(一)安装elasticsearch
1 创建es安装路径
mkdir -p /data/es/{logs,data}
2 创建用户
useradd elastic -s /sbin/nologin
chown elastic -R /data/es
3 修改limit限制
vim /etc/security/limits.conf
* soft nofile 65536
* hard nofile 65536
* soft nproc 65536
* hard nproc 65536
4 修改内核参数并使之生效
vim /etc/sysctl.conf
vm.overcommit_memory = 1
#内核允许分配所有的物理内存,而不管当前的内存状态如何。
vm.max_map_count=655360
#max_map_count文件包含限制一个进程可以拥有的VMA(虚拟内存区域)的数量
sysctl -p
5 上传elasticsearch包到/data/es/目录。
cd /data/es
wget -c https://artifacts.elastic.co/downloads/elasticsearch/elasticsearch-7.1.1-linux-x86_64.tar.gz
tar -xvf elasticsearch-7.1.1-linux-x86_64.tar.gz
mv elasticsearch-7.1.1 elasticsearch
6 修改elasticsearch.yml
mv elasticsearch/config/elasticsearch.yml elasticsearch/config/elasticsearch.yml-template
vim elasticsearch/config/elasticsearch.yml
cluster.name: elkcluster #集群名称
node.name: elk #节点名称
cluster.initial_master_nodes: ["elk"] #主节点信息
path.data: /data/es/data #数据存放路径
path.logs: /data/es/logs #日志存放路径
bootstrap.memory_lock: false
bootstrap.system_call_filter: false
network.host: 0.0.0.0 #所有ip可以访问,
discovery.seed_hosts: ["elk"] #输出至elasticsearch服务器
discovery.zen.minimum_master_nodes: 2 #最多有几个可参与主节点选举
http.cors.enabled: true
http.max_initial_line_length: "1024k"
http.max_header_size: "1024k"
7 jvm heap分配设置堆内存值。 -Xms4g:初始化堆内存大小为2GB
vim elasticsearch/config/jvm.options
-Xms2g
-Xmx2g
#es7.6版本默认1GB,这个值太小,很容易导致OOM,大小不要超过物理内存的50%,最大值和最小值要相同,避免jvm heap在运行中resize,这是一个非常耗性能的过程。
#环境变量:ES_HEAP_SIZE,环境变量的优先级高于jvm.options中的设置的数值。
8 ik分词器安装
将准备好的ik分词器安装包解压后将文件复制到 es的安装目录/plugins/ik下面即可,没有目录则自行创建目录,目录文件夹下不能有其他东西
cd /data/es/elasticsearch/plugins/
mkdir ik
wget -c https://github.com/medcl/elasticsearch-analysis-ik/releases/download/v7.1.1/elasticsearch-analysis-ik-7.1.1.zip
unzip elasticsearch-analysis-ik-7.1.1.zip
9 启动elasticsearch
chown elastic -R /data/es/
su - elastic -s /bin/bash -c "/data/es/elasticsearch/bin/elasticsearch -d"
service文件
vim /usr/lib/systemd/system/elastic.service
[Unit]
Description=Elasticsearch server daemon
After=network.target
[Service]
User=elastic
Group=elastic
LimitNOFILE=100000
LimitNPROC=100000
ExecStart=/data/es/elasticsearch/bin/elasticsearch
ExecReload=/bin/kill -HUP $MAINPID
ExecStop=/bin/kill -SIGINT $MAINPID
KillMode=process
#Restart=always
Restart=on-failure
RestartSec=42s
[Install]
WantedBy=multi-user.target
10 访问x.x.x.x:port

11 配置 TLS
生成CA证书(一路回车就行)
