1、显示/etc/rc.d/rc.sysinit文件中以不区分大小的h开头的行;
[root@server ~]# grep -i "^h" /etc/rc.d/rc.sysinit
haha
HAHA
hehe
HEHE
2、显示/etc/passwd中以sh结尾的行;
[root@server ~]# egrep "sh$" /etc/passwd
root:x:0:0:root:/root:/bin/bash
fox:x:1000:1000:fox:/home/fox:/bin/bash
haha:x:1001:1001::/home/haha:/bin/bash
3、显示/etc/fstab中以#开头,且后面跟一个或多个空白字符,而后又跟了任意非空白字符的行;
[root@server ~]# egrep "^#[[:space:]]+.*" /etc/fstab
# /etc/fstab
# Created by anaconda on Wed Oct 11 13:19:56 2023
# Accessible filesystems, by reference, are maintained under '/dev/disk/'.
# See man pages fstab(5), findfs(8), mount(8) and/or blkid(8) for more info.
# After editing this file, run 'systemctl daemon-reload' to update systemd
# units generated from this file.
4、查找/etc/rc.d/rc.local中包含“以to开始并以to结尾”的字串行;
[root@server ~]# egrep "\<to\>" /etc/rc.d/rc.local
# It is highly advisable to create own systemd services or udev rules
# to run scripts during boot instead of using this file.
# In contrast to previous versions due to parallel execution during boot
# Please note that you must run 'chmod +x /etc/rc.d/rc.local' to ensure
5、查找/etc/inittab中含有“以s开头,并以d结尾的单词”模式的行;
[root@server ~]# egrep "\<s[a-z]*d\>" /etc/inittab
# Ctrl-Alt-Delete is handled by /usr/lib/systemd/system/ctrl-alt-del.target
# systemd uses 'targets' instead of runlevels. By default, there are two main targets:
6、查找ifconfig命令结果中的1-255之间的整数;
[root@server ~]# ifconfig | egrep -o -w "[1-9]{1}|[1-9]{1}[0-9]{1}|[1-2]{1}[0-9]{2}"
192
168
139
136
255
255
255
192
168
139
255
64
29
66
261
4
222
2
73
127
1
255
1
128
20
2
1
20
2
1
7、显示/var/log/secure文件中包含“Failed”或“FAILED”的行
[root@server ~]# egrep "Failed|FAILED" /var/log/secure
/var/log/secure中无此单词所以可以换一个
[root@server ~]# egrep "Received|disconnect" /var/log/secure
Dec 11 17:42:11 server polkitd[858]: Unregistered Authentication Agent for unix-session:c1 (system bus name :1.25, object path /org/freedesktop/PolicyKit1/AuthenticationAgent, locale zh_CN.UTF-8) (disconnected from bus)
