ezAndroid
用jadx反编译APK看看

逻辑很简单,就是简单的账号密码验证,验证都放在so文件里了
接着用IDA反编译libezandroid.so看看
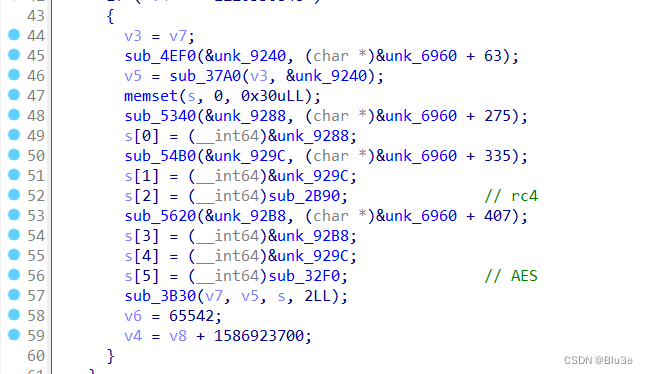
从JNI_OnLoad函数开始慢慢分析,可以分析出在这两个函数里分别是RC4算法魔改和AES算法魔改,其中RC4算法加密后还需异或下标,AES算法的SBOX被魔改了,账号用RC4算法加密,密码用AES算法加密。
先在sub_2B90函数里找到关键判断
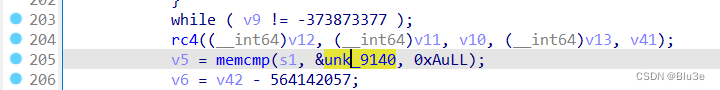
查看unk_9140处没有数据,于是猜测是在运行中赋值的,交叉引用(对准unk_9140按X)找到赋值的地方,可以发现是在sub_2540函数

接着回去分析rc4算法(sub_57D0函数),可以看出a4存放的是密钥
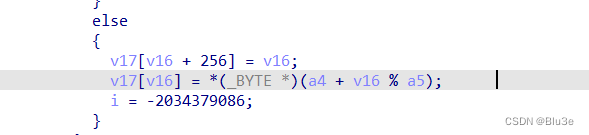
于是通过交叉引用可以找到sub_4D80函数
sub_4D80((__int64)&qword_9230, (__int64)&unk_6960 + 0x11);
在该函数里只有一个简单的异或运算,取8个字节当作密钥
*(_BYTE *)(a1 + v5) = *(_BYTE *)(a2 + v5 % 21u) ^ *(_BYTE *)(a2 + 21 + v5);
提取对应数据异或下
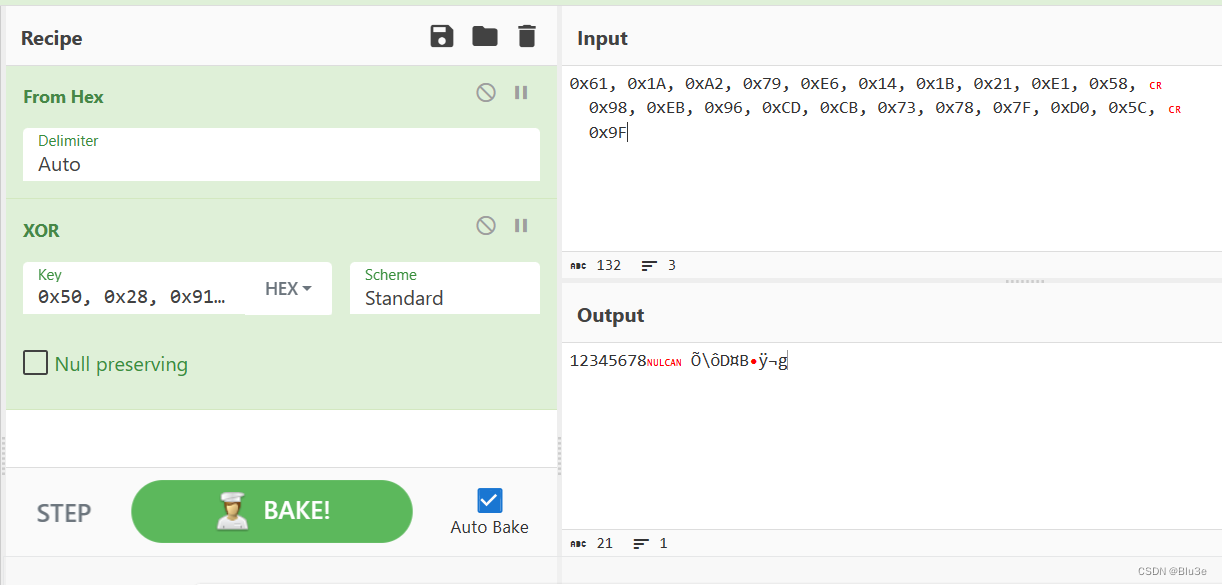
可知密钥为12345678
于是可以求出账号为Re_1s_eaSy
接着分析下AES算法(sub_32F0函数)
其中AES算法的密钥为 Re_1s_eaSy123456
同样的在sub_32F0函数里先找到关键判断
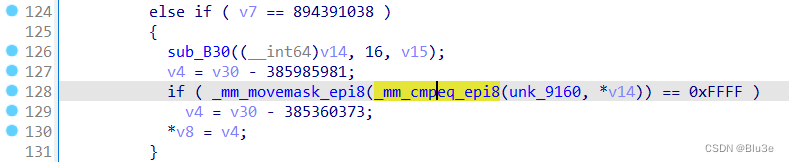
同样用交叉引用找到unk_9160数组赋值的地方
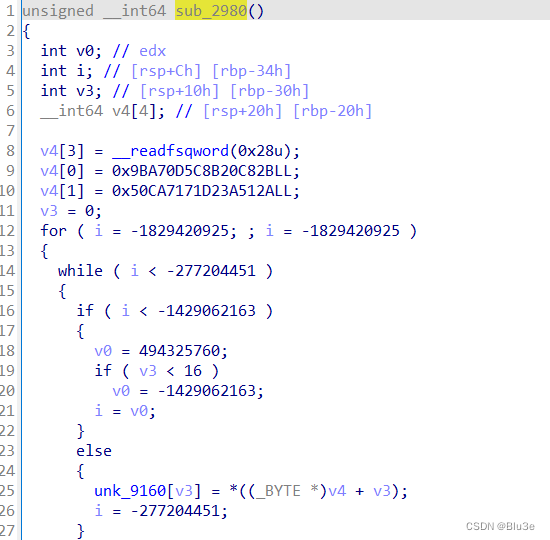
接下来分析算法
sub_32F0->sub_B30->sub_18C0->sub_41F0
可以看到一个数组
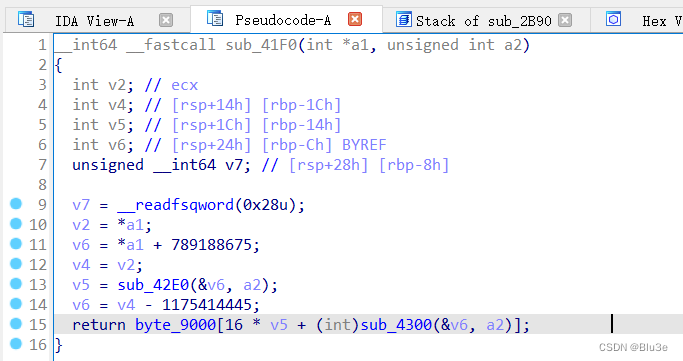
跟踪过去发现是熟悉的SBOX
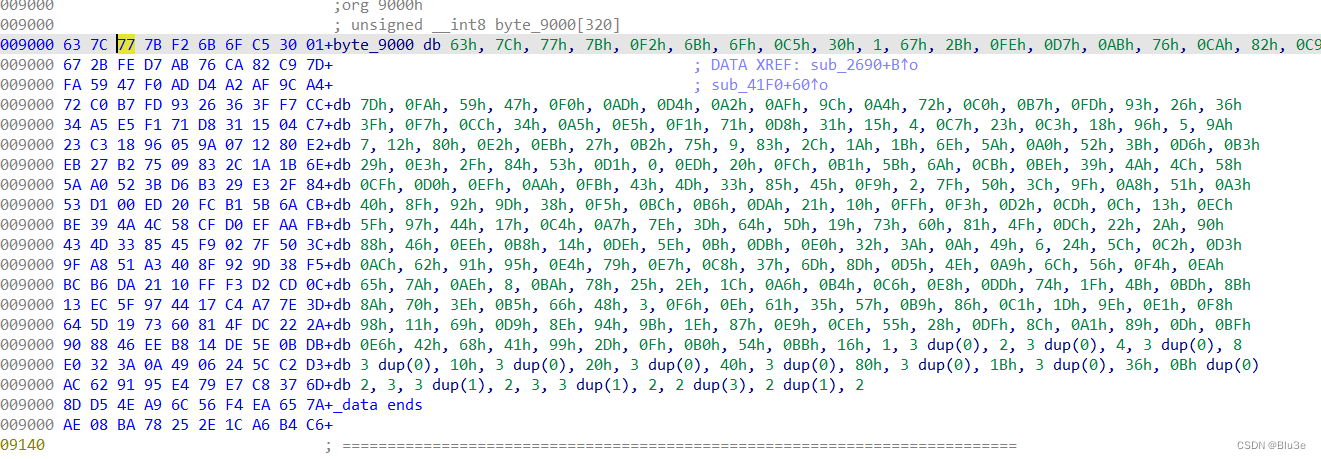
于是猜测是AES加密,先用常规的AES解密,发现解出来是乱码,于是猜测被魔改了,先对byte_9000数组交叉引用看下,可以发现byte_9000数组在sub_2690函数里被重新赋值了
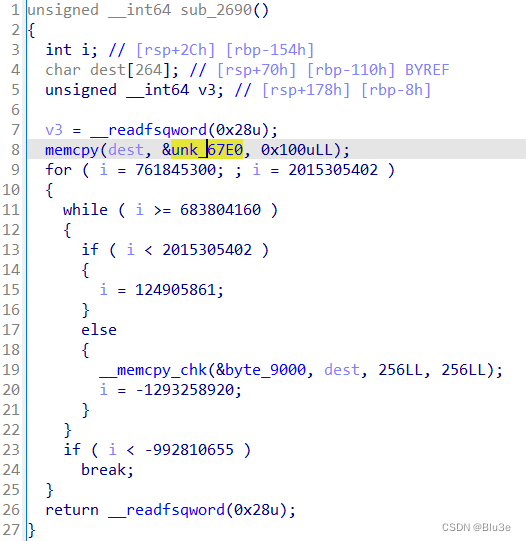
提取出unk_67E0数组,先求下逆S盒
new_s_box = [0x29, 0x40, 0x57, 0x6E, 0x85, 0x9C, 0xB3, 0xCA, 0xE1, 0xF8,
0x0F, 0x26, 0x3D, 0x54, 0x6B, 0x82, 0x99, 0xB0, 0xC7, 0xDE,
0xF5, 0x0C, 0x23, 0x3A, 0x51, 0x68, 0x7F, 0x96, 0xAD, 0xC4,
0xDB, 0xF2, 0x09, 0x20, 0x37, 0x4E, 0x65, 0x7C, 0x93, 0xAA,
0xC1, 0xD8, 0xEF, 0x06, 0x1D, 0x34, 0x4B, 0x62, 0x79, 0x90,
0xA7, 0xBE, 0xD5, 0xEC, 0x03, 0x1A, 0x31, 0x48, 0x5F, 0x76,
0x8D, 0xA4, 0xBB, 0xD2, 0xE9, 0x00, 0x17, 0x2E, 0x45, 0x5C,
0x73, 0x8A, 0xA1, 0xB8, 0xCF, 0xE6, 0xFD, 0x14, 0x2B, 0x42,
0x59, 0x70, 0x87, 0x9E, 0xB5, 0xCC, 0xE3, 0xFA, 0x11, 0x28,
0x3F, 0x56, 0x6D, 0x84, 0x9B, 0xB2, 0xC9, 0xE0, 0xF7, 0x0E,
0x25, 0x3C, 0x53, 0x6A, 0x81, 0x98, 0xAF, 0xC6, 0xDD, 0xF4,
0x0B, 0x22, 0x39, 0x50, 0x67, 0x7E, 0x95, 0xAC, 0xC3, 0xDA,
0xF1, 0x08, 0x1F, 0x36, 0x4D, 0x64, 0x7B, 0x92, 0xA9, 0xC0,
0xD7, 0xEE, 0x05, 0x1C, 0x33, 0x4A, 0x61, 0x78, 0x8F, 0xA6,
0xBD, 0xD4, 0xEB, 0x02, 0x19, 0x30, 0x47, 0x5E, 0x75, 0x8C,
0xA3, 0xBA, 0xD1, 0xE8, 0xFF, 0x16, 0x2D, 0x44, 0x5B, 0x72,
0x89, 0xA0, 0xB7, 0xCE, 0xE5, 0xFC, 0x13, 0x2A, 0x41, 0x58,
0x6F, 0x86, 0x9D, 0xB4, 0xCB, 0xE2, 0xF9, 0x10, 0x27, 0x3E,
0x55, 0x6C, 0x83, 0x9A, 0xB1, 0xC8, 0xDF, 0xF6, 0x0D, 0x24,
0x3B, 0x52, 0x69, 0x80, 0x97, 0xAE, 0xC5, 0xDC, 0xF3, 0x0A,
0x21, 0x38, 0x4F, 0x66, 0x7D, 0x94, 0xAB, 0xC2, 0xD9, 0xF0,
0x07, 0x1E, 0x35, 0x4C, 0x63, 0x7A, 0x91, 0xA8, 0xBF, 0xD6,
0xED, 0x04, 0x1B, 0x32, 0x49, 0x60, 0x77, 0x8E, 0xA5, 0xBC,
0xD3, 0xEA, 0x01, 0x18, 0x2F, 0x46, 0x5D, 0x74, 0x8B, 0xA2,
0xB9, 0xD0, 0xE7, 0xFE, 0x15, 0x2C, 0x43, 0x5A, 0x71, 0x88,
0x9F, 0xB6, 0xCD, 0xE4, 0xFB, 0x12]
new_contrary_sbox = [0] * 256
for i in range(256):
line = (new_s_box[i] & 0xf0) >> 4
rol = new_s_box[i] & 0xf
new_contrary_sbox[(line * 16) + rol] = i
for i in range(0, len(new_s_box), 16):
print(new_s_box[i:i + 16], end='')
print(',')
print()
for i in range(0, len(new_contrary_sbox), 16):
print(new_contrary_sbox[i:i + 16], end='')
print(',')
将原本的S盒和逆S盒替换下
最终解题脚本:
from Crypto.Cipher import ARC4
from Crypto.Util.number import *
class AES:
MIX_C = [[0x2, 0x3, 0x1, 0x1], [0x1, 0x2, 0x3, 0x1], [0x1, 0x1, 0x2, 0x3], [0x3, 0x1, 0x1, 0x2]]
