1.[NPUCTF2020]你好sao啊
ida64位,无壳
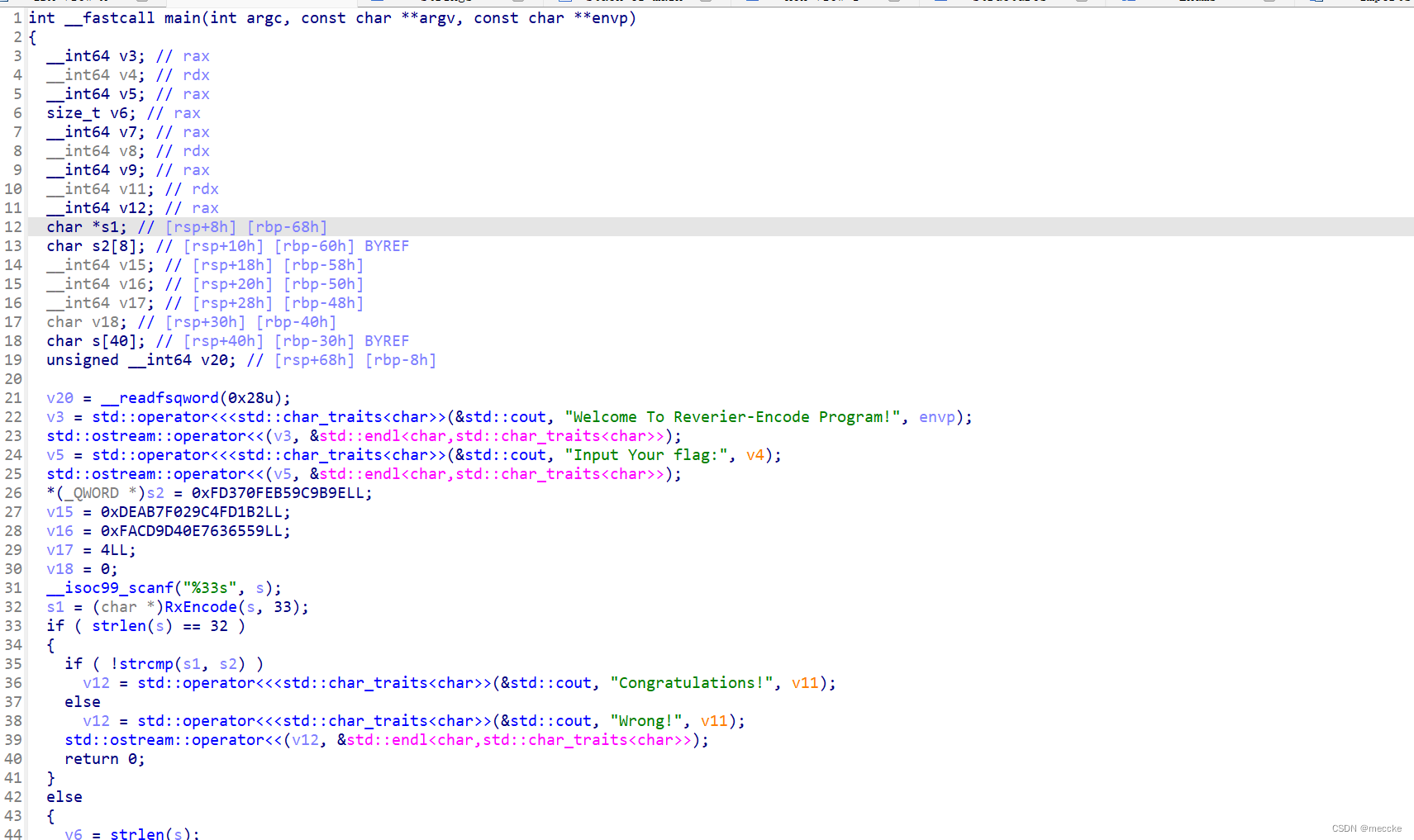
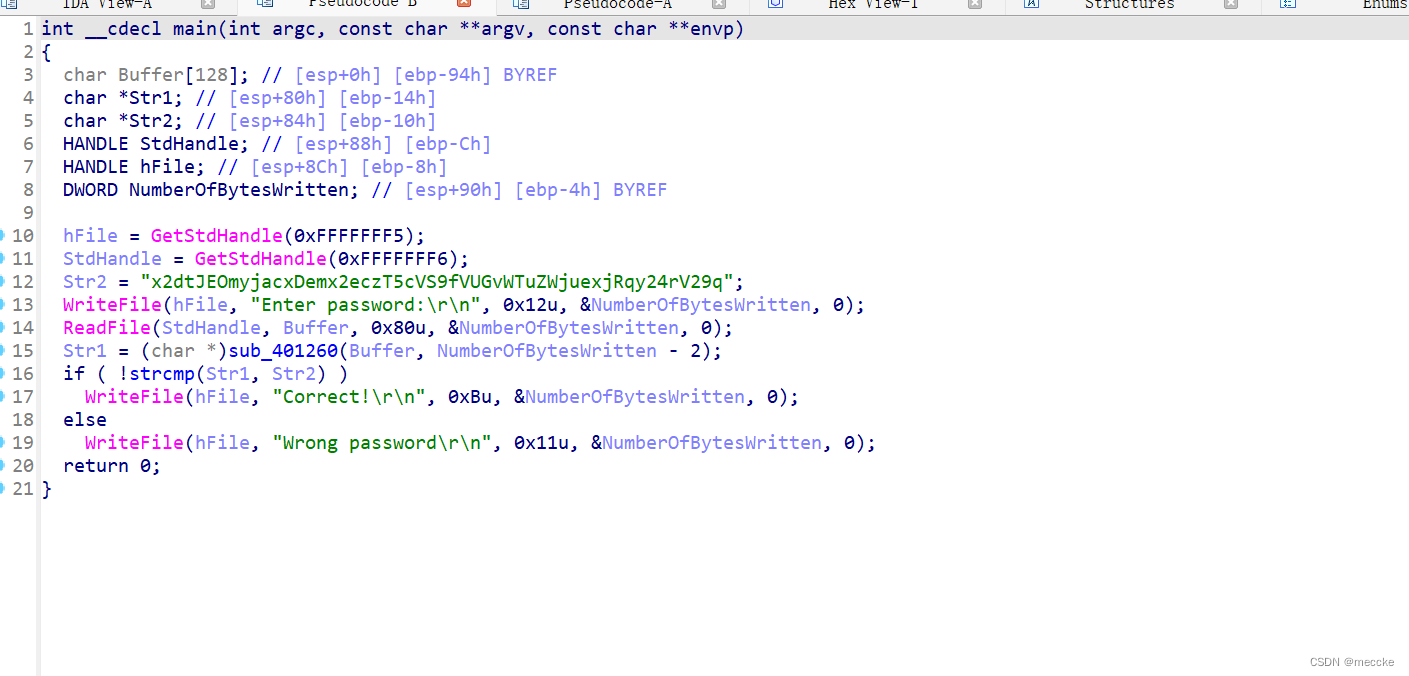
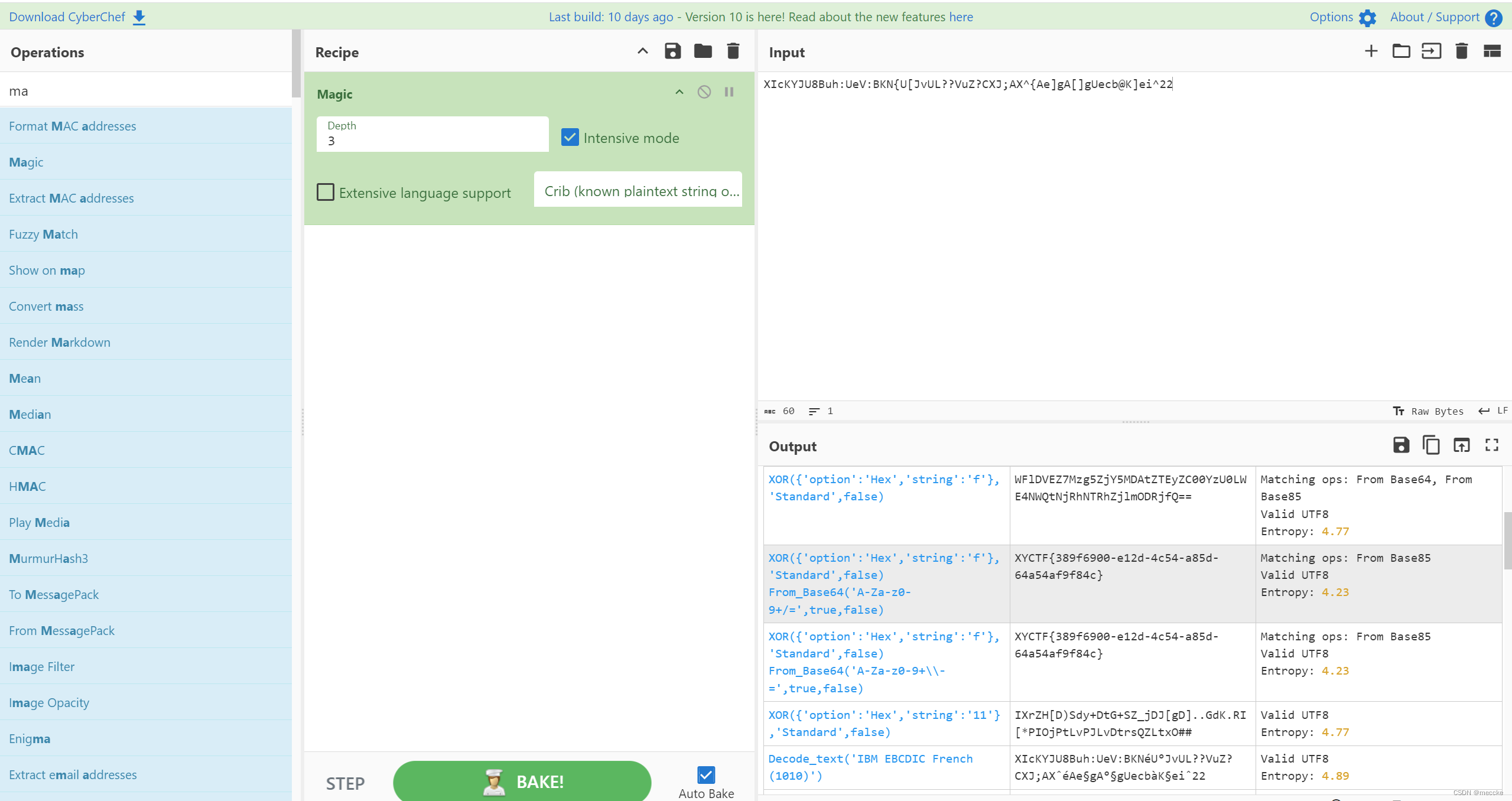
查看主函数,留个心眼看了一下各个变量的位置
这几个是挨着的
继续分析函数
对S1和S2进行了对比,s1是将输入进行了加密
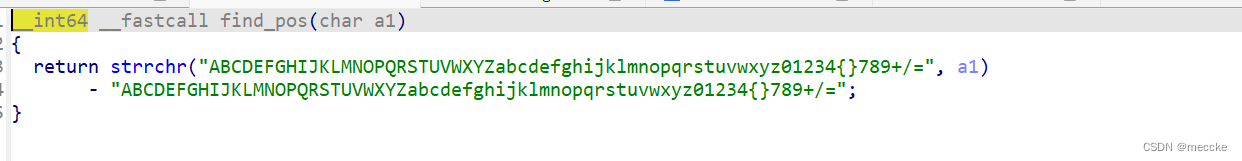
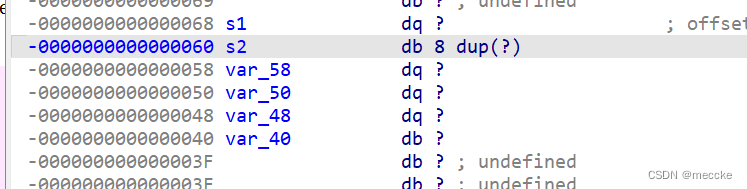
依次点进去,发现是base64变表加密
