简介
日志系统是每个公司都会使用的一套系统,小编在参考官方和网络上的资源后,手把手教你搭建一套具备生产环境使用的日志集群。
整个文章由于内容太长,分成5篇完成,时间会较长请大家耐心阅读,特别是配置文件中的注释信息。
目录:
手把手教你搭建Kafka(带SASL认证)+ELK集群 - 二
手把手教你搭建Kafka(带SASL认证)+ELK集群 - 三
手把手教你搭建Kafka(带SASL认证)+ELK集群 - 四
手把手教你搭建Kafka(带SASL认证)+ELK集群 - 五
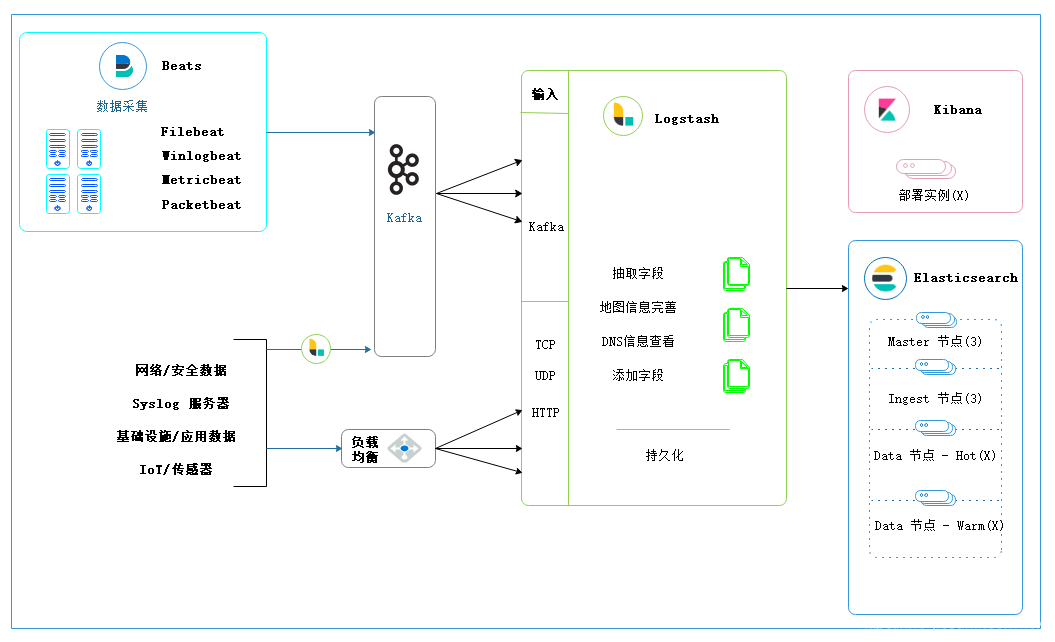
部署架构
整体日志系统以ELK Stack为基础,整合Kafka作为缓存层,即可以对爆发的日志量进行削峰,也可以保护后端的日志集群。整套架构包含Beats,Logstash,ElasticSearch,Kibana,Kafka,Kafka-Eagle(管理kafka集群的可视化工具)架构图如下:
文件准备
- Zookeeper
- Logstash
- Filebeat
- Elasticsearch
- Kibana
- Kafka
- Kafka-Eagle
- JDK 1.8
所需的所有文件以及相关的配置文件下载地址如下:
链接:https://pan.baidu.com/s/1SW05azyq2gQsiGtL4hYP2g
提取码:wnga
资源准备
| 资源角色 | 资源配置 | 数量 | EIP地址(内部IP) | 备注 |
| Elasticsearch集群 | 32C128G 1T数据盘 操作系统: CentOS 7.6 | 3 | 10.228.82.9(10.10.0.160) | 小编使用的所有主机为云平台的主机,拥有EIP(弹性IP)和内部IP两个IP地址,用过公有云的同学应该比较容易理解 |
| Zookeeper+Kafka+Logstash集群 | 4C16G 500G数据盘 操作系统: CentOS 7.6 | 3 | 10.228.82.156(10.50.0.36) | 将3个组件复用到一起 |
| Kibana集群 | 2C4G 40G系统盘 操作系统: CentOS 7.6 | 1 | 10.228.82.83(10.50.0.197) | 与Kafka-Eagle资源复用 |
| Kafka-Eagle | 2C4G 40G系统盘 操作系统: CentOS 7.6 | 1 | 10.228.82.83(10.50.0.197) | 与Kibana资源复用 |
部署组件
1. 系统初始化
以下操作需要对所有节点进行
- 以root账号登录主机,在/etc/security/limits.conf文件中添加以下内容
* soft nofile 65535
* hard nofile 65535
- 在/etc/sysctl.conf文件中添加以下内容
vm.max_map_count=262144 - 是内核参数配置生效
[root@vm10-10-0-160 ~]# systemctl -p -
将数据盘格式化并挂载到/data目录
[root@ ~]#fdisk /dev/vdb [root@ ~]#mkfs.ext4 /dev/vdb1 [root@ ~]#mkdir -p /data && mount /dev/vdb1 /data [root@ ~]#vi /etc/fstab #将下面的内容添加到文件中 /dev/vdb1 /data ext4 defaults 0 0 -
安装Java环境,将下载的jdk-8u301-linux-x64.tar.gz文件上传到服务器中
[root@ ~]#tar -zxvf jdk-8u301-linux-x64.tar.gz -C /data/ [root@ ~]#vi /etc/profile,将下面的内容加入到文件中: export JAVA_HOME=/data/jdk1.8.0_301 export PATH=$PATH:$JAVA_HOME/bin -
重启服务器
2.部署Elasticsearch集群
以下的步骤需要在Elasticsearch集群的节点上执行
- 创建应用账号 elastic
useradd elastic - 将elasticsearch-7.14.0-linux-x86_64.tar.gz上传到服务器并解压到/data目录
tar -zxvf elasticsearch-7.14.0-linux-x86_64.tar.gz -C /data/ -
将文件目录的所有者切换为elastic用户
chown -R elastic:elastic /data/elasticsearch-7.14.0 - 创建elasticsearch的数据和日志目录
mkdir -p /data/esdata && mkdir -p /data/eslogs && chown -R elastic:elastic /data/esdata && chown -R elastic:elastic /data/eslogs - 生成ca 文件(该操作只需要在一个节点上完成),记得将ca证书添加密码保护
[root@elasticsearch-master-1 elasticsearch-7.14.0]# ./bin/elasticsearch-certutil ca This tool assists you in the generation of X.509 certificates and certificate signing requests for use with SSL/TLS in the Elastic stack. The 'ca' mode generates a new 'certificate authority' This will create a new X.509 certificate and private key that can be used to sign certificate when running in 'cert' mode. Use the 'ca-dn' option if you wish to configure the 'distinguished name' of the certificate authority By default the 'ca' mode produces a single PKCS#12 output file which holds: * The CA certificate * The CA's private key If you elect to generate PEM format certificates (the -pem option), then the output will be a zip file containing individual files for the CA certificate and private key Please enter the desired output file [elastic-stack-ca.p12]: Enter password for elastic-stack-ca.p12 : - 生成transport ssl 证书,用于节点内部的TLS加密,将步骤生成的文件(elastic-certificates.p12)分发到所有的节点/data/elasticsearch-7.14.0/config目录中,第一次输入的密码是CA证书的密码,就是上面一步设置的密码,第二次让输入密码,是设置transport证书的密码,我没有设置