I_MIXC = [[0xe, 0xb, 0xd, 0x9], [0x9, 0xe, 0xb, 0xd], [0xd, 0x9, 0xe, 0xb], [0xb, 0xd, 0x9, 0xe]]
RCon = [0x01000000, 0x02000000, 0x04000000, 0x08000000, 0x10000000, 0x20000000, 0x40000000, 0x80000000, 0x1B000000,
0x36000000]
S_BOX = [[41, 64, 87, 110, 133, 156, 179, 202, 225, 248, 15, 38, 61, 84, 107, 130],
[153, 176, 199, 222, 245, 12, 35, 58, 81, 104, 127, 150, 173, 196, 219, 242],
[9, 32, 55, 78, 101, 124, 147, 170, 193, 216, 239, 6, 29, 52, 75, 98],
[121, 144, 167, 190, 213, 236, 3, 26, 49, 72, 95, 118, 141, 164, 187, 210],
[233, 0, 23, 46, 69, 92, 115, 138, 161, 184, 207, 230, 253, 20, 43, 66],
[89, 112, 135, 158, 181, 204, 227, 250, 17, 40, 63, 86, 109, 132, 155, 178],
[201, 224, 247, 14, 37, 60, 83, 106, 129, 152, 175, 198, 221, 244, 11, 34],
[57, 80, 103, 126, 149, 172, 195, 218, 241, 8, 31, 54, 77, 100, 123, 146],
[169, 192, 215, 238, 5, 28, 51, 74, 97, 120, 143, 166, 189, 212, 235, 2],
[25, 48, 71, 94, 117, 140, 163, 186, 209, 232, 255, 22, 45, 68, 91, 114],
[137, 160, 183, 206, 229, 252, 19, 42, 65, 88, 111, 134, 157, 180, 203, 226],
[249, 16, 39, 62, 85, 108, 131, 154, 177, 200, 223, 246, 13, 36, 59, 82],
[105, 128, 151, 174, 197, 220, 243, 10, 33, 56, 79, 102, 125, 148, 171, 194],
[217, 240, 7, 30, 53, 76, 99, 122, 145, 168, 191, 214, 237, 4, 27, 50],
[73, 96, 119, 142, 165, 188, 211, 234, 1, 24, 47, 70, 93, 116, 139, 162],
[185, 208, 231, 254, 21, 44, 67, 90, 113, 136, 159, 182, 205, 228, 251, 18]]
I_SBOX = [[65, 232, 143, 54, 221, 132, 43, 210, 121, 32, 199, 110, 21, 188, 99, 10],
[177, 88, 255, 166, 77, 244, 155, 66, 233, 144, 55, 222, 133, 44, 211, 122],
[33, 200, 111, 22, 189, 100, 11, 178, 89, 0, 167, 78, 245, 156, 67, 234],
[145, 56, 223, 134, 45, 212, 123, 34, 201, 112, 23, 190, 101, 12, 179, 90],
[1, 168, 79, 246, 157, 68, 235, 146, 57, 224, 135, 46, 213, 124, 35, 202],
[113, 24, 191, 102, 13, 180, 91, 2, 169, 80, 247, 158, 69, 236, 147, 58],
[225, 136, 47, 214, 125, 36, 203, 114, 25, 192, 103, 14, 181, 92, 3, 170],
[81, 248, 159, 70, 237, 148, 59, 226, 137, 48, 215, 126, 37, 204, 115, 26],
[193, 104, 15, 182, 93, 4, 171, 82, 249, 160, 71, 238, 149, 60, 227, 138],
[49, 216, 127, 38, 205, 116, 27, 194, 105, 16, 183, 94, 5, 172, 83, 250],
[161, 72, 239, 150, 61, 228, 139, 50, 217, 128, 39, 206, 117, 28, 195, 106],
[17, 184, 95, 6, 173, 84, 251, 162, 73, 240, 151, 62, 229, 140, 51, 218],
[129, 40, 207, 118, 29, 196, 107, 18, 185, 96, 7, 174, 85, 252, 163, 74],
[241, 152, 63, 230, 141, 52, 219, 130, 41, 208, 119, 30, 197, 108, 19, 186],
[97, 8, 175, 86, 253, 164, 75, 242, 153, 64, 231, 142, 53, 220, 131, 42],
[209, 120, 31, 198, 109, 20, 187, 98, 9, 176, 87, 254, 165, 76, 243, 154]]
def SubBytes(self, State):
# 字节替换
return [self.S_BOX[i][j] for i, j in
[(_ >> 4, _ & 0xF) for _ in State]]
def SubBytes_Inv(self, State):
# 字节逆替换
return [self.I_SBOX[i][j] for i, j in
[(_ >> 4, _ & 0xF) for _ in State]]
def ShiftRows(self, S):
# 行移位
return [S[0], S[5], S[10], S[15],
S[4], S[9], S[14], S[3],
S[8], S[13], S[2], S[7],
S[12], S[1], S[6], S[11]]
def ShiftRows_Inv(self, S):
# 逆行移位
return [S[0], S[13], S[10], S[7],
S[4], S[1], S[14], S[11],
S[8], S[5], S[2], S[15],
S[12], S[9], S[6], S[3]]
def MixColumns(self, State):
# 列混合
return self.Matrix_Mul(self.MIX_C, State)
def MixColumns_Inv(self, State):