Dec 12 19:45:27 server polkitd[859]: Unregistered Authentication Agent for unix-session:c1 (system bus name :1.25, object path /org/freedesktop/PolicyKit1/AuthenticationAgent, locale zh_CN.UTF-8) (disconnected from bus)
Dec 14 17:14:23 server polkitd[857]: Unregistered Authentication Agent for unix-session:c1 (system bus name :1.25, object path /org/freedesktop/PolicyKit1/AuthenticationAgent, locale zh_CN.UTF-8) (disconnected from bus)
Dec 14 17:27:49 server sshd[2246]: Received disconnect from 192.168.139.1 port 51384:11:
Dec 14 17:27:56 server sshd[2331]: Received disconnect from 192.168.139.1 port 51392:11:
Dec 14 17:30:21 server sshd[2429]: Received disconnect from 192.168.139.1 port 51411:11:
Dec 14 17:33:21 server sshd[2527]: Received disconnect from 192.168.139.1 port 51421:11:
Dec 14 17:33:38 server sshd[2617]: Received disconnect from 192.168.139.1 port 51452:11:
Dec 14 17:33:54 server polkitd[858]: Unregistered Authentication Agent for unix-session:c1 (system bus name :1.25, object path /org/freedesktop/PolicyKit1/AuthenticationAgent, locale zh_CN.UTF-8) (disconnected from bus)
Dec 14 17:56:37 server sshd[3419]: Received disconnect from 192.168.139.1 port 51693:11:
Dec 15 12:42:16 server sshd[1422]: Received disconnect from 192.168.139.1 port 58611:11:
Dec 16 17:07:04 server sshd[2084]: Received disconnect from 192.168.139.1 port 58161:11:
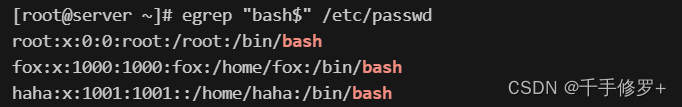
8、在/etc/passwd中取出默认shell为bash
[root@server ~]# egrep "bash$" /etc/passwd
root:x:0:0:root:/root:/bin/bash
fox:x:1000:1000:fox:/home/fox:/bin/bash
haha:x:1001:1001::/home/haha:/bin/bash
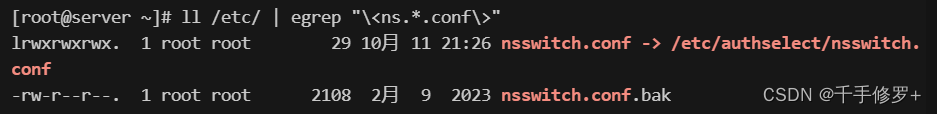
9、以长格式列出/etc/目录下以ns开头、.conf结尾的文件信息
[root@server ~]# ll /etc/ | egrep "\<ns.*.conf\>"
lrwxrwxrwx. 1 root root 29 10月 11 21:26 nsswitch.conf -> /etc/authselect/nsswitch.conf
-rw-r--r--. 1 root root 2108 2月 9 2023 nsswitch.conf.bak
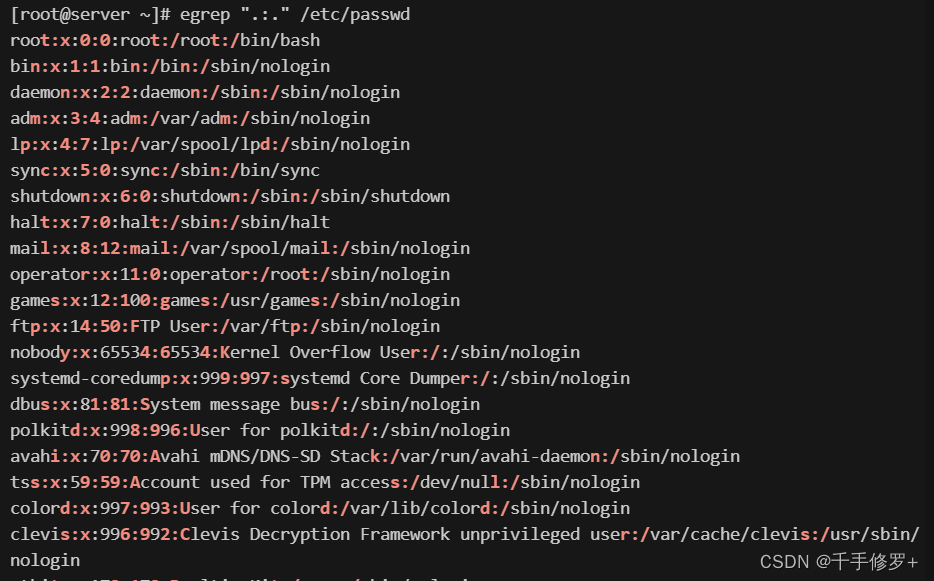
