IDA反编译看一下,逻辑很简单,就是一个输入400个字符进行验证的程序,输入错误会直接退出,正确的话会输出 Correct
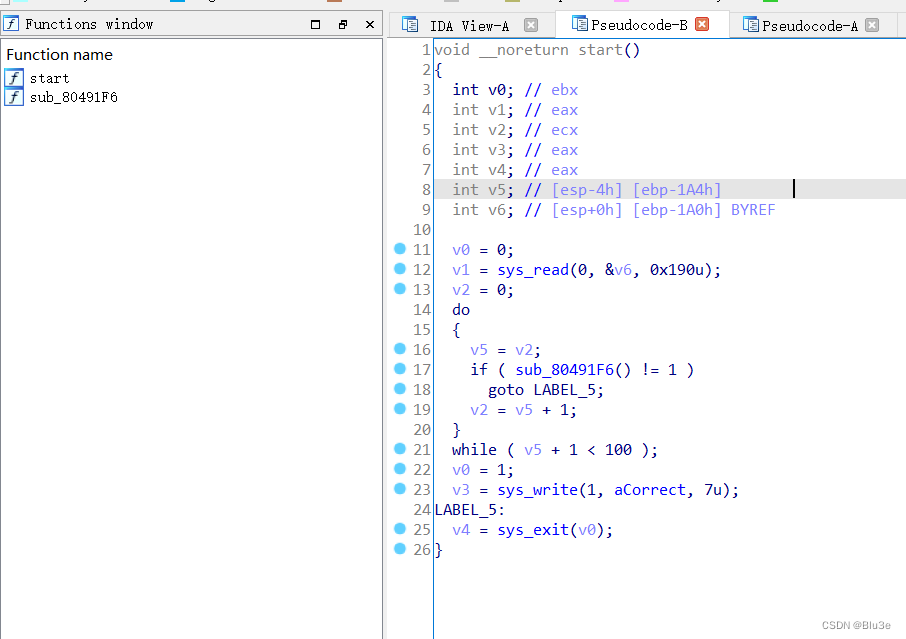
由于sub_80491F6函数太大,无法反编译,于是看汇编代码进行分析
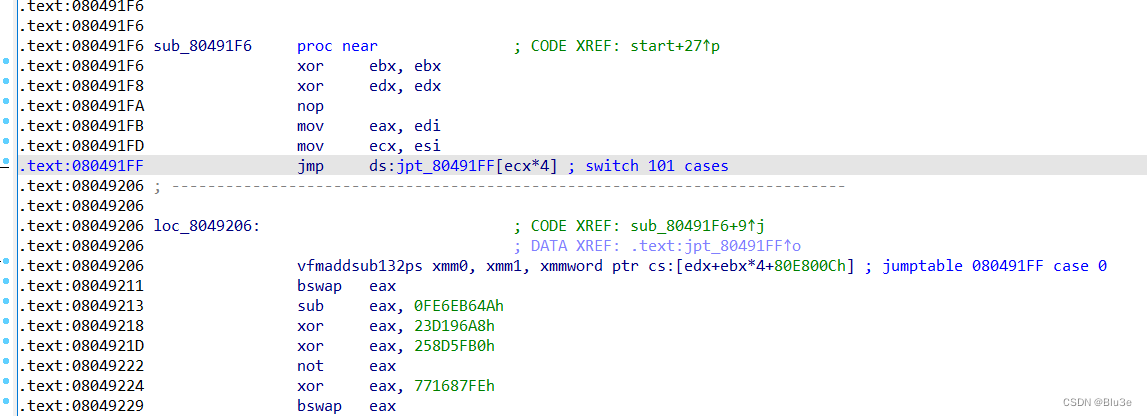
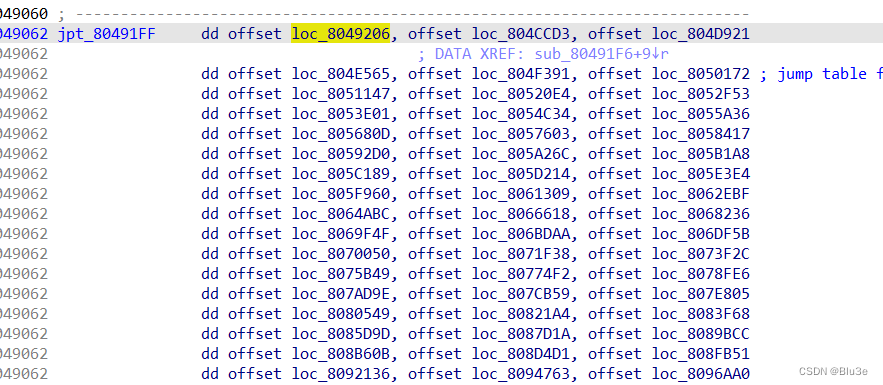
根据v2的值跳转到不同的函数进行操作
随便找个函数分析下
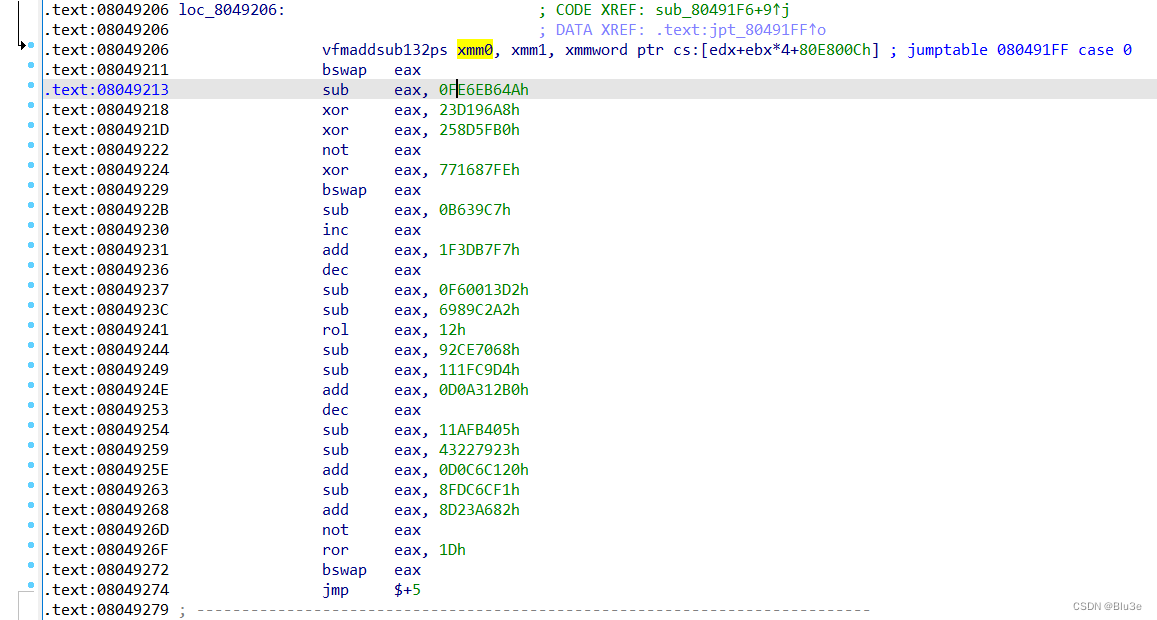
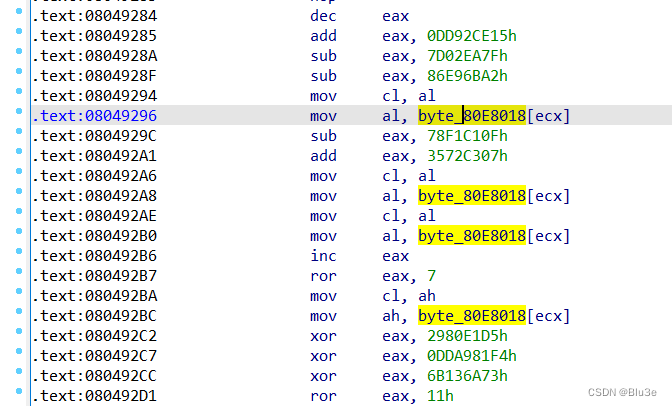
大致分析下,可以发现都是一些基础的指令,都是可以逆的,就是指令有点多,不太好分析
于是用qiling模拟执行下,但每次执行该指令就会出错
vfmaddsub132ps xmm0, xmm1, xmmword ptr cs:[edx+ebx*4+80E800Ch]
这条指令并不影响结果,于是我对其进行了patch,先提取出该指令的特征值
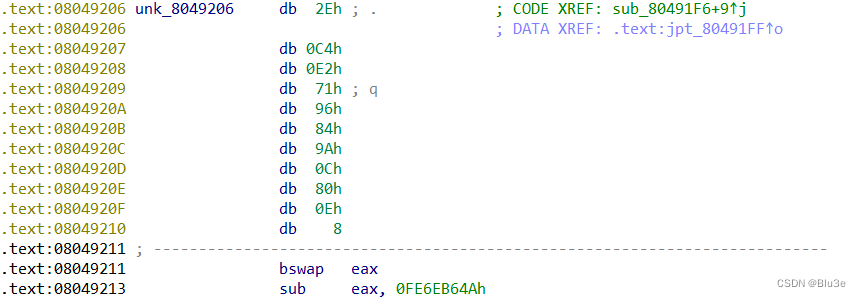
用 IDA_python 进行patch,将该指令nop掉
addr=0x8049206
list=[0x2E, 0xC4, 0xE2, 0x71, 0x96, 0x84, 0x9A, 0x0C, 0x80, 0x0E, 0x08]
while addr <=0x80E69EA:
flag=1
for j in range(len(list)):
if idc.get_wide_byte(addr+j)!=list[j]:
flag=0
break
if flag==1:
for j in range(len(list)):
ida_bytes.patch_byte(addr+j,0x90)
addr+=10
addr+=1
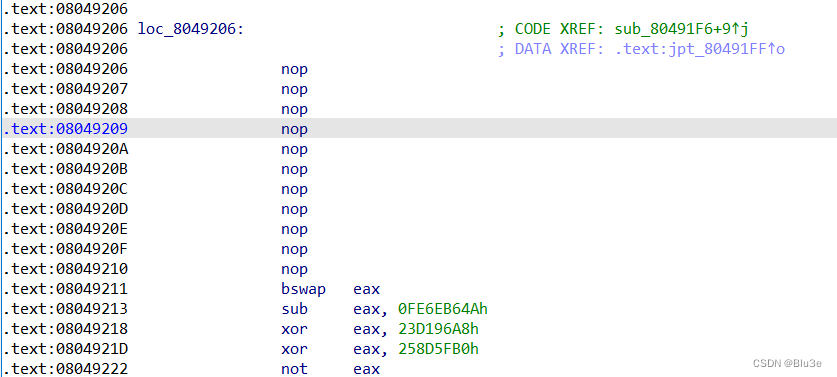
找到关键比较地方
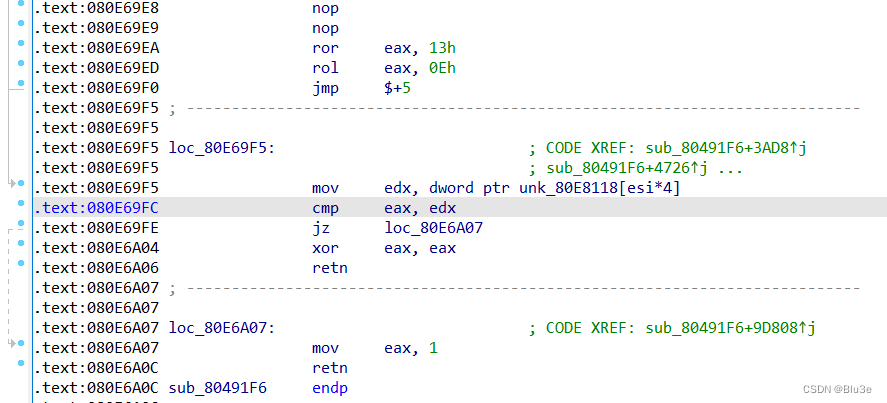
byte_80E8018数组已知,可以直接提取出来,unk_80E8118数组可以用qiling模拟执行直接提取相应的值,直接上qiling脚本
from qiling import Qiling
from qiling.const import QL_VERBOSE
from Crypto.Util.number import *
