一、源码包及环境准备
CentOS 7.X 系统的主机
openssh-8.4p1.tar.gz openssh的源码包
二、装包修改配置文件
创建对应的文件目录:
#mkdir -p /home/malico/rpmbuild/{SOURCES,SPECS,RPMS,SRPMS,BUILD,BUILDROOT}
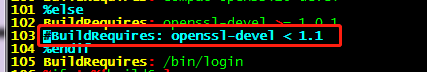
安装源码编译及依赖包:
# yum install gcc gcc-c++ glibc glibc-devel openssl-devel openssl prce pcre-devel zlib zlib-devel make wget krb5-devel pam-devel libX11-devel xmkmf libXt-devel initscripts libXt-devel imake gtk2-devel
安装制作rpm包工具
#yum install -y rpm-build.x86_64
#cp openssh-8.4p1.tar.gz /home/malico/rpmbuild/SOURCES/
#tar -xzf openssh-8.4p1.tar.gz ##openssh-8.4p1.tar.gz 源文件包不要删除,后面有用到;
#cp /home/malico/rpmbuild/SOURCES/openssh-8.4p1/contrib/redhat/openssh.spec /home/malico/rpmbuild/SPECS/
#vim /home/malico/rpmbuild/SPECS/openssh.spec
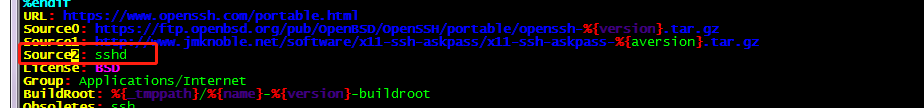
要找一个sshd文件模板,
#cp /etc/pam.d/sshd /home/malico/rpmbuild/SOURCES/
配置文件修改完毕,下面是所有的修改内容可cp,
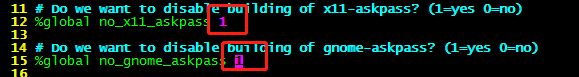
%global no_x11_askpass 1
%global no_gnome_askpass 1
Source2: sshd
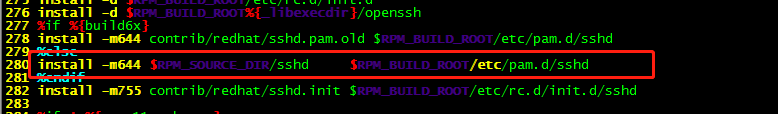
install -m644 $RPM_SOURCE_DIR/sshd $RPM_BUILD_ROOT/etc/pam.d/sshd
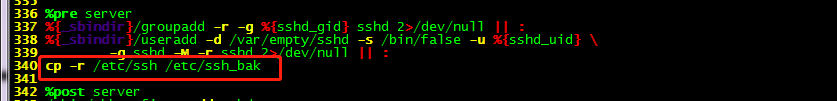
cp -r /etc/ssh /etc/ssh_bak
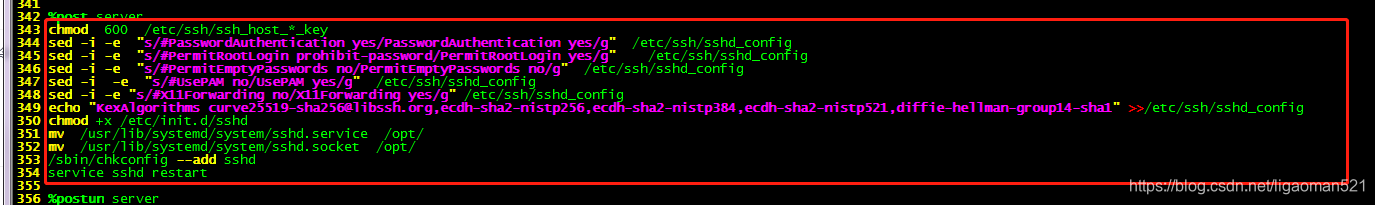
chmod 600 /etc/ssh/ssh_host_*_key
sed -i -e "s/#PasswordAuthentication yes/PasswordAuthentication yes/g" /etc/ssh/sshd_config
sed -i -e "s/#PermitRootLogin prohibit-password/PermitRootLogin yes/g" /etc/ssh/sshd_config
sed -i -e "s/#PermitEmptyPasswords no/PermitEmptyPasswords no/g" /etc/ssh/sshd_config
sed -i -e "s/#UsePAM no/UsePAM yes/g" /etc/ssh/sshd_config
sed -i -e "s/#X11Forwarding no/X11Forwarding yes/g" /etc/ssh/sshd_config
echo "KexAlgorithms curve25519-sha256@libssh.org,ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group14-sha1" >>/etc/ssh/sshd_config
chmod +x /etc/init.d/sshd
mv /usr/lib/systemd/system/sshd.service /opt/
mv /usr/lib/systemd/system/sshd.socket /opt/
/sbin/chkconfig --add sshd
service sshd restart
三、构建rpm包
为安全起见用普通用户操作,
#chown -R malico:malico /home/malico/rpmbuild
#su - malico
#cd /home/malico/rpmbuild/SPECS/
#rpmbuild -bb openssh.spec
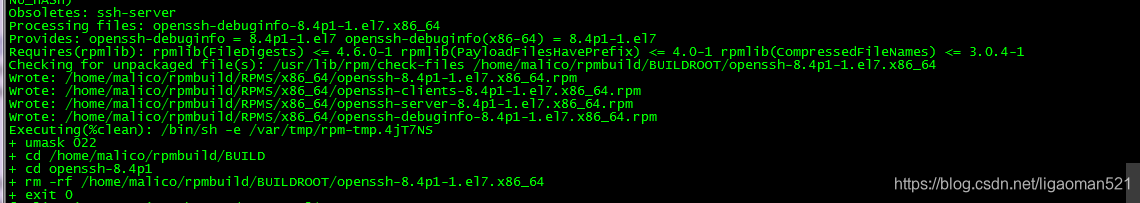
到此处恭喜,已生成想要的rpm包,
#cd /home/malico/rpmbuild/RPMS/x86_64
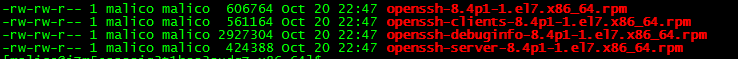
四、升级openssh
#su - root
#rpm -Uvh openssh-8.4p1-1.el7.x86_64.rpm openssh-clients-8.4p1-1.el7.x86_64.rpm openssh-server-8.4p1-1.el7.x86_64.rpm
