1、Shuffle
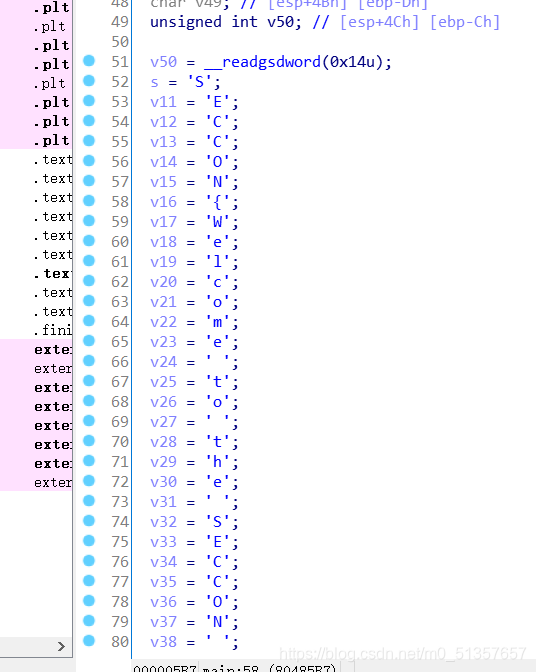
进入ida,按R,直接明文,shift+e提取出来,用C++转一下直接提交
2、666
输入的flag经过encode函数的变换后与enflag对比,相等即拿到flag

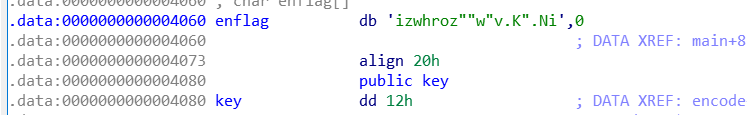
看一下encode,a1传入的是我们的输入,经过跟 key(0x12)的异或后存入a2,emmm也就是enflag
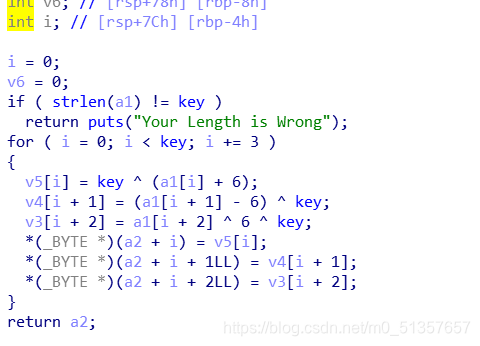
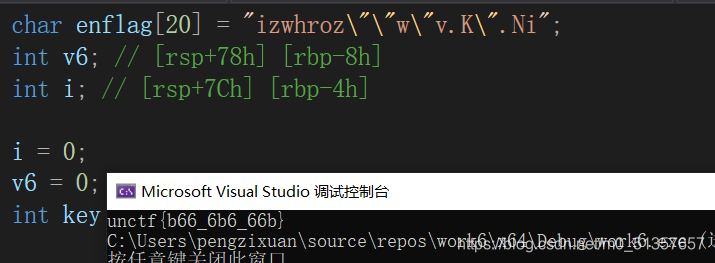
写一下脚本,因为运算优先级的问题,要记得加括号
#include<iostream>
#define _CRT_SECURE_NO_WARNINGS
using namespace std;
int main()
{
char enflag[20] = "izwhroz\"\"w\"v.K\".Ni";
int v6; // [rsp+78h] [rbp-8h]
int i; // [rsp+7Ch] [rbp-4h]
i = 0;
v6 = 0;
int key = 0x12;
int a1[19] = { 105, 122, 119, 104, 114, 111, 122, 34, 34, 119,