# 逆列混合
return self.Matrix_Mul(self.I_MIXC, State)
def RotWord(self, _4byte_block):
# 用于生成轮密钥的字移位
return ((_4byte_block & 0xffffff) << 8) + (_4byte_block >> 24)
def SubWord(self, _4byte_block):
# 用于生成密钥的字节替换
result = 0
for position in range(4):
i = _4byte_block >> position * 8 + 4 & 0xf
j = _4byte_block >> position * 8 & 0xf
result ^= self.S_BOX[i][j] << position * 8
return result
def mod(self, poly, mod=0b100011011):
# poly模多项式mod
while poly.bit_length() > 8:
poly ^= mod << poly.bit_length() - 9
return poly
def mul(self, poly1, poly2):
# 多项式相乘
result = 0
for index in range(poly2.bit_length()):
if poly2 & 1 << index:
result ^= poly1 << index
return result
def Matrix_Mul(self, M1, M2): # M1 = MIX_C M2 = State
# 用于列混合的矩阵相乘
M = [0] * 16
for row in range(4):
for col in range(4):
for Round in range(4):
M[row + col * 4] ^= self.mul(M1[row][Round], M2[Round + col * 4])
M[row + col * 4] = self.mod(M[row + col * 4])
return M
def round_key_generator(self, _16bytes_key):
# 轮密钥产生
w = [_16bytes_key >> 96,
_16bytes_key >> 64 & 0xFFFFFFFF,
_16bytes_key >> 32 & 0xFFFFFFFF,
_16bytes_key & 0xFFFFFFFF] + [0] * 40
for i in range(4, 44):
temp = w[i - 1]
if not i % 4:
temp = self.SubWord(self.RotWord(temp)) ^ self.RCon[i // 4 - 1]
w[i] = w[i - 4] ^ temp
return [self.num_2_16bytes(
sum([w[4 * i] << 96, w[4 * i + 1] << 64,
w[4 * i + 2] << 32, w[4 * i + 3]])
) for i in range(11)]
def AddRoundKey(self, State, RoundKeys, index):
# 异或轮密钥
return self._16bytes_xor(State, RoundKeys[index])
def _16bytes_xor(self, _16bytes_1, _16bytes_2):
return [_16bytes_1[i] ^ _16bytes_2[i] for i in range(16)]
def _16bytes2num(cls, _16bytes):
# 16字节转数字
return int.from_bytes(_16bytes, byteorder='big')
def num_2_16bytes(cls, num):
# 数字转16字节
return num.to_bytes(16, byteorder='big')
def aes_encrypt(self, plaintext_list, RoundKeys):
State = plaintext_list
State = self.AddRoundKey(State, RoundKeys, 0)
for Round in range(1, 10):
State = self.SubBytes(State)
State = self.ShiftRows(State)
State = self.MixColumns(State)
State = self.AddRoundKey(State, RoundKeys, Round)
State = self.SubBytes(State)
State = self.ShiftRows(State)
State = self.AddRoundKey(State, RoundKeys, 10)
return State
def aes_decrypt(self, ciphertext_list, RoundKeys):
State = ciphertext_list
State = self.AddRoundKey(State, RoundKeys, 10)
for Round in range(1, 10):
State = self.ShiftRows_Inv(State)
State = self.SubBytes_Inv(State)
State = self.AddRoundKey(State, RoundKeys, 10 - Round)
State = self.MixColumns_Inv(State)
State = self.ShiftRows_Inv(State)
State = self.SubBytes_Inv(State)
State = self.AddRoundKey(State, RoundKeys, 0)
return State
def rc4_decrypt(data, key1): # 解密
enc = ARC4.new(key1.encode())
res = enc.decrypt(bytes(data))
res = str(res, 'gbk')
return res
if __name__ == '__main__':
data = [0xE9, 0x97, 0x64, 0xE6, 0x7E, 0xEB, 0xBD, 0xC1, 0xAB, 0x43]
key = '12345678'
msg = rc4_decrypt(data, key)
flag1 = ''
for i in range(len(msg)):
flag1 += chr(ord(msg[i]) ^ i)
print('flag1 = ' + flag1) # Re_1s_eaSy
aes = AES()
key = bytes_to_long((flag1+'123456').encode())
RoundKeys = aes.round_key_generator(key)
# 解密
ciphertext = 0x2BC8208B5C0DA79B2A513AD27171CA50
ciphertext = aes.num_2_16bytes(ciphertext)
flag2 = aes.aes_decrypt(ciphertext, RoundKeys)
print('flag2 = ' + bytes(flag2).decode()) # _eZ_Rc4_@nd_AES!
