward (17).
Although these three learning paradigms help to organize ideas, much current research involves blends across these categories. For example, semisupervised learning makes use of unlabeled data to augment labeled data in a supervised learning context, and discriminative training blends architectures developed for unsupervised learning with optimization formulations that make use of labels. Model selection is the broad activity of using training data not only to fit a model but also to select from a family of models, and the fact that training data do not directly indicate which model to use leads to the use of algorithms developed for bandit problems and to Bayesian optimization procedures. Active learning arises when the learner is allowed to choose data points and query the trainer to request targeted information, such as the label of an otherwise unlabeled example. Causal modeling is the effort to go beyond simply discovering predictive relations among variables, to distinguish which variables causally influence others (e.g., a high white-blood-cell count can predict the existence of an infection, but it is the infection that causes the high white-cell count). Many issues influence the design of learning algorithms across all of these paradigms, including whether data are available in batches or arrive sequentially over time, how data have been sampled, requirements that learned models be interpretable by users, and robustness issues that arise when data do not fit prior modeling assumptions.
机器学习的第三个主要类型是强化学习(14、15)。在这里,训练数据中可用的信息介于有监督学习和无监督学习之间。在强化学习中,我们假设训练数据只提供一个动作是否正确的提示,而不是给出一个给定输入的正确输出。如果某个操作不正确,则继续存在寻找正确操作。换句话说,在输入序列的设置中,假设奖励信号指的是整个序列。没有直接提供序列中对单个操作的权重或责任分配。的确,尽管研究了强化学习的简化形式——强盗问题,但假定在每次行动后都会获得奖励,强化学习问题通常涉及一般的控制理论环境,学习任务是学习在未知的动态环境中如何行动能获得最大奖励的控制策略(一种“策略”),在新的行动中,受过训练的控制策略被训练为在任何给定状态选择行为,目的是在一段时间内最大化其预期报酬。多年来,控制理论研究与运筹学研究之间的联系日益紧密,诸如马尔可夫决策过程和部分观察到的马尔可夫决策过程等公式提供了联系点(15、16)。强化学习算法通常利用控制理论文献中熟悉的思想,例如策略迭代,值迭代,推出和减小方差,并出现了一些创新来满足机器学习的特定需求(例如大规模问题,对未知动态环境的一些假设,以及使用监督学习体系来表示策略)。值得注意的是,强化学习与心理学和神经科学领域的许多研究工作之间有着密切的联系,一个值得注意的例子是在猴子学习遇到刺激光反应与后续糖奖励时使用强化学习算法来预测多巴胺神经元的反应(17)。
尽管这三种学习模式更加容易思考,但当前仍有许多研究涉及将这些类别进行融合。例如,半监督学习在监督学习的上下文中利用未标记的数据来增强标记的数据,这种判别式训练将针对无监督学习而开发的架构与利用标签的优化公式相结合。
模型选择是一项有很多选项的行为,虽然训练数据不能直接指示要使用哪种模型,但不仅可以使用训练数据来拟合模型,而且还可以从一系列模型中进行选择,这一事实导致了使用针对强盗问题和贝叶斯优化程序。当允许学习者选择数据点并向训练者查询以获得目标信息(例如另一个未标记示例的标签)时,这就是主动学习。
因果模型不仅仅是发现变量之间的预测关系,而是要努力区分哪些变量会对其他变量造成因果影响(例如,高白细胞计数可以预测感染的存在,但正是感染导致了高白细胞计数)。许多问题都会影响所有这些范式中学习算法的设计,包括数据是成批提供还是随时间顺序到达,数据是如何采样的,要求学习的模型可由用户解释的要求以及在数据不符合先前的建模假设时出现的鲁棒性问题。
Emerging trends
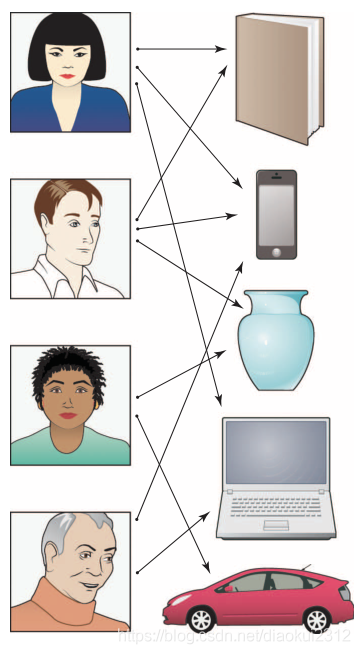
The field of machine learning is sufficiently young that it is still rapidly expanding, often by inventing new formalizations of machine-learning problems driven by practical applications. (An example is the development of recommendation systems, as described in Fig. 4.) One major trend driving this expansion is a growing concern with the environment in which a machine-learning algorithm operates. The word “environment” here refers in part to the computing architecture; whereas a classical machine-learning system involved a single program running on a single machine, it is now