34, 118, 46, 75, 34, 46, 78, 105, 0 };
int a2[19] = {};
for (i = 0; i < key; i += 3)
{
//v5[i] = key ^ (a1[i] + 6);
//v4[i + 1] = (a1[i + 1] - 6) ^ key;
//v3[i + 2] = a1[i + 2] ^ 6 ^ key;
a2[i] = (key ^ (a1[i])) - 6;
a2[i + 1] = ((a1[i + 1]) ^ key) + 6;
a2[i + 2] = a1[i + 2] ^ 6 ^ key;
}
for (int a = 0; a < 19; a++)
{
printf("%c", a2[a]);
}
}
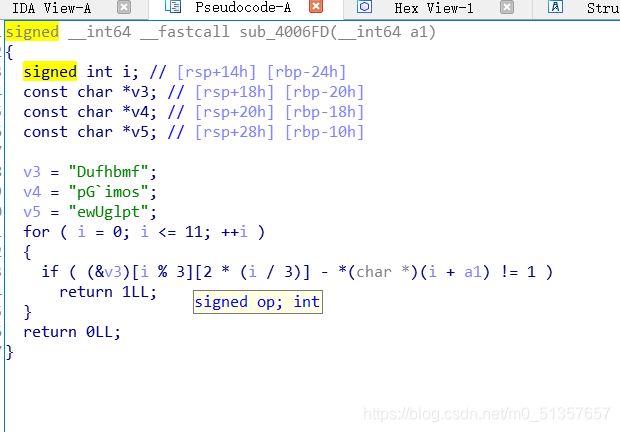
2、Reversing-x64Elf-100
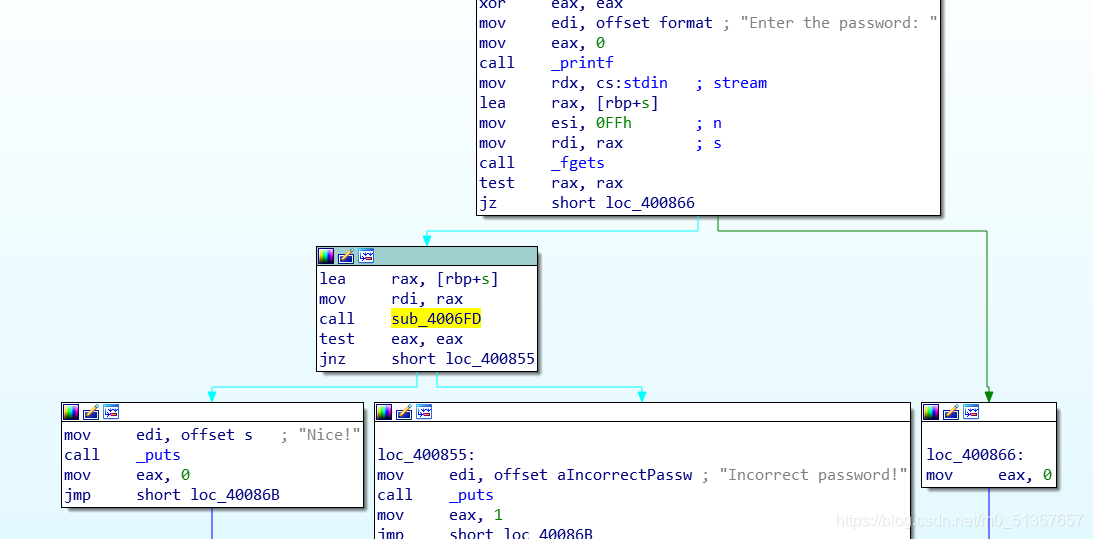
直奔sub_4006F0,因为是if,不能动调,看逻辑逆推即可
脚本:
#include<iostream>
#define _CRT_SECURE_NO_WARNINGS
using namespace std;
int main()
{