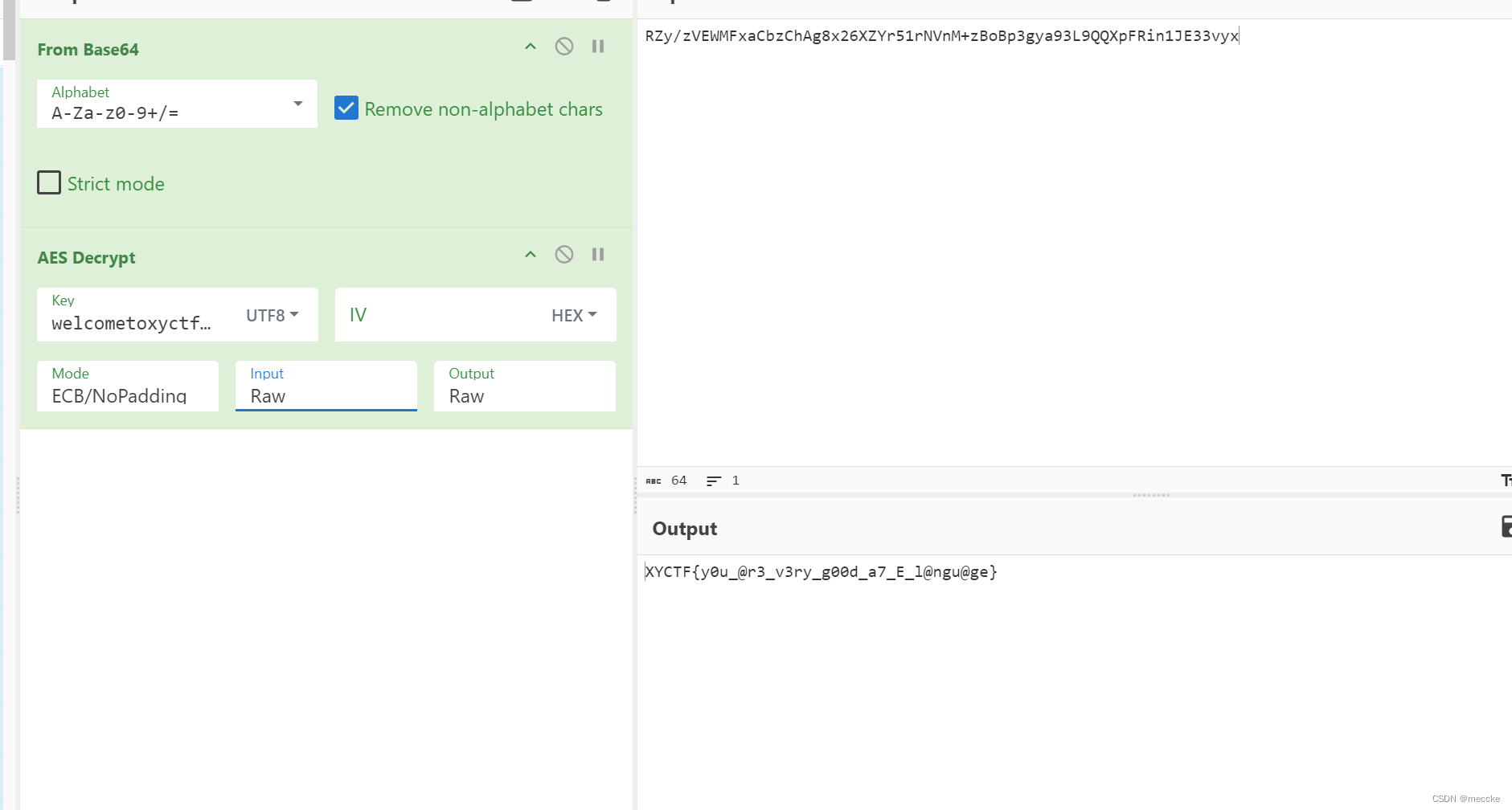
s2是一串十六进制数,python搞起来怪麻烦的,正好试试新工具
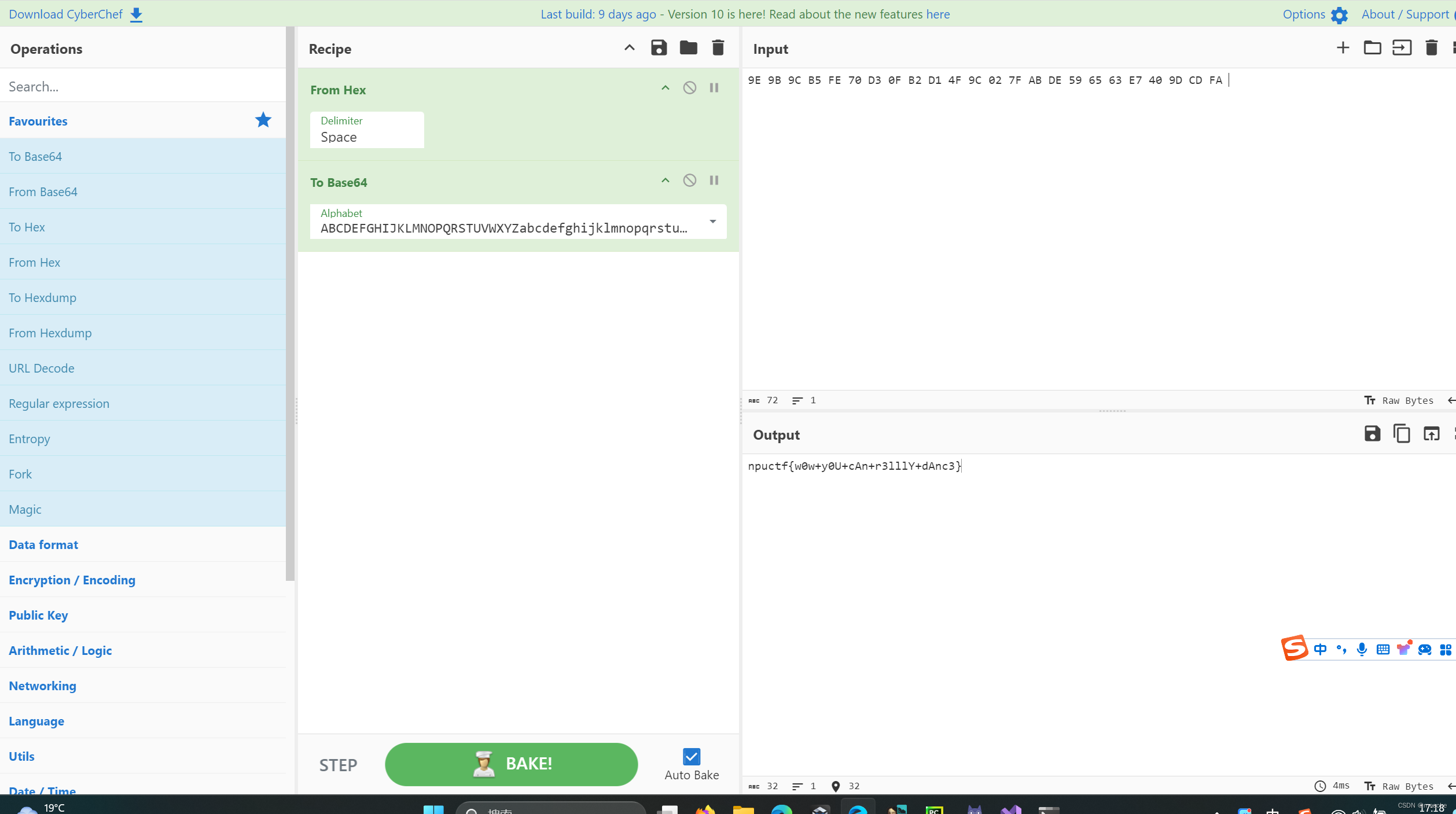
厨子真是个好人
[WUSTCTF2020]level1
下载附件,两个文件
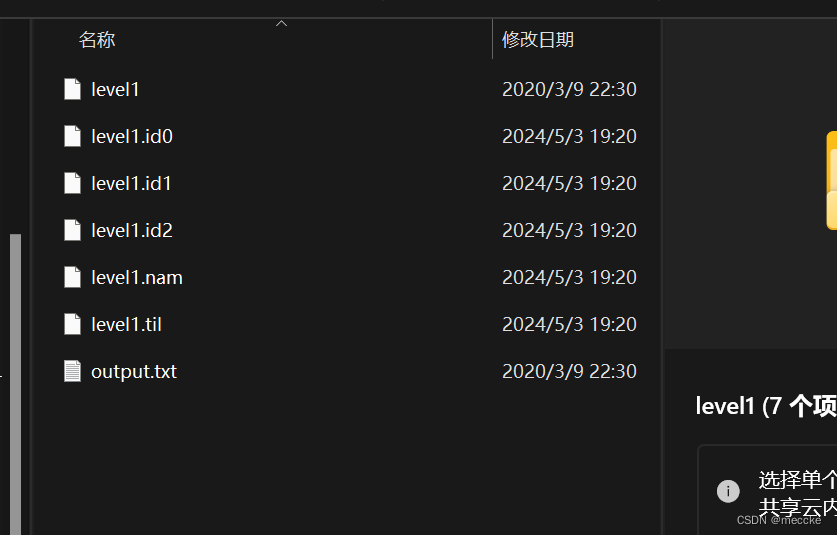
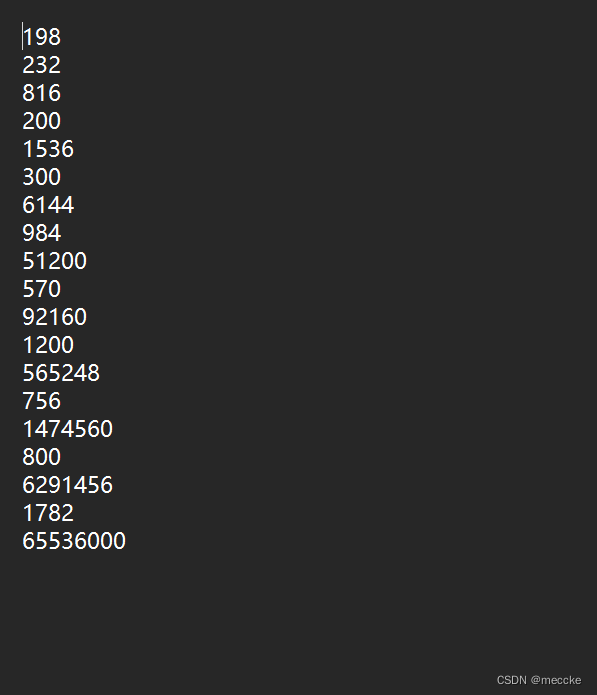
有一个output,猜测是程序运行后输出的内容
不是enc文件,能打开,不错
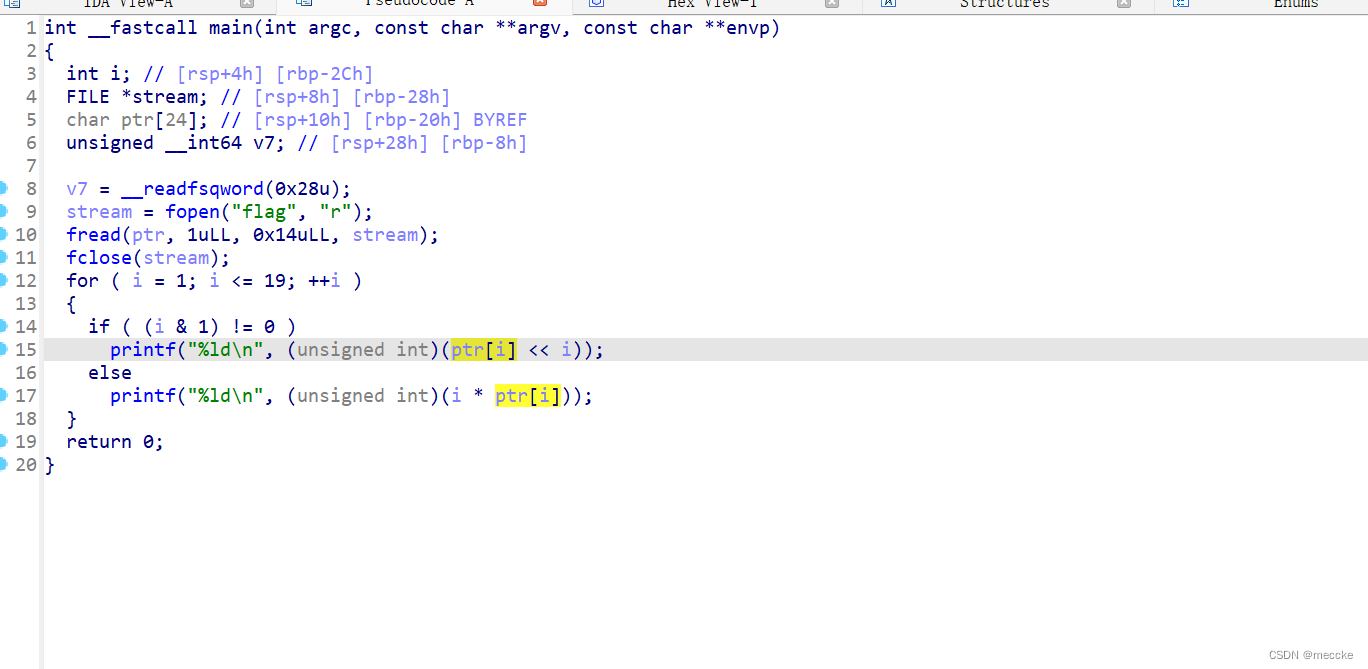