10、高亮显示passwd文件中冒号,及其两侧的字符
[root@server ~]# egrep ".:." /etc/passwd
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:65534:65534:Kernel Overflow User:/:/sbin/nologin
systemd-coredump:x:999:997:systemd Core Dumper:/:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
polkitd:x:998:996:User for polkitd:/:/sbin/nologin
avahi:x:70:70:Avahi mDNS/DNS-SD Stack:/var/run/avahi-daemon:/sbin/nologin
tss:x:59:59:Account used for TPM access:/dev/null:/sbin/nologin
colord:x:997:993:User for colord:/var/lib/colord:/sbin/nologin
clevis:x:996:992:Clevis Decryption Framework unprivileged user:/var/cache/clevis:/usr/sbin/nologin
rtkit:x:172:172:RealtimeKit:/proc:/sbin/nologin
sssd:x:995:991:User for sssd:/:/sbin/nologin
geoclue:x:994:990:User for geoclue:/var/lib/geoclue:/sbin/nologin
libstoragemgmt:x:988:988:daemon account for libstoragemgmt:/:/usr/sbin/nologin
systemd-oom:x:987:987:systemd Userspace OOM Killer:/:/usr/sbin/nologin
setroubleshoot:x:986:986:SELinux troubleshoot server:/var/lib/setroubleshoot:/sbin/nologin
pipewire:x:985:984:PipeWire System Daemon:/var/run/pipewire:/sbin/nologin
flatpak:x:984:983:User for flatpak system helper:/:/sbin/nologin
gdm:x:42:42::/var/lib/gdm:/sbin/nologin
cockpit-ws:x:983:982:User for cockpit web service:/nonexisting:/sbin/nologin
cockpit-wsinstance:x:982:981:User for cockpit-ws instances:/nonexisting:/sbin/nologin
gnome-initial-setup:x:981:980::/run/gnome-initial-setup/:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/usr/share/empty.sshd:/sbin/nologin
chrony:x:980:979:chrony system user:/var/lib/chrony:/sbin/nologin
dnsmasq:x:979:978:Dnsmasq DHCP and DNS server:/var/lib/dnsmasq:/sbin/nologin
tcpdump:x:72:72::/:/sbin/nologin
fox:x:1000:1000:fox:/home/fox:/bin/bash
apache:x:48:48:Apache:/usr/share/httpd:/sbin/nologin
nginx:x:978:975:Nginx web server:/var/lib/nginx:/sbin/nologin
mysql:x:27:27:MySQL Server:/var/lib/mysql:/sbin/nologin
haha:x:1001:1001::/home/haha:/bin/bash
