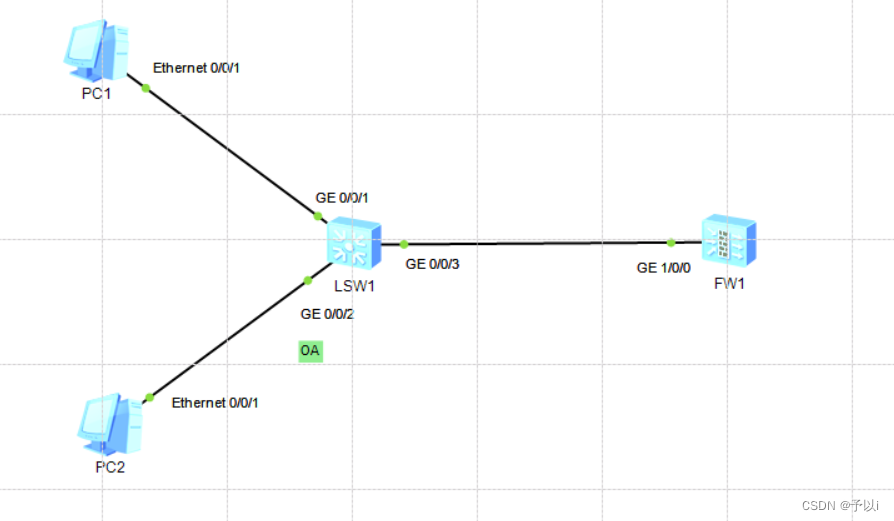
实验目的
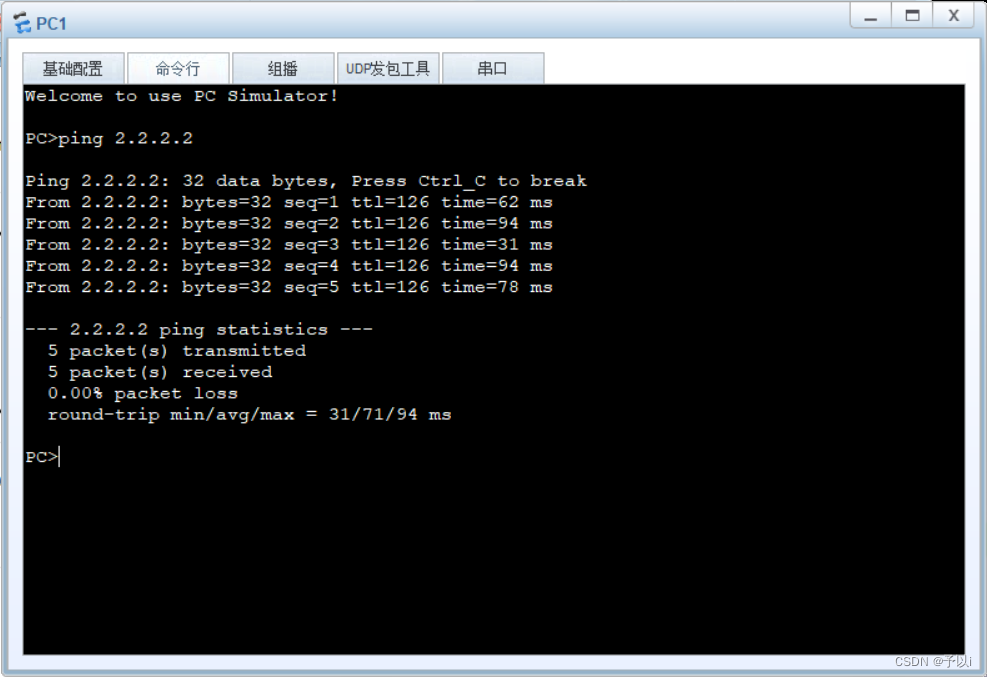
实例OA内用户流量去PC1,走防火墙过滤
实验过程
a.交换机创建VLAN,VLANif,配置接口类型,绑定实例
SW1
[S1]vlan batch 10 20
interface GigabitEthernet0/0/1
port link-type access
port default vlan 10
interface GigabitEthernet0/0/2
port link-type access
port default vlan 20
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 10 20
ip vpn-instance oa
ipv4-family
route-distinguisher 1:1
interface Vlanif20
ip binding vpn-instance oa
ip address 2.2.2.254 255.255.255.0
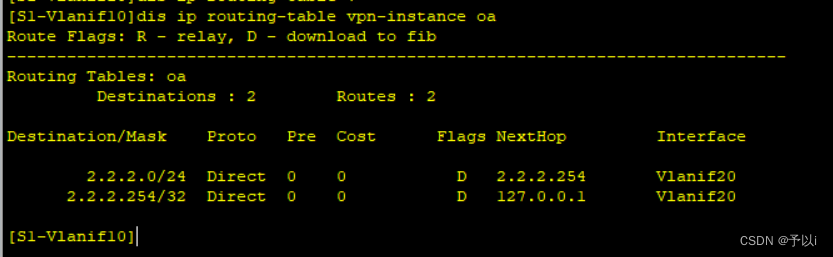
此时交换机全局下有1.1.1.0/24路由
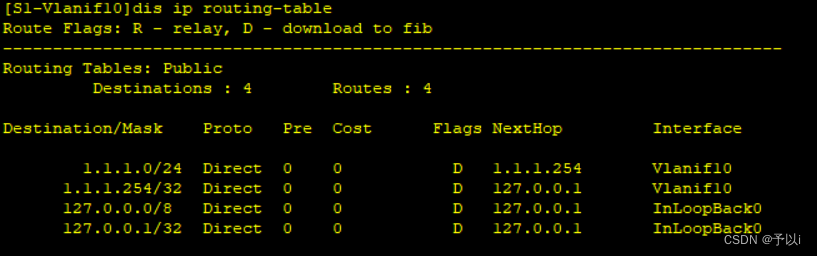
2.2.2.0/24的路由在实例OA里
b.防火墙放通VLAN,创建虚墙,绑定实例,放通虚墙策略
FW
interface GigabitEthernet1/0/0
portswitch
undo shutdown