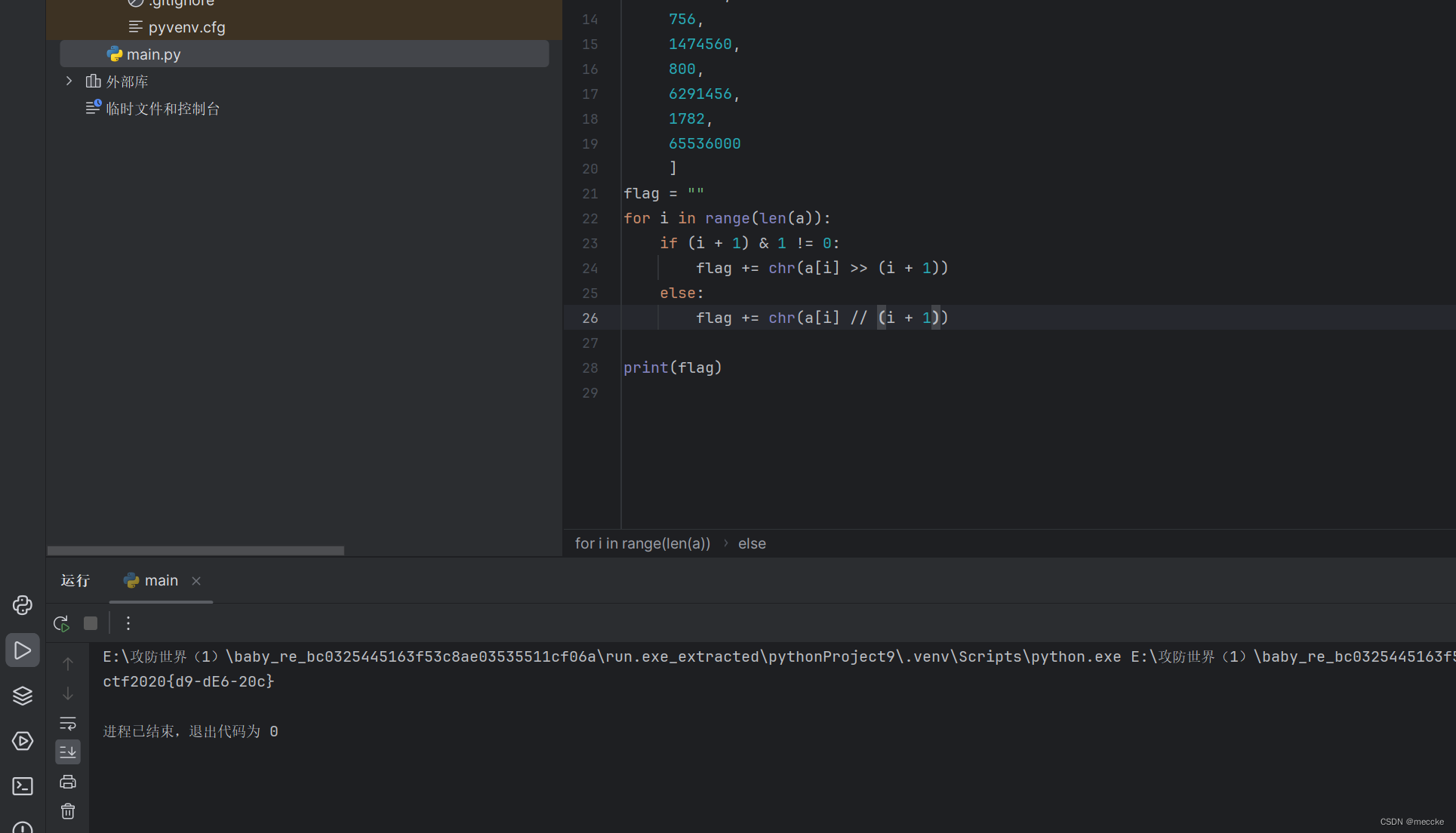
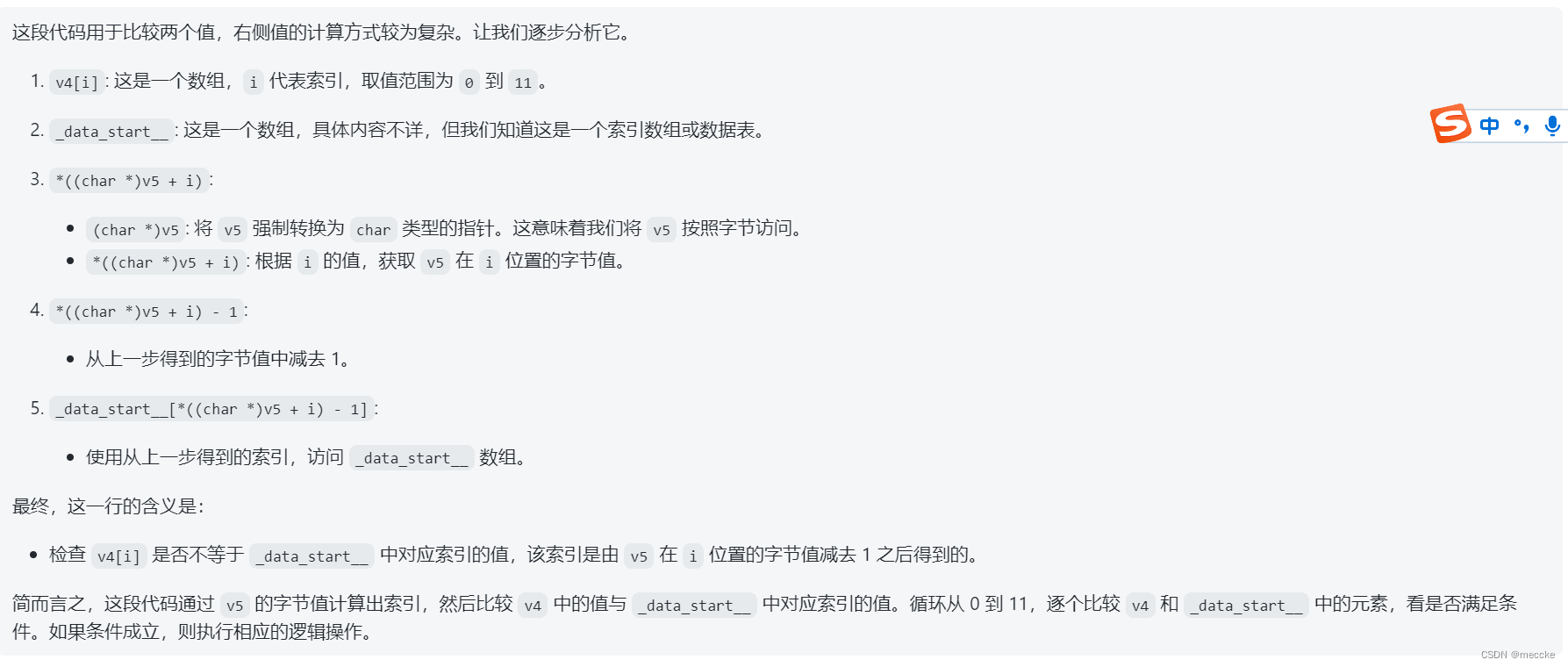
发现读写输入之类的函数,根据主函数写代码
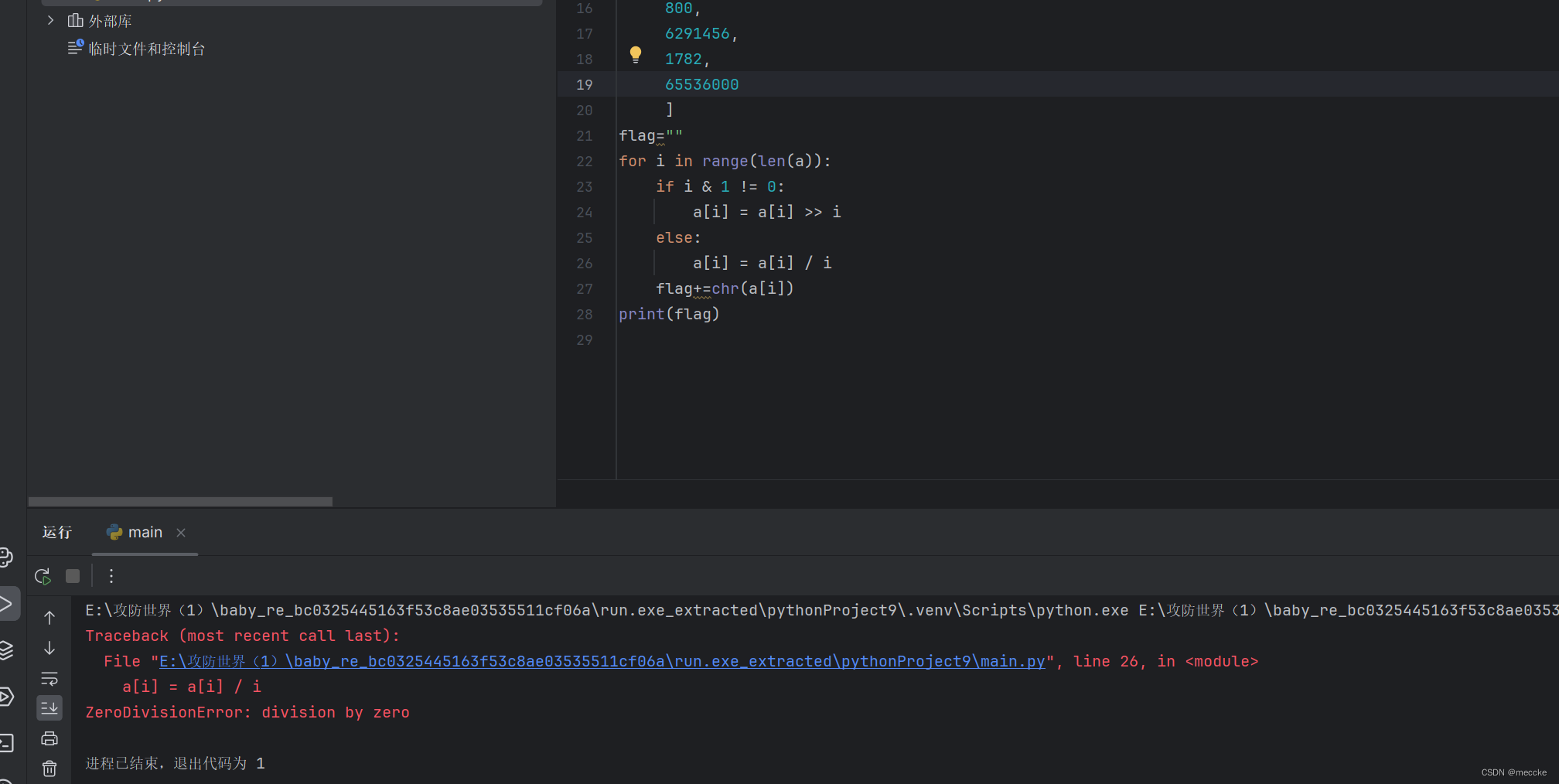
有个问题,i是从0开始的,所以要把i改成i+1,且字符串转化要是整数
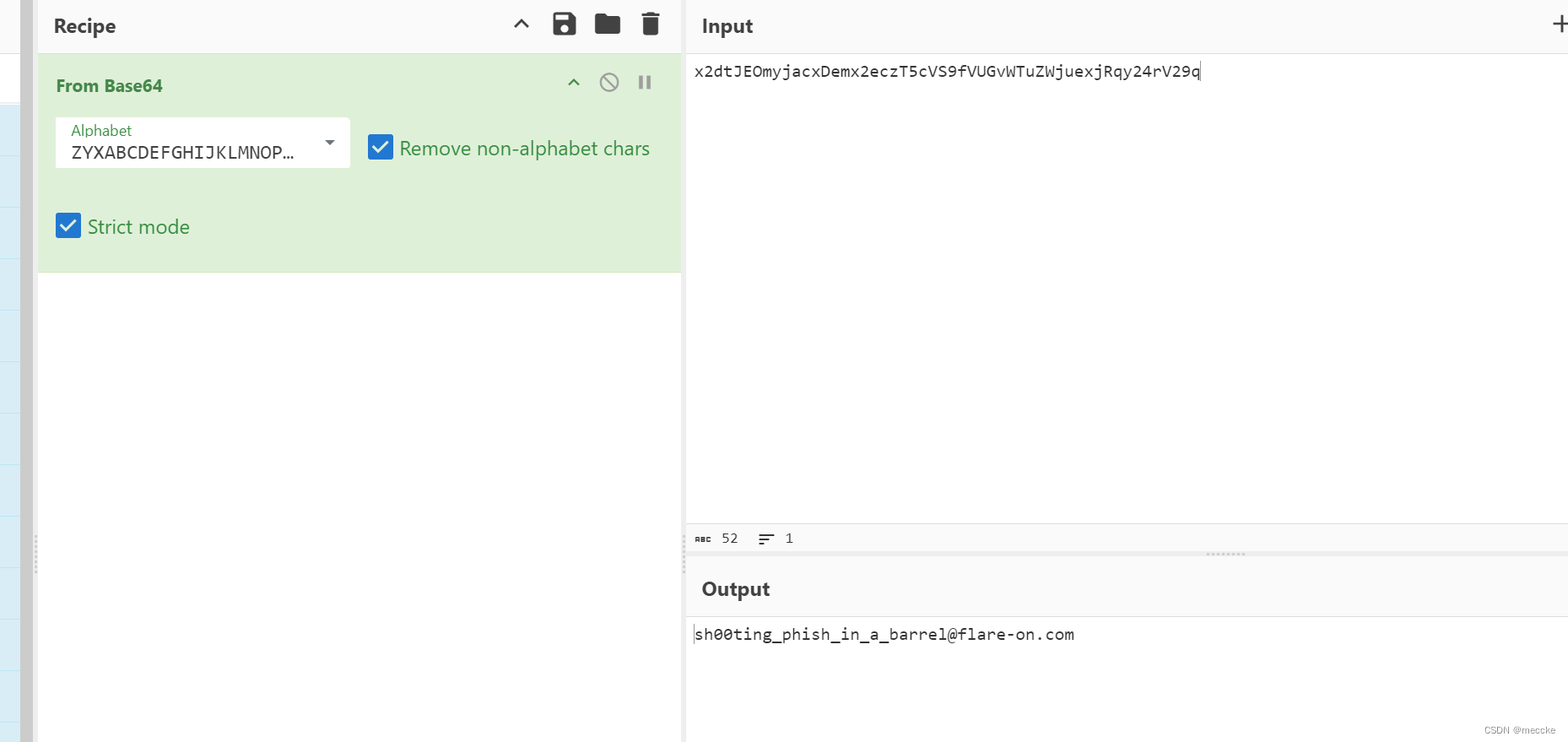
[WUSTCTF2020]level2
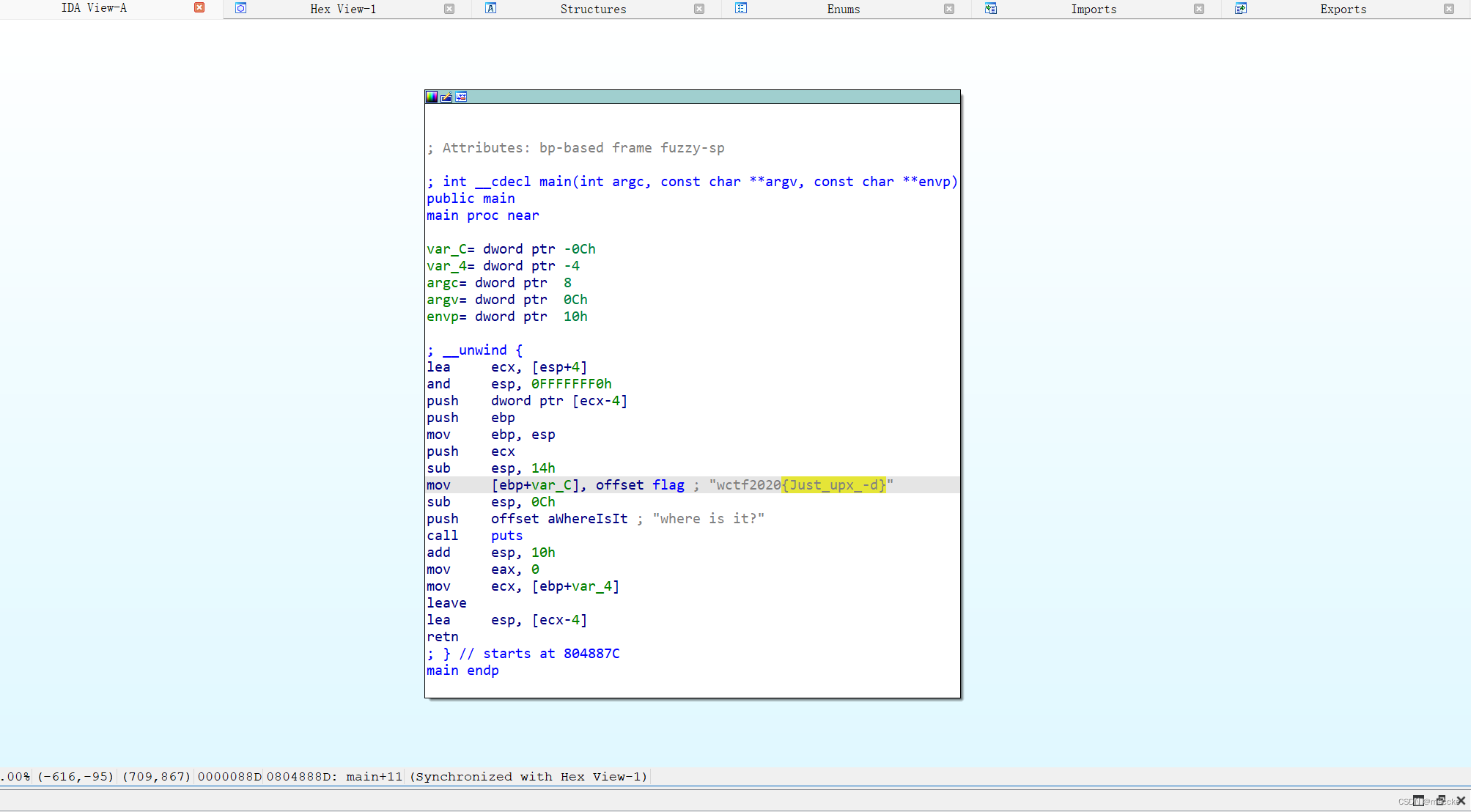
upx脱壳
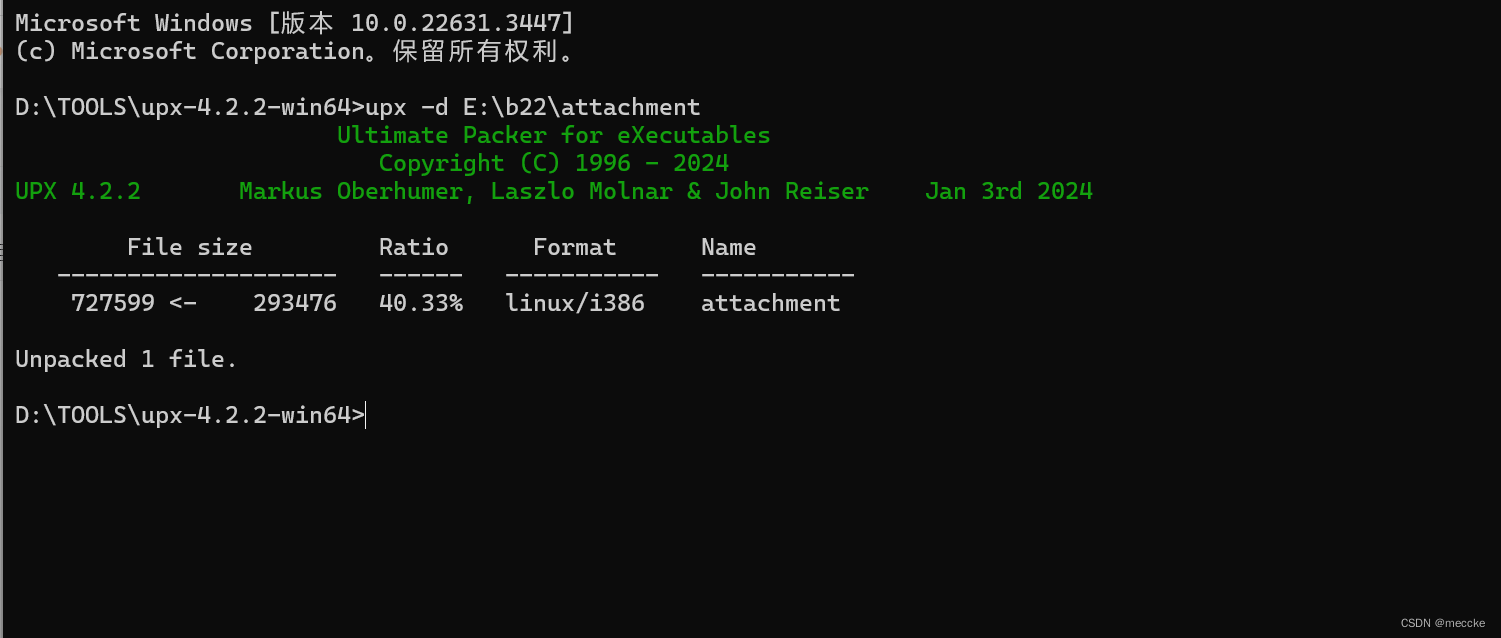