signed int i; // [rsp+14h] [rbp-24h]
char v3[3][8] = { "Dufhbmf","pG`imos","ewUglpt" };
char a1[30] = " ";
int a, b;
for (i = 0; i <= 11; ++i)
{
a = i % 3;
b = 2 * (i / 3);
*(char*)(i + a1) = v3[a][b] - 1;
}
printf("%s", a1);
}

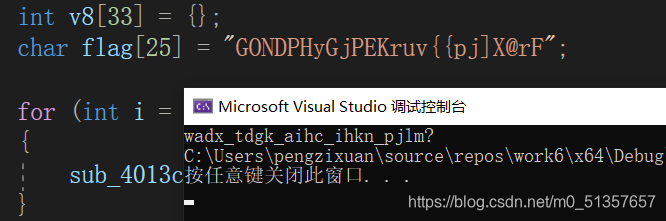
3、IgniteMe
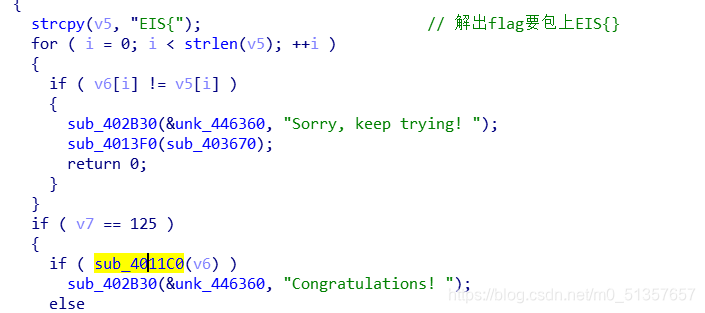
直奔Congratulations,找到主要函数sub_4011C0,看着往回逆
shift+e 提取出byte_4420B0里的数据

先让转换完的字符串和byte_4420b0里的数异或。。。总之求出v8即可
这里有点奇怪,字符串只有25位,但异或的数有32个。。取字符串的位数异或25位吧
#include<iostream>
using namespace std;
int main()
{
int byte_4420b0[32] = { 0x0D, 0x13, 0x17, 0x11, 0x02, 0x01, 0x20, 0x1D, 0x0C, 0x02,