print('WMCTF{'+flag1 + bytes(flag2).decode()+'}') # WMCTF{Re_1s_eaSy_eZ_Rc4_@nd_AES!}
RightBack
用python3.9编译的pyc文件,无法用uncompyle6反编译,于是用pydisasm将pyc文件转成字节码
pydisasm -F xasm RightBack.pyc>test.txt
开始手撕字节码,大致还原成如下代码,其中一些print是后面加上用于输出解密的字符串和VM解释用的
import struct
from Crypto.Util.number import *
s = []
Sbox = [82, 9, 106, 213, 48, 54, 165, 56, 191, 64, 163, 158, 129, 243, 215, 251, 124, 227, 57, 130, 155, 47, 255, 135, 52, 142, 67, 68, 196, 222, 233, 203, 84, 123, 148, 50, 166, 194, 35, 61, 238, 76, 149, 11, 66, 250, 195, 78, 8, 46, 161, 102, 40, 217, 36, 178, 118, 91, 162, 73, 109, 139, 209, 37, 114, 248, 246, 100, 134, 104, 152, 22, 212, 164, 92, 204, 93, 101, 182, 146, 108, 112, 72, 80, 253, 237, 185, 218, 94, 21, 70, 87, 167, 141, 157, 132, 144, 216, 171, 0, 140, 188, 211, 10, 247, 228, 88, 5, 184, 179, 69, 6, 208, 44, 30, 143, 202, 63, 15, 2, 193, 175, 189, 3, 1, 19, 138, 107, 58, 145, 17, 65, 79, 103, 220, 234, 151, 242, 207, 206, 240, 180, 230, 115, 150, 172, 116, 34, 231, 173, 53, 133, 226, 249, 55, 232, 28, 117, 223, 110, 71, 241, 26, 113, 29, 41, 197, 137, 111, 183, 98, 14, 170, 24, 190, 27, 252, 86, 62, 75, 198, 210, 121, 32, 154, 219, 192, 254, 120, 205, 90, 244, 31, 221, 168, 51, 136, 7, 199, 49, 177, 18, 16, 89, 39, 128, 236, 95, 96, 81, 127, 169, 25, 181, 74, 13, 45, 229, 122, 159, 147, 201, 156, 239, 160, 224, 59, 77, 174, 42, 245, 176, 200, 235, 187, 60, 131, 83, 153, 97, 23, 43, 4, 126, 186, 119, 214, 38, 225, 105, 20, 99, 85, 33, 12, 125]
Rcon = [16777216, 33554432, 67108864, 134217728, 268435456, 536870912, 1073741824, 2147483648, 452984832, 905969664]
opcode = [69, 136, 121, 24, 179, 67, 209, 20, 27, 169, 205, 146, 212, 160, 124, 49, 20, 155, 157, 253, 52, 71, 174, 164, 134, 60, 184, 203, 131, 210, 57, 151, 77, 241, 61, 6, 13, 52, 235, 37, 100, 178, 8, 238, 205, 27, 194, 159, 230, 165, 211, 221, 100, 217, 111, 202, 185, 207, 226, 50, 88, 4, 58, 73, 10, 92, 24, 230, 246, 245, 21, 110, 182, 151, 85, 28, 181, 191, 185, 236, 92, 98, 222, 85, 228, 14, 235, 93, 77, 161, 61, 140, 222, 74, 124, 13, 211, 75, 134, 235, 164, 228, 235, 16, 29, 41, 49, 105, 188, 51, 232, 65, 209, 165, 35, 182, 248, 245, 69, 18, 152, 71, 223, 85, 114]
REG={}
EIP=0
reg_table = {
1:'EAX',
2:'EBX',
3:'ECX',
4:'EDX',
5:'R8',
6:'CNT',
7:'EIP',
}
def T(num, round):
numArr = bytearray(struct.pack('<I', num))
for i in range(4):
numArr[i] = Sbox[numArr[i]]
numArr = struct.unpack('<I', numArr)[0]
return numArr ^ Rcon[round]
def p1(s, key):
j = 0
k = []
for i in range(256):
s.append(i)
k.append(key[i % len(key)])
j = 0
for i in range(256):
j = (j + s[i] + ord(k[i])) % 256
s[i], s[j] = s[j], s[i]
def p2(key):
w = [0] * 44
for i in range(4):
w[i] = struct.unpack('<I', key[i * 4: i * 4 + 4])[0]
cnt = 0
for i in range(4, 44):
if i % 4 == 0:
w[i] = w[i - 4] ^ T(w[i - 1],cnt)
cnt+=1
else:
w[i] = w[i - 4] ^ w[i - 1]
return w
def p3(s, p):
i = j = 0
for z in range(len(p)):
i = (i + 1) % 256
j = (j + s[i]) % 256
s[i], s[j] = s[j], s[i]
p[z] ^= s[(s[i] + s[j]) % 256]
return p
def F1(part1, part2):
global REG
REG = {'EAX': 0, 'EBX': 0, 'ECX': 0, 'EDX': 0, 'R8': 0, 'CNT': 0, 'EIP': 0}
REG['EAX'] = part1
REG['EBX'] = part2
def F2(v1, v2, v3):
# print(extendKey)
if v1 == 1:
REG[reg_table[v2]]=extendKey[REG[reg_table[v3]]]