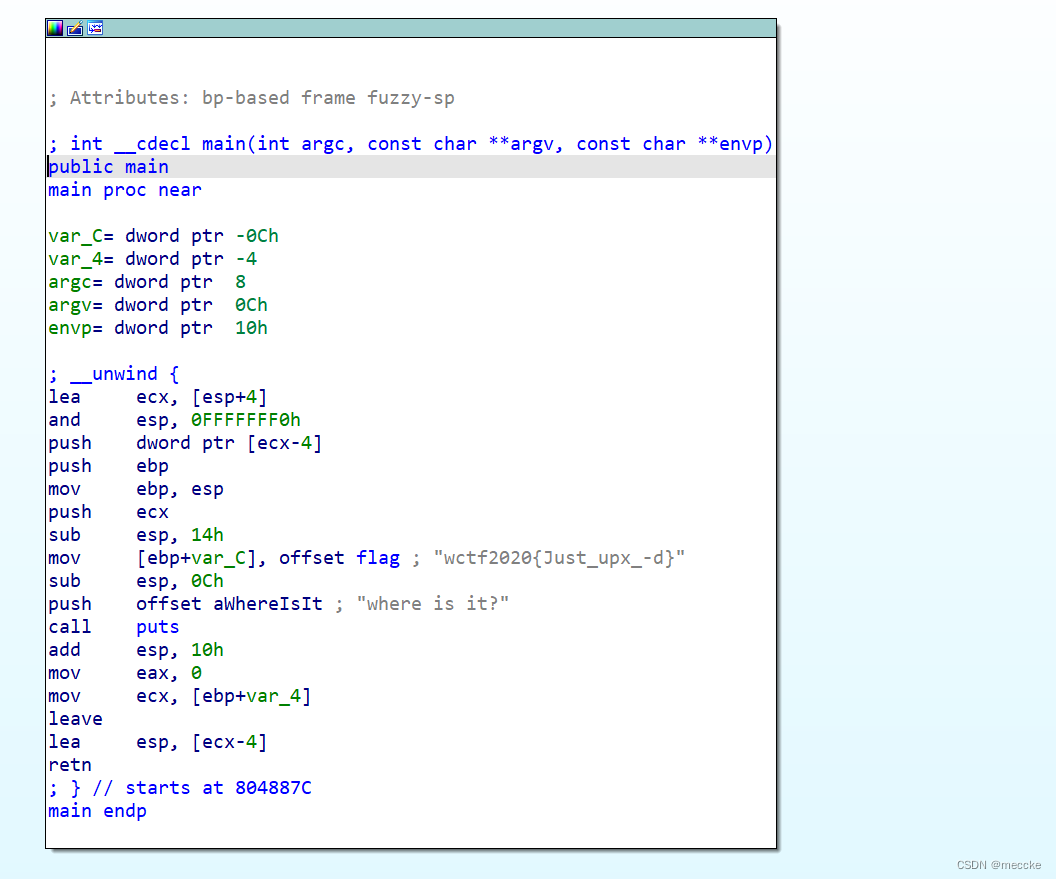
拖进ida就有flag
[WUSTCTF2020]level2
upx脱壳
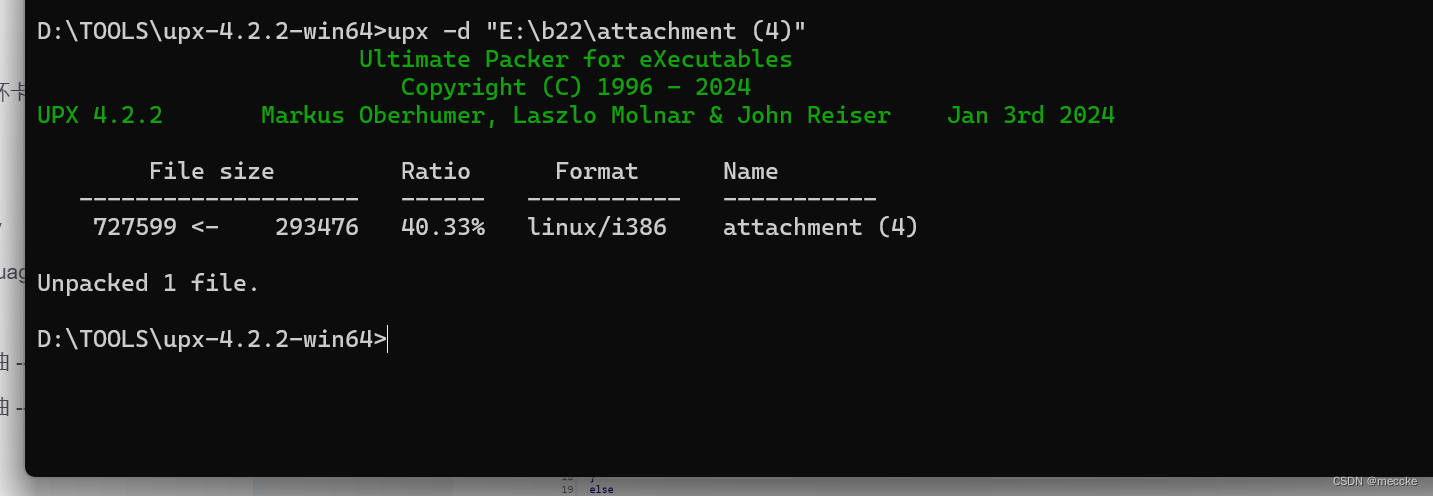
ida flag
[WUSTCTF2020]level3
ida打开
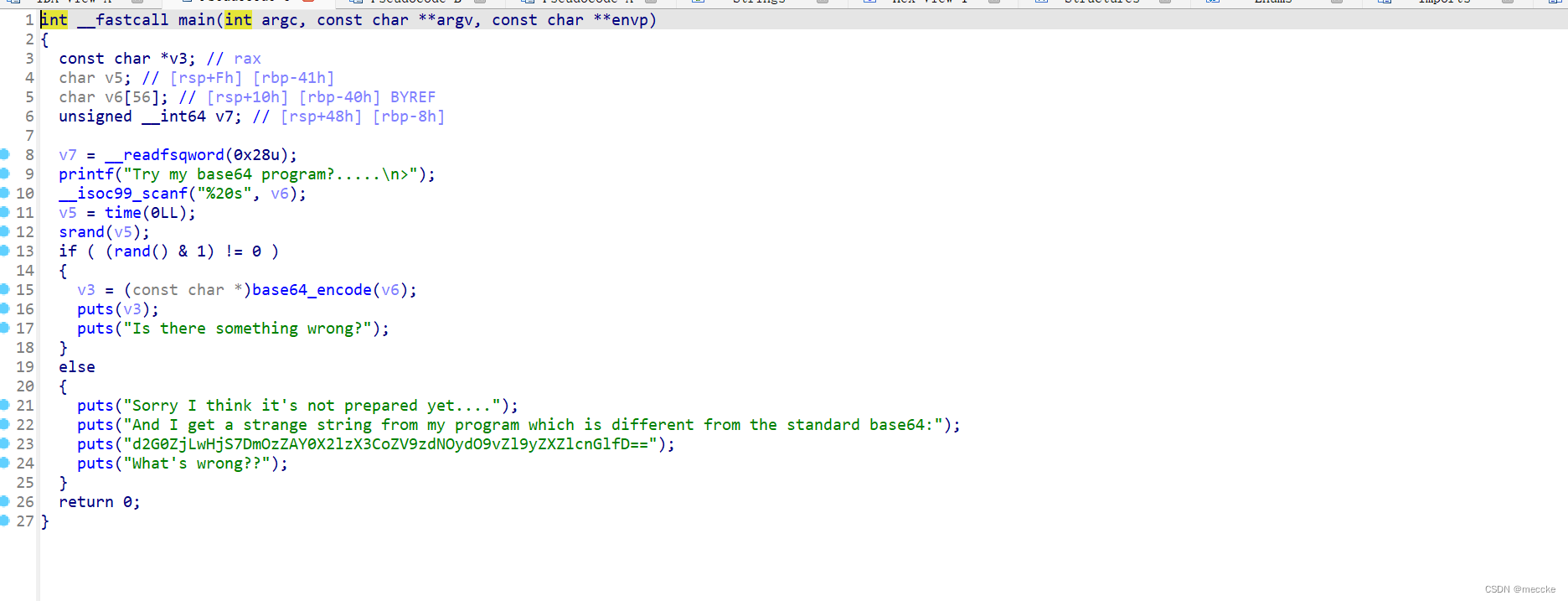
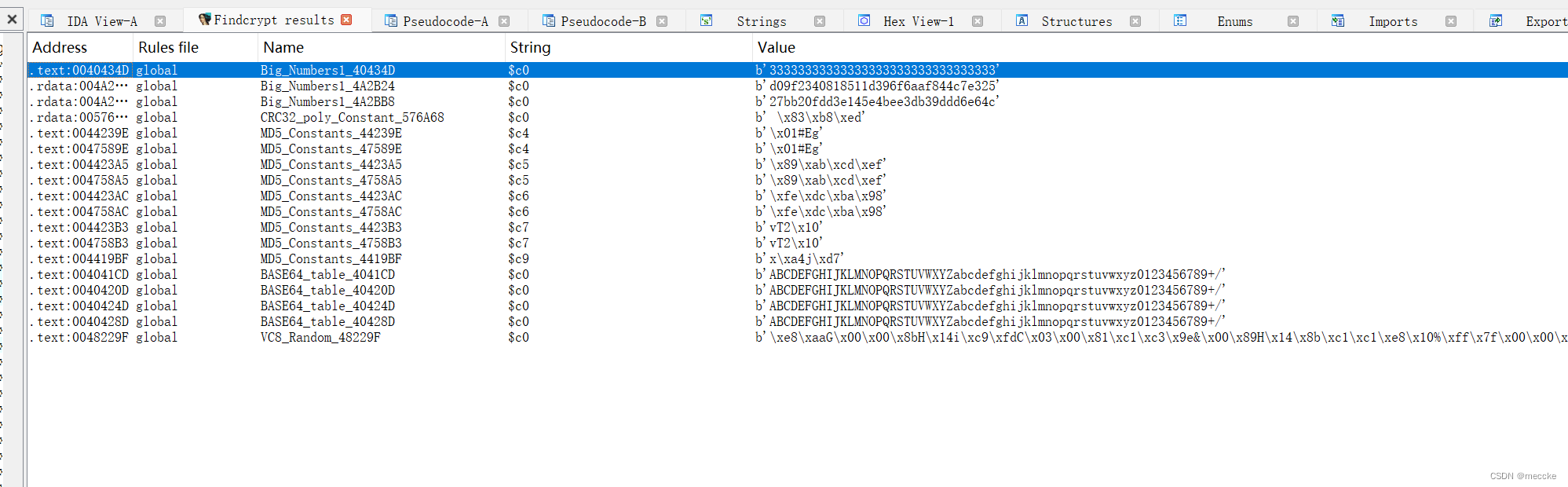
一看就像base64,但是不对
字符串打开
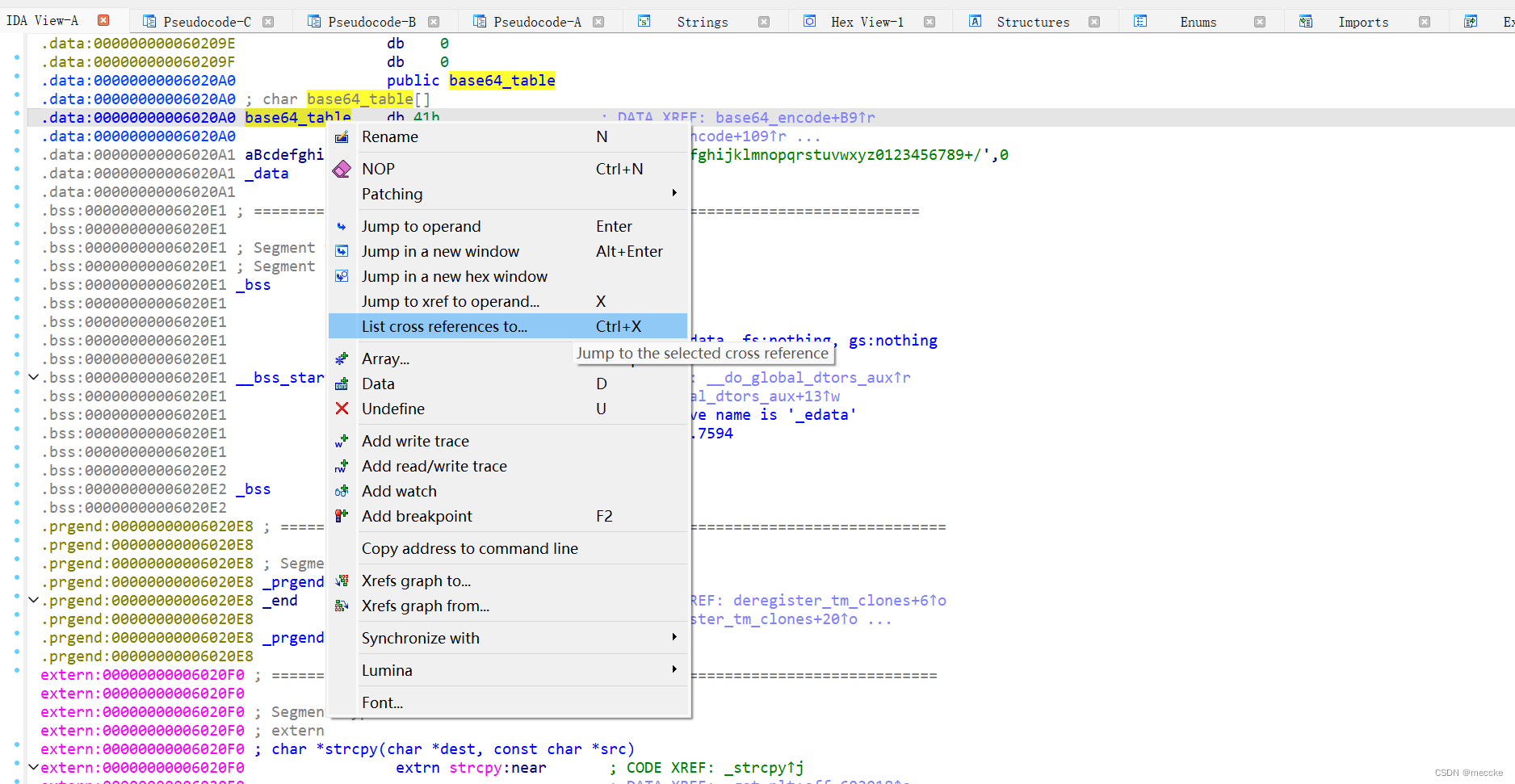
追踪交叉引用
