- 从外部访问Service的第二种方式,适用于公有云上的Kubernetes服务。这时候可以指定一个LoadBalancer类型的Service
- 在Service提交后,Kubernetes就会调用CloudProvider在公有云上为你创建一个负载均衡服务,并且把代理的Pod的IP地址配置给负载均衡服务做后端。
[root@server2 ~]# kubectl edit configmaps -n kube-system kube-proxy

[root@server2 ~]# kubectl get pod -n kube-system |grep kube-proxy | awk '{system("kubectl delete pod "$1" -n kube-system")}'
[root@server2 ~]# mkdir metallb
[root@server2 ~]# cd metallb/
[root@server2 metallb]# wget https://raw.githubusercontent.com/metallb/metallb/v0.9.5/manifests/namespace.yaml
[root@server2 metallb]# wget https://raw.githubusercontent.com/metallb/metallb/v0.9.5/manifests/metallb.yaml
建立metall公共仓库

上传所需镜像
[root@server1 harbor]# docker pull metallb/controller:v0.9.5
[root@server1 harbor]# docker pull metallb/speaker:v0.9.5
[root@server1 harbor]# docker tag metallb/controller:v0.9.5 reg.westos.org/metallb/controller:v0.9.5
[root@server1 harbor]# docker push reg.westos.org/metallb/controller:v0.9.5
[root@server1 harbor]# docker tag metallb/speaker:v0.9.5 reg.westos.org/metallb/speaker:v0.9.5
[root@server1 harbor]# docker push reg.westos.org/metallb/speaker:v0.9.5

[root@server2 metallb]# kubectl apply -f namespace.yaml
[root@server2 metallb]# kubectl apply -f metallb.yaml
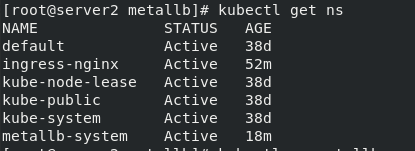
[root@server2 metallb]# kubectl get ns
[root@server2 metallb]# kubectl create secret generic -n metallb-system memberlist --from-literal=secretkey="$(openssl rand -base64 128)"
[root@server2 metallb]# kubectl -n metallb-system get secrets
[root@server2 metallb]# kubectl -n metallb-system get pod

[root@server2 metallb]# vim config.yaml
apiVersion: v1
kind: ConfigMap
metadata:
namespace: metallb-system
name: config
data:
config: |
address-pools:
- name: default
protocol: layer2
addresses:
- 192.168.3.100-192.168.3.200
[root@server2 metallb]# kubectl apply -f config.yaml
[root@server2 metallb]# vim nginx-svc.yml
---
apiVersion: v1
kind: Service
metadata:
name: nginx-svc
spec:
selector:
app: nginx
ports:
- protocol: TCP
port: 80
targetPort: 80
type: LoadBalancer
---
apiVersion: apps/v1
kind: Deployment
metadata:
name: deployment
spec:
replicas: 2
selector:
matchLabels:
app: nginx
template:
metadata:
labels:
app: nginx
spec:
containers:
- name: nginx
image: myapp:v1
[root@server2 metallb]# kubectl apply -f nginx-svc.yml
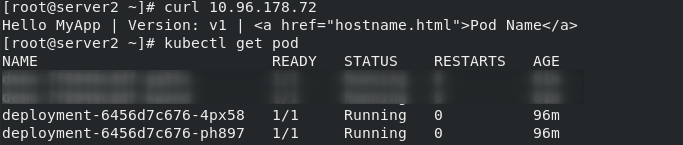
[root@server2 metallb]# kubectl get svc
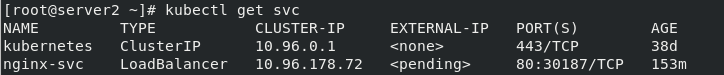
错误:EXTERNAL-IP理应分配的ip为192.168.3.100,可以通过外部主机访问
[root@server2 ~]# curl 10.96.178.72
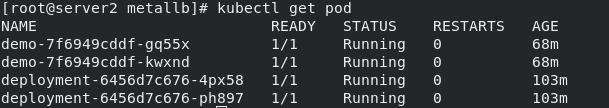
[root@server2 ~]# kubectl get pod
[root@server2 metallb]# vim demo-svc.yaml
---
apiVersion: v1
kind: Service
metadata:
name: demo-svc
spec:
selector:
app: demo
ports:
- protocol: TCP
port: 80
targetPort: 80
type: LoadBalancer
---
apiVersion: apps/v1
kind: Deployment
metadata:
name: demo
spec:
replicas: 2
selector:
matchLabels:
app: demo
template:
metadata:
labels:
app: demo
spec:
containers:
- name: demo
image: myapp:v2
[root@server2 metallb]# kubectl apply -f demo-svc.yaml
[root@server2 metallb]# kubectl get svc
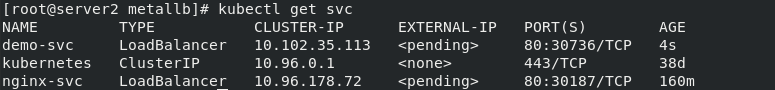
错误:EXTERNAL-IP处demo-svc理应分配的ip为192.168.3.101,可以通过外部主机访问
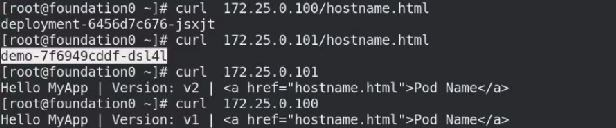
测试:
[root@westos ~]# curl 192.168.3.100
[root@westos ~]# curl 192.168.3.101
结果参考下图
2.
[root@server2 ~]# cd ingress/
[root@server2 ingress]# vim deploy.yaml
取消注释,做如下修改