print('%s=extendKey[%s]' %(reg_table[v2],reg_table[v3]))
elif v1 == 2:
REG[reg_table[v2]]=REG[reg_table[v3]]
print('%s=%s' %(reg_table[v2],reg_table[v3]))
elif v1 == 3:
REG[reg_table[v2]]=v3
print(reg_table[v2]+'=%d'%v3)
REG['EIP'] += 4
return None
def F3(v1, v2, v3):
if v1 == 1:
REG[reg_table[v2]]=(REG[reg_table[v2]]+extendKey[REG[reg_table[v3]]])&0xffffffff
print('%s=(%s+extendKey[%s])&0xffffffff' %(reg_table[v2],reg_table[v2],reg_table[v3]))
elif v1 == 2:
REG[reg_table[v2]]=(REG[reg_table[v2]]+REG[reg_table[v3]])&0xffffffff
print('%s=(%s+%s)&0xffffffff' %(reg_table[v2],reg_table[v2],reg_table[v3]))
elif v1 == 3:
REG[reg_table[v2]]=(REG[reg_table[v2]]+v3)&0xffffffff
print('%s=(%s+%d)&0xffffffff' %(reg_table[v2],reg_table[v2],v3))
REG['EIP'] += 4
return None
def F4(v1, v2):
REG[reg_table[v1]] ^= REG[reg_table[v2]]
print('%s ^= %s' %(reg_table[v1],reg_table[v2]))
REG['EIP'] += 3
return None
def F5(v1, v2):
REG[reg_table[v1]] &= v2
print('%s &= %d' %(reg_table[v1],v2))
REG['EIP'] += 3
return None
def F6(v1, v2, v3):
if v1 == 1:
REG[reg_table[v2]]-=extendKey[v3]
print('REG[reg_table[v2]]-=extendKey[v3]')
elif v1 == 2:
REG[reg_table[v2]]-=REG[reg_table[v3]]
print('%s-=%s'%(reg_table[v2],reg_table[v3]))
elif v1 == 3:
REG[reg_table[v2]]-=v3
print('REG[reg_table[v2]]-=v3')
REG['EIP'] += 4
return None
def F7(v1, v2):
REG[reg_table[v1]] |= REG[reg_table[v2]]
print('%s |= %s'%(reg_table[v1],reg_table[v2]))
REG['EIP'] += 3
return None
def F8(v1, v2):
REG[reg_table[v1]]=(REG[reg_table[v1]]>>REG[reg_table[v2]])&0xffffffff
print('%s=(%s>>%s)&0xffffffff' %(reg_table[v1],reg_table[v1],reg_table[v2]))
REG['EIP'] += 3
return None
def F9(v1, v2):
REG[reg_table[v1]]=(REG[reg_table[v1]]<<REG[reg_table[v2]])&0xffffffff
print('%s=(%s<<%s)&0xffffffff' %(reg_table[v1],reg_table[v1],reg_table[v2]))
REG['EIP'] += 3
return None
def FA(v1, v2, v3):
if v1 == 1:
REG[reg_table[v2]]*=extendKey[v3]
print('REG[reg_table[v2]]*=extendKey[v3]')
elif v1 == 2:
REG[reg_table[v2]]*=REG[reg_table[v3]]
print('REG[reg_table[v2]]*=REG[reg_table[v3]]')
elif v1 == 3:
REG[reg_table[v2]]*=v3
print('%s*=%d' %(reg_table[v2],v3))
REG['EIP'] += 4
return None
def FB():
print('----------------------')
print(REG)
REG['R8']=REG['CNT']==21
REG['EIP']+=1
return None
def WC():
if REG['R8']:
REG['EIP']+=1
else:
REG['EIP']=16
def VM(part1, part2):
F1(part1,part2)
EIP = REG['EIP']
print(REG)
while opcode[EIP]!=255:
if opcode[EIP] == 80:
F2(opcode[EIP + 1], opcode[EIP + 2], opcode[EIP + 3])
elif opcode[EIP] == 29:
F3(opcode[EIP + 1], opcode[EIP + 2], opcode[EIP + 3])
elif opcode[EIP] == 113:
F4(opcode[EIP + 1], opcode[EIP + 2])
elif opcode[EIP] == 114:
F5(opcode[EIP + 1], opcode[EIP + 2])
elif opcode[EIP] == 150:
F6(opcode[EIP + 1], opcode[EIP + 2], opcode[EIP + 3])
elif opcode[EIP] == 87:
F7(opcode[EIP + 1], opcode[EIP + 2])
elif opcode[EIP] == 116:
F8(opcode[EIP + 1], opcode[EIP + 2])
elif opcode[EIP] == 41:
F9(opcode[EIP + 1], opcode[EIP + 2])
elif opcode[EIP] == 220:
FA(opcode[EIP + 1], opcode[EIP + 2], opcode[EIP + 3])
elif opcode[EIP] == 7:
FB()
elif opcode[EIP] == 153:
WC()
EIP = REG['EIP']
# print(REG['EIP'])
return None
def Have():
Hello = '''
|| / | / /
|| / | / / ___ // ___ ___ _ __ ___ __ ___ ___
|| / /||/ / //___) ) // // ) ) // ) ) // ) ) ) ) //___) ) / / // ) )