port link-type trunk
port trunk allow-pass vlan 10 20
vsys name vsys1 1
assign vlan 10
assign vlan 20
interface Vlanif10
ip binding vpn-instance vsys1
ip address 1.1.1.21 255.255.255.0
interface Vlanif20
ip binding vpn-instance vsys1
ip address 2.2.2.22 255.255.255.0
[USG6000V1]switch vsys vsys1
[USG6000V1-vsys1]firewall zone trust
[USG6000V1-vsys1-zone-trust]add interface Vlanif 10
[USG6000V1-vsys1-zone-trust]add interface Vlanif 20
rule name xu
source-zone trust
destination-zone trust
service icmp
service ospf
service udp
action permit
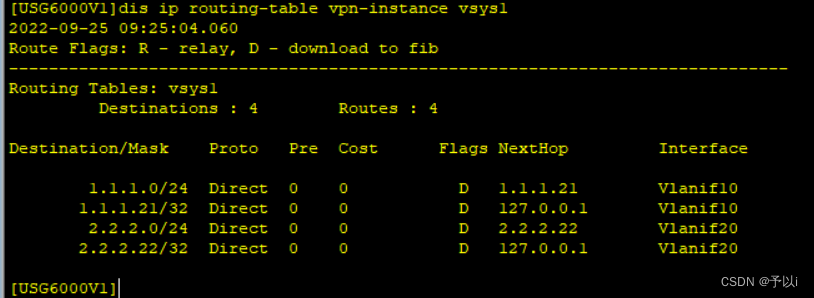
上下联路由都在虚墙上
c.通过ospf互通路由
SW
ospf 1 router-id 1.1.1.1
area 0.0.0.0
[S1-Vlanif10]ospf enable 1 ar 0
ospf 2 router-id 1.1.1.1 vpn-instance oa
area 0.0.0.0
