介绍
lldap是一个轻量级的身份验证服务器,它提供了一个简化的 LDAP 接口来进行身份验证。更多请参考: openLdap
安装lldap
version: "3.7"
services:
lldap:
image: nitnelave/lldap:latest
container_name: lldap
ports:
# For LDAP
- "3890:3890"
# For the web front-end
- "17170:17170"
volumes:
- "./lldap_data:/data"
# Alternatively, you can mount a local folder
# - "./lldap_data:/data"
environment:
- UID=1001
- GID=1001
- TZ=Asia/Shanghai
# jwt
- LLDAP_JWT_SECRET=dDVuWtnaSeWt974j
- LLDAP_LDAP_USER_PASS=admin123 # 登录密码
# 以域名test.com为例: dc=test,db=com
- LLDAP_LDAP_BASE_DN=dc=test,db=com
networks:
application:
aliases:
- lldap
networks:
application:
name: commons
driver: bridge
lldap web
访问地址 http://192.168.0.1:17170
lldap 用户列表

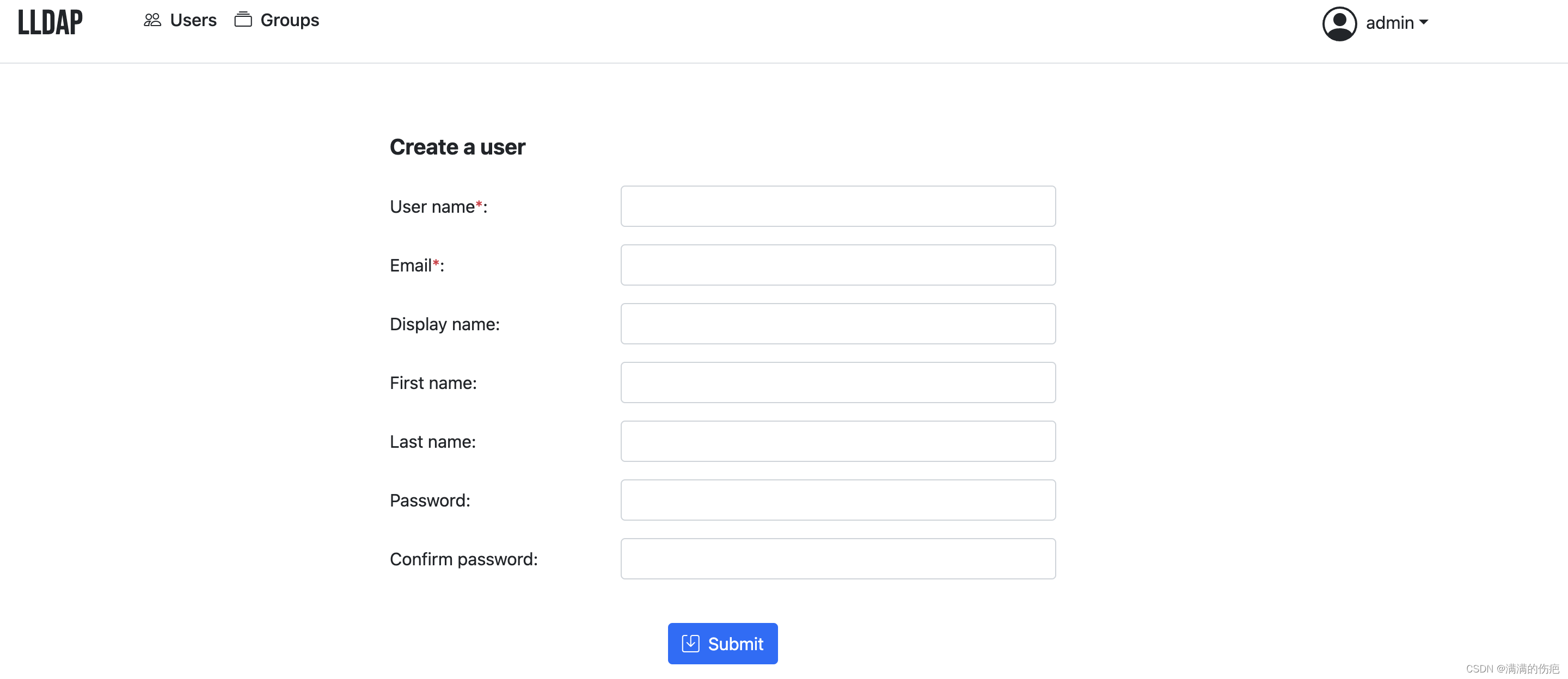