cd /data/es/elasticsearch/bin
./elasticsearch-certutil ca
./elasticsearch-certutil cert --ca elastic-stack-ca.p12
mkdir /data/es/elasticsearch/config/certs
mv elastic-*.p12 config/certs/
chown -R elastic:elastic config/certs/
生成elastic-stack-ca.p12文件
./bin/elasticsearch-certutil ca
生成elastic-certificates.p12文件,供elasticsearch使用
./bin/elasticsearch-certutil cert --ca elastic-stack-ca.p12
生成newfile.crt.pem文件,供kibana和filebeat连接elastic认证使用,复制到各自对应目录下
openssl pkcs12 -in elastic-stack-ca.p12 -out newfile.crt.pem -clcerts -nokeys
生成certificate-bundle.zip文件,包含ca/ca.crt,instance/instance.crt,instance/instance.key
./bin/elasticsearch-certutil cert --pem elastic-stack-ca.p12
使用yml文件生成证书
vim /tmp/instance.yml
instances:
- name: 'server1'
dns: [ 'server1.example.com' ]
ip: [ '192.168.0.11' ]
- name: "server2"
dns: [ 'server2.example.com' ]
ip: [ '192.168.0.12' ]
- name: 'server3'
dns: [ 'server3.example.com' ]
ip: [ '192.168.0.13' ]
- name: 'centos-8'
dns: [ 'centos-8.example.com' ]
ip: [ '192.168.0.14' ]
./elasticsearch-certutil cert --keep-ca-key ca --pem --in /tmp/instance.yml --out /tmp/certs/certs.zip
vim /data/nusp/es/elasticsearch-7.1.1/config/elasticsearch.yml
只开启https,不验证
xpack.security.http.ssl.enabled: true
xpack.security.http.ssl.keystore.path: certs/elastic-certificates.p12
xpack.security.http.ssl.truststore.path: certs/elastic-certificates.p12
配置认证用户
手动配置每个用户密码模式(需要一个一个的输入)
cd /data/es/elasticsearch/bin
./elasticsearch-setup-passwords interactive
自动配置每个用户密码(随机生成并返回字符串密码,需要保存好)
./elasticsearch-setup-passwords auto
开启安全验证
xpack.security.enabled: true
xpack.security.transport.ssl.enabled: true
xpack.security.transport.ssl.verification_mode: certificate # 证书认证级别
xpack.security.transport.ssl.keystore.path: certs/elastic-certificates.p12
xpack.security.transport.ssl.keystore.type: PKCS12
xpack.security.transport.ssl.truststore.path: certs/elastic-stack.p12#(也可用certs/elastic-certificates.p12)
xpack.security.transport.ssl.truststore.type: PKCS12
示例:
cluster.name: elkcluster #集群名称
node.name: elk #节点名称
cluster.initial_master_nodes: ["elk:9300"] #主节点信息
path.data: /data/es/data #数据存放路径
path.logs: /data/es/logs #日志存放路径
bootstrap.memory_lock: false
bootstrap.system_call_filter: false
network.host: 0.0.0.0 #所有ip可以访问,
http.port: 9200
transport.tcp.port: 9300
discovery.seed_hosts: ["elk:9300"] #输出至elasticsearch服务器
discovery.zen.minimum_master_nodes: 2 #最多有几个可参与主节点选举