interface Vlanif20
ip binding vpn-instance oa
ip address 2.2.2.254 255.255.255.0
ospf enable 2 area 0.0.0.0
FW
ospf 1 router-id 2.2.2.2 vpn-instance vsys1
area 0.0.0.0
interface Vlanif10
ip binding vpn-instance vsys1
ip address 1.1.1.21 255.255.255.0
ospf enable 1 area 0.0.0.0
#
interface Vlanif20
ip binding vpn-instance vsys1
ip address 2.2.2.22 255.255.255.0
ospf enable 1 area 0.0.0.0
查看邻居情况
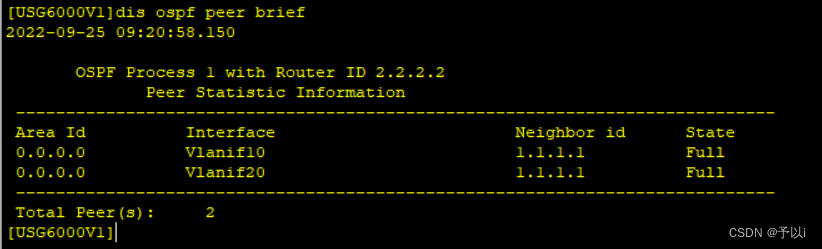
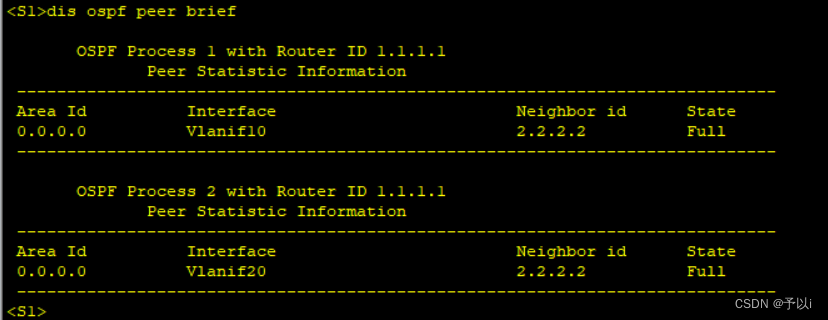
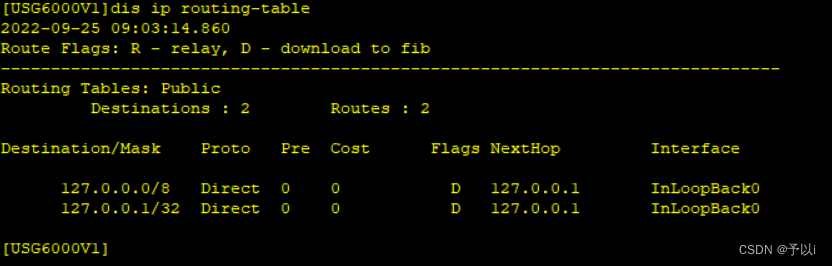
查看路由
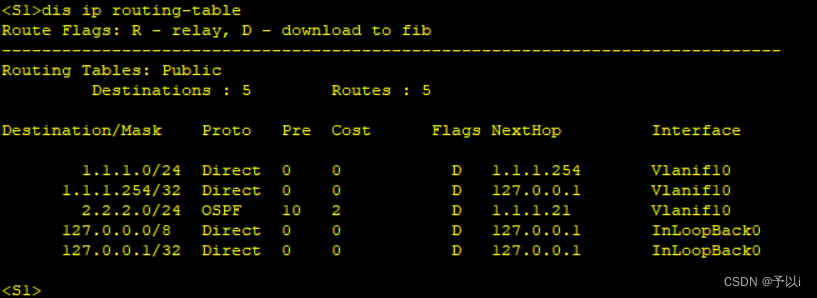
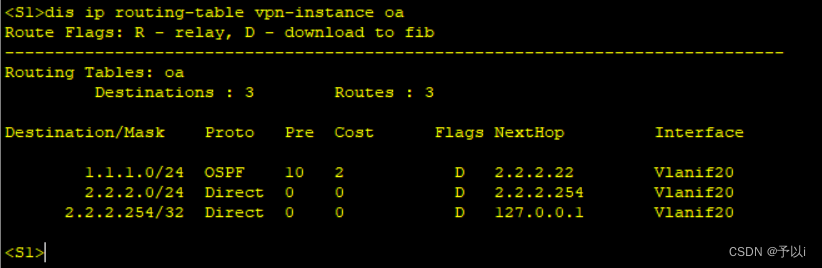
都学到了对方的路由。
























 9389
9389











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