[root@elasticsearch-master-1 elasticsearch-7.14.0]# ./bin/elasticsearch-certutil cert --ca elastic-stack-ca.p12 This tool assists you in the generation of X.509 certificates and certificate signing requests for use with SSL/TLS in the Elastic stack. The 'cert' mode generates X.509 certificate and private keys. * By default, this generates a single certificate and key for use on a single instance. * The '-multiple' option will prompt you to enter details for multiple instances and will generate a certificate and key for each one * The '-in' option allows for the certificate generation to be automated by describing the details of each instance in a YAML file * An instance is any piece of the Elastic Stack that requires an SSL certificate. Depending on your configuration, Elasticsearch, Logstash, Kibana, and Beats may all require a certificate and private key. * The minimum required value for each instance is a name. This can simply be the hostname, which will be used as the Common Name of the certificate. A full distinguished name may also be used. * A filename value may be required for each instance. This is necessary when the name would result in an invalid file or directory name. The name provided here is used as the directory name (within the zip) and the prefix for the key and certificate files. The filename is required if you are prompted and the name is not displayed in the prompt. * IP addresses and DNS names are optional. Multiple values can be specified as a comma separated string. If no IP addresses or DNS names are provided, you may disable hostname verification in your SSL configuration. * All certificates generated by this tool will be signed by a certificate authority (CA) unless the --self-signed command line option is specified. The tool can automatically generate a new CA for you, or you can provide your own with the --ca or --ca-cert command line options. By default the 'cert' mode produces a single PKCS#12 output file which holds: * The instance certificate * The private key for the instance certificate * The CA certificate If you specify any of the following options: * -pem (PEM formatted output) * -keep-ca-key (retain generated CA key) * -multiple (generate multiple certificates) * -in (generate certificates from an input file) then the output will be be a zip file containing individual certificate/key files Enter password for CA (elastic-stack-ca.p12) : #ca证书的密码 Please enter the desired output file [elastic-certificates.p12]: Enter password for elastic-certificates.p12 : #直接回车,不设置transport证书的密码 Certificates written to /data/ELK/elasticsearch-7.14.0/elastic-certificates.p12 This file should be properly secured as it contains the private key for your instance. This file is a self contained file and can be copied and used 'as is' For each Elastic product that you wish to configure, you should copy this '.p12' file to the relevant configuration directory and then follow the SSL configuration instructions in the product guide. For client applications, you may only need to copy the CA certificate and configure the client to trust this certificate. - 生成http ssl 证书用于Kibana的https访问,将压缩包里elasticsearch目录中的http.p12文件分发到所有的节点/data/elasticsearch-7.14.0/config中,kibana下的elasticsearch-ca.pem文件是用于kibana连接elasticsearch服务
[root@elasticsearch-master-1 elasticsearch-7.14.0]# ./bin/elasticsearch-certutil http ## Elasticsearch HTTP Certificate Utility The 'http' command guides you through the process of generating certificates for use on the HTTP (Rest) interface for Elasticsearch. This tool will ask you a number of questions in order to generate the right set of files for your needs. ## Do you wish to generate a Certificate Signing Request (CSR)? A CSR is used when you want your certificate to be created by an existing Certificate Authority (CA) that you do not control (that is, you don't have access to the keys for that CA). If you are in a corporate environment with a central security team, then you may have an existing Corporate CA that can generate your certificate for you. Infrastructure within your organisation may already be configured to trust this CA, so it may be easier for clients to connect to Elasticsearch if you use a CSR and send that request to the team that controls your CA. If you choose not to generate a CSR, this tool will generate a