lldap 创建用户
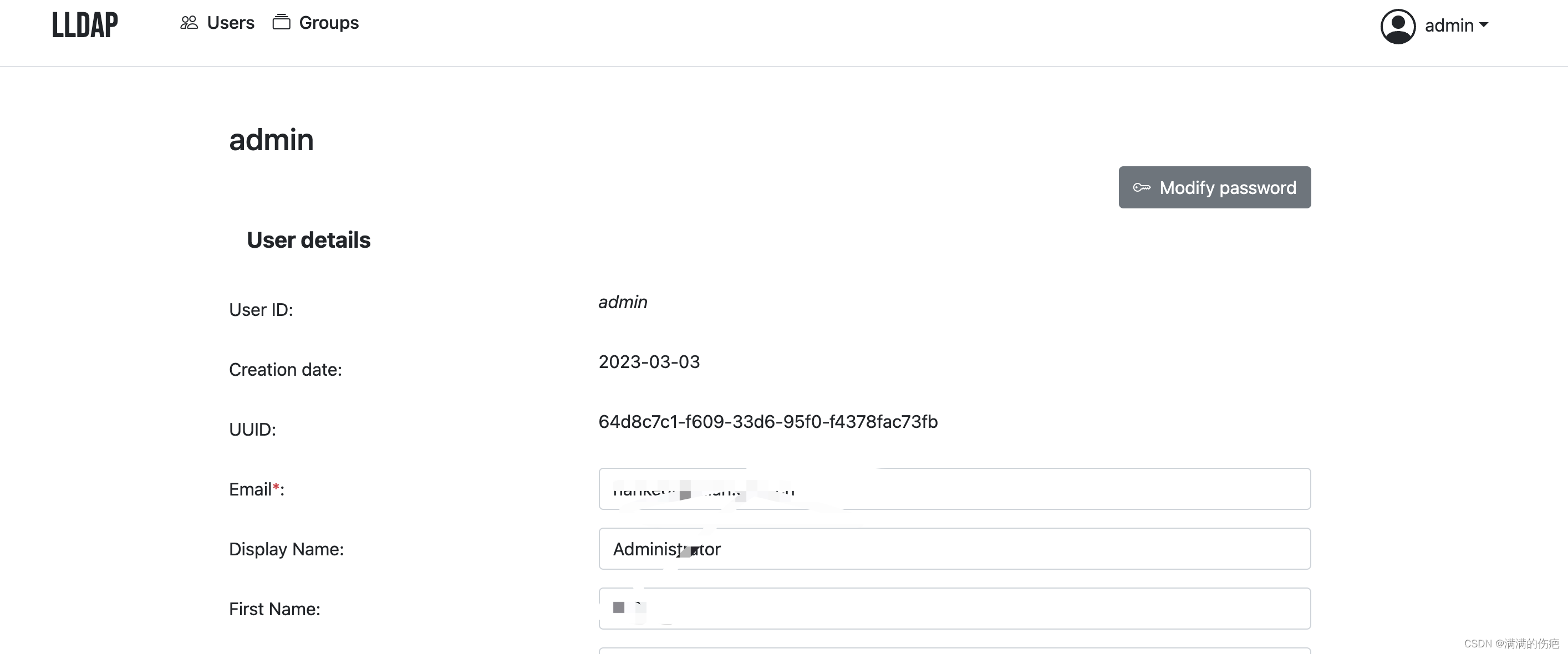
lldap 个人信息,可以修改密码
和Jenkins对接
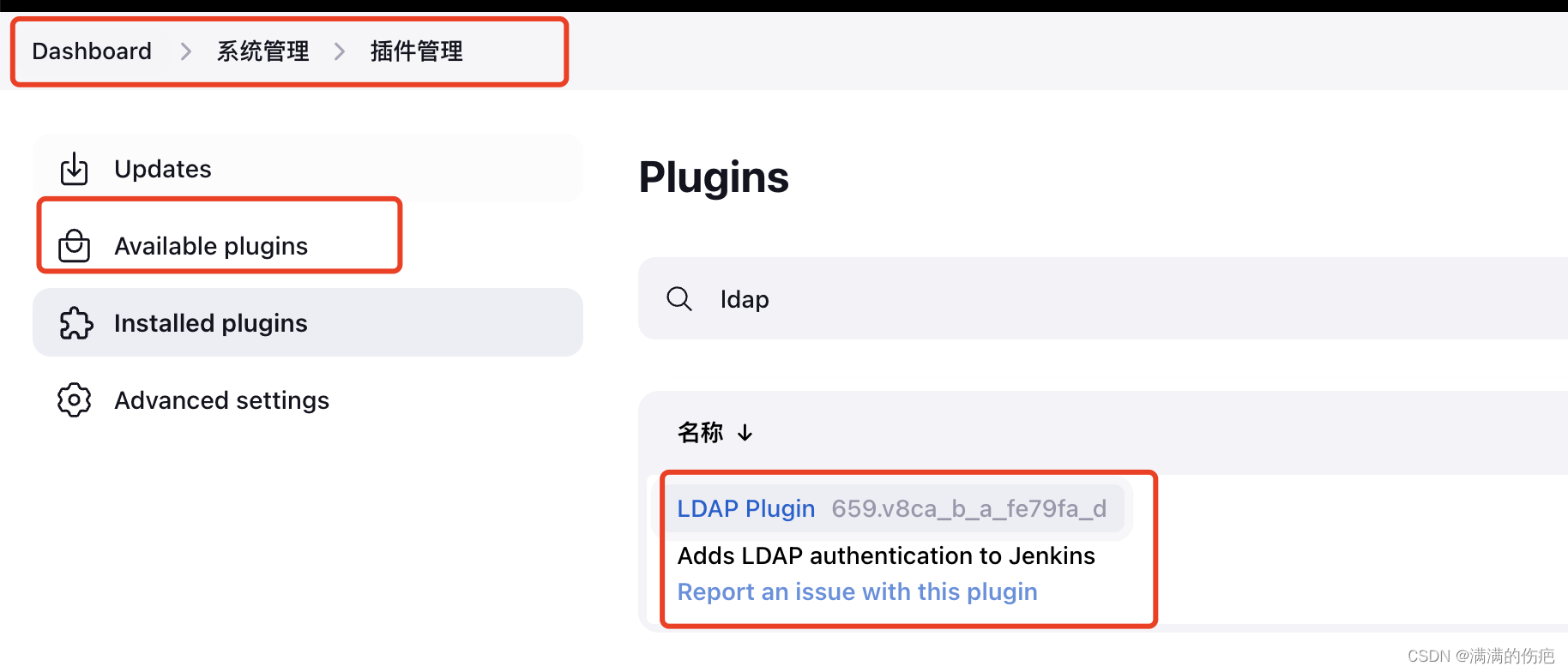
1、安装ldap插件(Jenkins LDAP Plugin)
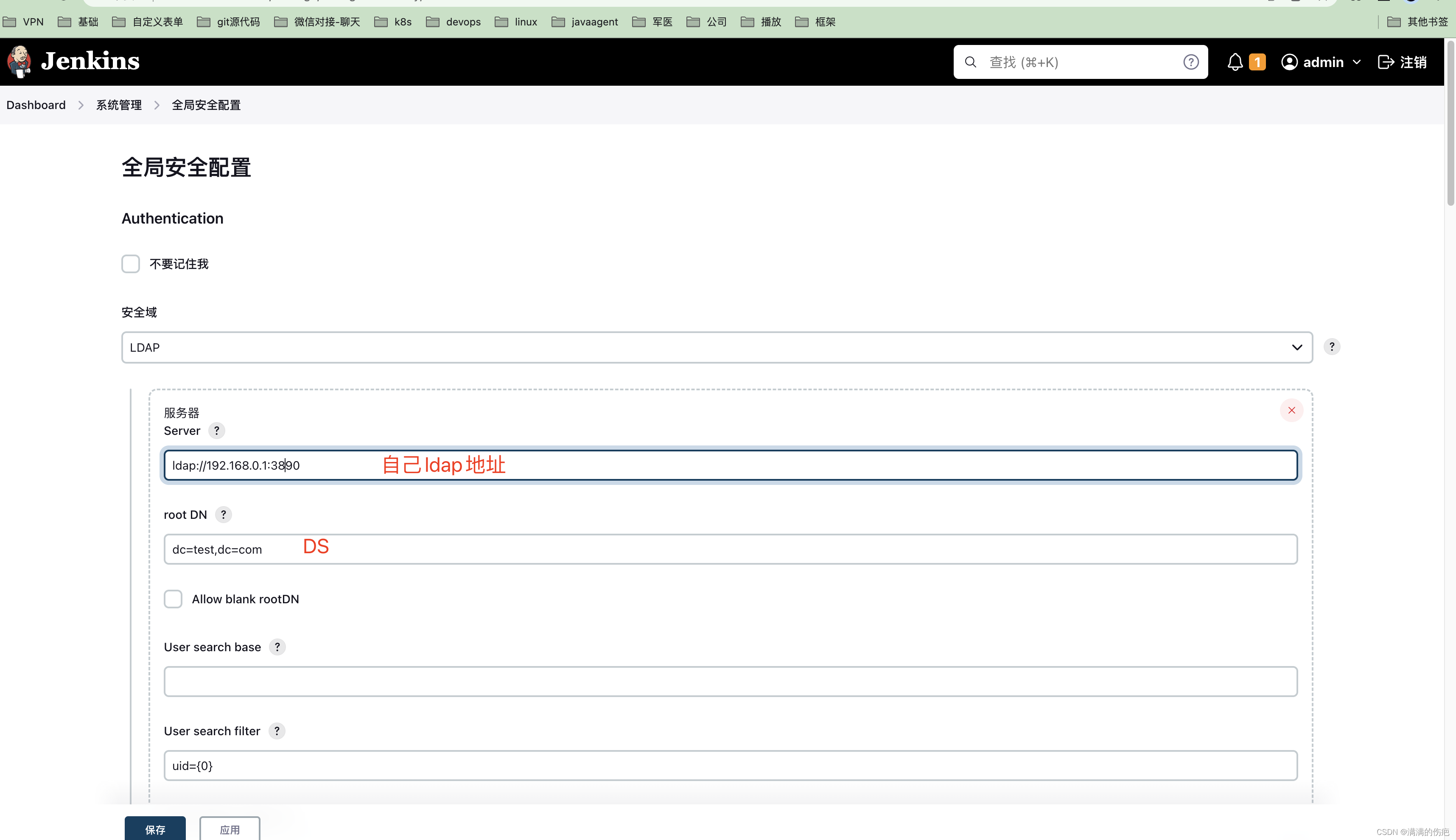
1、Jenkins ldap使用
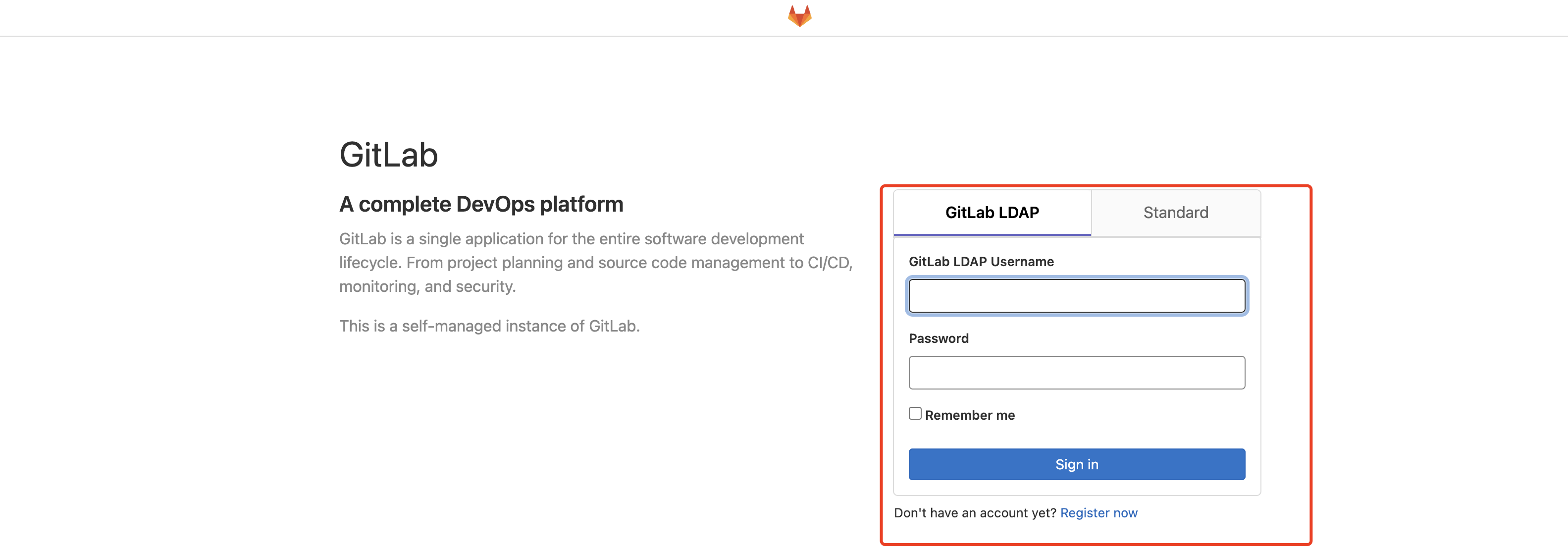
和gitlab对接
version: '3.7'
services:
gitlab:
image: 'gitlab/gitlab-ce:latest'
hostname: 'gitlab.test.com'
container_name: gitlab
environment:
GITLAB_OMNIBUS_CONFIG: |
external_url 'https://gitlab.test.com'
gitlab_rails['time_zone'] = 'Asia/Shanghai'
nginx['listen_port'] = 443
nginx['redirect_http_to_https'] = true
nginx['ssl_certificate'] = "/etc/ssl/certs/gitlab/9295742__test.com.pem"
nginx['ssl_certificate_key'] = "/etc/ssl/certs/gitlab/9295742__test.com.key"