0x19, 0x2F, 0x17, 0x2B, 0x24, 0x1F, 0x1E, 0x16, 0x09, 0x0F,
0x15, 0x27, 0x13, 0x26, 0x0A, 0x2F, 0x1E, 0x1A, 0x2D, 0x0C,
0x22, 0x04 };
int sub_4013c0[33] = {};
int v8[33] = {};
char flag[25] = "GONDPHyGjPEKruv{{pj]X@rF";
for (int i = 0; i < 25; i++)
{
sub_4013c0[i] = int(flag[i]) ^ byte_4420b0[i];
}
for (int i = 0; i < 25; i++)
{
v8[i] = (sub_4013c0[i] - 72) ^ 0x55;
if (v8[i] >= 97 && v8[i] <= 122)
{
v8[i] -= 32;
}
if ( v8[i] >= 65 && v8[i] <= 90)
v8[i] += 32;
}
for (int i = 0; i < 25; i++)
{
printf("%c", v8[i]);
}
//包上EIS{}
}
emmmmm忽略那个问号。。。记得加EIS{}
4、hackme
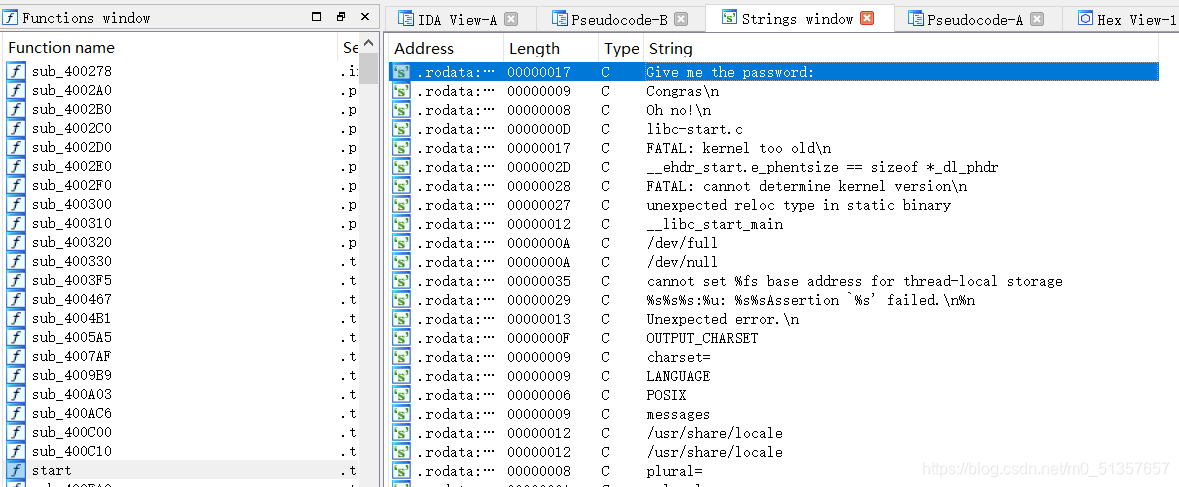
