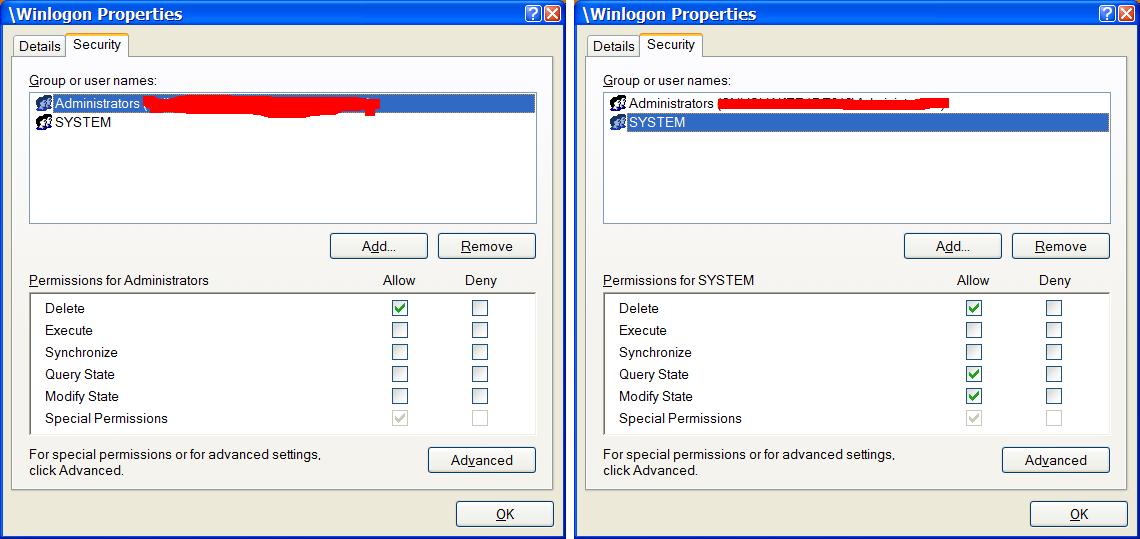
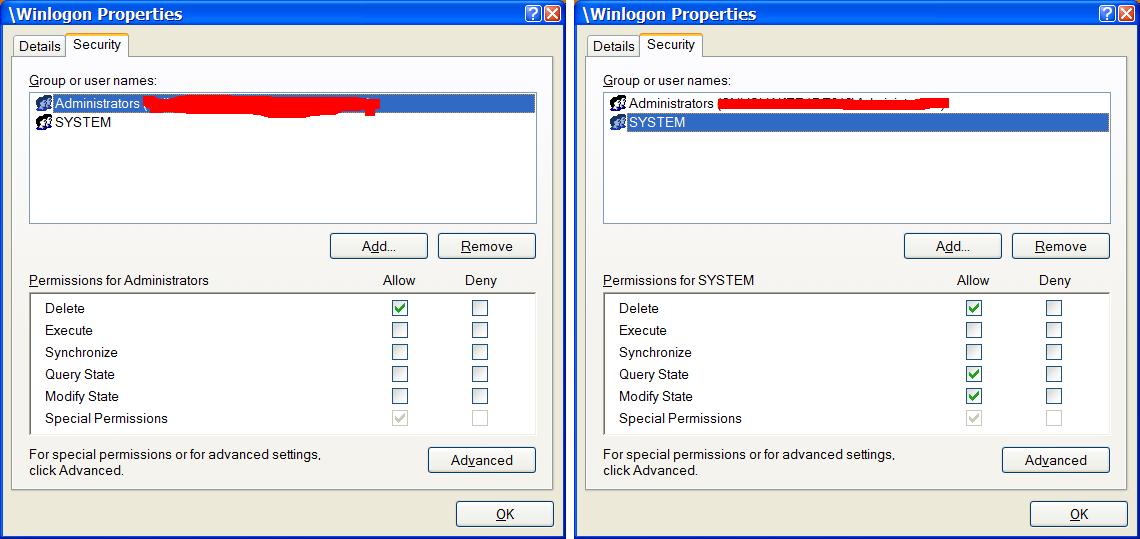
前面说在系统登陆桌面运行程序必须取得TCB特权,今天研究了一下,这话说的有点儿绝对了。在网上搜索了一下,大名鼎鼎的Phrack上的有一篇文章介绍如何操作Physical Memory给了我启发。问题的关键不在于TCB特权,而在于ADMIN帐号没有权限操作"\Winlogon"内核对象。从下面这张图可以看出SYSTEM帐号和ADMIN帐号在"\Winlogon"内核对象上的权限区别:
那么在"\Winlogon"内核对象上给ADMIN帐号加上相应的访问权限是不是就可以了呢?答案是肯定的。添加权限的代码如下:
 BOOLGrantAccessRights(HANDLEhWinlogonDesktop)
BOOLGrantAccessRights(HANDLEhWinlogonDesktop)