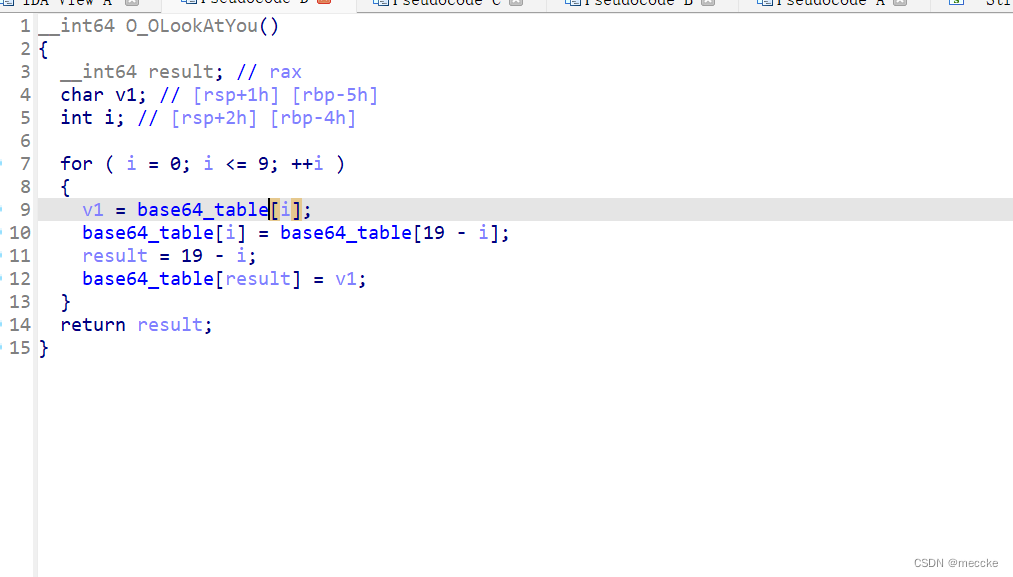
进行了加密
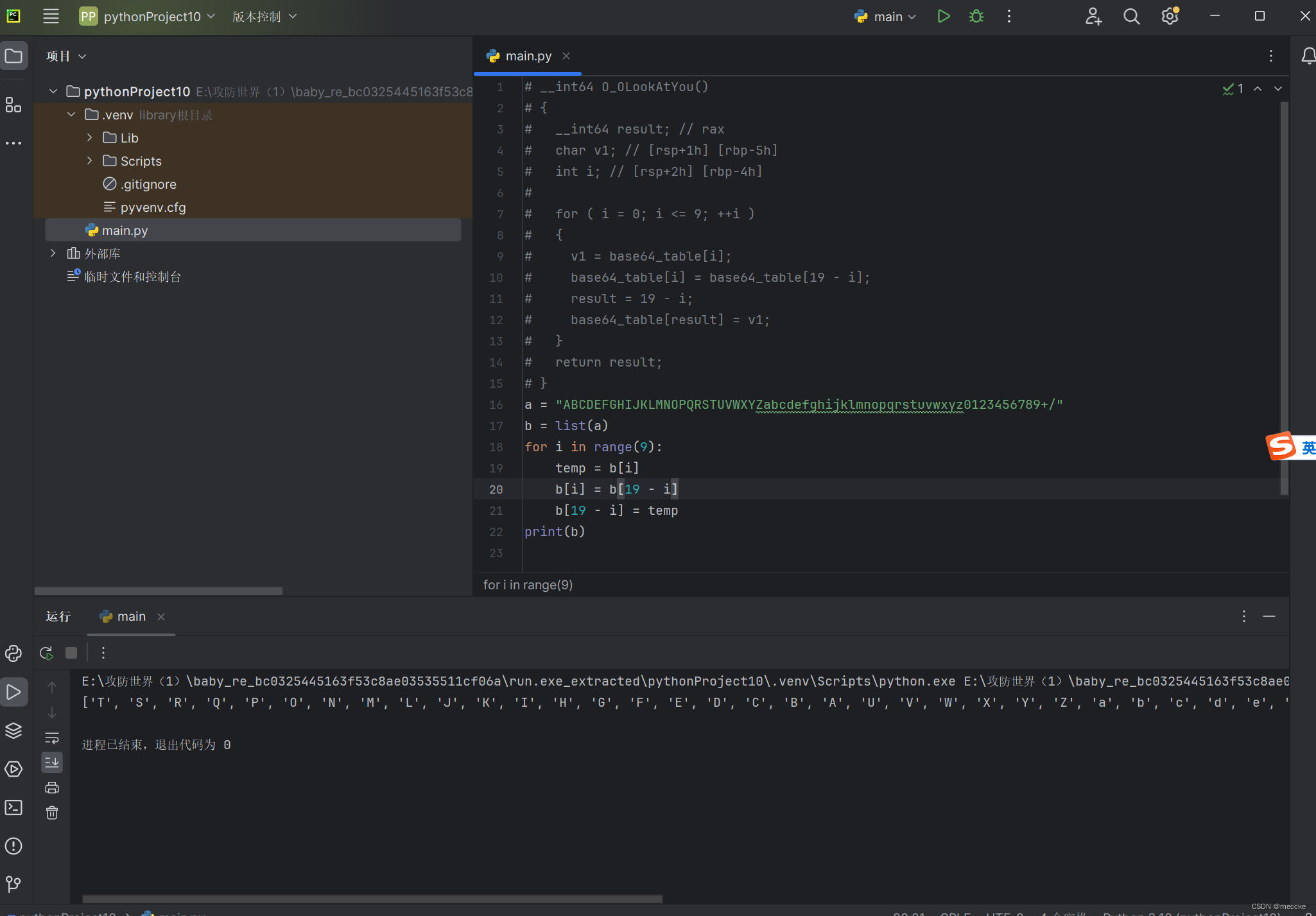
解密
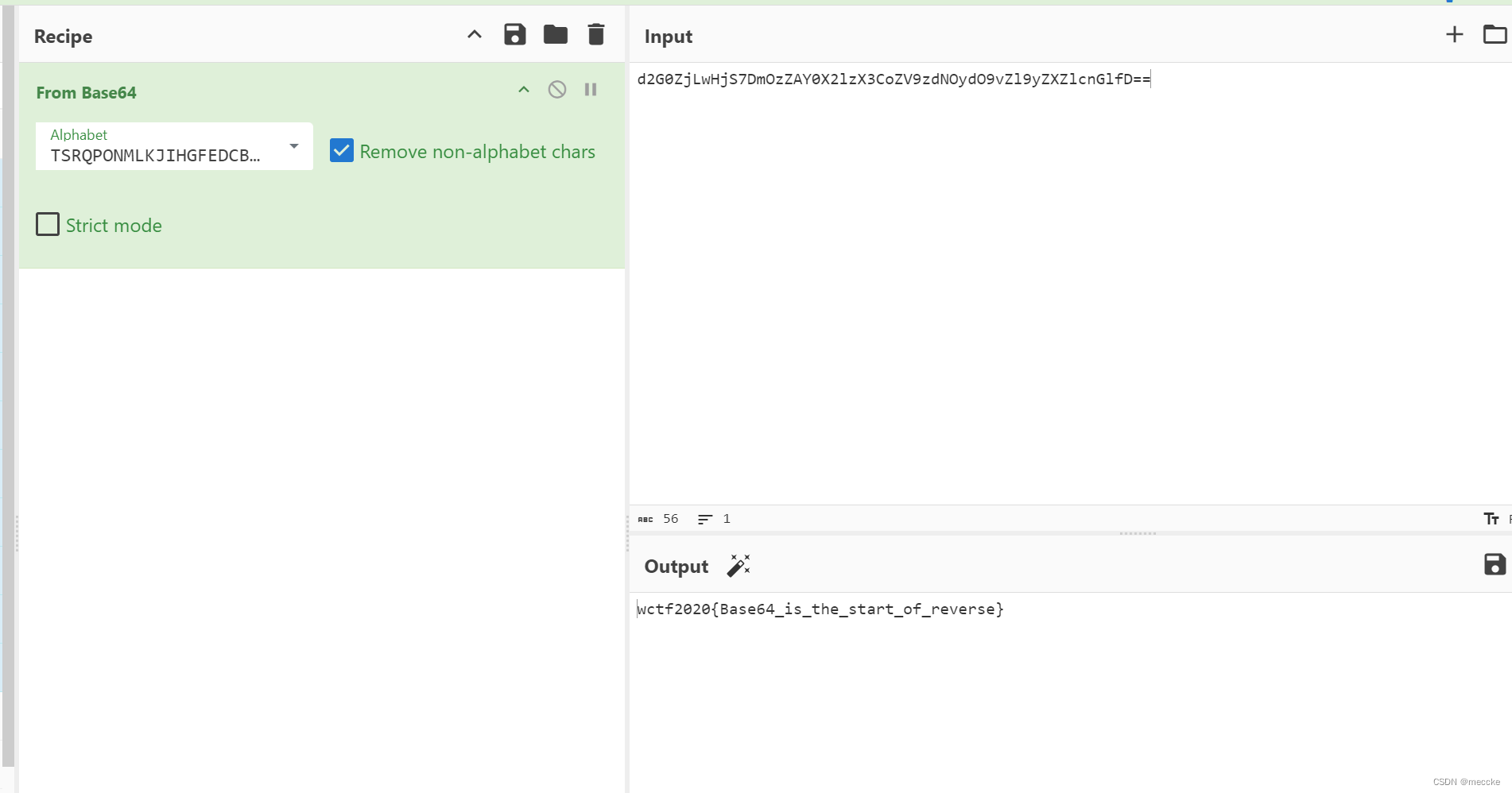
扔给厨子
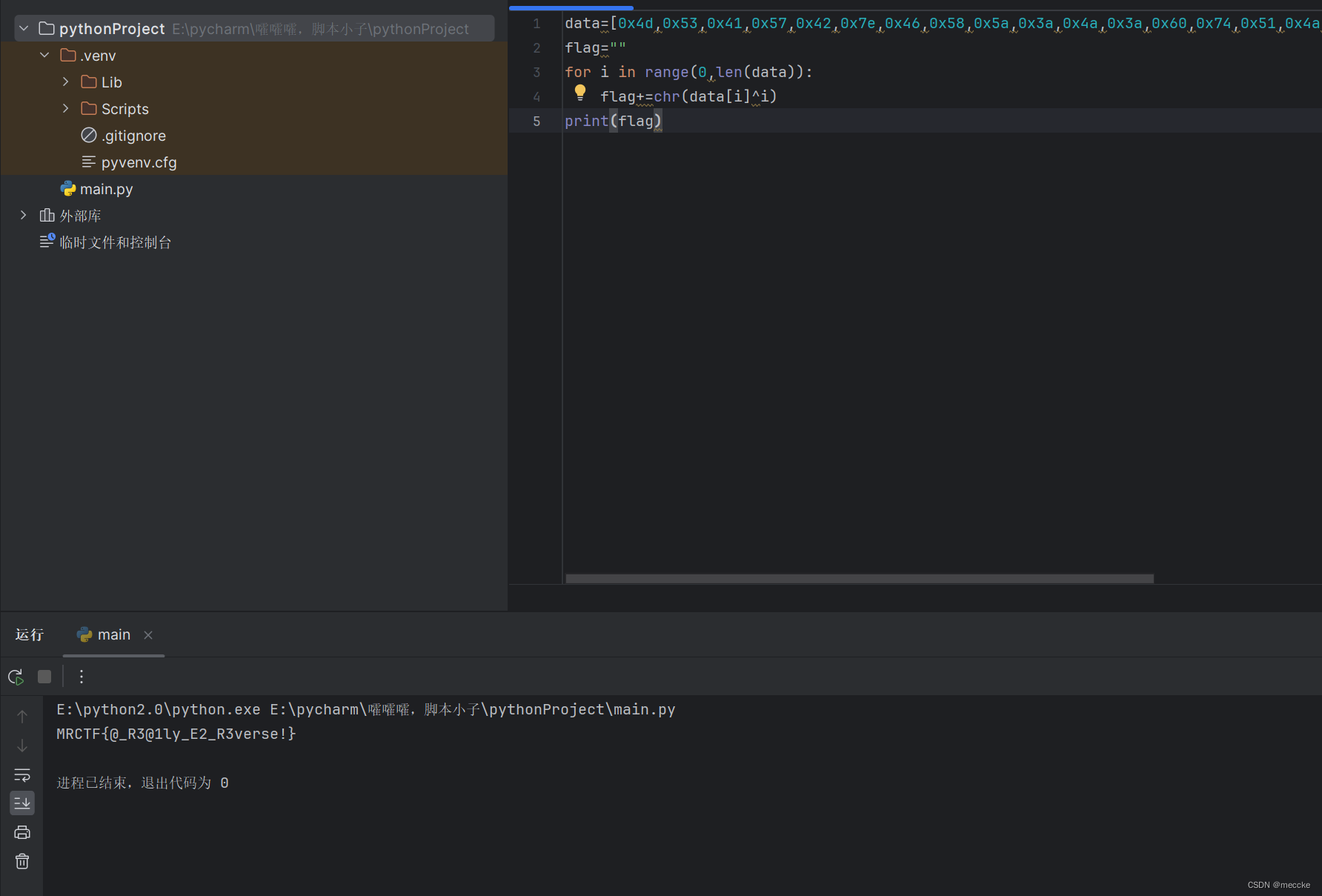
[MRCTF2020]Xor
拖进ida,发现反编译不了
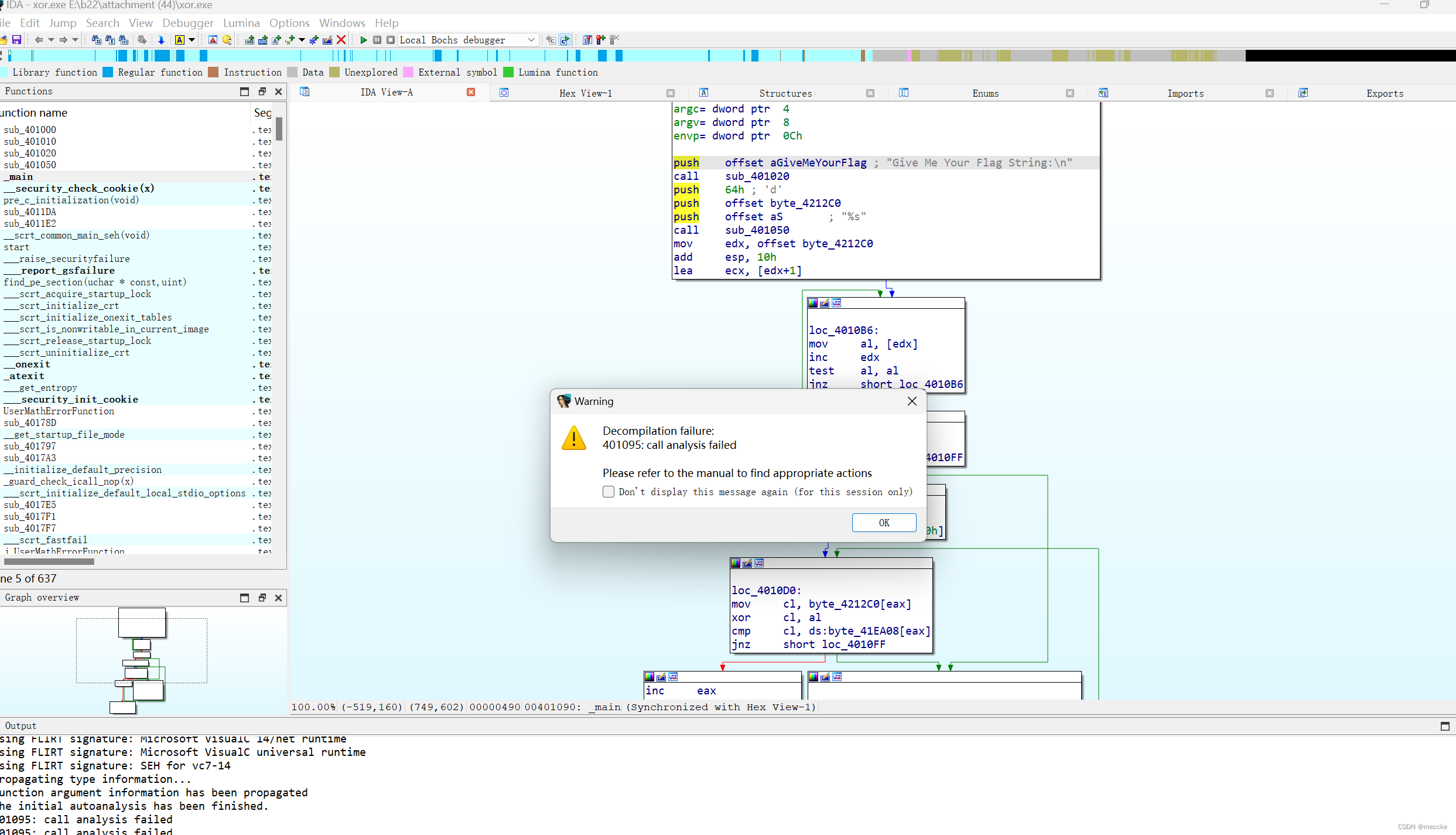
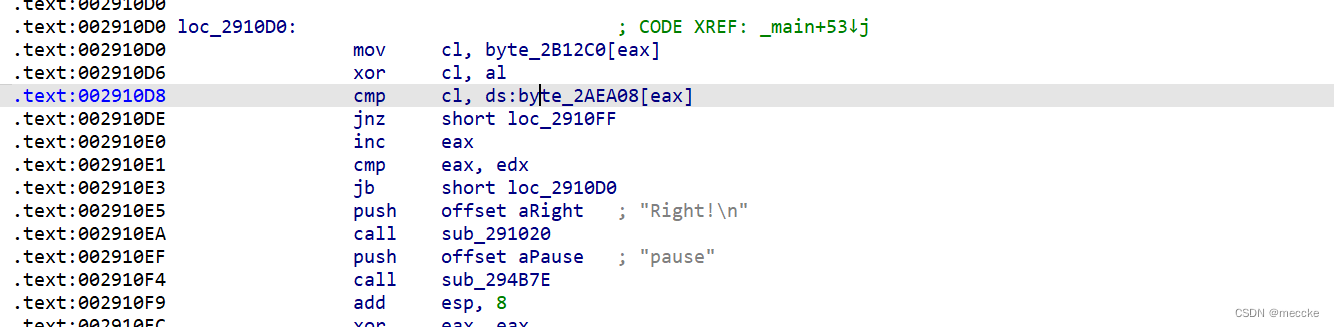
找到这里
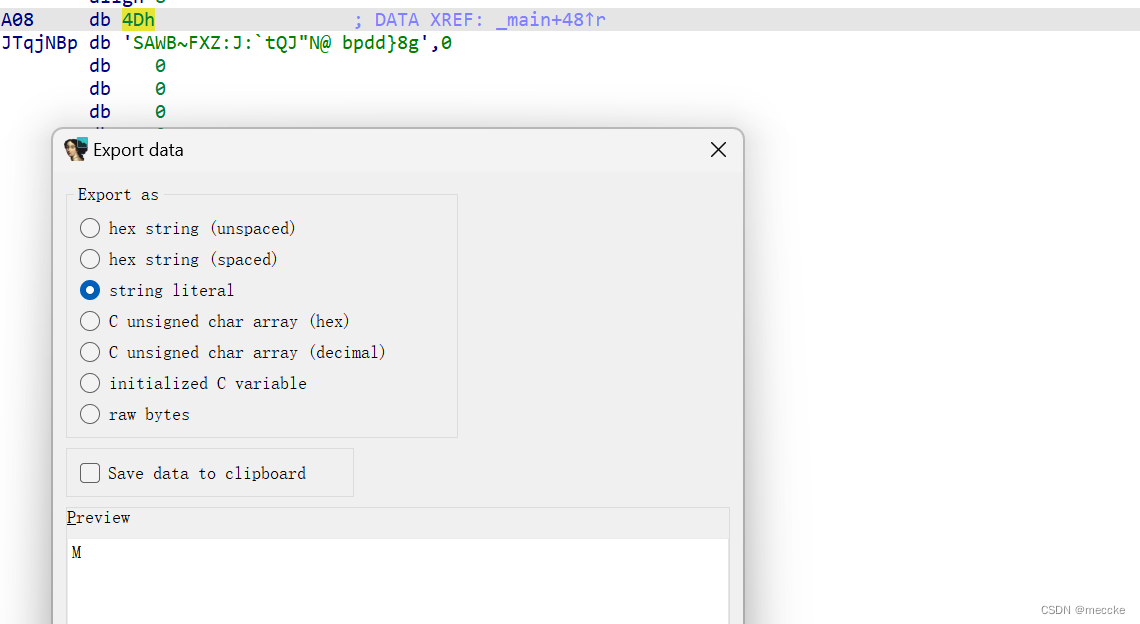
