玄机靶场第一章Linux日志分析

1.有多少IP在爆破主机ssh的root帐号,如果有多个使用","分割
2.ssh爆破成功登陆的IP是多少,如果有多个使用","分割
3.爆破用户名字典是什么?如果有多个使用","分割
4.登陆成功的IP共爆破了多少次
5.黑客登陆主机后新建了一个后门用户,用户名是多少
flag1:
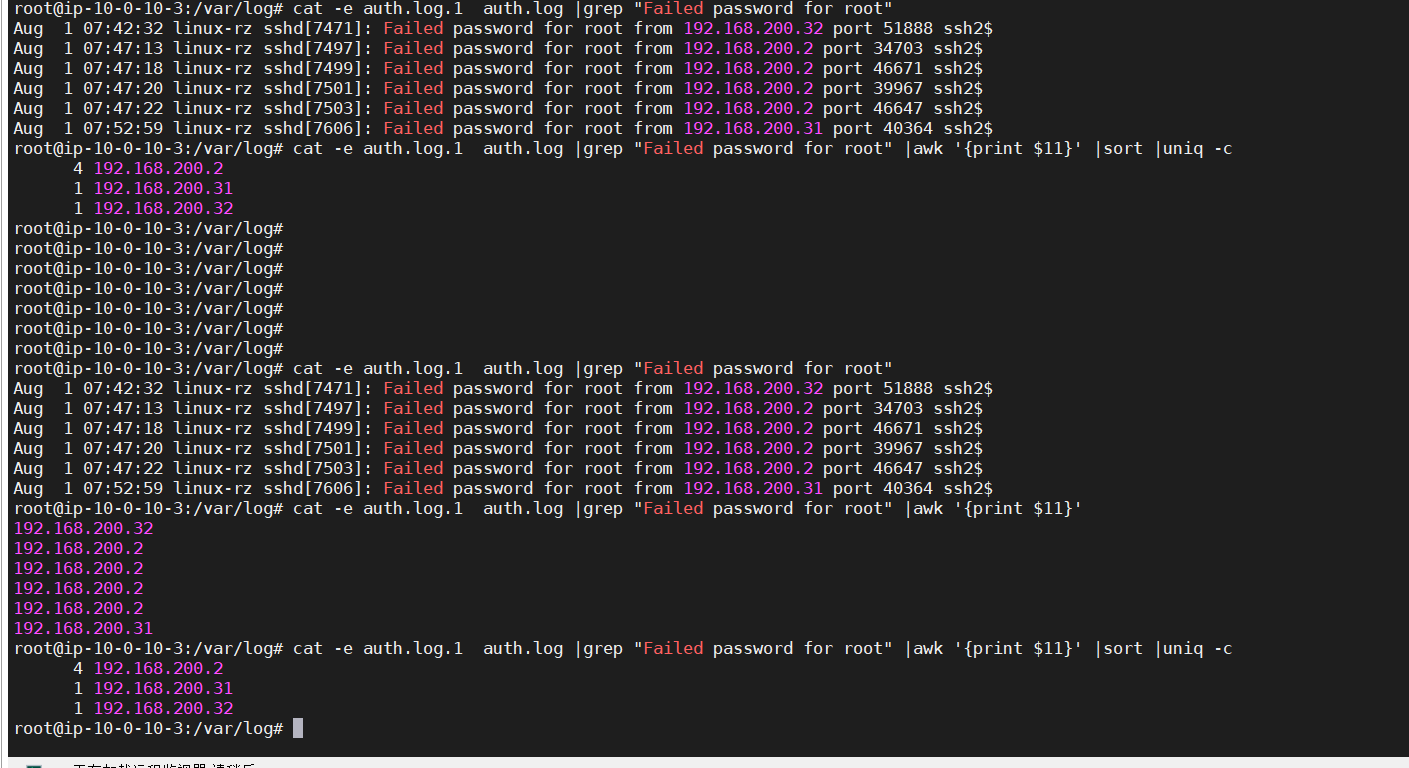
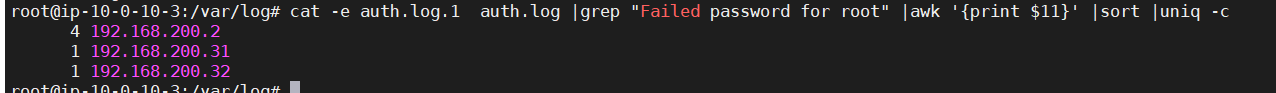
爆破主机ssh的root账号查找语句“Failed password for root”
之后进行awk切割,sort排序,uniq -c进行统计拿到flag1
cat -e auth.log.1 auth.log |grep "Failed password for root"
cat -e auth.log.1 auth.log |grep "Failed password for root" |awk '{print $10}'
cat -e auth.log.1 auth.log |grep "Failed password for root" |awk '{print $11}'