||/ / | / // // // // / / // / / / / // / / // / /
| / | / ((____ // ((____ ((___/ / // / / / / ((____ / / ((___/ /
|| / | / / /| //| | // ) ) /__ ___/ // / / ___ ___ ___ ___
|| / | / / //| // | | // / / //___ // ) ) // ) ) // ) ) // ) )
|| / /||/ / // | // | | // / / / ___ ___/ / // / / ___/ / __ / /
||/ / | / // | // | | // / / // / ____/ // / / / ____/ ) )
| / | / // |// | | ((____/ / / / // / /____ ((___/ / / /____ ((___/ /
'''
print(Hello)
return input('RightBack: ').encode()
def Fun(right):
# if len(right) != 64:
# print('XD')
# exit()
back = b''
for i in range(0, len(right), 8):
part1 = struct.unpack('>I', right[i:i+4])[0]
part2 = struct.unpack('>I', right[i+4:i+8])[0]
if i != 0:
part1 ^= struct.unpack('>I', back[i-8:i-4])[0]
part2 ^= struct.unpack('>I', back[i-4:i])[0]
VM(part1, part2)
back += struct.pack('>I', REG['EAX']) + struct.pack('>I', REG['EBX'])
return back
if __name__ == "__main__":
data1 = [228, 244, 207, 251, 194, 124, 252, 61, 198, 145, 97, 98, 89, 25, 92, 208, 155, 38, 34, 225, 98, 206, 234, 245, 223, 54, 214, 137, 35, 86, 180, 66, 223, 234, 90, 136, 5, 189, 166, 117, 111, 222, 39, 156, 163, 173, 36, 174, 47, 144, 15, 160, 45, 239, 211, 11, 190, 181, 24, 164, 234, 114, 174, 27]
data2 = [165, 83, 203, 51, 99, 164, 30, 91, 230, 64, 181, 55, 190, 47, 125, 240, 186, 173, 116, 47, 89, 64, 68, 215, 124, 138, 34, 175, 60, 136, 77, 216, 250, 127, 14, 14, 66, 168, 198, 247, 252, 189, 243, 239, 25, 63, 143, 7, 177, 13, 99, 226, 100, 6, 207, 77, 46, 136, 251, 123, 225, 27, 76, 183]
data3 = [95, 219, 46, 178, 111, 141, 17, 168, 254, 60, 68, 59, 41, 183, 182, 118, 3, 47, 150, 240, 140, 159, 110, 238]
key = 'CalmDownBelieveU'
p1(s,key)
key = [61, 15, 58, 65, 177, 180, 182, 248, 192, 143, 37, 238, 50, 29, 215, 190]
key=p3(s,key)
# print(bytes(key))#CalmDownBelieveU
global extendKey
extendKey=p2(bytes(key))
# print(extendKey)
opcode=p3(s,opcode)
print(opcode)
right = Have()
back = Fun(right)
data1 = bytes(p3(s,data1))#b'WOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOW!!!'
#04 3a f2 36 56 b1 9a fc f7 1e 21 dc db 8f 8e 94 4d 34 e7 9d 9c 52 0c 6e fb fa d5 fd 32 f9 78 2c bb be 39 c1 d9 85 75 b6 28 f8 cc 78 a4 e4 85 92 0e bd 72 c5 af 87 91 2a 8b f1 ef 96 16 60 d1 12
data2 = bytes(p3(s,data2))#b'\x04:\xf26V\xb1\x9a\xfc\xf7\x1e!\xdc\xdb\x8f\x8e\x94M4\xe7\x9d\x9cR\x0cn\xfb\xfa\xd5\xfd2\xf9x,\xbb\xbe9\xc1\xd9\x85u\xb6(\xf8\xccx\xa4\xe4\x85\x92\x0e\xbdr\xc5\xaf\x87\x91*\x8b\xf1\xef\x96\x16`\xd1\x12'
data3 = bytes(p3(s,data3))#b'I believe you can do it!'
# print(data1)
# print(data2)
# print(data3)
if back == data2:
print(bytes(data1).decode())#b'WOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOWOW!!!'
else:
print(bytes(data3).decode())#b'I believe you can do it!'
None # Return None
VM实现的功能:
for i in range(21):
CNT=(CNT+1)&0xffffffff
EAX ^= EBX
ECX=EAX
R8=EBX
EBX &= 31
EAX=(EAX<<EBX)&0xffffffff
EDX=32
EDX-=EBX
ECX=(ECX>>EDX)&0xffffffff
EAX |= ECX
EBX=CNT
EBX*=2
ECX=extendKey[EBX]
EAX=(EAX+ECX)&0xffffffff
EBX=R8
EBX ^= EAX
ECX=EBX
EDX=EAX
EDX &= 31
EBX=(EBX<<EDX)&0xffffffff
R8=32
R8-=EDX
ECX=(ECX>>R8)&0xffffffff
EBX |= ECX
ECX=CNT
ECX*=2
ECX=(ECX+1)&0xffffffff
EDX=extendKey[ECX]
EBX=(EBX+EDX)&0xffffffff
可以直接逆,脚本如下:
from Crypto.Util.number import *
def ROL(val,count):