common for machine-learning systems to be deployed in architectures that include many thousands or ten of thousands of processors, such that communication constraints and issues of parallelism and distributed processing take center stage. Indeed, as depicted in Fig. 5, machine-learning systems are increasingly taking the form of complex collections of software that run on large-scale parallel and distributed computing platforms and provide a range of algorithms and services to data analysts.
新兴趋势
机器学习领域是一个新兴领域,它仍在迅速扩张,实际应用驱动的机器学习问题的新形式不断体现着机器学习的扩展程度。(一个示例是推荐系统的开发,如图4所示。)推动这种扩展的一个主要因素是人们对机器学习算法运行的环境的关注日益增长的趋势。
这里的“环境”一词是指计算架构。传统的机器学习系统只涉及在单个机器上运行的单个程序,而如今,机器学习系统通常部署在包含成千上万个处理器的体系结构中,从而实现通信约束和并行性以及成为中心焦点的分布式处理问题。
确实,如图5所示,机器学习系统越来越多地采用复杂软件集合的形式,这些软件在大规模并行和分布式计算平台上运行,并为数据分析人员提供一系列算法和服务。

The word “environment” also refers to the source of the data, which ranges from a set of people who may have privacy or ownership concerns, to the analyst or decision-maker who may have certain requirements on a machine-learning system (for example, that its output be visualizable), and to the social, legal, or political framework surrounding the deployment of a system. The environment also may include other machine learning systems or other agents, and the overall collection of systems may be cooperative or adversarial. Broadly speaking, environments provide various resources to a learning algorithm and place constraints on those resources. Increasingly, machine-learning researchers are formalizing these relationships, aiming to design algorithms that are provably effective in various environments and explicitly allow users to express and control trade-offs among resources.
As an example of resource constraints, let us suppose that the data are provided by a set of individuals who wish to retain a degree of privacy. Privacy can be formalized via the notion of “differential privacy,” which defines a probabilistic channel between the data and the outside world such that an observer of the output of the channel cannot infer reliably whether particular individuals have supplied data or not (18). Classical applications of differential privacy have involved insuring that queries (e.g., “what is the maximum balance across a set of accounts?”) to a privatized database return an answer that is close to that returned on the nonprivate data. Recent research has brought differential privacy into contact with machine learning, where queries involve predictions or other inferential assertions (e.g., “given the data I’ve seen so far, what is the probability that a new transaction is fraudulent?”) (19, 20). Placing the overall design of a privacy-enhancing machine-learning system within a decision-theoretic framework provides users with a tuning knob whereby they can choose a desired level of privacy that takes into account the kinds of questions that will be asked of the data and their own personal utility for the answers. For example, a person may be willing to reveal most of their genome in the context of research on a disease that runs in their family but may ask for more stringent protection if information about their genome is being used to set insurance rates.