new certificate for you. That certificate will be signed by a CA under your control. This is a quick and easy way to secure your cluster with TLS, but you will need to configure all your clients to trust that custom CA. Generate a CSR? [y/N]n #是否创建CSR文件,选择n ## Do you have an existing Certificate Authority (CA) key-pair that you wish to use to sign your certificate? If you have an existing CA certificate and key, then you can use that CA to sign your new http certificate. This allows you to use the same CA across multiple Elasticsearch clusters which can make it easier to configure clients, and may be easier for you to manage. If you do not have an existing CA, one will be generated for you. Use an existing CA? [y/N]y #是否使用现成的CA,这个CA我们已经自己创建了,所以选择y ## What is the path to your CA? Please enter the full pathname to the Certificate Authority that you wish to use for signing your new http certificate. This can be in PKCS#12 (.p12), JKS (.jks) or PEM (.crt, .key, .pem) format. CA Path: /data/ELK/elasticsearch-7.14.0/elastic-stack-ca.p12 #填写ca文件的绝对路径 Reading a PKCS12 keystore requires a password. It is possible for the keystore's password to be blank, in which case you can simply press <ENTER> at the prompt Password for elastic-stack-ca.p12: #输入ca文件设置的保护密码 ## How long should your certificates be valid? Every certificate has an expiry date. When the expiry date is reached clients will stop trusting your certificate and TLS connections will fail. Best practice suggests that you should either: (a) set this to a short duration (90 - 120 days) and have automatic processes to generate a new certificate before the old one expires, or (b) set it to a longer duration (3 - 5 years) and then perform a manual update a few months before it expires. You may enter the validity period in years (e.g. 3Y), months (e.g. 18M), or days (e.g. 90D) For how long should your certificate be valid? [5y] 100y #证书的有效期,我设置的100年 ## Do you wish to generate one certificate per node? If you have multiple nodes in your cluster, then you may choose to generate a separate certificate for each of these nodes. Each certificate will have its own private key, and will be issued for a specific hostname or IP address. Alternatively, you may wish to generate a single certificate that is valid across all the hostnames or addresses in your cluster. If all of your nodes will be accessed through a single domain (e.g. node01.es.example.com, node02.es.example.com, etc) then you may find it simpler to generate one certificate with a wildcard hostname (*.es.example.com) and use that across all of your nodes. However, if you do not have a common domain name, and you expect to add additional nodes to your cluster in the future, then you should generate a certificate per node so that you can more easily generate new certificates when you provision new nodes. Generate a certificate per node? [y/N]n #是否为每个elasticsearch的节点生成单独的证书,选n ## Which hostnames will be used to connect to your nodes? These hostnames will be added as "DNS" names in the "Subject Alternative Name" (SAN) field in your certificate. You should list every hostname and variant that people will use to connect to your cluster over http. Do not list IP addresses here, you will be asked to enter them later. If you wish to use a wildcard certificate (for example *.es.example.com) you can enter that here. Enter all the hostnames that you need, one per line. When you are done, press <ENTER> once more to move on to the next step. elastic-master-1 #这里将elasticsearch集群的hostname,域名都配置上,也可以配置通配符域名 elastic-master-2 elastic-master-3 *.es.cecinvestment.com You entered the following hostnames. - elastic-master-1 - elastic-master-2 - elastic-master-3 - *.es.cecinvestment.com Is this correct [Y/n]y #确认信息,选y ## Which IP addresses will be used to connect to