instructions_skip_list = []
read_flag = [0]
table = [0x65, 0xF2, 0xAA, 0x4F, 0x01, 0x89, 0x93, 0x3A, 0xC2, 0x08,
0x1C, 0xC3, 0x3B, 0x3F, 0x7B, 0x6F, 0x38, 0xFE, 0xDB, 0x7A,
0x90, 0x7F, 0x5F, 0x51, 0x4B, 0x3D, 0x17, 0x68, 0x80, 0x9B,
0x29, 0xC4, 0x88, 0x79, 0xF5, 0xCA, 0x28, 0x0F, 0x06, 0x2A,
0x70, 0x44, 0x67, 0x2F, 0x23, 0x8B, 0xB9, 0x74, 0x78, 0x0B,
0x72, 0x6A, 0x8D, 0x37, 0x1E, 0xFD, 0xAF, 0x4A, 0x50, 0x56,
0xA1, 0x20, 0xFF, 0xEB, 0x5E, 0xA3, 0xB7, 0x22, 0xF8, 0xDD,
0x6E, 0x6D, 0x59, 0xC6, 0xD1, 0x36, 0xE2, 0x19, 0x5D, 0xA9,
0xE5, 0x14, 0x83, 0x53, 0xD0, 0x9C, 0xBB, 0x87, 0x34, 0x58,
0xA5, 0x26, 0x8F, 0xA4, 0xAC, 0xBA, 0xD5, 0x76, 0x7C, 0x73,
0x1A, 0x57, 0x4E, 0x9F, 0x24, 0xB5, 0x97, 0x0A, 0x27, 0x5C,
0xE3, 0xBF, 0x5B, 0x13, 0x7E, 0x43, 0x04, 0x32, 0x1F, 0x00,
0x16, 0x02, 0x61, 0xA2, 0xD9, 0xAD, 0x91, 0xC1, 0xD4, 0xEF,
0x33, 0x85, 0xE0, 0x31, 0xF3, 0x47, 0x18, 0xEC, 0xF4, 0x48,
0xB4, 0x45, 0x3C, 0x86, 0xE4, 0x9E, 0x77, 0x12, 0xCB, 0x6C,
0x84, 0xBE, 0xC9, 0xA7, 0x35, 0xA8, 0x98, 0xEE, 0xDA, 0xFA,
0xE7, 0xA0, 0xC7, 0xBD, 0x4C, 0x8C, 0xFC, 0xAE, 0x0C, 0xF9,
0x41, 0x39, 0x4D, 0x69, 0x92, 0xC5, 0x25, 0x52, 0x07, 0x42,