11、匹配/etc/services中开头结尾字母一样的单词
[root@server ~]# egrep -o -w "(^[a-z])\w*\1" /etc/services
discard
discard
telnet
telnet
router
socks
socks
netmon
netmon
corbaloc
amanda
amanda
prsvp
prsvp
wnn4_Tw
discard
discard
mpm
mpm
mpm
mpm
mpm
mpm
isi
isi
file.txt文件内容:
48 Dec 3BC1977 LPSX 68.00 LVX2A 138
483 Sept 5AP1996 USP 65.00 LVX2C 189
47 Oct 3ZL1998 LPSX 43.00 KVM9D 512
219 dec 2CC1999 CAD 23.00 PLV2C 68
484 nov 7PL1996 CAD 49.00 PLV2C 234
483 may 5PA1998 USP 37.00 KVM9D 644
216 sept 3ZL1998 USP 86.00 KVM9E 234
[root@server ~]# vim file.txt
48 Dec 3BC1977 LPSX 68.00 LVX2A 138
483 Sept 5AP1996 USP 65.00 LVX2C 189
47 Oct 3ZL1998 LPSX 43.00 KVM9D 512
219 dec 2CC1999 CAD 23.00 PLV2C 68
484 nov 7PL1996 CAD 49.00 PLV2C 234
483 may 5PA1998 USP 37.00 KVM9D 644
216 sept 3ZL1998 USP 86.00 KVM9E 234
1含有“48”字符串的行的总数
[root@server ~]# grep -c "48" file.txt
4
2显示含有“48”字符串的所有行的行号
[root@server ~]# grep -n "48" file.txt
1:48 Dec 3BC1977 LPSX 68.00 LVX2A 138
2:483 Sept 5AP1996 USP 65.00 LVX2C 189
5:484 nov 7PL1996 CAD 49.00 PLV2C 234
6:483 may 5PA1998 USP 37.00 KVM9D 644
3精确匹配只含有“48字符串的行
[root@server ~]# grep -o -n "48" file.txt
1:48
2:48
5:48
6:48
4抽取代码为484和483的城市位置
[root@server ~]# egrep "\<(483|484)\>" file.txt
483 Sept 5AP1996 USP 65.00 LVX2C 189
484 nov 7PL1996 CAD 49.00 PLV2C 234
483 may 5PA1998 USP 37.00 KVM9D 644
5显示行首不是4或8
[root@server ~]# egrep "^[^(48)]" file.txt
219 dec 2CC1999 CAD 23.00 PLV2C 68
216 sept 3ZL1998 USP 86.00 KVM9E 234
6显示含有九月份(Sept)的行
[root@server ~]# egrep -i "sept" file.txt
483 Sept 5AP1996 USP 65.00 LVX2C 189
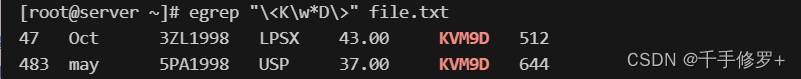
7显示以K开头,以D结尾的所有代码
[root@server ~]# egrep "\<K\w*D\>" file.txt
47 Oct 3ZL1998 LPSX 43.00 KVM9D 512
483 may 5PA1998 USP 37.00 KVM9D 644
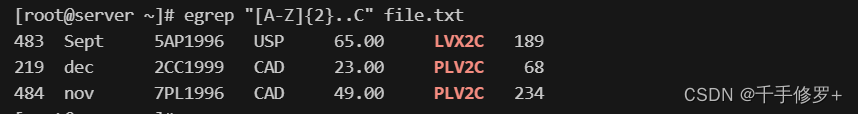
8显示头两个是大写字母,中间至少两个任意,并以C结尾的代码
[root@server ~]# egrep "[A-Z]{2}..C" file.txt
483 Sept 5AP1996 USP 65.00 LVX2C 189
219 dec 2CC1999 CAD 23.00 PLV2C 68
484 nov 7PL1996 CAD 49.00 PLV2C 234