http.cors.enabled: true
http.max_initial_line_length: "1024k"
http.max_header_size: "1024k"
#配置集群密码
#xpack.security.enabled: true
#用HTTPS方式访问es(method1/2)
xpack.security.http.ssl.enabled: true
xpack.security.http.ssl.key: /data/es/elasticsearch/config/certs/private.key
xpack.security.http.ssl.certificate: /data/es/elasticsearch/config/certs/private.crt
xpack.security.http.ssl.certificate_authorities: /data/es/elasticsearch/config/certs/CA-certificate.crt
#xpack.security.http.ssl.enabled: true
#xpack.security.http.ssl.keystore.path: /data/es/elasticsearch/config/certs/elk.p12
#xpack.security.http.ssl.truststore.path: /data/es/elasticsearch/config/certs/elk.p12
##集群内部通信(method1/2)
xpack.security.transport.ssl.enabled: true
xpack.security.transport.ssl.verification_mode: certificate
xpack.security.transport.ssl.key: /data/es/elasticsearch/config/certs/private.key
xpack.security.transport.ssl.certificate: /data/es/elasticsearch/config/certs/private.crt
xpack.security.transport.ssl.certificate_authorities: ["/data/es/elasticsearch/config/certs/CA-certificate.crt"]
#xpack.security.transport.ssl.enabled: true
#xpack.security.transport.ssl.verification_mode: certificate # 证书认证级别
#xpack.security.transport.ssl.keystore.path: /data/es/elasticsearch/config/certs/elastic-certificates.p12
#xpack.security.transport.ssl.truststore.path: /data/es/elasticsearch/config/certs/elastic-certificates.p12
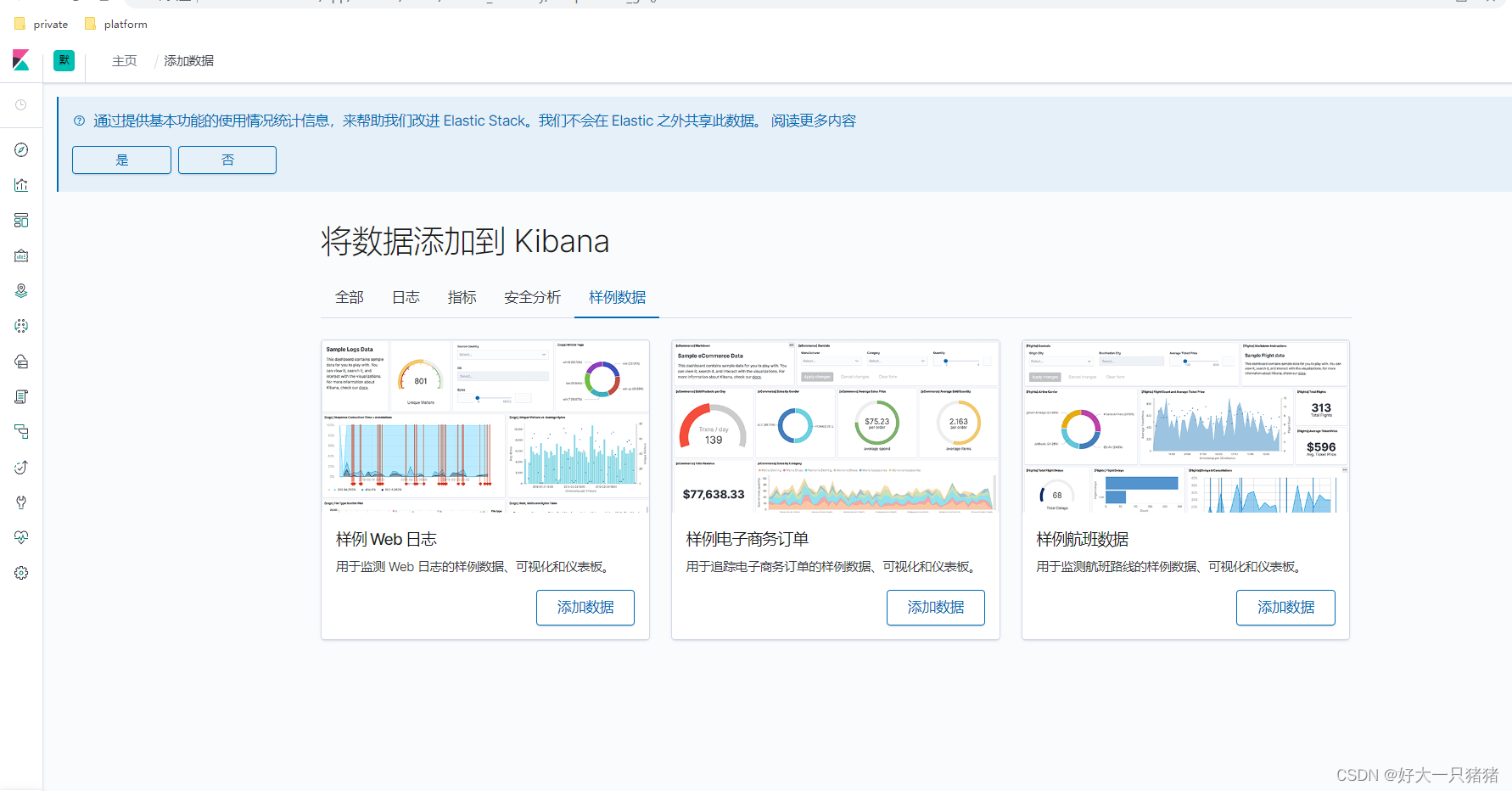
(二)部署kibana
1 上传kibana的tar包
cd /data/es
wget -c https://artifacts.elastic.co/downloads/kibana/kibana-7.1.1-linux-x86_64.tar.gz
tar -xvf kibana-7.1.1-linux-x86_64.tar.gz
mv kibana-7.1.1-linux-x86_64/ kibana
2 修改配置文件
mv kibana/config/kibana.yml kibana/config/kibana.yml-template
vim kibana/config/kibana.yml
server.port: 5601 #修改绑定ip,使外部可以通过http访问
server.host: "0.0.0.0" ##监听端口,可以不修改
elasticsearch.hosts: ["https://127.0.0.1:9200"]
i18n.locale: "zh-CN"
#elastic访问账号(如果存在)
#elasticsearch.username: "xx"
#elasticsearch.password: "xx"
#kibana访问elastic集群(method1/2)
elasticsearch.ssl.verificationMode: certificate
elasticsearch.ssl.certificateAuthorities: ["/data/es/kibana/config/certs/CA-certificate.crt"]
#elasticsearch.ssl.verificationMode: none
#elasticsearch.ssl.certificateAuthorities: ["/data/es/kibana/config/certs/kibana.crt.pem"]
#ssl访问kibana
server.ssl.enabled: true
server.ssl.certificate: /data/es/kibana/config/certs/private.crt