cat -e auth.log.1 auth.log |grep "Failed password for root" |awk '{print $11}' |sort
cat -e auth.log.1 auth.log |grep "Failed password for root" |awk '{print $11}' |sort |uniq -c
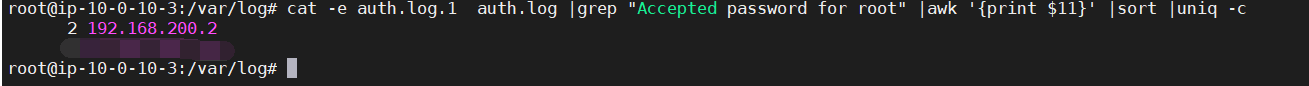
flag2:
查找爆破成功语句“Accepted password for root”进行上述操作拿到flag2
cat -e auth.log.1 auth.log |grep "Accepted password for root" |awk '{print $11}' |sort |uniq -c
flag3:
寻找爆破名字典,可寻找字段“invalid user”进行统计排除加上root
cat -e auth.log.1 auth.log |grep "invalid user"
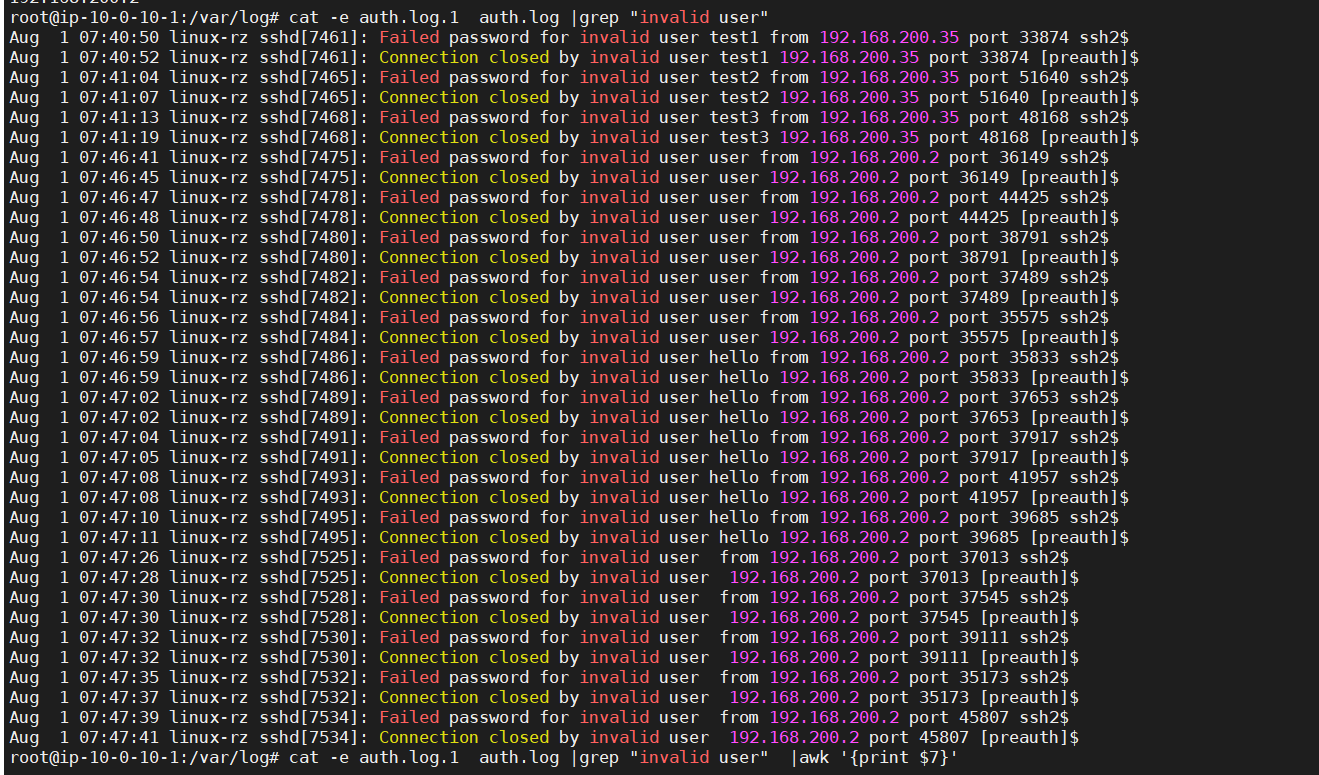
cat -e auth.log.1 auth.log |grep "invalid user" |awk '{print $11}'
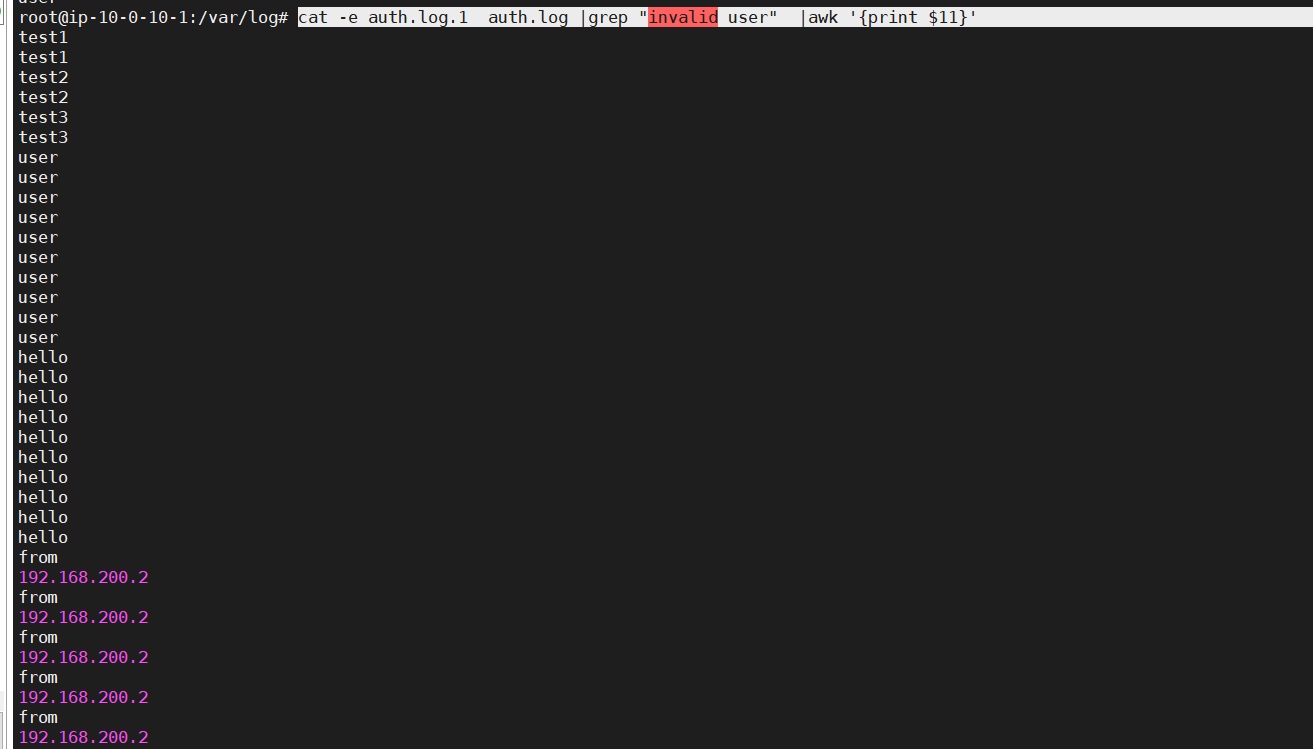