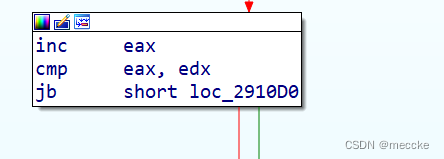
与输入的flag进行异或的是eax寄存器的低八位,观察看出
xor eax, eax
将eax清空了然后开始循环,每次循环
inc eax
eax自增1
可以知道每次与flag异或的数据是0,1,2,3,4......(个数为flag长度)
写脚本
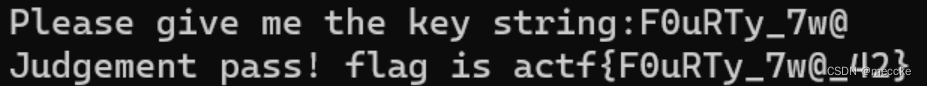
[FlareOn3]Challenge1
拖进ida,进行字符串比较后输出正确
点进sub-401260函数
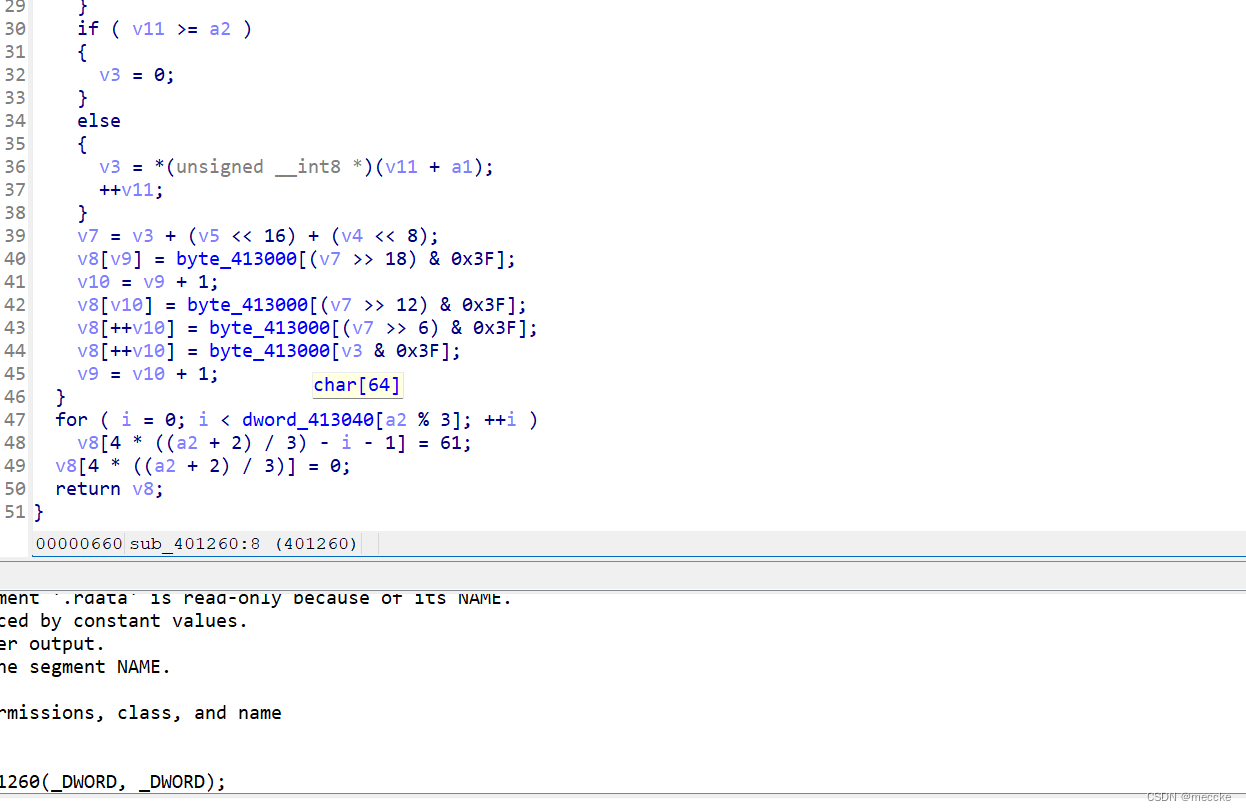
点进数组