nginx['ssl_protocols'] = "TLSv1.1 TLSv1.2 TLSv1.3"
# Add any other gitlab.rb configuration options if desired
# start ldap
gitlab_rails['ldap_enabled'] = true
gitlab_rails['ldap_servers'] = {
'main' => {
'label' => 'GitLab LDAP',
'host' => '192.168.0.1',
'port' => 3890,
'uid' => 'uid',
'bind_dn' => 'uid=admin,ou=people,dc=test,dc=com',
'password' => 'admin123',
'timeout' => 10,
'active_directory' => false,
'allow_username_or_email_login' => false,
'block_auto_created_users' => false,
'encryption' => 'plain',
'base' => 'dc=test,dc=com',
'user_filter' => ''
}
}
ports:
- '443:443'
- '222:22'
volumes:
- './data/gitlab/config:/etc/gitlab'
- './data/gitlab/logs:/var/log/gitlab'
- './data/gitlab/data:/var/opt/gitlab'
- './data/ssl:/etc/ssl/certs/gitlab:rw'
shm_size: '256m'
privileged: true
user: root
restart: always
networks:
application:
aliases:
- jenkins
gitlab-runner:
image: gitlab/gitlab-runner:latest
container_name: gitlab-runner
privileged: true
user: root
restart: always
volumes:
- './data/runner/config:/etc/gitlab-runner'
- /var/run/docker.sock:/var/run/docker.sock
- /bin/docker:/bin/docker
depends_on:
- gitlab
extra_hosts:
- "gitlab.test.com:192.168.0.1"
networks:
application:
aliases:
- gitlab-runner
networks:
application:
name: commons
driver: bridge
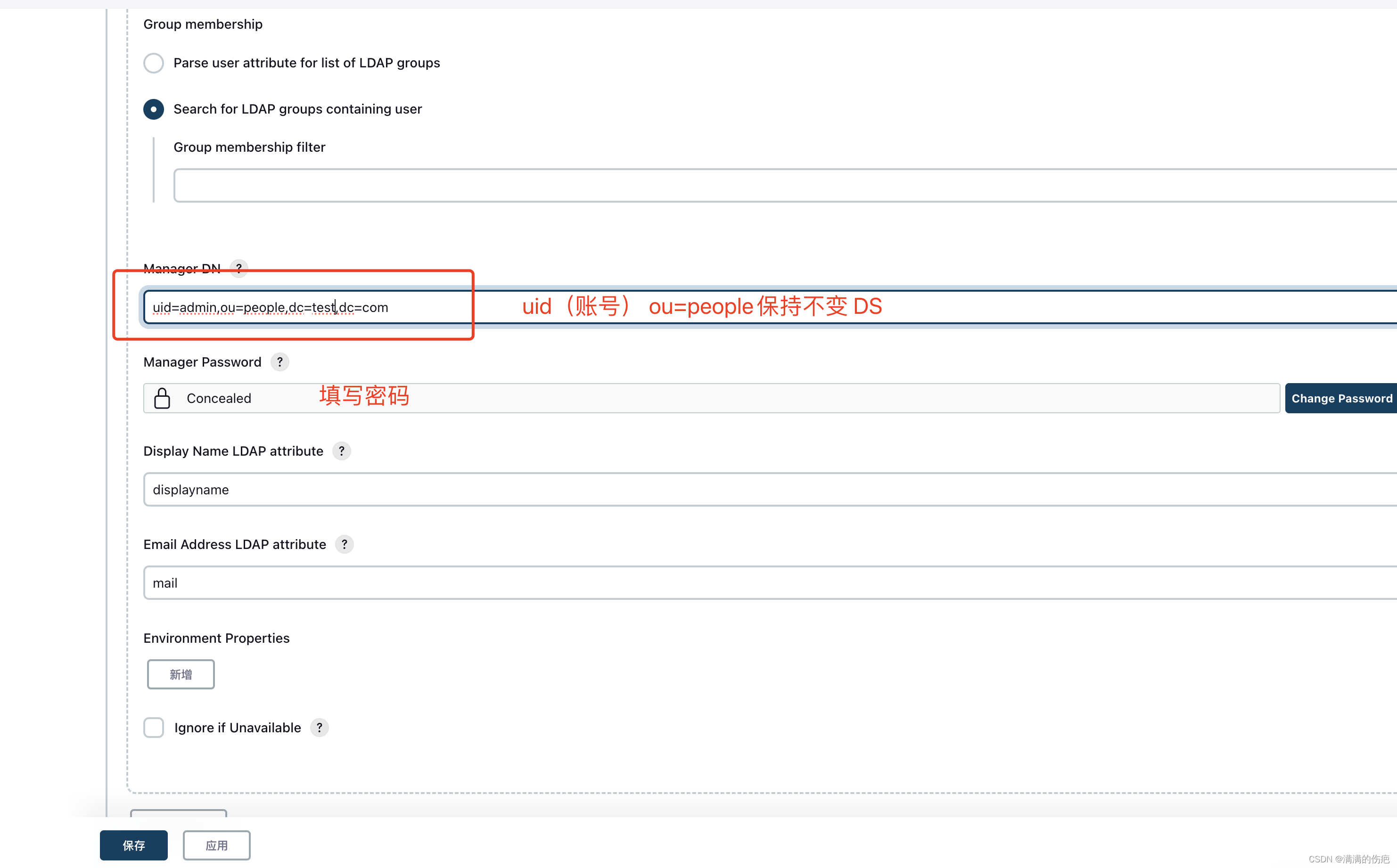
具体如下图
java 代码测试
package com.xxx.ldap;
import javax.naming.AuthenticationException;
import javax.naming.CommunicationException;