0xCE, 0x2C, 0x0D, 0xD7, 0x63, 0xB0, 0xD2, 0x2B, 0x96, 0x94,
0xB8, 0xA6, 0x40, 0x8E, 0x11, 0xBC, 0x60, 0x9A, 0x82, 0xDF,
0x21, 0xD8, 0x7D, 0x5A, 0x2D, 0x71, 0x1B, 0x46, 0x1D, 0xE8,
0xCD, 0xE9, 0x54, 0xED, 0x81, 0xCF, 0xDE, 0x8A, 0x55, 0xDC,
0x15, 0x66, 0xB2, 0xC0, 0xEA, 0x3E, 0x95, 0x10, 0xD6, 0x6B,
0x05, 0xB1, 0x03, 0xC8, 0x99, 0x9D, 0xB3, 0xE6, 0xAB, 0xFB,
0xF6, 0xE1, 0xCC, 0xF1, 0x49, 0x09, 0xD3, 0xF7, 0xB6, 0x0E,
0x64, 0xF0, 0x62, 0x75, 0x2E, 0x30]
inp = []
def ROL(val, count):
return ((val >> (32 - count)) & 0xffffffff) | ((val << count) & 0xffffffff)
def ROR(val, count):
return ((val << (32 - count)) & 0xffffffff) | ((val >> count) & 0xffffffff)
def solve(ql, a):
i = 0
ql.arch.regs.eax = ql.arch.regs.edx
print(hex(ql.arch.regs.eax))
while i < len(a):
x = a[i].split()
if x[0] == 'rol':
a[i] = 'ql.arch.regs.eax = ROR(ql.arch.regs.eax, ' + x[-1] + ')'
exec(a[i])
elif x[0] == 'ror':
a[i] = 'ql.arch.regs.eax = ROL(ql.arch.regs.eax, ' + x[-1] + ')'
exec(a[i])
elif x[0] == 'xor':
a[i] = 'ql.arch.regs.eax ^= ' + x[-1]
# print(a[i])
exec(a[i])
elif x[0] == 'add':
a[i] = 'ql.arch.regs.eax -= ' + x[-1]