your nodes? If your clients will ever connect to your nodes by numeric IP address, then you can list these as valid IP "Subject Alternative Name" (SAN) fields in your certificate. If you do not have fixed IP addresses, or not wish to support direct IP access to your cluster then you can just press <ENTER> to skip this step. Enter all the IP addresses that you need, one per line. When you are done, press <ENTER> once more to move on to the next step. 10.228.82.9 #这里将elasticsearch集群的所以内部和外部IP都配置上,不然通过IP连接的时候会证书验证失败 10.228.82.232 10.228.82.36 10.10.0.160 10.10.0.135 10.10.0.196 You entered the following IP addresses. - 10.228.82.9 - 10.228.82.232 - 10.228.82.36 - 10.10.0.160 - 10.10.0.135 - 10.10.0.196 Is this correct [Y/n]y #确认信息 ## Other certificate options The generated certificate will have the following additional configuration values. These values have been selected based on a combination of the information you have provided above and secure defaults. You should not need to change these values unless you have specific requirements. Key Name: elastic-master-1 Subject DN: CN=elastic-master-1 Key Size: 2048 Do you wish to change any of these options? [y/N]n #是不是要修改,选n ## What password do you want for your private key(s)? Your private key(s) will be stored in a PKCS#12 keystore file named "http.p12". This type of keystore is always password protected, but it is possible to use a blank password. If you wish to use a blank password, simply press <enter> at the prompt below. Provide a password for the "http.p12" file: [<ENTER> for none] #默认证书名字就可以了 ## Where should we save the generated files? A number of files will be generated including your private key(s), public certificate(s), and sample configuration options for Elastic Stack products. These files will be included in a single zip archive. What filename should be used for the output zip file? [/data/ELK/elasticsearch-7.14.0/elasticsearch-ssl-http.zip] #证书文件产生的绝对路径 Zip file written to /data/ELK/elasticsearch-7.14.0/elasticsearch-ssl-http.zip - 在所有节点的/etc/hosts文件中添加以下记录,根据自己机器的IP地址进行调整
10.228.82.9 elastic-master-1
10.228.82.232 elastic-master-2
10.228.82.36 elastic-master-3
- 修改elasticsearch的配置文件(/data/elasticsearch-7.14.0/config/elasticsearch.yml),其中节点相关的信息,根据每个节点进行修改,node.name填写的是节点的hostname,每个节点名称不一样.
node.name: elastic-master-1 path.data: /data/esdata path.logs: /data/eslogs network.host: 0.0.0.0 http.port: 9200 discovery.seed_hosts: ["elastic-master-1","elastic-master-2","elastic-master-3"] cluster.initial_master_nodes: ["elastic-master-1","elastic-master-2","elastic-master-3"] xpack.security.enabled: true xpack.security.transport.ssl.enabled: true xpack.security.http.ssl.enabled: true xpack.security.http.ssl.keystore.path: http.p12 #这个文件是在生成的zip文件中解压出来的kibana目录里面的,后面kibana连接ES也是使用这个文件 xpack.security.transport.ssl.verification_mode: certificate xpack.security.transport.ssl.client_authentication: required xpack.security.transport.ssl.keystore.path: elastic-certificates.p12 xpack.security.transport.ssl.truststore.path: elastic-certificates.p12 - 将elasticsearch配置为系统服务,并跟随系统一起启动
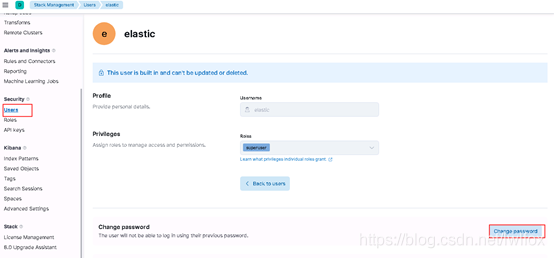
将下面的文件放入到/usr/lib/systemd/system/elasticsearch.service[Unit] Description=elasticsearch After=network.target [Service] Type=simple User=elastic Group=elastic LimitNOFILE=65535 LimitNPROC=65535 Restart=on-failure ExecStart=/data/elasticsearch-7.14.0/bin/elasticsearch [Install] WantedBy=multi-user.target - 修改系统内置默认账号密码,集群中默认会有apm_system,beats_system,elastic,kibana,kibana_system,logstash_system这些内置账号,
bin/elasticsearch-setup-passwords interactive -u https://elastic-master-1:9200 - Kibana在ES集群部署完成后就可以部署了, Kibana的部署步骤: https://blog.csdn.net/lwlfox/article/details/119803391
链接到下一篇






















 956
956











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