return ((val>>(32-count))&0xffffffff)|((val<<count)&0xffffffff)
def ROR(val,count):
return ((val<<(32-count))&0xffffffff)|((val>>count)&0xffffffff)
extendKey = [1835819331, 1853321028, 1768711490, 1432712805, 2177920767, 4020699579, 2261476601, 3551400604, 711874531, 3318306392, 1124217505, 2427199549, 3099853672, 2098025776, 1041196945, 2929936300, 246748610, 1941455090, 1303848803, 3809763535, 1395557789, 546751855, 1830937100, 2385871555, 2516030638, 3043054017, 3628118989, 1450520846, 1825094265, 3651791800, 32069749, 1469868411, 919887482, 4017993154, 4002737591, 3104343244, 4134211933, 420914335, 4152510760, 1317719524, 1990496755, 1873950060, 2553314372, 3602559392]
result='043af23656b19afcf71e21dcdb8f8e944d34e79d9c520c6efbfad5fd32f9782cbbbe39c1d98575b628f8cc78a4e485920ebd72c5af87912a8bf1ef961660d112'
flag=b''
for x in range(0,len(result),16):
r1=int(result[x:x+8],16)
r2=int(result[x+8:x+16],16)
r6=21
for i in range(20,-1,-1):
r2 = (r2-extendKey[r6 * 2 + 1]) & 0xFFFFFFFF
r4 = r1 & 31
r2 = ROR(r2,r4)
r2 = r2^r1
r1 = (r1-extendKey[r6 * 2]) & 0xFFFFFFFF
r5 = r2&31
r1 = ROR(r1,r5)
r1 ^= r2
r6 -= 1
r2 = (r2-extendKey[1]) & 0xFFFFFFFF
r1 = (r1-extendKey[0]) & 0xFFFFFFFF
if x!=0:
k1=int(result[x-16:x-8],16)
k2=int(result[x-8:x],16)
else:
k1=0
k2=0
flag+=long_to_bytes(r1^k1)+long_to_bytes(r2^k2)
print(flag)#WMCTF{G00dEv3ning!Y0uAreAwes0m3!!RightBackFromB1ackM1rr0r!WOW!!}
gohunt
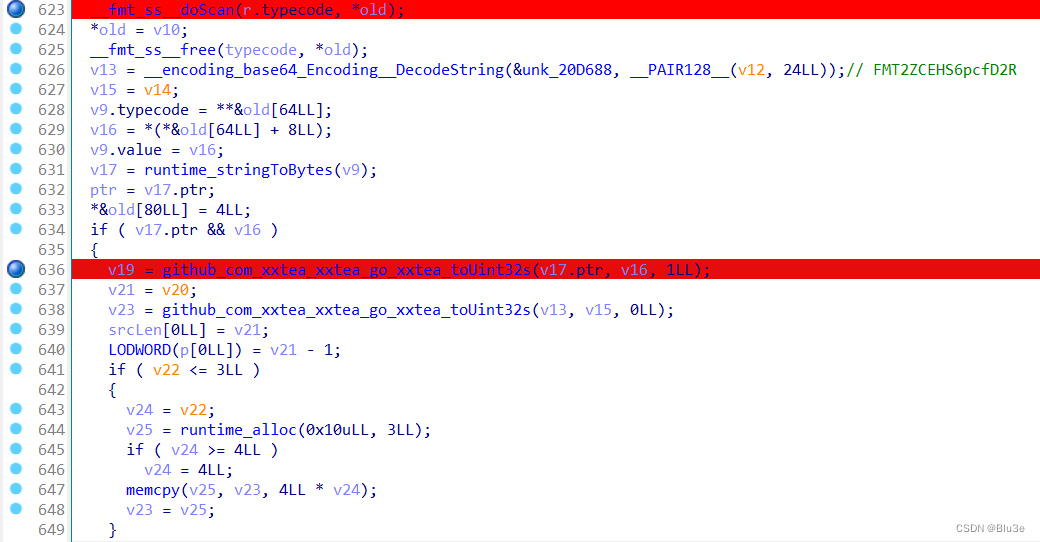
可以发现其中的字符串、密钥等都是用base64换表加密过的,
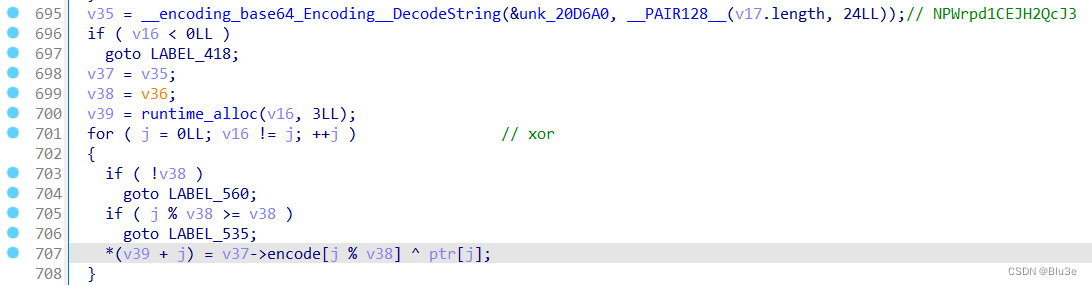
主要逻辑就是:先输入字符串,xxtea加密,异或,base58换表加密,最后生成qrcode
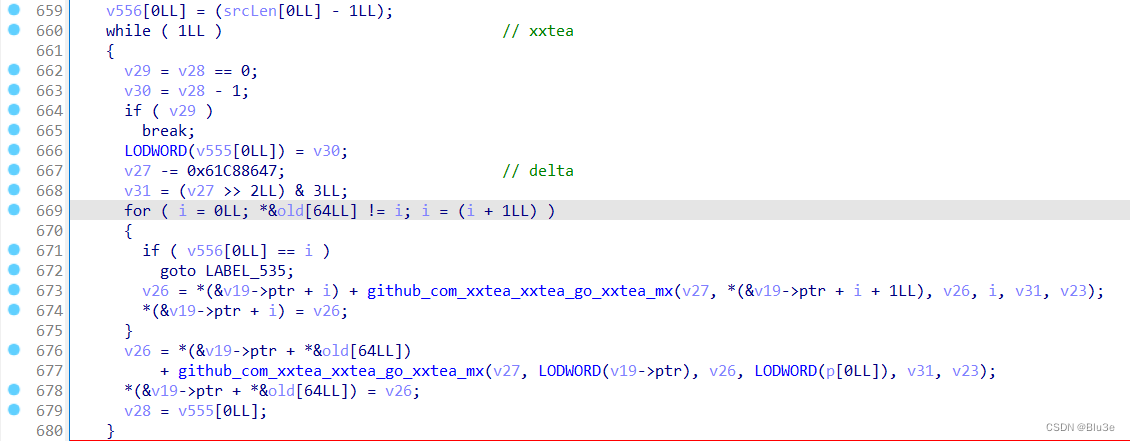
xxtea密钥及算法
异或
在这里发现base58表,猜测是base58算法

其中base64表为:
NkQxHyXmiZTReo05ngu7dlv1BpE2SfLwM@qr6IUjb4AaP9+z3cDVOCKhJYFWs8tG
base58表为:
nY7TwcE41bzWvMQZXa8fyeprJoBdmhsu9DqVgxRPtFLKN65UH2CikG3SAj
先用CQR扫一下二维码
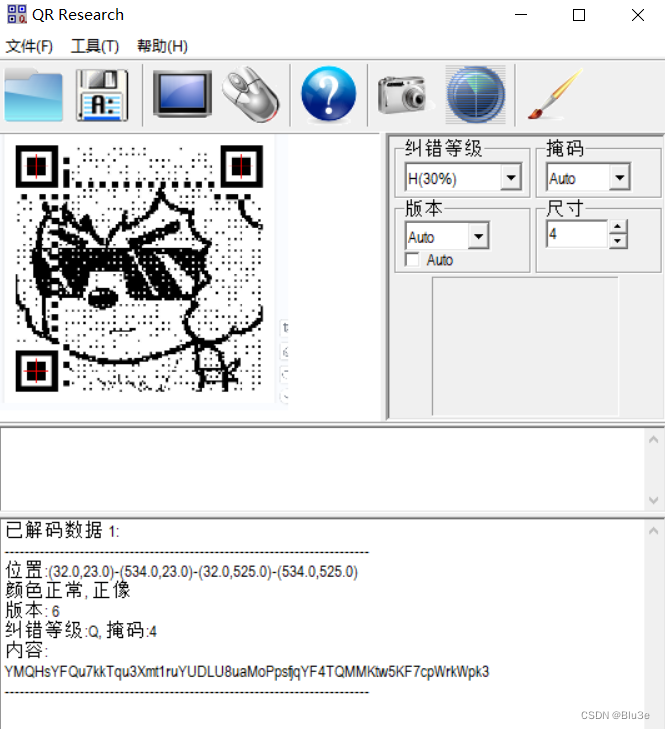
得到base58加密的字符串,先base58 - xor - to hex解密下
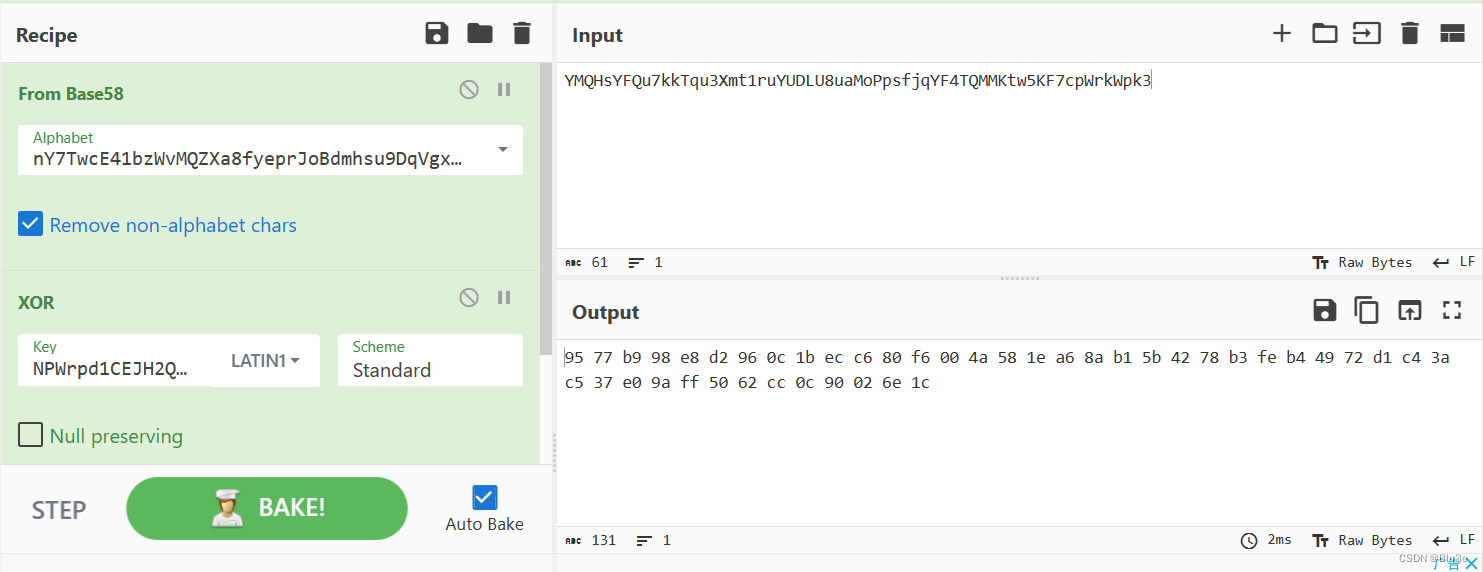
最后解xxtea
解题脚本:
#include <stdio.h>
#include <stdint.h>
#define DELTA 0x9E3779B9
#define MX (((z>>5^y<<2) + (y>>3^z<<4)) ^ ((sum^y) + (key[(p&3)^e] ^ z)))
void btea(uint32_t *v, int n, uint32_t const key[4])
{
uint32_t y, z, sum;
unsigned p, rounds, e;
if (n > 1) /* Coding Part */
{
rounds = 52/n+6;
sum = 0;
z = v[n-1];
do
{
sum += DELTA;
e = (sum >> 2) & 3;
for (p=0; p<n-1; p++)
{
y = v[p+1];
z = v[p] += MX;
}
y = v[0];
z = v[n-1] += MX;
}
while (--rounds);
// printf("\n%x\n",sum);
}
else if (n < -1) /* Decoding Part */
{
n = -n;
rounds = 52/n+6;
sum = 0x2e2ac13a;
y = v[0];
do
{
e = (sum >> 2) & 3;
for (p=n-1; p>0; p--)
{
z = v[p-1];
y = v[p] -= MX;
}
z = v[n-1];
y = v[0] -= MX;
sum -= DELTA;
}
while (--rounds);
// printf("\n%x\n",sum);
}
}
int main()
{
uint32_t v[11]= {0x98b97795,0x0c96d2e8,0x80c6ec1b,0x584a00f6,0xb18aa61e,0xb378425b,0x7249b4fe,0xc53ac4d1,0xff9ae037,0x0ccc6250,0x1c6e0290};
uint32_t const k[4]={0x32544d46,0x4845435a,0x63703653,0x52324466};
int i,n= 11;
btea(v, -n, k);
for(i=0;i<11;i++)
{
printf("%c",v[i]&0xff);
printf("%c",(v[i]&0xff00)%0xff);
printf("%c",(v[i]&0xff0000)%0xffff);
printf("%c",(v[i]&0xff000000)%0xffffff);//wmctf{YHNEBJx1WG0cKtZk8e2PNbxJa45WQF09}
}
return 0;
}
BabyAnti-2.0
用CE非预期解了,像BabyAnti-1.0一样先对libanticheat.so文件中的以下三个函数进行patch
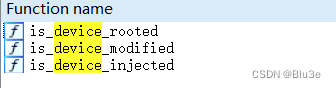