exec(a[i])
exec('ql.arch.regs.eax&=0xffffffff')
elif x[0] == 'sub':
a[i] = 'ql.arch.regs.eax += ' + x[-1]
exec(a[i])
exec('ql.arch.regs.eax&=0xffffffff')
elif x[0] == 'inc':
a[i] = 'ql.arch.regs.eax -= 1'
exec(a[i])
exec('ql.arch.regs.eax&=0xffffffff')
elif x[0] == 'dec':
a[i] = 'ql.arch.regs.eax += 1'
exec(a[i])
exec('ql.arch.regs.eax&=0xffffffff')
elif 'bswap' in a[i]:
a[i] = "ql.arch.regs.eax=bytes_to_long(long_to_bytes(ql.arch.regs.eax)[::-1].ljust(4,bytes([0])))"
exec(a[i])
elif 'not' in a[i]:
a[i] = 'ql.arch.regs.eax=(~ql.arch.regs.eax)&0xffffffff'
exec(a[i])
elif 'nop' in a[i] or 'jmp' in a[i]:
pass
elif 'mov cl, ah' in a[i + 1]:
a[i] = 'ah=(ql.arch.regs.eax&0xffff)//0x100\nah=table.index(ah)\nql.arch.regs.eax=ql.arch.regs.eax//0x10000*0x10000+ah*0x100+ql.arch.regs.eax%0x100'
exec(a[i])
i += 1
elif 'mov cl, al' in a[i + 1]:
a[i] = 'al=ql.arch.regs.eax%0x100\nal=table.index(al)\nql.arch.regs.eax=ql.arch.regs.eax//0x100*0x100+al'
exec(a[i])
i += 1
i += 1
# print(hex(ql.arch.regs.eax))
print(long_to_bytes(ql.arch.regs.eax)[::-1])
inp.append(ql.arch.regs.eax)
instructions_skip_list.clear()