Communication is another resource that needs to be managed within the overall context of a distributed learning system. For example, data may be distributed across distinct physical locations because their size does not allow them to be aggregated at a single site or because of administrative boundaries. In such a setting, we may wish to impose a bit-rate communication constraint on the machine-learning algorithm. Solving the design problem under such a constraint will generally show how the performance of the learning system degrades under decrease in communication bandwidth, but it can also reveal how the performance improves as the number of distributed sites (e.g., machines or processors) increases, trading off these quantities against the amount of data (21, 22). Much as in classical information theory, this line of research aims at fundamental lower bounds on achievable performance and specific algorithms that achieve those lower bounds.
A major goal of this general line of research is to bring the kinds of statistical resources studied in machine learning (e.g., number of data points, dimension of a parameter, and complexity of a hypothesis class) into contact with the classical computational resources of time and space. Such a bridge is present in the “probably approximately correct” (PAC) learning framework, which studies the effect of adding a polynomial-time computation constraint on this relationship among error rates, training data size, and other parameters of the learning algorithm (3). Recent advances in this line of research include various lower bounds that establish fundamental gaps in performance achievable in certain machine-learning problems (e.g., sparse regression and sparse principal components analysis) via polynomial-time and exponential-time algorithms (23). The core of the problem, however, involves time-data tradeoffs that are far from the polynomial/exponential boundary. The large data sets that are increasingly the norm require algorithms whose time and space requirements are linear or sublinear in the problem size (number of data points or number of dimensions). Recent research focuses on methods such as subsampling, random projections, and algorithm weakening to achieve scalability while retaining statistical control (24, 25). The ultimate goal is to be able to supply time and space budgets to machine-learning systems in addition to accuracy requirements, with the system finding an operating point that allows such requirements to be realized.
“环境”一词也指数据的来源,从可能有隐私或所有权顾虑的人,到可能对机器学习系统有某些要求(例如,其输出是可视化的)的分析员或决策者,以及周围的社会、法律或政治框架系统的部署。该环境还可以包括其他机器学习系统或其他代理,并且系统的整体集合可以是协作的或对抗的。广义地说,环境为学习算法提供各种资源,并对这些资源施加限制。越来越多的机器学习研究人员正规范这些关系,旨在设计在各种环境中有效的算法,并找到允许用户表达和控制资源之间的折衷点。
作为资源限制的示例,我们假设数据是由一组希望保留一定程度隐私的个人提供的。隐私可以通过“差异性隐私”的概念来形式化,“差异性隐私”定义了数据与外部世界之间的概率通道,因此通道输出的观察者无法可靠地推断出特定个人是否提供了数据(18)。
差异隐私的经典应用涉及确保对私有化数据库的查询(例如“一组帐户中的最大余额是多少?”)返回的答案与对非私有数据返回的答案相近。最近的研究已将差异性隐私与机器学习联系起来,其中查询涉及预测或其他推断性断言(例如,“鉴于我到目前为止所看到的数据,新交易有欺诈性的可能性是多少?”)(19, 20)。
将增强隐私机器学习系统的总体设计放在决策理论框架内,为用户提供了一个调节旋钮,使他们可以选择所需的隐私级别,其中要考虑将要询问的数据和信息的种类。他们自己的实用程序来寻找答案。例如,一个人可能愿意在有关其家庭中所患疾病的研究中揭示其大部分基因组,但如果有关其基因组的信息被用于设定保险费率,则可能要求更严格的保护。
通信是另一个需要在分布式学习系统的整体环境中进行管理的资源。例如,数据可能会分布在不同的物理位置,因为它们的大小不允许它们在单个站点上聚合,或者由于管理边界的限制。
在这种情况下,我们可能希望对机器学习算法施加一个比特率通信约束。在这种约束下解决设计问题通常会显示出学习系统的性能如何在通信带宽降低的情况下下降,但也可以揭示性能随着分布式站点(例如机器或处理器)数量的增加而提高,将这些数量与数据量进行权衡(21,22)。与经典的编队理论非常相似,该研究领域的主要目标是实现性能的基本下限以及实现这些下限的特定算法。
这条研究路线的主要目标是将机器学习中研究的统计资源的种类(例如,数据点的数量,参数的维数,假设类的复杂性)与时间和空间的经典计算资源联系起来。“probably approximately correct”(PAC)学习框架可以将这些结合起来,该框架研究在误差率,训练数据大小和学习算法的其他参数之间的关系上添加多项式时间计算约束的影响(3)。
该研究领域的最新进展包括各种下界,这些下界通过多项式时间和指数时间算法在某些机器学习问题(例如,稀疏回归和稀疏主成分分析)中可实现的性能上体现出了巨大的差距(23)。然而,问题的核心在于时间数据的权衡要远离多项式/指数边界。越来越多的大型数据集需要算法,这些算法的时间和空间要求在问题大小(数据点数或维数)方面是线性或次线性的。
最近的研究集中在子采样,随机投影和弱化算法以在保持统计控制的同时实现定标能力的方法上(24,25)。最终目标是,除了准确性要求外,还能够为机器学习系统提供时间和空间预算,并且系统会找到一个可以实现此类要求的工作点。
Opportunities and challenges