[root@server2 ingress]# kubectl apply -f deploy.yaml
[root@server2 ingress]# kubectl -n ingress-nginx get all
[root@server2 ingress]# kubectl -n ingress-nginx delete daemonsets.apps ingress-nginx-controller

[root@server2 ingress]# kubectl -n ingress-nginx get pod
[root@server2 ingress]# kubectl -n ingress-nginx get svc
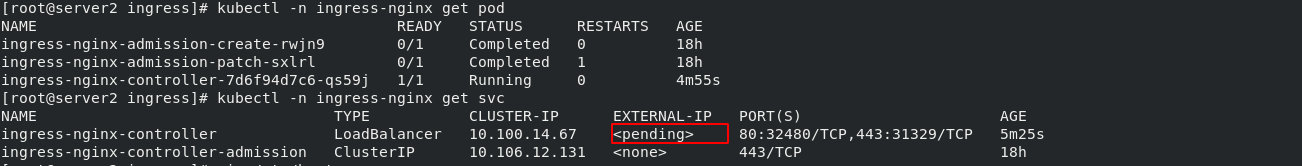
错误:红框此处应该为192.168.3.100
查看解析(双向)
[root@westos Desktop]# vim /etc/hosts

[root@server2 ingress]# kubectl get ingress
[root@server2 ingress]# kubectl delete -f nginx.yml

[root@server2 ingress]# vim demo.yml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-demo
spec:
#tls:
# - hosts:
# - www1.westos.org
# secretName: tls-secret
rules:
- host: www1.westos.org
http:
paths:
- path: /
backend:
serviceName: nginx-svc
servicePort: 80

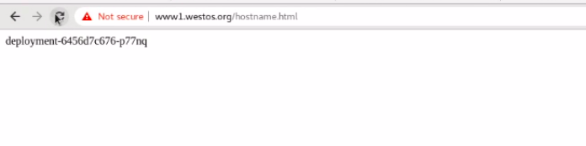
[root@server2 ingress]# kubectl apply -f demo.yml
[root@server2 ingress]# kubectl get svc
[root@server2 ingress]# kubectl get pod
[root@server2 ingress]# kubectl get ingress

[root@westos Desktop]# curl www1.westos.org
可以访问到
之前的加密有问题,重新作一次
[root@server2 ingress]# rm -rf tls.*
[root@server2 ingress]# openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.crt -subj "/CN=www1.westos.org/O=www1.westos.org"
[root@server2 ingress]# kubectl get secrets
[root@server2 ingress]# kubectl delete secrets tls-secret
[root@server2 ingress]# kubectl create secret tls tls-secret --key tls.key --cert tls.crt

[root@server2 ingress]# vim demo.yml

[root@server2 ingress]# kubectl apply -f demo.yml
[root@westos Desktop]# curl www1.westos.org -I























 481
481











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