def hook_code(ql, address, size, user_data):
buf = ql.mem.read(address, size)
asm = next(user_data.disasm(buf, address))
x = f"{asm.mnemonic} {asm.op_str}"
if read_flag[0] == 1:
instructions_skip_list.append(x) # 存储执行过的指令
if ql.arch.regs.eip == 0x08049026:
# print(hex(ql.arch.regs.edi))
pass
elif ql.arch.regs.eip == 0x80491FF:
read_flag[0] = 1
elif ql.arch.regs.eip == 0x80E69F5:
read_flag[0] = 0
elif ql.arch.regs.eip == 0x804901a: # 跳过sys_read()函数
ql.arch.regs.eip = 0x804901C
# 验证得到的字符串是否正确
# ql.mem.write(ql.arch.regs.esp, b"Eha1eNvFmgD4sZJHKJ3lsfszArr4HphX7kyGmygUEodK6PpaQ6Pj3kTyXvWVJBZL6RiNPwMn1kb0oeoSJ0EH6obmmRvvHlrvQsU8fM922HJkb98dNVUvYl5FReBCytwQ8zeOFD3Qc4OEkdLjX5riXhDYC5SiGbOektwQeNepzD3e87FzV2qJaTd9rVEWXGAVHtXrVX4JrZf6PlRJAUIZhzNlKlV4A8iRdlTFfLgWngtHoDT7GMscdePm0qH5XNfjUl50zKLN6OdFON1lLmoIIzUmhkfVGw16JtbCUW2sHUI6PB35KtNwNfNJa4lYu6QfhOaN7h2E1PvyuNHOGcBmlssNkGXzAfTuuWpYd7NtBPjHbL2et2afS8iXRXIyjUyAMFIyD2ZJ2S1ZwAXo")
elif ql.arch.regs.eip == 0x80E69FC:
if ql.arch.regs.eax == ql.arch.regs.edx:
instructions_skip_list.clear()
else:
solve(ql, instructions_skip_list[:-1][::-1]) # 将执行过的指令从后往前挨个逆运算