推荐:配置sshd_config文件
HostKey /etc/ssh/ssh_host_dsa_key
HostKey /etc/ssh/ssh_host_rsa_key
HostKey /etc/ssh/ssh_host_ecdsa_key
HostKey /etc/ssh/ssh_host_ed25519_key
SyslogFacility AUTHPRIV
PermitRootLogin yes
AuthorizedKeysFile .ssh/authorized_keys
PasswordAuthentication yes
PermitEmptyPasswords no
UsePAM yes
X11Forwarding yes
#UsePrivilegeSeparation sandbox # Default for new installations.
AcceptEnv LANG LC_CTYPE LC_NUMERIC LC_TIME LC_COLLATE LC_MONETARY LC_MESSAGES
AcceptEnv LC_PAPER LC_NAME LC_ADDRESS LC_TELEPHONE LC_MEASUREMENT
AcceptEnv LC_IDENTIFICATION LC_ALL LANGUAGE
AcceptEnv XMODIFIERS
Subsystem sftp /usr/libexec/openssh/sftp-server
KexAlgorithms curve25519-sha256@libssh.org,ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group14-sha1
注:为安全起见,做好后手准备,安装一个telnet 或者 多打开链接几个标签。
稳!!!
报错1、/etc/pam.d/sshd 文件内容有变化
# systemctl status sshd
● sshd.service - SYSV: OpenSSH server daemon
....
Aug 14 15:30:34 VM_167_123_centos sshd[915241]: PAM unable to dlopen(/usr/lib64/security/pam_stack.so): /usr/lib64/security/pam_stack.so: cannot open shared object file: No such file or directory
Aug 14 15:30:34 VM_167_123_centos sshd[915241]: PAM adding faulty module: /usr/lib64/security/pam_stack.so
Aug 14 15:30:34 VM_167_123_centos sshd[915241]: fatal: Access denied for user root by PAM account configuration [preauth]
解决方法:
恢复/etc/pam.d/sshd文件内容,重启sshd服务即可
cat /etc/pam.d/sshd
#%PAM-1.0
auth required pam_sepermit.so
auth substack password-auth
auth include postlogin
# Used with polkit to reauthorize users in remote sessions
-auth optional pam_reauthorize.so prepare
account required pam_nologin.so
account include password-auth
password include password-auth
# pam_selinux.so close should be the first session rule
session required pam_selinux.so close
session required pam_loginuid.so
# pam_selinux.so open should only be followed by sessions to be executed in the user context
session required pam_selinux.so open env_params
session required pam_namespace.so
session optional pam_keyinit.so force revoke
ession include password-auth
session include postlogin
# Used with polkit to reauthorize users in remote sessions
-session optional pam_reauthorize.so prepare






















 4432
4432











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








