使用ida打开程序,找到main函数:
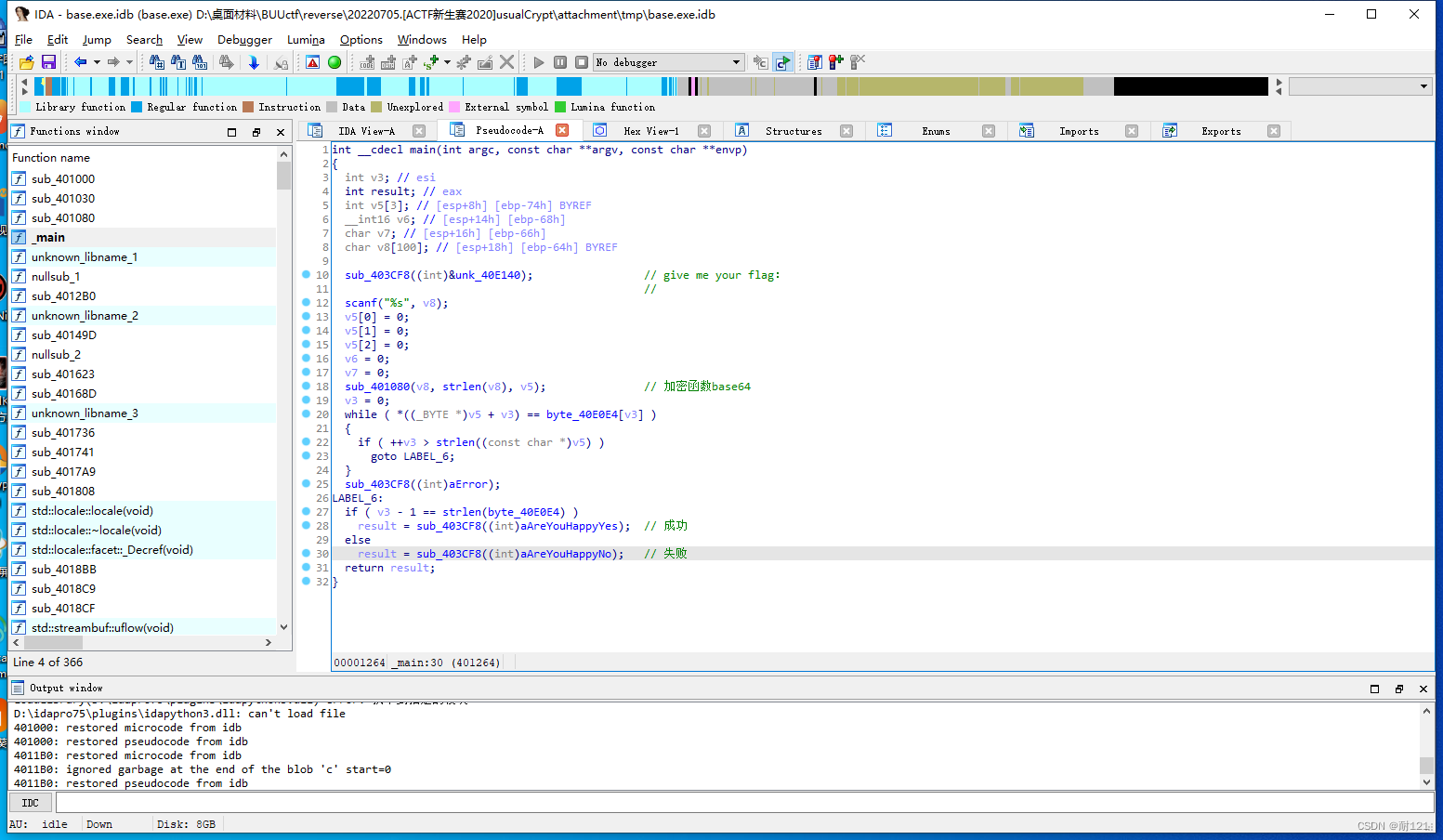
观察发现:
sub_403CF8()是输出函数。
sub_401080()是关键加密函数。
while循环是比较操作,byte_40E0E4存放了加密后的密文,长度未知。
导出密文数据:
c = 'zMXHz3TIgnxLxJhFAdtZn2fFk3lYCrtPC2l9'
进入关键加密函数,观察:
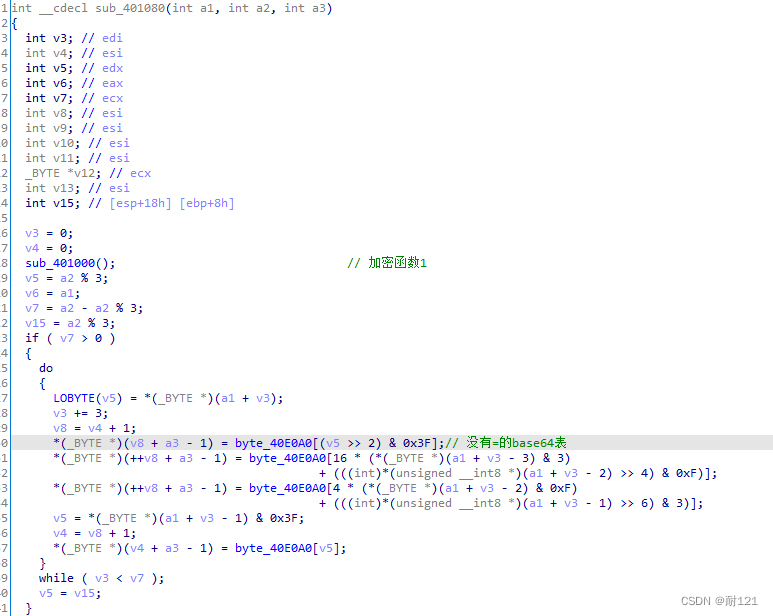
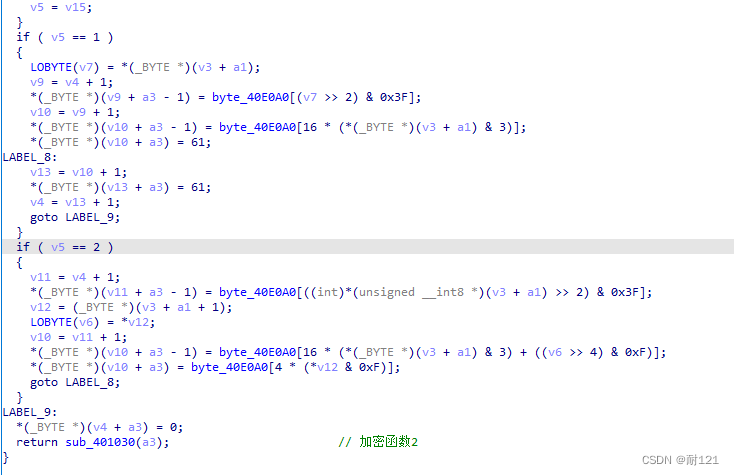
分析出flag经过加密函数1->变异的base64加密->加密函数2得到密文。
逆向过程:
先分析加密函数2sub_401030():
ida中有宏定义#define HIDWORD(x) (((_DWORD)&(x)+1))
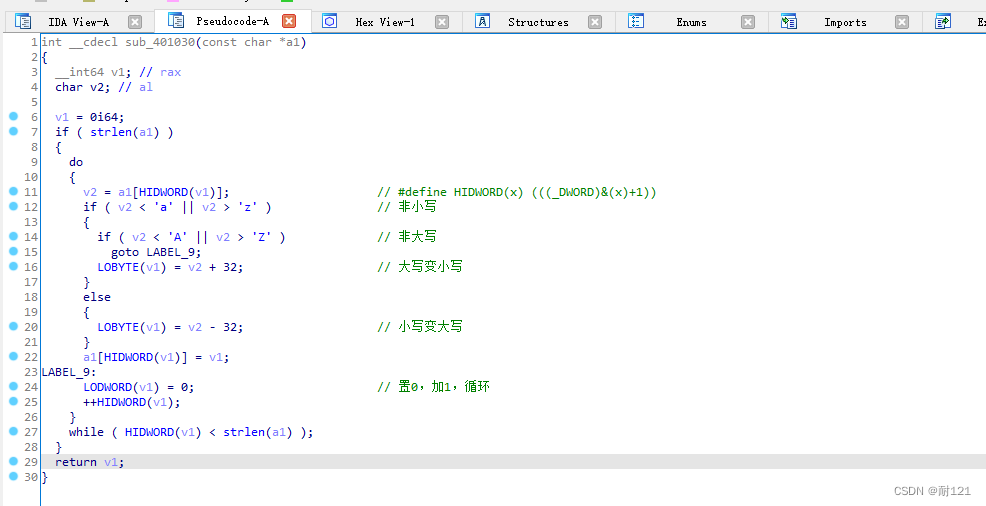
将密文的大写字母变小写,小写字母变大写。
解密脚本:
if __name__ == '__main__':
c = 'zMXHz3TIgnxLxJhFAdtZn2fFk3lYCrtPC2l9'
m = ''
for i in c:
if 'Z'>=i>='A':
m += chr(ord(i)+32)
elif 'z' >= i >= 'a':
m += chr(ord(i) - 32)
else:
m += i
print(m)ZmxhZ3tiGNXlXjHfaDTzN2FfK3LycRTpc2L9
也可以使用函数:
if __name__ == '__main__':
c = 'zMXHz3TIgnxLxJhFAdtZn2fFk3lYCrtPC2l9'
m = c.swapcase()查看加密函数1:
发现改变了base64的表:
仿写加密函数1:
for i in range(6,15):
v1 = base64list[i + 10]
base64list[i+10]= base64list[i]
base64list[i]=v1
for i in range(len(base64list)):
print(chr(base64list[i]),end='')结果如下:
ABCDEFQRSTUVWXYPGHIJKLMNOZabcdefghijklmnopqrstuvwxyz0123456789+/
使用新的表进行base解密即可,完整代码:
import base64
if __name__ == '__main__':
c = 'zMXHz3TIgnxLxJhFAdtZn2fFk3lYCrtPC2l9'
m = ''
for i in c:
if 'Z'>=i>='A':
m += chr(ord(i)+32)
elif 'z' >= i >= 'a':
m += chr(ord(i) - 32)
else:
m += i
base64list=[ 65, 66, 67, 68, 69, 70, 71, 72, 73, 74, 75, 76, 77, 78, 79, 80, 81, 82, 83, 84, 85, 86, 87, 88, 89, 90, 97, 98, 99, 100, 101, 102, 103, 104, 105, 106, 107, 108, 109, 110, 111, 112, 113, 114, 115, 116, 117, 118, 119, 120, 121, 122, 48, 49, 50, 51, 52, 53, 54, 55, 56, 57, 43, 47]
base64list0='ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/'
base64list1 = ''
for i in range(6,15):
v1 = base64list[i + 10]
base64list[i+10]= base64list[i]
base64list[i]=v1
for i in range(len(base64list)):
base64list1 += chr(base64list[i])
print(base64.b64decode(m.translate(str.maketrans(base64list1, base64list0))))flag{bAse64_h2s_a_Surprise}























 536
536











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