import javax.naming.Context;
import javax.naming.directory.Attributes;
import javax.naming.ldap.InitialLdapContext;
import javax.naming.ldap.LdapContext;
import java.util.Hashtable;
public class LdapContextTest {
public void test(){
try {
LdapContext ldapConnection = getLDAPConnection();
Attributes people = ldapConnection.getAttributes("uid=hankeqi,ou=people,dc=bjingling,dc=com");
System.out.println(people);
}catch (Exception e){
String message = e.getMessage();
//[LDAP: error code 49 - Invalid Credentials]
e.printStackTrace();
}
}
/**
* 获取默认LDAP连接 * Exception 则登录失败,ctx不为空则登录成功
*
* @return void
*/
public static LdapContext getLDAPConnection() throws AuthenticationException, CommunicationException, Exception {
//LDAP 连接地址 ldap://IP:PORT (default port 389)
String LDAP_URL = "ldap://192.168.0.1:3890";
//LDAP SSL连接地址 ldaps://IP:PORT (default port 636)
//(这个用起来比较麻烦,目前知道管理员改密码必须使用SSL)
String LDAP_SSL_URL = "";
//用户名
String userAccount = "admin";
//用户密码
String userPassword = "admin123";
// 方式1
// 基于姓名(cn),此cn为Display Name,部门有同名就麻烦了
//userAccount = "cn=xxx,OU=xxx,DC=xxx,DC=com";
// 方式2
// 基于Account User Logon name:
// userAccount = "xxx@domain.xxx";
// 方式3
// 基于Account User Logon name(pre-windows 2000):
// userAccount = "domain\\xxx"
// 基于登录名(uid (User ID)与 unix 的 uid 完全不同)(请注意objectSID,此处尝试失败)
//uid=zhangsan,ou=users,
userAccount = "uid=admin,ou=people,dc=test,dc=com";
userPassword = "admin123";
Hashtable<String, String> HashEnv = new Hashtable<String, String>();
HashEnv.put(Context.SECURITY_AUTHENTICATION, "simple"); // LDAP访问安全级别(none,simple,strong)
HashEnv.put(Context.SECURITY_PRINCIPAL, userAccount); //AD的用户名
HashEnv.put(Context.SECURITY_CREDENTIALS, userPassword); //AD的密码
HashEnv.put(Context.INITIAL_CONTEXT_FACTORY, "com.sun.jndi.ldap.LdapCtxFactory"); // LDAP工厂类
HashEnv.put("com.sun.jndi.ldap.connect.timeout", "3000");//连接超时设置为3秒
HashEnv.put("com.sun.jndi.ldap.read.timeout", "30000");//连接超时设置为30秒
HashEnv.put(Context.PROVIDER_URL, LDAP_URL);
return new InitialLdapContext(HashEnv, null);
}
}
























 565
565











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