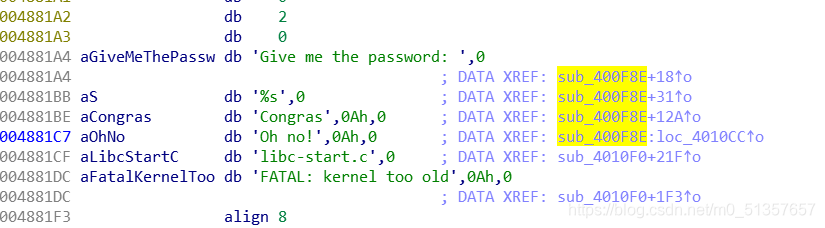
一堆函数不知道看哪个,f12看字符串
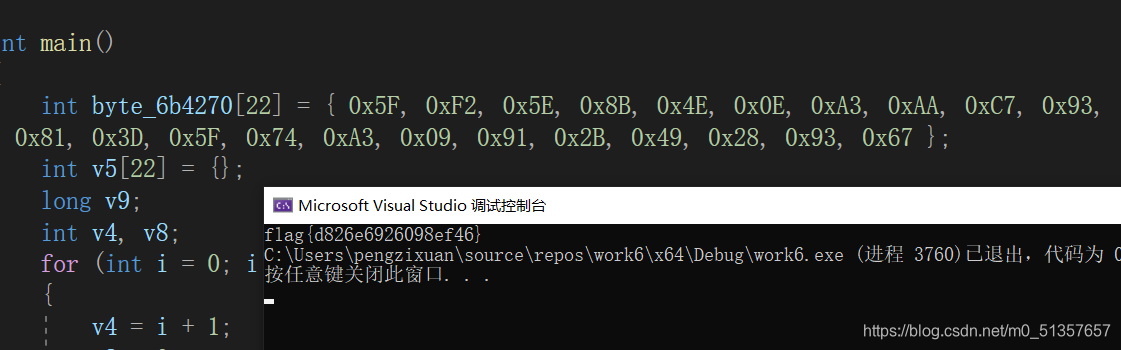
看函数取了十位验证,所以动调不太行,还是得写脚本老老实实逆
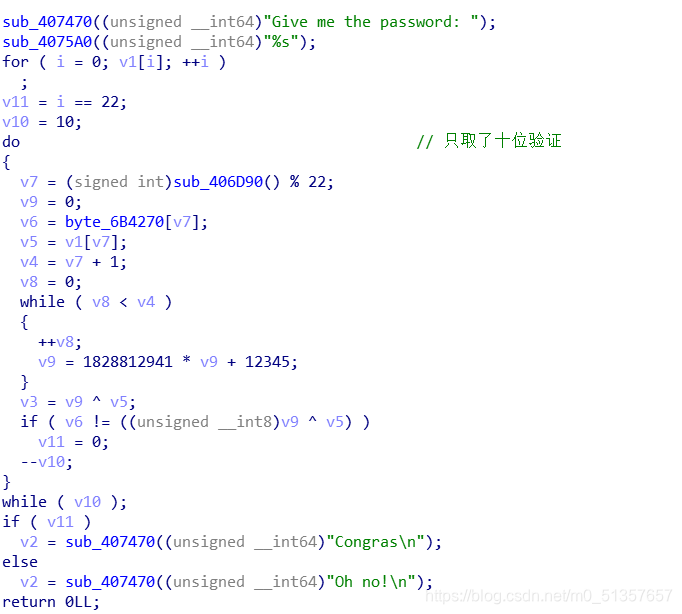
写脚本第一要注意v9每次循环置零,二是&0xff (详解 &0xff 的作用
#include<iostream>
using namespace std;
int main()
{
int byte_6b4270[22] = { 0x5F, 0xF2, 0x5E, 0x8B, 0x4E, 0x0E, 0xA3, 0xAA, 0xC7, 0x93,
0x81, 0x3D, 0x5F, 0x74, 0xA3, 0x09, 0x91, 0x2B, 0x49, 0x28, 0x93, 0x67 };
int v5[22] = {};
long v9;
int v4, v8;
for(int i= 0 ;i < 22 ; i++)
{
v4 = i + 1;
v8 = 0;
v9 = 0; //记得每次循环v9要置零
while (v8 < v4)
{
++v8;
v9 = 1828812941 * v9 + 12345;