 ...
{
...
{
 PACLOldDacl=NULL,NewDacl=NULL;
PACLOldDacl=NULL,NewDacl=NULL;
 PSECURITY_DESCRIPTORSecDesc=NULL;
PSECURITY_DESCRIPTORSecDesc=NULL;
 EXPLICIT_ACCESSAccess;
EXPLICIT_ACCESSAccess;
 BOOLretval=FALSE;
BOOLretval=FALSE;

 DWORDRes=GetSecurityInfo(
hWinlogonDesktop
,SE_KERNEL_OBJECT,
DWORDRes=GetSecurityInfo(
hWinlogonDesktop
,SE_KERNEL_OBJECT,
 DACL_SECURITY_INFORMATION,NULL,NULL,&OldDacl,
DACL_SECURITY_INFORMATION,NULL,NULL,&OldDacl,
 NULL,&SecDesc);
NULL,&SecDesc);

 if(Res!=ERROR_SUCCESS)
if(Res!=ERROR_SUCCESS)
 returnFALSE;
returnFALSE;

 Access.grfAccessPermissions=ACTRL_PERM_1|ACTRL_PERM_2;
Access.grfAccessPermissions=ACTRL_PERM_1|ACTRL_PERM_2;
 Access.grfAccessMode=GRANT_ACCESS;
Access.grfAccessMode=GRANT_ACCESS;
 Access.grfInheritance=NO_INHERITANCE;
Access.grfInheritance=NO_INHERITANCE;
 Access.Trustee.MultipleTrusteeOperation=NO_MULTIPLE_TRUSTEE;
Access.Trustee.MultipleTrusteeOperation=NO_MULTIPLE_TRUSTEE;
 //changetheseinformationstograntaccesstoagrouporotheruser
//changetheseinformationstograntaccesstoagrouporotheruser

 Access.Trustee.TrusteeForm=TRUSTEE_IS_NAME;
Access.Trustee.TrusteeForm=TRUSTEE_IS_NAME;
 Access.Trustee.TrusteeType=TRUSTEE_IS_USER;
Access.Trustee.TrusteeType=TRUSTEE_IS_USER;
 Access.Trustee.ptstrName="CURRENT_USER";
Access.Trustee.ptstrName="CURRENT_USER";

 //createthenewACL
//createthenewACL

 if(ERROR_SUCCESS!=SetEntriesInAcl(1,&Access,OldDacl,&NewDacl))
if(ERROR_SUCCESS!=SetEntriesInAcl(1,&Access,OldDacl,&NewDacl))
 gotocleanup;
gotocleanup;

 //updateACL
//updateACL

 retval=ERROR_SUCCESS==SetSecurityInfo(
hWinlogonDesktop
,SE_KERNEL_OBJECT,
retval=ERROR_SUCCESS==SetSecurityInfo(
hWinlogonDesktop
,SE_KERNEL_OBJECT,
 DACL_SECURITY_INFORMATION,NULL,NULL,NewDacl,
DACL_SECURITY_INFORMATION,NULL,NULL,NewDacl,
 NULL);
NULL);

 cleanup:
cleanup:
 if(NewDacl)
if(NewDacl)
 LocalFree(NewDacl);
LocalFree(NewDacl);
 if(SecDesc)
if(SecDesc)
 LocalFree(SecDesc);
LocalFree(SecDesc);
 returnretval;
returnretval;
 }
}