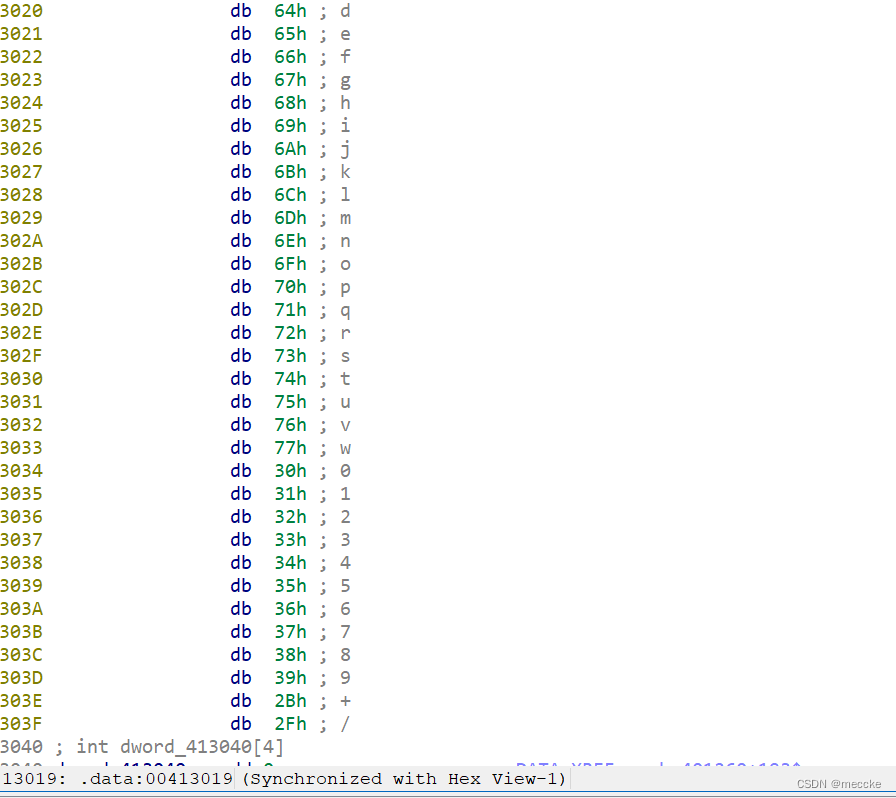
base64变表啊
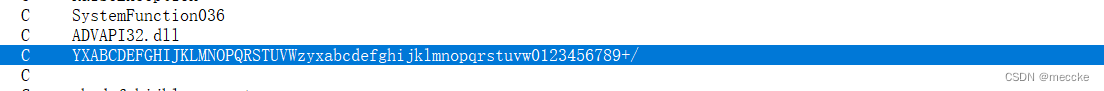
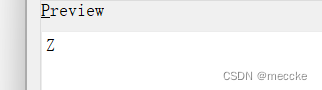
前面还有一个z
[UTCTF2020]basic-re
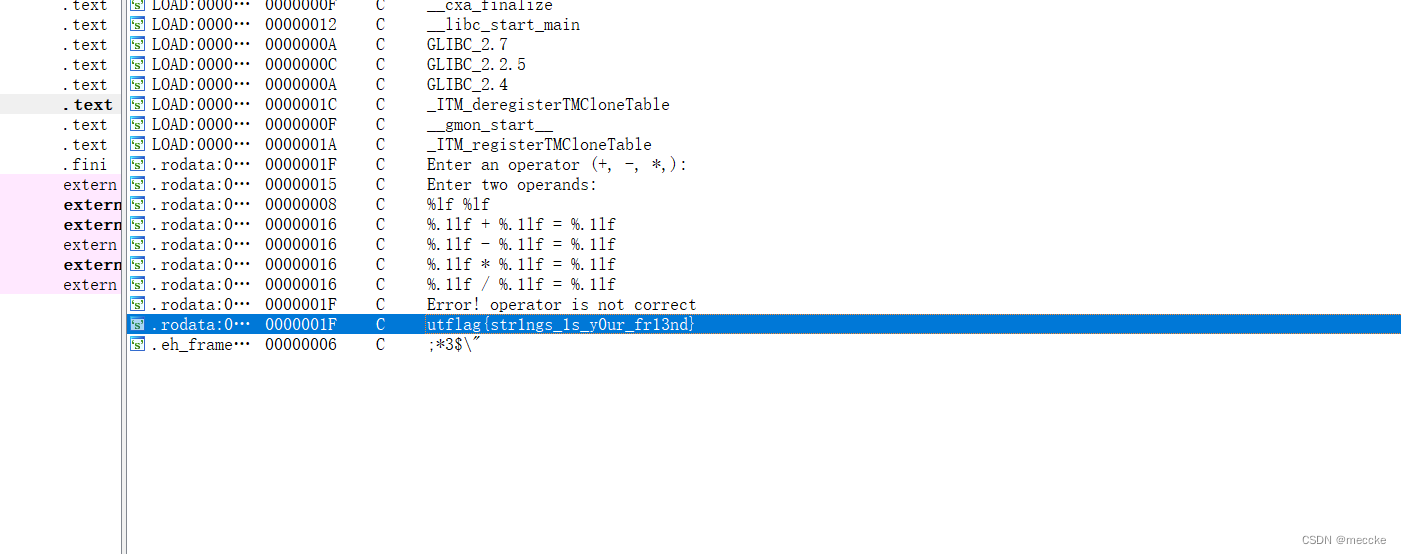
[FlareOn6]Snake
附件有一个文件,英文的
下载一个新的工具
fceux
拖进去
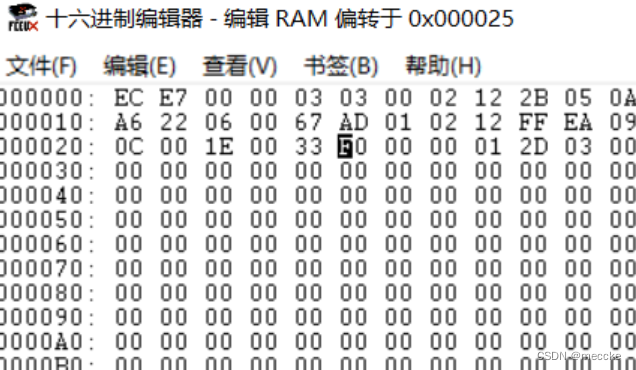
debug-hex窗口,动调发现0x25位置存的是蛇吃到苹果数,debug-debugger下断点