server.ssl.key: /data/es/kibana/config/certs/private.key
3 启动kibana
cd kibana/bin/
./kibana &
service文件
vim /usr/lib/systemd/system/kibana.service
[Unit]
Description=kibana server daemon
After=network.target
[Service]
User=elastic
Group=elastic
ExecStart=/bin/bash -c "exec /data/es/kibana/bin/kibana"
ExecReload=/bin/kill -HUP $MAINPID
ExecStop=/bin/kill -SIGINT $MAINPID
KillMode=process
#Restart=always
Restart=on-failure
RestartSec=42s
[Install]
WantedBy=multi-user.target
4 访问kibana
x.x.x.x:port
(三)部署logstast
1 上传包
cd /data/es
wget -c https://artifacts.elastic.co/downloads/logstash/logstash-7.1.1.tar.gz
tar -xvf logstash-7.1.1.tar.gz
mv logstash-7.1.1/ logstash
mkdir /data/es/logstash/logs
chown elastic -R /data/es/
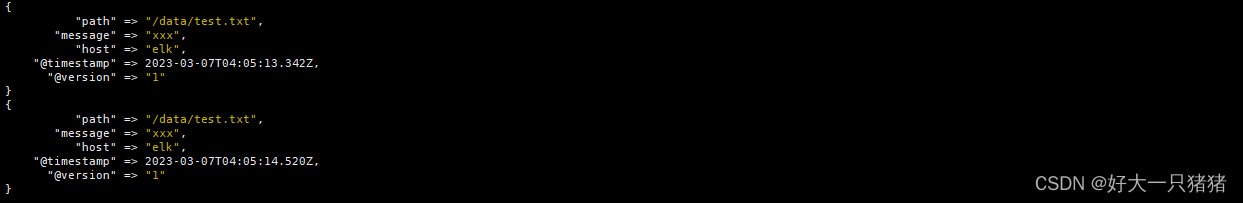
2 编辑pipelines.yml,mall.conf文件(演示)
vim /data/es/logstash/config/pipelines.yml
- pipeline.id: mall
pipeline.workers: 1 #CPU内核数
pipeline.output.workers: 1 #CPU内核数,这个配置可能会诱发报错。注释掉
pipeline.batch.size: 1000 # 每次发送的事件数
pipeline.batch.delay: 5 # 发送延时
path.config: "/data/es/logstash/config/mall.conf"
vim /data/es/logstash/config/mall.conf
input {
file {
path => "/data/test.txt"
}
}
filter {
}
output {
stdout { }
}
针对 Beats 输入插件,将 logstash.key 转换为 PKCS#8 格式
openssl pkcs8 -in logstash.key -topk8 -nocrypt -out logstash.pkcs8.key
input {
beats {
port => 5044
ssl => true
ssl_certificate_authorities => ["/data/es/logstash/config/certs/CA-certificate.crt"]
ssl_certificate => "/data/es/logstash/config/certs/private.crt"
ssl_key => "/data/es/logstash/config/certs/private.pkcs8.key"
#ssl_verify_mode => "force_peer"
ssl_verify_mode => "peer"
#Logstash server 是否验证 Filebeat client 证书。
#有效值有 peer 或 force_peer。如果是 force_peer,
#表示如果 Filebeat 没有提供证书,Logstash server 就会关闭连接。
include_codec_tag => false
#kibana每个文档中都有该tag“beats_input_codec_plain_applied”
client_inactivity_timeout => 36000
#通过修改配置 添加client_inactivity_timeout => 36000,filebeat偶尔连不上logstash
}
}
filter {
if "mall" in [tags] {
dissect {
mapping => {
"[log][file][path]" => "/%{}/%{}/%{}/%{}/%{ject}/%{}/%{}/%{rank}/%{}"
}
}
}
}
output {
if "dev" in [tags] {
elasticsearch {
hosts => ["elk:9200"]
index => "dev-%{rank}-%{ject}-%{+YYYY.MM.dd}"
ssl => true
cacert => "/data/es/logstash/config/certs/CA-certificate.crt"
user => "xxx"
password => "xxx"
}
}
}
yml文件。
node.name: elk
path.data: /data/es/logstash/data
#http.host: "192.168.1.241"
