Linux系统TCP连接数的限制
1. 操作系统级别限制(一般是够用的,主要是下面的第2项):查看看Linux系统对同时打开文件数的硬限制和端口限制
1.1 查看Linux系统对同时打开文件数的硬限制:sysctl -a|grep file-max
[root@localhost ~]# sysctl -a|grep file-max
fs.file-max = 173080
sysctl: reading key "net.ipv6.conf.all.stable_secret"
sysctl: reading key "net.ipv6.conf.default.stable_secret"
sysctl: reading key "net.ipv6.conf.ens33.stable_secret"
sysctl: reading key "net.ipv6.conf.lo.stable_secret"
sysctl: reading key "net.ipv6.conf.virbr0.stable_secret"
sysctl: reading key "net.ipv6.conf.virbr0-nic.stable_secret"
[root@localhost ~]#
1.2 端口限制: 默认值 [32768,60999], 3 万左右个客户端连接,当作客户端测试的时候,需要大量的端口
cat /proc/sys/net/ipv4/ip_local_port_range
[dd ~]$ cat /proc/sys/net/ipv4/ip_local_port_range
32768 60999
解决:
- 编辑 vim /etc/sysctl.conf
- 追加记录
fs.nr_open=2000000
fs.file-max=2000000
net.ipv4.ip_local_port_range = 1024 65535 - 立即生效 sysctl -p
[root@localhost ~]# vim /etc/sysctl.conf
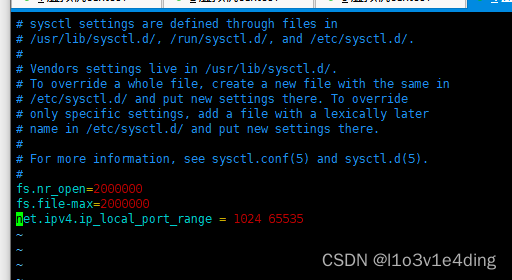
[root@localhost ~]# sysctl -p
2. 用户级别限制:查看Linux系统用户最大打开文件软限制
查看Linux系统用户最大打开文件限制:ulimit -n
[dd ~]$ ulimit -n
1024
解决:
- 编辑 /etc/security/limits.conf
- 追加记录
* soft nofile 600000
* hard nofile 600000 - 设置开机运行: sysctl --system
[root@localhost ~]# vim /etc/security/limits.conf
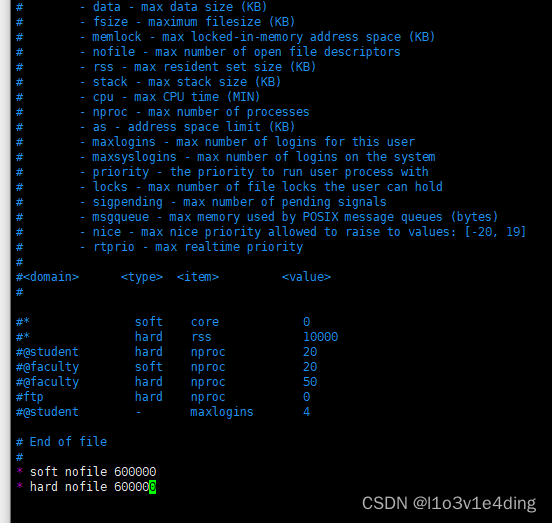
[root@localhost ~]# sysctl --system
* Applying /usr/lib/sysctl.d/00-system.conf ...
* Applying /usr/lib/sysctl.d/10-default-yama-scope.conf ...
kernel.yama.ptrace_scope = 0
* Applying /usr/lib/sysctl.d/50-default.conf ...
kernel.sysrq = 16
kernel.core_uses_pid = 1
kernel.kptr_restrict = 1
net.ipv4.conf.default.rp_filter = 1
net.ipv4.conf.all.rp_filter = 1
net.ipv4.conf.default.accept_source_route = 0
net.ipv4.conf.all.accept_source_route = 0
net.ipv4.conf.default.promote_secondaries = 1
net.ipv4.conf.all.promote_secondaries = 1
fs.protected_hardlinks = 1
fs.protected_symlinks = 1
* Applying /usr/lib/sysctl.d/60-libvirtd.conf ...
fs.aio-max-nr = 1048576
* Applying /etc/sysctl.d/99-sysctl.conf ...
fs.nr_open = 2000000
fs.file-max = 2000000
net.ipv4.ip_local_port_range = 1024 65535
* Applying /etc/sysctl.conf ...
fs.nr_open = 2000000
fs.file-max = 2000000
net.ipv4.ip_local_port_range = 1024 65535
[root@localhost ~]#
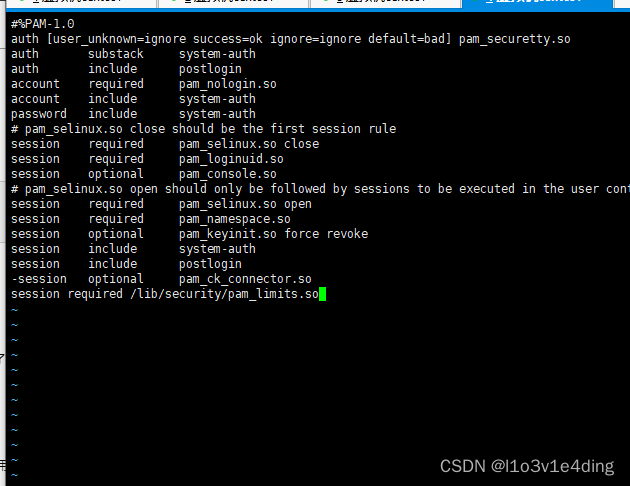
3. 用户完成系统登录后使用这些限制值
- 编辑 vi /etc/pam.d/login
- 追加记录 session required /lib/security/pam_limits.so
[root@localhost ~]# vi /etc/pam.d/login























 456
456











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