那么在"\Winlogon"内核对象上给ADMIN帐号加上相应的访问权限是不是就可以了呢?答案是肯定的。添加权限的代码如下:
 BOOLGrantAccessRights(HANDLEhWinlogonDesktop)
BOOLGrantAccessRights(HANDLEhWinlogonDesktop)
 ...
{
...
{ PACLOldDacl=NULL,NewDacl=NULL;
PACLOldDacl=NULL,NewDacl=NULL; PSECURITY_DESCRIPTORSecDesc=NULL;
PSECURITY_DESCRIPTORSecDesc=NULL; EXPLICIT_ACCESSAccess;
EXPLICIT_ACCESSAccess; BOOLretval=FALSE;
BOOLretval=FALSE;
 DWORDRes=GetSecurityInfo(
hWinlogonDesktop
,SE_KERNEL_OBJECT,
DWORDRes=GetSecurityInfo(
hWinlogonDesktop
,SE_KERNEL_OBJECT, DACL_SECURITY_INFORMATION,NULL,NULL,&OldDacl,
DACL_SECURITY_INFORMATION,NULL,NULL,&OldDacl, NULL,&SecDesc);
NULL,&SecDesc);
 if(Res!=ERROR_SUCCESS)
if(Res!=ERROR_SUCCESS) returnFALSE;
returnFALSE;
 Access.grfAccessPermissions=ACTRL_PERM_1|ACTRL_PERM_2;
Access.grfAccessPermissions=ACTRL_PERM_1|ACTRL_PERM_2; Access.grfAccessMode=GRANT_ACCESS;
Access.grfAccessMode=GRANT_ACCESS; Access.grfInheritance=NO_INHERITANCE;
Access.grfInheritance=NO_INHERITANCE; Access.Trustee.MultipleTrusteeOperation=NO_MULTIPLE_TRUSTEE;
Access.Trustee.MultipleTrusteeOperation=NO_MULTIPLE_TRUSTEE; //changetheseinformationstograntaccesstoagrouporotheruser
//changetheseinformationstograntaccesstoagrouporotheruser
 Access.Trustee.TrusteeForm=TRUSTEE_IS_NAME;
Access.Trustee.TrusteeForm=TRUSTEE_IS_NAME; Access.Trustee.TrusteeType=TRUSTEE_IS_USER;
Access.Trustee.TrusteeType=TRUSTEE_IS_USER; Access.Trustee.ptstrName="CURRENT_USER";
Access.Trustee.ptstrName="CURRENT_USER";
 //createthenewACL
//createthenewACL
 if(ERROR_SUCCESS!=SetEntriesInAcl(1,&Access,OldDacl,&NewDacl))
if(ERROR_SUCCESS!=SetEntriesInAcl(1,&Access,OldDacl,&NewDacl)) gotocleanup;
gotocleanup;
 //updateACL
//updateACL
 retval=ERROR_SUCCESS==SetSecurityInfo(
hWinlogonDesktop
,SE_KERNEL_OBJECT,
retval=ERROR_SUCCESS==SetSecurityInfo(
hWinlogonDesktop
,SE_KERNEL_OBJECT, DACL_SECURITY_INFORMATION,NULL,NULL,NewDacl,
DACL_SECURITY_INFORMATION,NULL,NULL,NewDacl, NULL);
NULL);
 cleanup:
cleanup: if(NewDacl)
if(NewDacl) LocalFree(NewDacl);
LocalFree(NewDacl); if(SecDesc)
if(SecDesc) LocalFree(SecDesc);
LocalFree(SecDesc); returnretval;
returnretval; }
}





















 1万+
1万+

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








