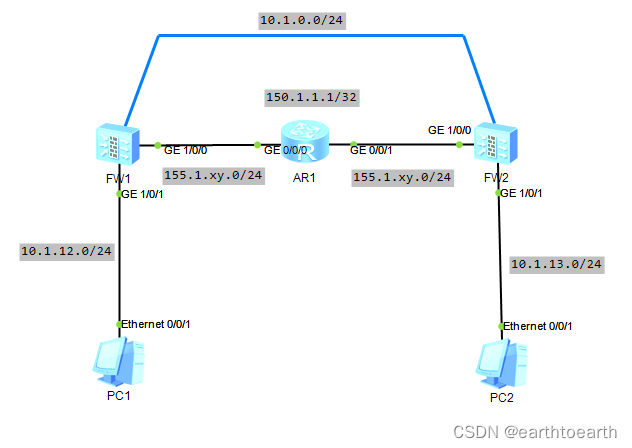
一、网络拓扑
实验思路:通过虚拟接口设置GRE隧道,使用ospf宣告路由,通过GRE联通PC1和PC2;第二步启用IPSEC传输模式,通过IPSEC方式承载GRE联通PC1和PC2
二、基础配置
安装拓扑所示配置相应的即可地址。(此处省略...............)
三、详细配置
(一)单纯GRE配置
FW1上配置:
[FW1-Tunnel0]dis th
#
interface Tunnel0
ip address 10.1.0.12 255.255.255.0
tunnel-protocol gre
source GigabitEthernet1/0/0
destination 155.1.131.13
#
[FW1-zone-dmz]dis th
#
firewall zone dmz
set priority 50
add interface Tunnel0
#
安全策略
[FW1-policy-security]dis th
#
security-policy
rule name LOCAL_TO_ANY
source-zone local
action permit
rule name IN_TO_OUT
source-zone trust
destination-zone untrust
action permit
rule name OUT_TO_LOCAL
source-zone untrust
destination-zone local
service protocol 47
service protocol 50
service protocol udp destination-port 500
action permit
rule name OUT_TO_IN
source-zone untrust
destination-zone trust
source-address 10.1.0.0 mask 255.255.0.0
destination-address 10.1.0.0 mask 255.255.0.0
action permit
rule name DMZ_TO_IN
source-zone dmz
destination-zone trust
source-address 10.1.0.0 mask 255.255.0.0
destination-address 10.1.0.0 mask 255.255.0.0
action permit
rule name IN_TO_DMZ
source-zone trust
destination-zone dmz
action permit
#
在隧道接口及内网接口上启用OSPF
[FW1]dis ospf peer brief
OSPF Process 1 with Router ID 10.1.12.12
Peer Statistic Information
----------------------------------------------------------------------------
Area Id Interface Neighbor id State
0.0.0.0 Tunnel0 155.1.131.13 Full
----------------------------------------------------------------------------
FW2上的配置与FW1上一致,但需修改响应的IP地址和对端
(二)GRE over IPSEC
IPSEC设置
#
acl number 3000
rule 5 permit gre
#
ipsec proposal LAN_SET
encapsulation-mode transport
esp authentication-algorithm sha1
esp encryption-algorithm 3des
#
ike proposal 10
encryption-algorithm 3des
dh group2
authentication-algorithm sha1
authentication-method pre-share
integrity-algorithm hmac-sha2-256
prf hmac-sha2-256
#
ike peer FW2
pre-shared-key HUAWEI@123
ike-proposal 10
remote-address 155.1.131.13
#
ipsec policy LAN_MAP 10 isakmp
security acl 3000
ike-peer FW2
proposal LAN_SET
#
安全策略设置
[FW1-policy-security]dis th
#
security-policy
rule name LOCAL_TO_ANY
source-zone local
action permit
rule name OUT_TO_LOCAL
source-zone untrust
destination-zone local
service protocol 50
service protocol udp destination-port 500
action permit
rule name DMZ_TO_IN
source-zone dmz
destination-zone trust
source-address 10.1.0.0 mask 255.255.0.0
destination-address 10.1.0.0 mask 255.255.0.0
action permit
rule name IN_TO_DMZ
source-zone trust
destination-zone dmz
action permit
#
端口应用
[FW1-GigabitEthernet1/0/0]dis th
#
interface GigabitEthernet1/0/0
undo shutdown
ip address 155.1.121.12 255.255.255.0
ipsec policy LAN_MAP
#
FW2上的配置与FW1上一致,但需修改响应的IP地址和对端
四、结果验证
(一)单纯GRE
PC>PING 10.1.13.10
Ping 10.1.13.10: 32 data bytes, Press Ctrl_C to break
Request timeout!
From 10.1.13.10: bytes=32 seq=2 ttl=126 time=15 ms
From 10.1.13.10: bytes=32 seq=3 ttl=126 time=16 ms
(二)GRE over IPSEC
[FW1]dis ike sa
IKE SA information :
Conn-ID Peer VPN Flag(
s) Phase RemoteType RemoteID
--------------------------------------------------------------------------------
----------------------------------------------------
31 155.1.131.13:500 RD|ST
|A v2:2 IP 155.1.131.13
30 155.1.131.13:500 RD|ST
|A v2:1 IP 155.1.131.13
Number of IKE SA : 2
--------------------------------------------------------------------------------
----------------------------------------------------
PC>PING 10.1.13.10
Ping 10.1.13.10: 32 data bytes, Press Ctrl_C to break
Request timeout!
From 10.1.13.10: bytes=32 seq=2 ttl=126 time=16 ms
From 10.1.13.10: bytes=32 seq=3 ttl=126 time=16 ms





















 1234
1234











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