ql.arch.regs.eax = ql.arch.regs.edx # 对判断的数据patch成相等的值,保证程序正常运行,获取到结果
ql = Qiling(["./masterpiece"], "F:/桌面/qiling_test/qiling/examples/rootfs/x86_linux", verbose=QL_VERBOSE.OFF)
ql.arch.disassembler.detail = True
ql.mem.map(0x10000, 0x10000)
ql.hook_code(hook_code, user_data=ql.arch.disassembler)
ql.run(0x8049000, 0x8049060)
# ql.run(0x8050172, 0x80E69FE)
print()
input = b''
for i in range(len(inp)):
input += long_to_bytes(inp[i])[::-1]
print(input)
# Eha1eNvFmgD4sZJHKJ3lsfszArr4HphX7kyGmygUEodK6PpaQ6Pj3kTyXvWVJBZL6RiNPwMn1kb0oeoSJ0EH6obmmRvvHlrvQsU8fM922HJkb98dNVUvYl5FReBCytwQ8zeOFD3Qc4OEkdLjX5riXhDYC5SiGbOektwQeNepzD3e87FzV2qJaTd9rVEWXGAVHtXrVX4JrZf6PlRJAUIZhzNlKlV4A8iRdlTFfLgWngtHoDT7GMscdePm0qH5XNfjUl50zKLN6OdFON1lLmoIIzUmhkfVGw16JtbCUW2sHUI6PB35KtNwNfNJa4lYu6QfhOaN7h2E1PvyuNHOGcBmlssNkGXzAfTuuWpYd7NtBPjHbL2et2afS8iXRXIyjUyAMFIyD2ZJ2S1ZwAXo
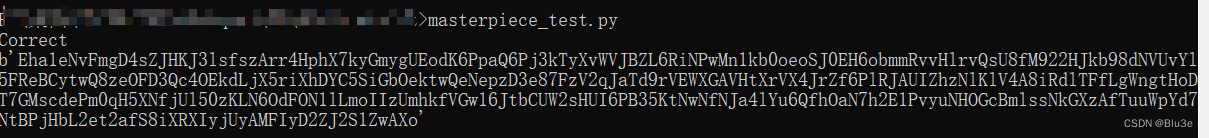
将得到的结果验证下
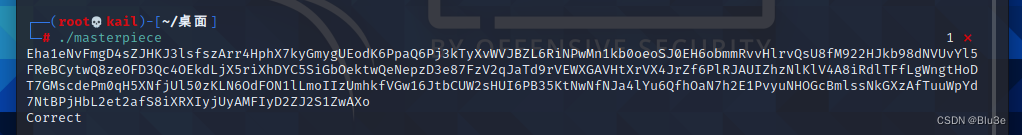
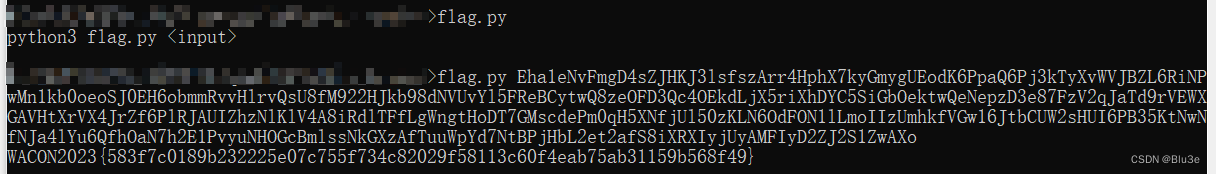
正确了,然后用题目附件给的 flag.py 跑一下,得到flag
























 950
950

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








