cocos creator2.4.5有效
支持对web平台和native平台进行加密,支持对文件名进行混淆。
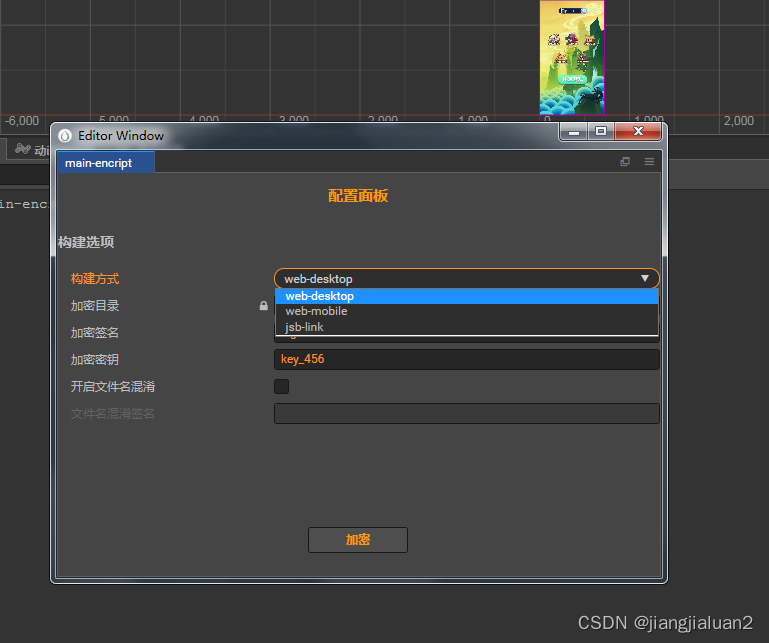
如图
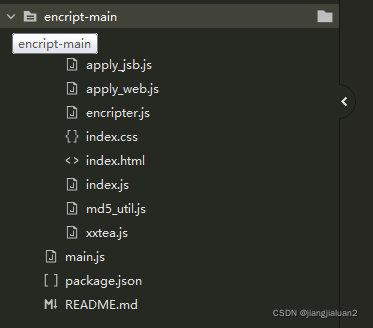
代码列表 :
web端
加密思路:不破坏原有工程,构建后修改导出的cocos2d-js.js文件,主要是修改有三点,解密代码放在downloadArrayBuffer,修改downloadText和downloadImage,改为通过downloadArrayBuffer先下载二进制流再解密解码为文本或图片。
var downloadArrayBuffer = function downloadArrayBuffer(url, options, onComplete) {
options.responseType = "arraybuffer";
url = _getRealPath(url)
downloadFile(url, options, options.onFileProgress, function (err,data) {
if(!err){
///解密
data = MainEnc._decriptTool.decodeArrayBuffer(data);
}
onComplete&&onComplete(err,data)
});
}
如上,主要是downloadArrayBuffer进行解密,另一个要注意的就是下载图片要手动转化一下。
加密解密使用的xxtea,代码如下:
encodeArrayBuffer(arrbuf, sign = this.encriptSign, key = this.encriptKey) {
Editor.log("11");
Editor.log(arrbuf);
Editor.log("22");
if (this.checkIsEncripted(arrbuf, sign)) {
return
}
let buffer = new Uint8Array(arrbuf);
let bufferStr = this.Uint8ArrayToString(buffer);
let enbufferStr = XXTEA.encryptToBase64(bufferStr, sign);
let enBuffer = this.stringToUint8Array(enbufferStr);
let signBuf = new Uint8Array(this.strToBytes(sign));
Editor.log("11");
Editor.log(signBuf);
Editor.log("12");
let _outBuffer = new ArrayBuffer(signBuf.length + enBuffer.length);
let outBuffer = new Uint8Array(_outBuffer);
for (let i = 0; i < signBuf.length; i++) {
outBuffer[i] = signBuf[i]
}
for (let i = 0; i < enBuffer.length; i++) {
outBuffer[signBuf.length + i] = enBuffer[i]
}
Editor.log(outBuffer);
return outBuffer;
}
decodeArrayBuffer(arrbuf, sign = this.encriptSign, key = this.encriptKey) {
if (!this.checkIsEncripted(arrbuf, sign)) {
return arrbuf;
}
let signBuf = new Uint8Array(this.strToBytes(sign));
let buffer = new Uint8Array(arrbuf);
let size = buffer.length - signBuf.length;
let _outArrBuf = new ArrayBuffer(size)
let outBuffer = new Uint8Array(_outArrBuf)
for (let i = 0; i < size; i++) {
outBuffer[i] = buffer[signBuf.length + i];
}
let enArrBufStr = this.Uint8ArrayToString(outBuffer);
let deArrBufStr=XXTEA.decryptFromBase64(enArrBufStr,sign);
let outBuffer2=this.stringToUint8Array(deArrBufStr);
return outBuffer2;
}
至于文件名混淆,就是对源uuid格式的文件名和一个混淆签名再次进行md5,得到新文件名。
如aaaa-bbbb-cccc-dddd.png变为1111-2222-3333-4444.png
关键是工程中如何识别新文件名。项目运行时,查找文件是根据文件路径查到uuid再组装成url的,我们只需要在url组装后,再按照我们的混淆规则,再算一次就好了,保险起见,只混淆uuid格式的文件名。native模式下,修改jsb-engine.js的transformUrl,对本地url进行再次转换;web模式下,downloadArrayBuffer里直接在下载之前将url转换成混淆后的文件名。
需要的可以加群聊一起讨论:

参考链接:https://www.jianshu.com/p/43ad9b4a4eb5





















 2255
2255











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