9查询所有以5开始以1996或1998结尾的所有记录
[root@server ~]# egrep "[A-Z]{2}..C" file.txt
483 Sept 5AP1996 USP 65.00 LVX2C 189
219 dec 2CC1999 CAD 23.00 PLV2C 68
484 nov 7PL1996 CAD 49.00 PLV2C 234
1、显示/etc/passwd文件中以bash结尾的行;
[root@server ~]# egrep "bash$" /etc/passwd
root:x:0:0:root:/root:/bin/bash
fox:x:1000:1000:fox:/home/fox:/bin/bash
haha:x:1001:1001::/home/haha:/bin/bash
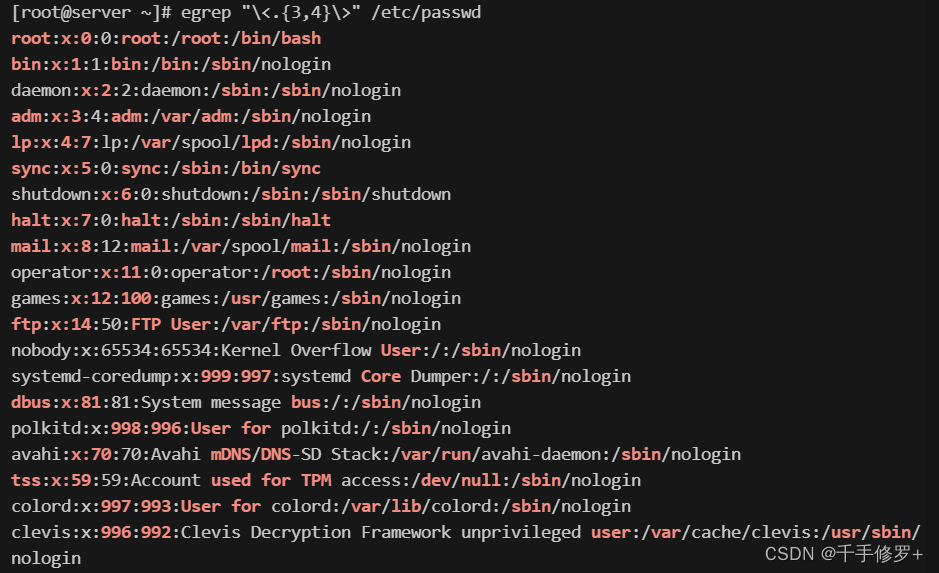
2、找出/etc/passwd文件中的三位或四位数;
[root@server ~]# egrep "\<.{3,4}\>" /etc/passwd
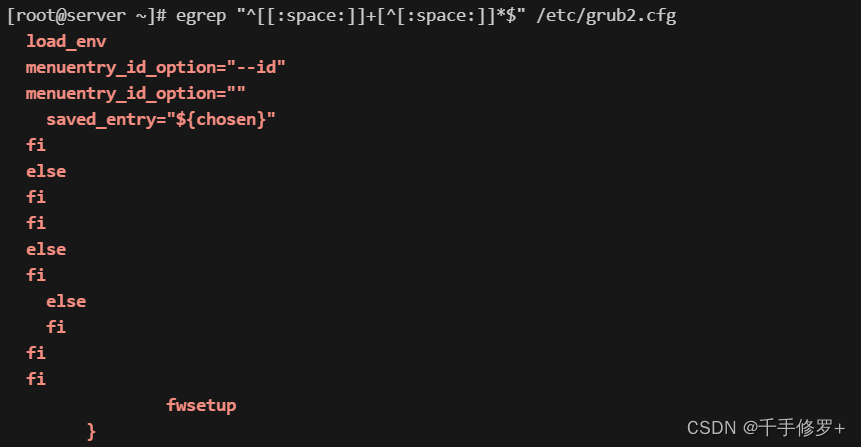
3、找出/etc/grub2.cfg文件中,以至少一个空白字符开头,后面又跟了非空白字符的行
[root@server ~]# egrep "^[[:space:]]+[^[:space:]]*$" /etc/grub2.cfg
4、找出"netstat -tan”命令的结果中,以‘LISTEN’后跟0或多个空白字符结尾的行;
[root@server ~]# netstat -tan | egrep "LISTEN[[:space:]]*$"
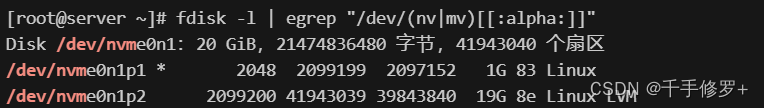
5、找出"fdisk -l“命令的结果中,包含以/dev/后跟sd或hd及一个字母的行;
[root@server ~]# fdisk -l | egrep "/dev/(sd|hd)[[:alpha:]]" 这里没有结果可以换一个
[root@server ~]# fdisk -l | egrep "/dev/(nv|mv)[[:alpha:]]"
6、找出”ldd /usr/bin/cat“命令的结果中文件路径;
[root@server ~]# ldd /usr/bin/cat | egrep -o "/[^ ]*"
7、找出/proc/meminfo文件中,所有以大写或小写s开头的行;至少用三种方式实现;
方法1:[root@server ~]# egrep -i "^s" /proc/meminfo
方法2:[root@server ~]# egrep "^[Ss]" /proc/meminfo
方法3:[root@server ~]# egrep "^(S|s)" /proc/meminfo
8、显示当前系统上root、centos或spark用户的相关信息;
[root@server ~]# egrep "^(root|centos|spark)" /etc/passwd
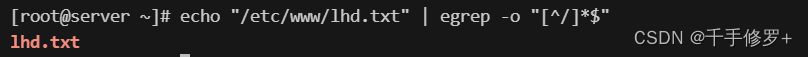
9、echo输出一个绝对路径,使用egrep取出其基名;
[root@server ~]# echo "/etc/www/lhd.txt" | egrep -o "[^/]*$"
10、找出ifconfig命令结果中的1-255之间的整数;
[root@server ~]# ifconfig | egrep -o -w "[1-9]{1}|[1-9]{1}[0-9]{1}|[1-2]{1}[0-9]{2}"
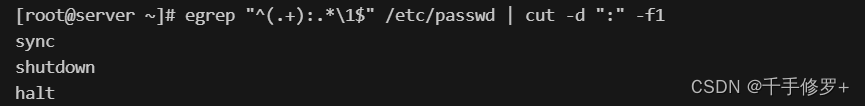
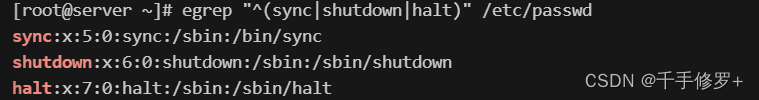
11、找出系统中其用户名与shell名相同的用户。
[root@server ~]# egrep "^(.+):.*\1$" /etc/passwd | cut -d ":" -f1
验证其结果:
[root@server ~]# egrep "^(sync|shutdown|halt)" /etc/passwd










































 1598
1598











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