Despite its practical and commercial successes, machine learning remains a young field with many underexplored research opportunities. Some of these opportunities can be seen by contrasting current machine-learning approaches to the types of learning we observe in naturally occurring systems such as humans and other animals, organizations, economies, and biological evolution. For example, whereas most machinelearning algorithms are targeted to learn one specific function or data model from one single data source, humans clearly learn many different skills and types of knowledge, from years of diverse training experience, supervised and unsupervised, in a simple-to-more-difficult sequence (e.g., learning to crawl, then walk, then run). This has led some researchers to begin exploring the question of how to construct computer lifelong or never-ending learners that operate nonstop for years, learning thousands of interrelated skills or functions within an overall architecture that allows the system to improve its ability to learn one skill based on having learned another (26–28). Another aspect of the analogy to natural learning systems suggests the idea of team-based, mixed-initiative learning. For example, whereas current machinelearning systems typically operate in isolation to analyze the given data, people often work in teams to collect and analyze data (e.g., biologists have worked as teams to collect and analyze genomic data, bringing together diverse experiments and perspectives to make progress on this difficult problem). New machine-learning methods capable of working collaboratively with humans to jointly analyze complex data sets might bring together the abilities of machines to tease out subtle statistical regularities from massive data sets with the abilities of humans to draw on diverse background knowledge to generate plausible explanations and suggest new hypotheses. Many theoretical results in machine learning apply to all learning systems, whether they are computer algorithms, animals, organizations, or natural evolution. As the field progresses, we may see machine-learning theory and algorithms increasingly providing models for understanding learning in neural systems, organizations, and biological evolution and see machine learning benefit from ongoing studies of these other types of learning systems.
As with any powerful technology, machine learning raises questions about which of its potential uses society should encourage and discourage. The push in recent years to collect new kinds of personal data, motivated by its economic value, leads to obvious privacy issues, as mentioned above. The increasing value of data also raises a second ethical issue: Who will have access to, and ownership of, online data, and who will reap its benefits? Currently, much data are collected by corporations for specific uses leading to improved profits, with little or no motive for data sharing. However, the potential benefits that society could realize, even from existing online data, would be considerable if those data were to be made available for public good.
To illustrate, consider one simple example of how society could benefit from data that is already online today by using this data to decrease the risk of global pandemic spread from infectious diseases. By combining location data from online sources (e.g., location data from cell phones, from credit-card transactions at retail outlets, and from security cameras in public places and private buildings) with online medical data (e.g., emergency room admissions), it would be feasible today to implement a simple system to telephone individuals immediately if a person they were in close contact with yesterday was just admitted to the emergency room with an infectious disease, alerting them to the symptoms they should watch for and precautions they should take. Here, there is clearly a tension and trade-off between personal privacy and public health, and society at large needs to make the decision on how to make this trade-off. The larger point of this example, however, is that, although the data are already online, we do not currently have the laws, customs, culture, or mechanisms to enable society to benefit from them, if it wishes to do so. In fact, much of these data are privately held and owned, even though they are data about each of us. Considerations such as these suggest that machine learning is likely to be one of the most transformative technologies of the 21st century. Although it is impossible to predict the future, it appears essential that society begin now to consider how to maximize its benefits.