将is_device_rooted->sub_62FA0函数里的此处patch成0
if ( !*(_DWORD *)&v9[*(_QWORD *)(v6[0] - 24LL) + 7] )
*a1 = 0;
将is_device_modified函数里的这两处patch成0
*(_BYTE *)(qword_D41C8 + 1) = 1;
return 1;
将is_device_injected函数里的此处patch成0
if ( strstr(v3, "frida") )
*(_BYTE *)(v0 + 2) = 1;
在AntiCheatPlugin里会检测在暂停和恢复游戏后,前后的HP和Score值是否改变
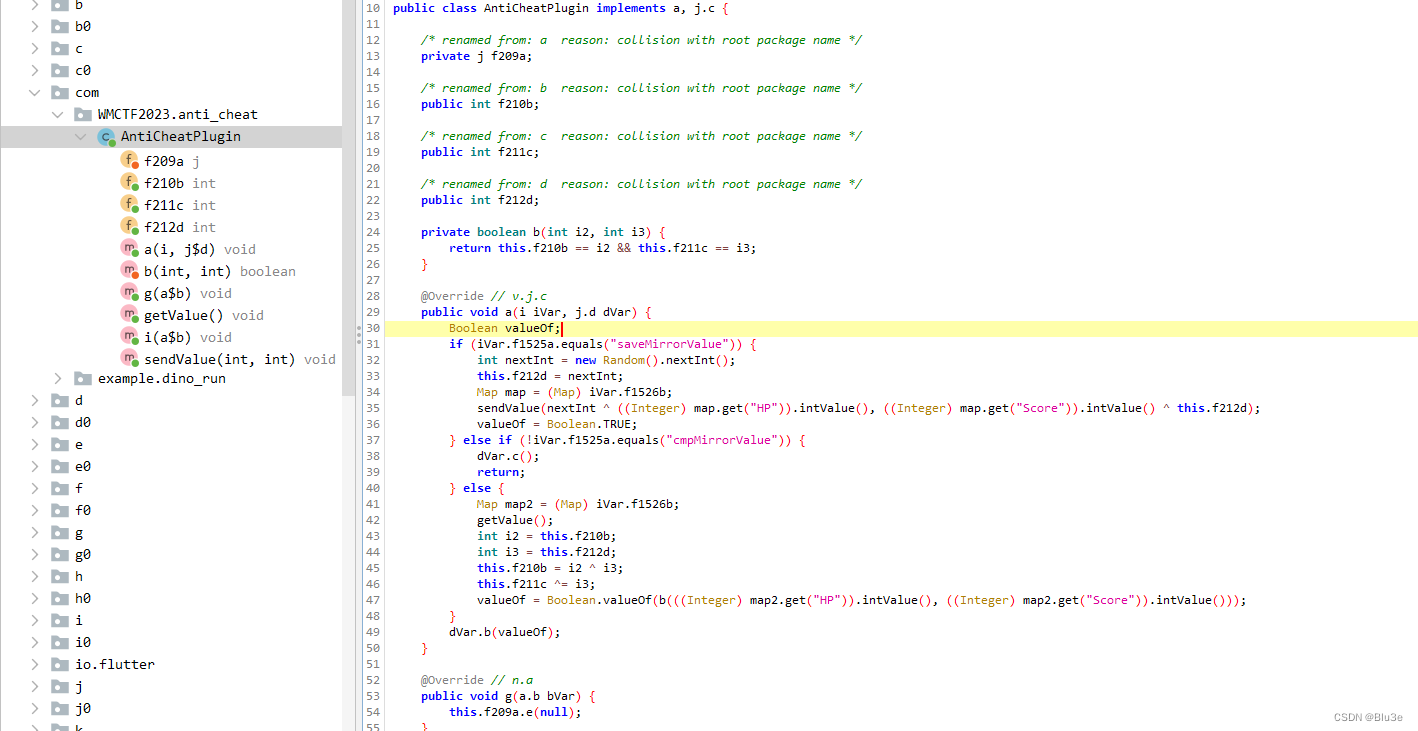
将以下代码patch下
private boolean b(int i2, int i3) {
return this.f210b == i2 && this.f211c == i3;
}
先使用baksmali工具将classes.dex转为smali文件:
java -jar baksmali-2.0.3.jar -x classes.dex
找到 b 方法
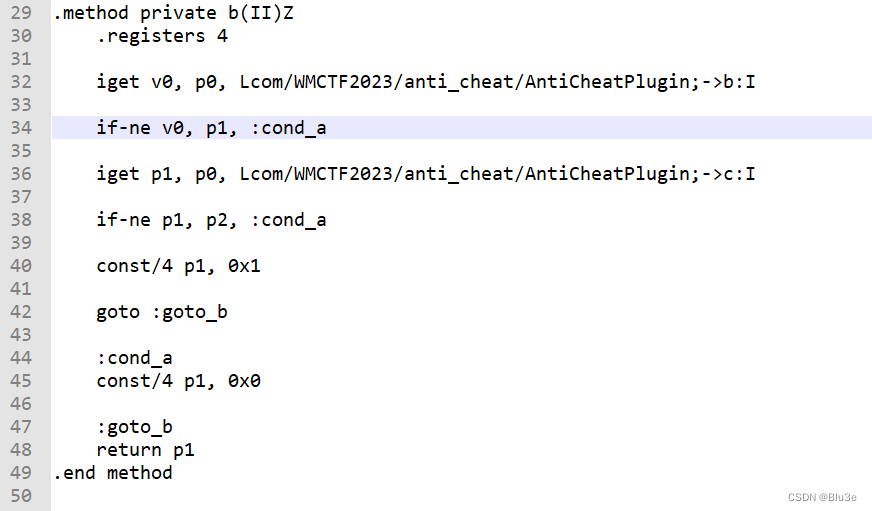
将 const/4 p1, 0x0 改为 const/4 p1, 0x1
然后使用smali-2.0.3.jar工具把smali文件转为dex文件:
java -jar smali-2.0.3.jar -o classes.dex out
然后用 ApkToolBox 重新打包成APK并签名
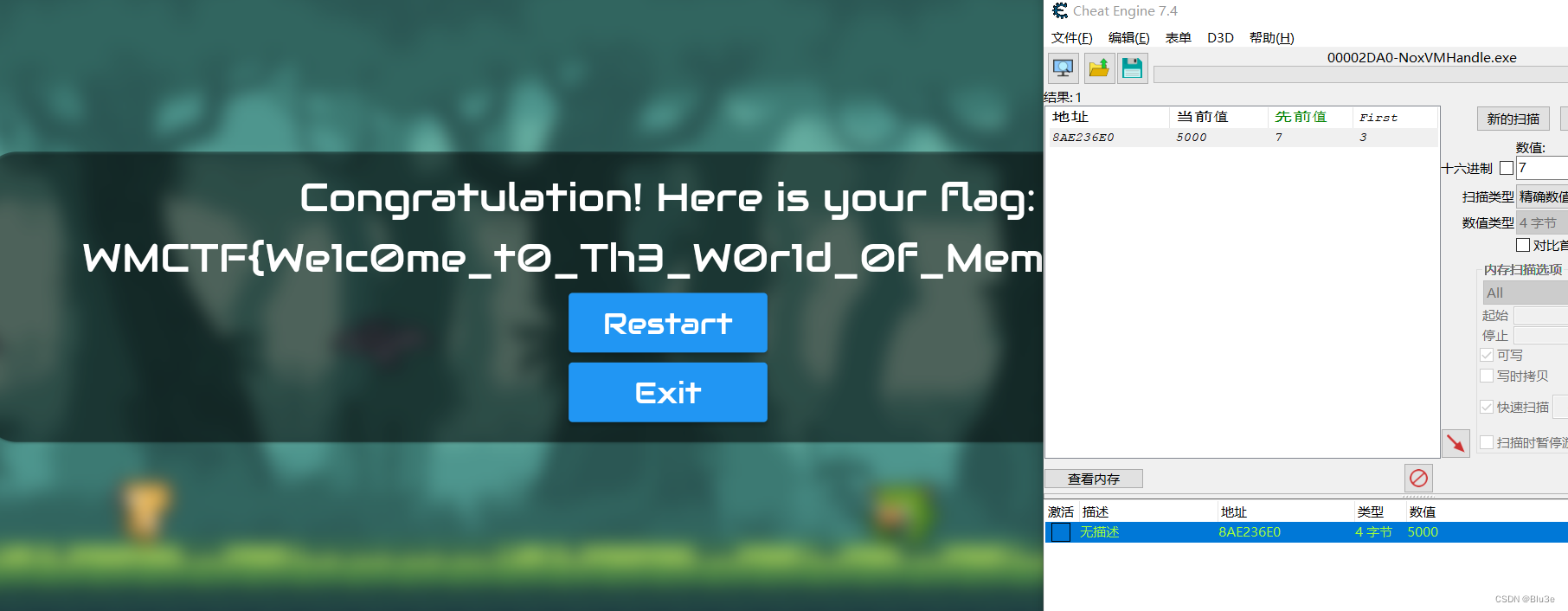
重新安装到夜神模拟器中,然后用CE进行修改
可以找到存放分值的对应地址

将数值改为5000后点击 Resume 即可得到flag
ezIos
(赛后出的)
把UnCrackable Level 3放入IDA中分析
在ViewController handleButtonClick函数里找到关键代码,其中发现许多异或运算
解密部分地方可以得到以下部分字符串
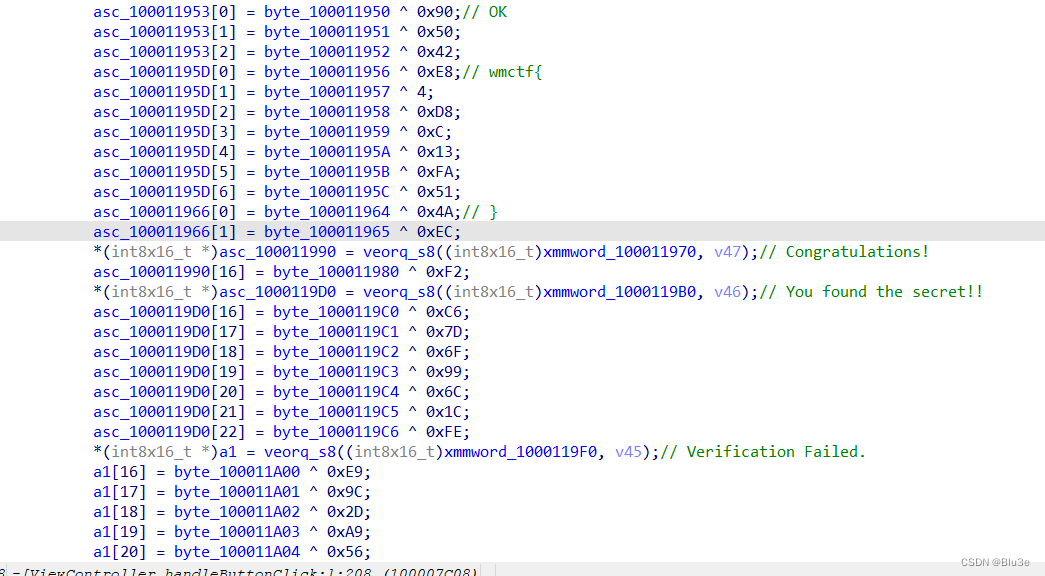
可以得知程序在运行时还原字符串
在该函数中找到sub_1000091E4函数进行分析
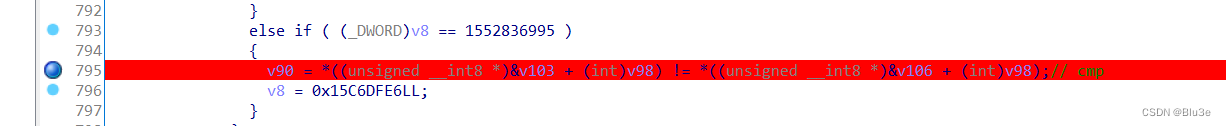
在sub_1000091E4函数里找到关键判断
在sub_1000091E4函数里找到sub_100004A9C函数和sub_100005434函数,
sub_100004A9C函数对输入的字符串进行RC4算法加密
sub_100005434函数用xtea算法还原出对比的字符
于是用qiling模拟执行,可以拿到密钥,用对比的字符RC4解密,也可以直接拿RC4最后异或的字符,和对比的字符进行异或,均可得到flag
from qiling import Qiling
from qiling.const import QL_VERBOSE
instructions_skip_list = [0x10000B888, 0x10000AE74, 0x10000BB4C, 0x10000BB74, 0x10000A404, 0x10000A418]
xor_key = []
cmp_key = []
def hook_code(ql, address, size):
# print('>>> Tracing instruction at 0x%x, instruction size = 0x%x' % (address, size))
if ql.arch.regs.arch_pc in instructions_skip_list:
ql.arch.regs.arch_pc += 4
elif ql.arch.regs.arch_pc == 0x100009D84:
print("CMP:", hex(ql.arch.regs.w8), hex(ql.arch.regs.w9))
cmp_key.append(ql.arch.regs.w8)
ql.arch.regs.w9 = ql.arch.regs.w8 # 将两个值patch成相等的值,因为flag挨个判断对错,避免字符错误后,拿不到后面的字符
elif ql.arch.regs.arch_pc == 0x10000B878: # _dyld_get_image_header 获取内存镜像模块基址
ql.arch.regs.x0 = 0x100000000
ql.arch.regs.arch_pc += size
# elif ql.arch.regs.arch_pc == 0x100005624:
# print(hex(ql.arch.regs.x5), hex(ql.arch.regs.x20), hex(ql.arch.regs.x26))
# print(ql.mem.read(ql.arch.regs.x20, 16)) # xtea_key = tfvq29bcom.runig
# print(hex(ql.arch.regs.w10))
# elif ql.arch.regs.arch_pc == 0x100005638:
# print(hex(ql.arch.regs.w10), hex(ql.arch.regs.w22)) # xtea v11=result[0],v12=result[1]
# elif ql.arch.regs.arch_pc == 0x100005648:
# print(hex(ql.arch.regs.w5)) # xtea_sum
# elif ql.arch.regs.arch_pc == 0x1000052C8:
# print(ql.mem.read(0x7ffd099ffd80, 16)) # rc4_key = tfvq29bcom.runig
elif ql.arch.regs.arch_pc == 0x1000053BC:
print("XOR:", hex(ql.arch.regs.w8), hex(ql.arch.regs.w9), hex(ql.arch.regs.w8 ^ ql.arch.regs.w9))
xor_key.append(ql.arch.regs.w8)
ql = Qiling(["./UnCrackable Level 3"], "./qiling/examples/rootfs/arm64_ios", verbose=QL_VERBOSE.OFF)
ql.mem.map(0x10000, 0x10000)
ql.arch.regs.x0 = 0x10000
ql.mem.write(ql.arch.regs.x0, b'1111111111111111111111111')
ql.hook_code(hook_code)
ql.run(0x1000091E4, 0x10000A998)
print(ql.arch.regs.x0)
print(cmp_key) # key='tfvq29bcom.runig',rc4解密
for i in range(len(cmp_key)):
print(chr(cmp_key[i] ^ xor_key[i]), end='')





















 1382
1382











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