不过flag顺序要进行排序猜测,不推荐这种,这里推荐vx公众号-靶场手记的做法
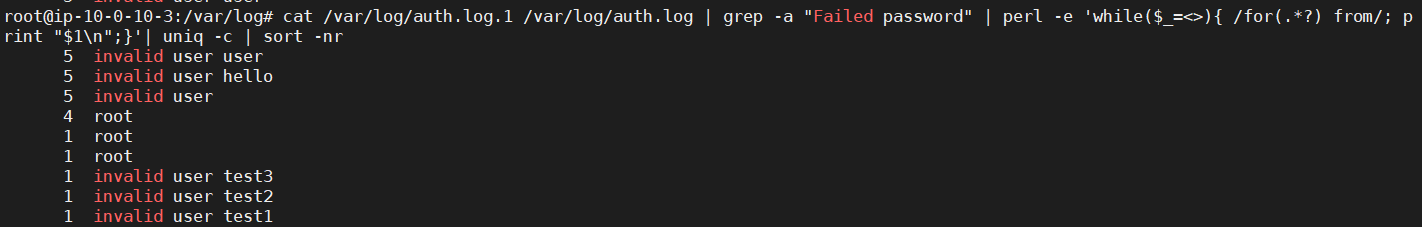
perl命令接受了grep的查询结果,之后匹配 “for” 和 “from” 之间的任何字符(用户名),最终 Flag 拼接后为user,hello,root,test3,test2,test1
cat /var/log/auth.log.1 /var/log/auth.log | grep -a "Failed password" | perl -e 'while($_=<>){ /for(.*?) from/; print "$1\n";}'| uniq -c | sort -nr
flag4:
次数在flag2中就已显示
flag5:
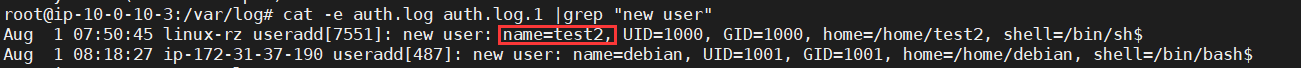
查找语句“new user”
cat -e auth.log auth.log.1 |grep "new user"






















 1683
1683

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