机遇和挑战
尽管机器学习在实践和商业上取得了成功,但它仍然是一个年轻的领域,仍有许多等待探索的研究机会。通过对比当前的机器学习方法和我们在自然系统(如人类和其他动物、组织、经济和生物进化)中观察到的学习模型,我们可以从中找到一些灵感。
例如,虽然大多数机器学习算法的目标是从一个单一的数据源中学习一种特定的功能或数据模型,但人类显然可以从多年的各种培训经验中,通过有监督的和无监督的学习,从简单到更加困难的序列中学习许多不同的技能和知识类型(例如,学习爬行,行走,然后奔跑)。这促使一些研究人员开始探索以下问题:如何构建多年不间断运行的终身学习者或永无止境的学习者,在整个体系结构中学习数千种相互关联的技能或功能,以使系统在提高其学习某一项技能的能力的同时学习了另一项技能(26-28)。基于团队的混合主动学习的思想是类比自然学习系统的另一个方面。例如,尽管当前的机器学习系统通常是独立运行以分析给定的数据,但是人们通常会以团队的形式收集和分析数据(例如,生物学家作为团队来收集和分析基因组数据,将各种实验和观点汇集在一起,在这个难题上取得进展)。能够与人类合作以共同分析复杂数据集,这种新的机器学习方法可能将机器从大量数据集中挑逗出细微统计规律的能力与人类利用各种背景知识来产生合理解释和提出新的假设相结合。机器学习的许多理论结果适用于所有的学习系统,无论是计算机算法、动物、组织还是自然进化。随着该领域的发展,我们可能会看到机器学习理论和算法越来越多地为理解神经系统、组织和生物进化中的学习提供模型,并看到机器学习从正在进行的这些其他类型的学习系统的研究中受益。
与任何强大的技术一样,机器学习存在着这样一个问题:社会应该鼓励和抑制哪些潜在用途。近年来,由于受其经济价值的驱使,人们开始大力收集新型个人数据,这导致了明显的隐私问题,如上所述。数据不断增长的价值还引发了第二个伦理问题:谁将能够访问和拥有在线数据,谁将从中获益?目前,企业收集的大量数据都是用于提高利润的特定用途,很少或根本没有共享数据的动机。然而,如果将这些数据用于公共利益,那么即使从现有的在线数据中,社会也可以实现的潜在利益将是可观的。
为了说明这一点,请考虑一个简单的例子,说明社会如何能够从今天已经在线的数据中受益,利用这些数据来减少传染病在全球大流行传播的风险。通过将来自在线资源的位置数据(例如,来自手机的位置数据,来自零售店的信用卡交易以及来自公共场所和私人建筑物中的安全摄像机)与在线医疗数据(例如,急诊室挂号)相结合,将可以今天可行的是,如果一个昨天与他密切联系的人刚刚被送进传染病的急诊室就诊,可以提醒他们注意的症状和应采取的预防措施,以便立即给个人打电话。在这方面,个人隐私和公共健康之间显然存在着一种紧张和权衡,整个社会需要就如何权衡做出决定。然而,这个例子更重要的一点是,虽然数据已经在网上,但我们目前还没有法律、习俗、文化或机制使社会能够从中受益,如果它愿意这样做的话。事实上,这些数据中的大部分都是私人拥有的,即使它们是关于我们每个人的数据。诸如此类的考虑表明,机器学习可能会成为21世纪最具变革性的技术之一。虽然预测未来是不可能的,但社会现在开始考虑如何使其利益最大化似乎是必要的。






















 1066
1066











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