http.port: 9700
path.logs: /data/es/logstash/logs
#path.config: /home/logstash/logstash-7.5.1/config/conf/*.conf
xpack.monitoring.enabled: true
#xpack.monitoring.elasticsearch.username: logstash_system
#xpack.monitoring.elasticsearch.password: TBQOrC23OjbivKfqonMg
xpack.monitoring.elasticsearch.hosts: ["https://172.16.0.1:9200"]
xpack.monitoring.elasticsearch.ssl.certificate_authority: "/data/es/logstash/config/certs/CA-certificate.crt"
3 启动logstash
su - elastic -s /bin/bash -c "/data/es/logstash/bin/logstash &"
service文件
vim /usr/lib/systemd/system/logstash.service
[Unit]
Description=logstash server daemon
After=network.target
[Service]
User=elastic
Group=elastic
ExecStart=/bin/bash -c "/data/es/logstash/bin/logstash"
ExecReload=/bin/kill -HUP $MAINPID
ExecStop=/bin/kill -SIGINT $MAINPID
KillMode=process
#Restart=always
Restart=on-failure
RestartSec=42s
[Install]
WantedBy=multi-user.target
4 向文件中输入内容测试
(四)使用filebeat收集日志
filebeat --> logstash -->elasticsearch
1 上传filebeat包
cd /data/es
wget -c https://artifacts.elastic.co/downloads/beats/filebeat/filebeat-7.1.1-linux-x86_64.tar.gz
tar -xvf filebeat-7.1.1-linux-x86_64.tar.gz
mv filebeat-7.1.1-linux-x86_64 filebeat
vim filebeat/filebeat.yml
filebeat.inputs:
- type: log
enabled: true
paths:
- /data/logs/*/*.log
tags: ["mall","dev"]
filebeat.config.modules:
path: ${path.config}/modules.d/*.yml
setup.template.settings:
index.number_of_shards: 1
output.logstash:
hosts: ["logstash:5044"]
#output.console:
# pretty: true
compression: gzip
max_message_bytes: 1000000
loadlance: true #logstash负载均衡配置
ssl.certificate_authorities: ["/home/beats/filebeat-7.5.1/certs/ca.crt"]
ssl.certificate: "/home/beats/filebeat-7.5.1/certs/filebeat.crt"
ssl.key: "/home/beats/filebeat-7.5.1/certs/filebeat.key
processors:
- drop_fields:
fields: ["agent","ecs","input","type"]
./filebeat -e -c filebeat.yml
service文件
[Unit]
Description=filebeat server daemon
After=network.target
[Service]
User=elastic
Group=elastic
Environment="BEAT_CONFIG_OPTS= -e -c /data/es/filebeat/filebeat.yml"
ExecStart=/data/es/filebeat/filebeat $BEAT_CONFIG_OPTS
ExecReload=/bin/kill -HUP $MAINPID
ExecStop=/bin/kill -SIGINT $MAINPID
KillMode=process
#Restart=always
Restart=on-failure
RestartSec=42s
[Install]
WantedBy=multi-user.target





















 451
451











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