}
v5[i] = (byte_6b4270[i] ^ v9) & 0xff;
printf("%c", v5[i]);
}
}
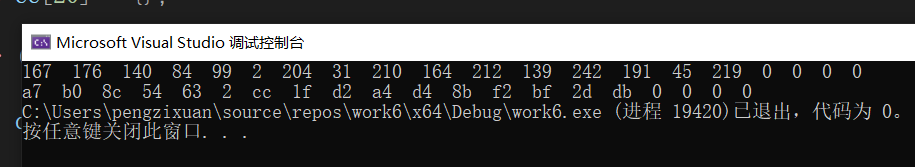
5、Guess-the-Number
是一道java的题,用jadx-gui反编译
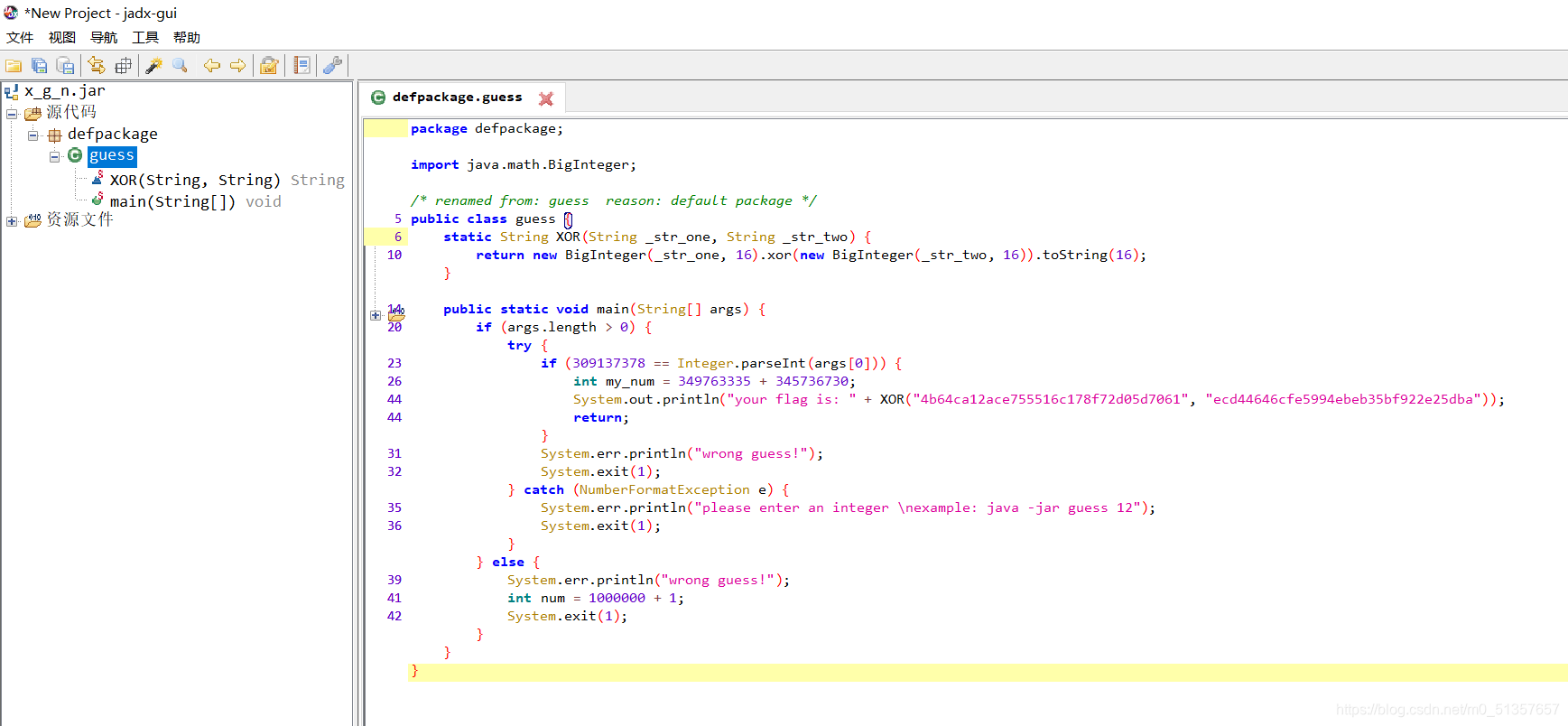
flag就是两个16进制数按位异或的结果
会java的直接用java逆就行了(我不会。。我是废物。。
用C++的需要注意一下:2之前要补0
所以结果是a7b08c546302cc1fd2a4d48bf2bf2ddb,一开始我还以为要转成字符,不对,就直接提交这一串16进制数即可
#include<iostream>
#define _CRT_SECURE_NO_WARNINGS
using namespace std;
int main()
{
int aa[20] = { 0x4b,0x64,0xca,0x12,0xac,0xe7,0x55,0x51,0x6c,0x17,0x8f,0x72,0xd0,0x5d,0x70,0x61 };
int bb[20] = { 0xec,0xd4,0x46,0x46,0xcf,0xe5,0x99,0x4e,0xbe,0xb3,0x5b,0xf9,0x22,0xe2,0x5d,0xba };
int cc[20] = {};
for (int i = 0; i < 20; i++)
{
cc[i] = aa[i] ^ bb[i];
}
for (int a = 0; a < 16; a++)
{
printf("%x", cc[a]);
}
}
6、dmd-50
拿到字符串解md5即可
7、re-for-50-plz-50
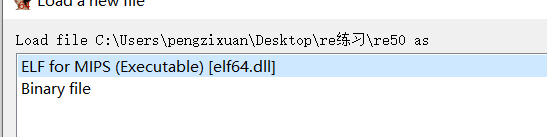
WIPS文件,没见过,还反编译不了。。。
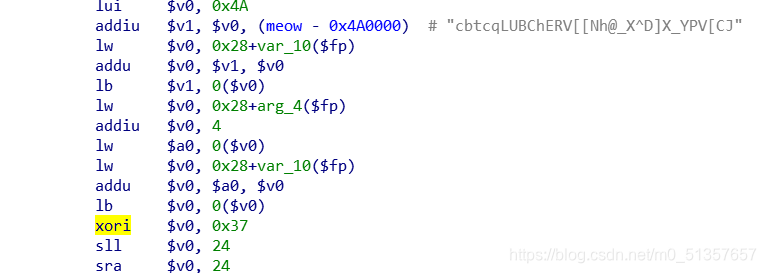
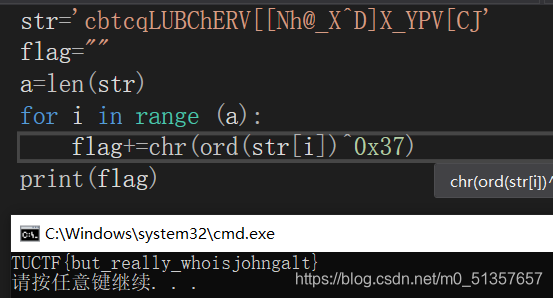
盲猜跟0x37异或,写个脚本,哈,蒙对了
8、debug
这题好像已经被换掉了。。emmmm
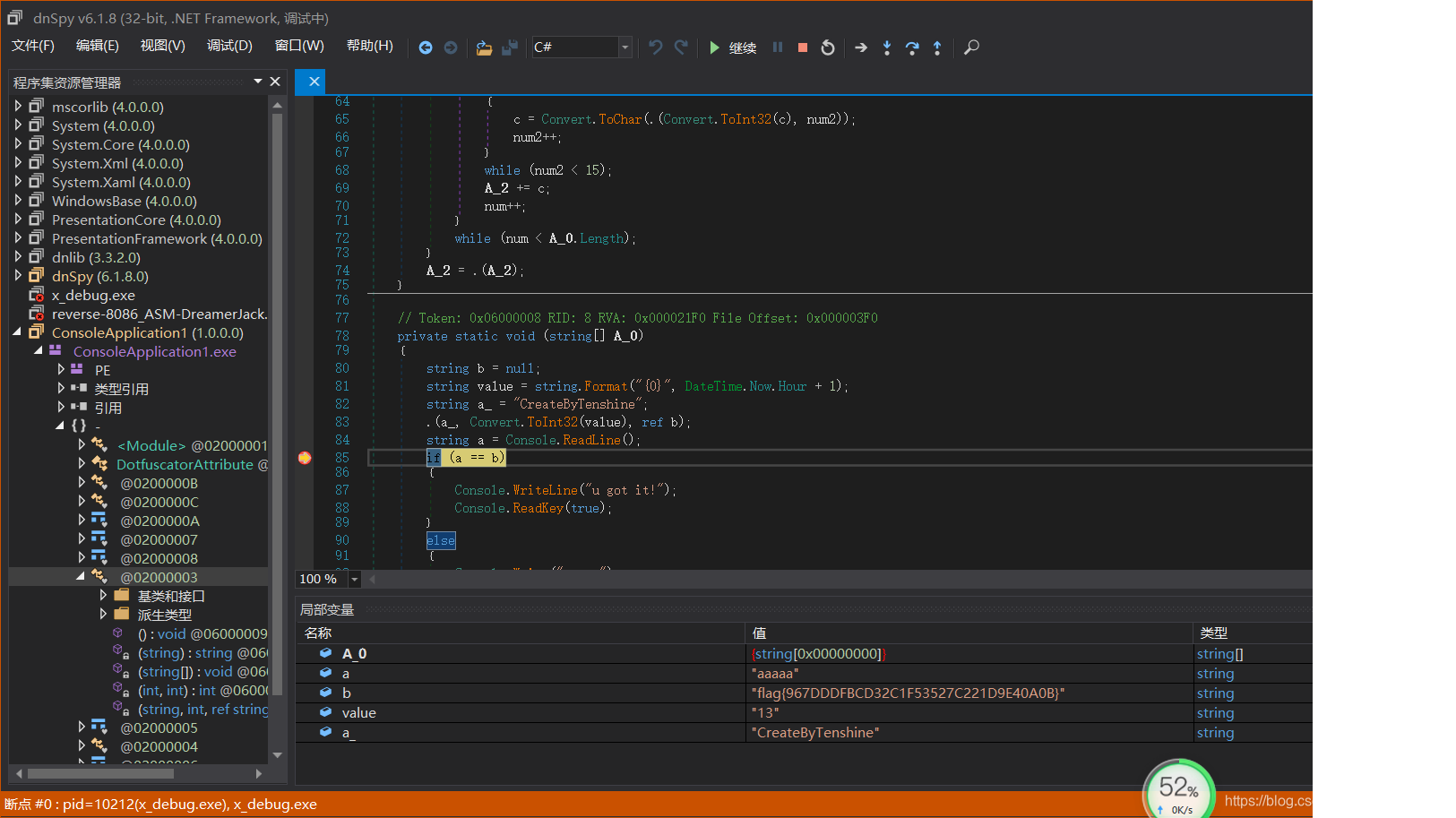
.NET文件,用dnSpy
主函数在0200003,在比对处下断,运行,得明文
大多都是异或的题,复制粘贴改脚本逆,没有套娃就很友好
想做动调的题55555






















 332
332











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