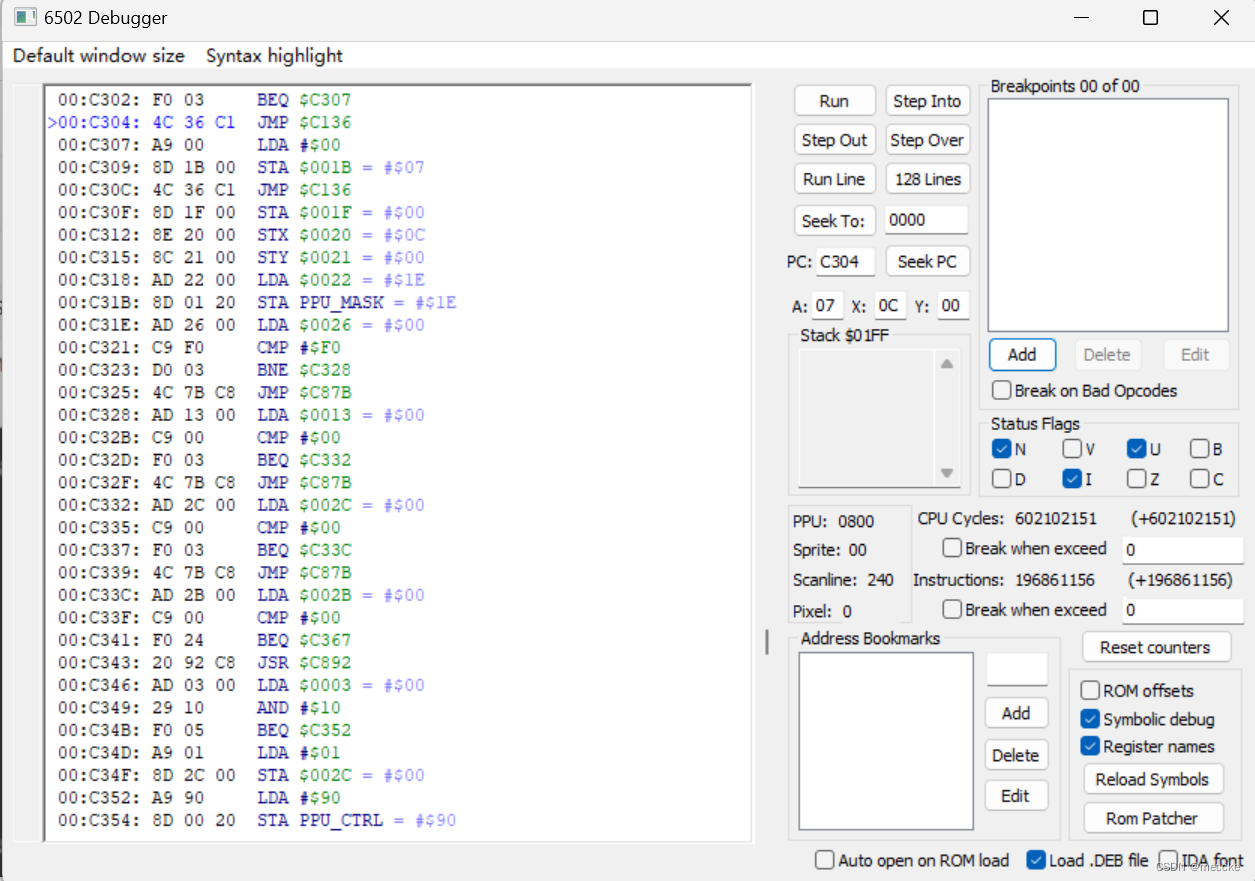
![]()
读和写都要勾上
蛇吃到苹果就停下来了
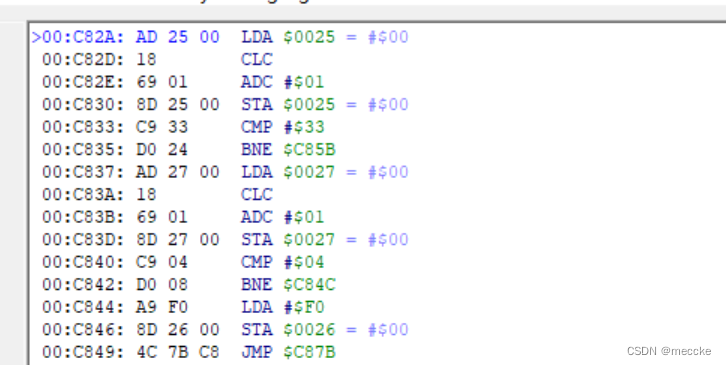
停在这里了,cmp比较了33,猜测是吃的苹果数
修改0x25的值为32
两次单步运行得到0x26的值为F0
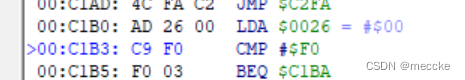
修改运行
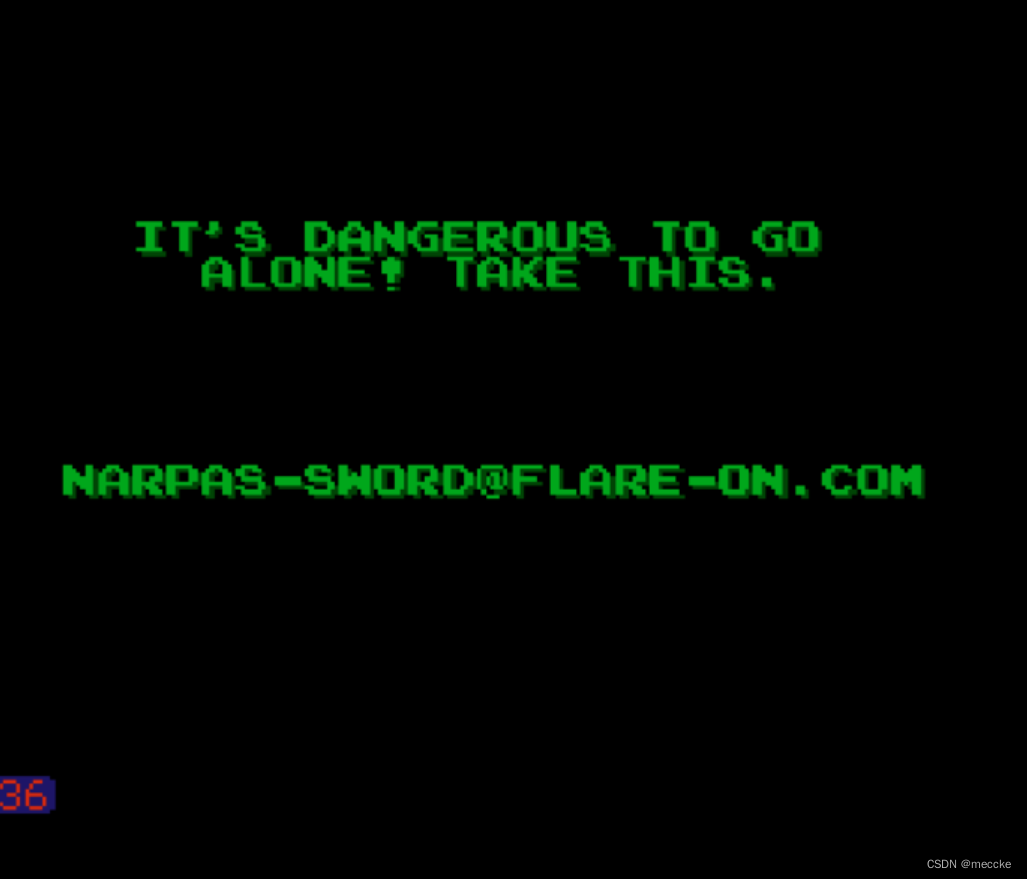
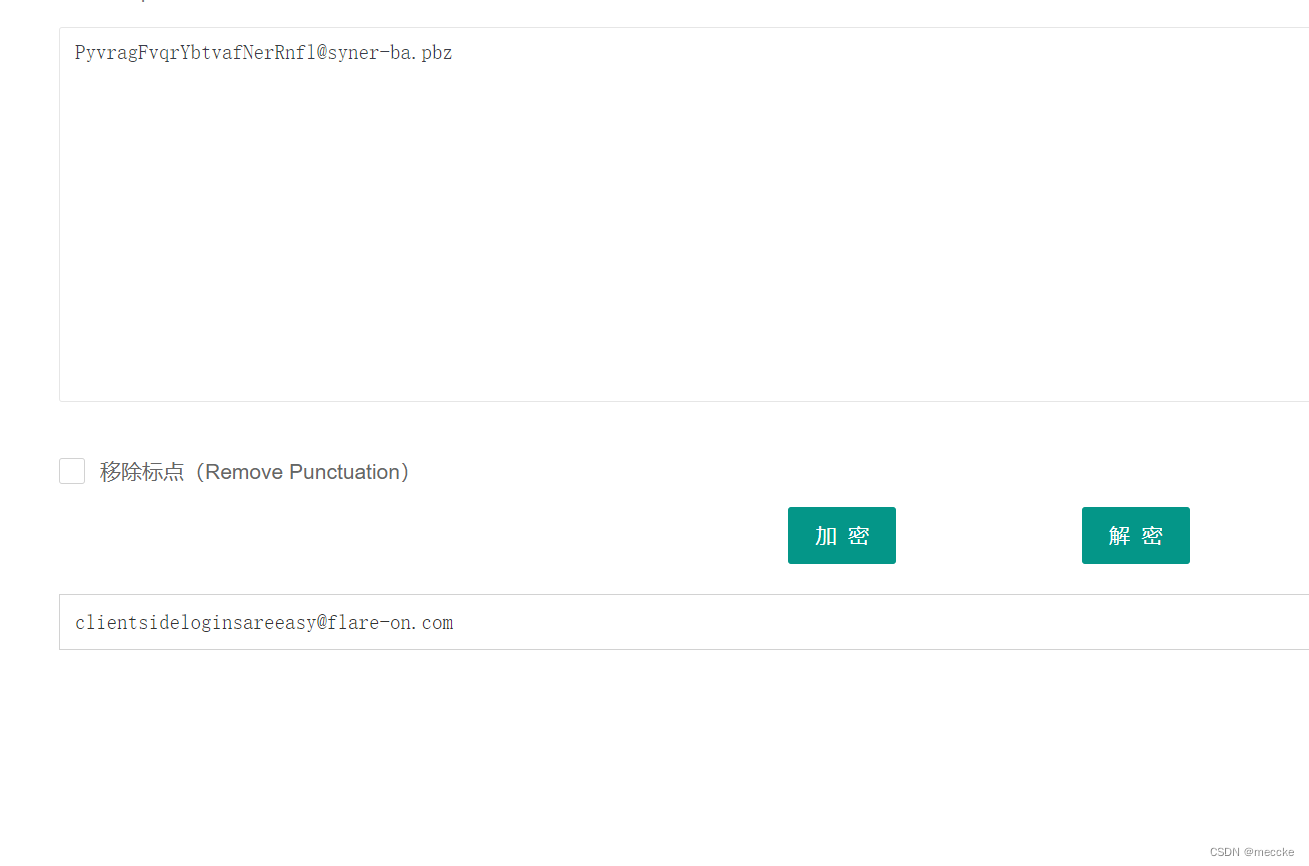
[FlareOn4]login
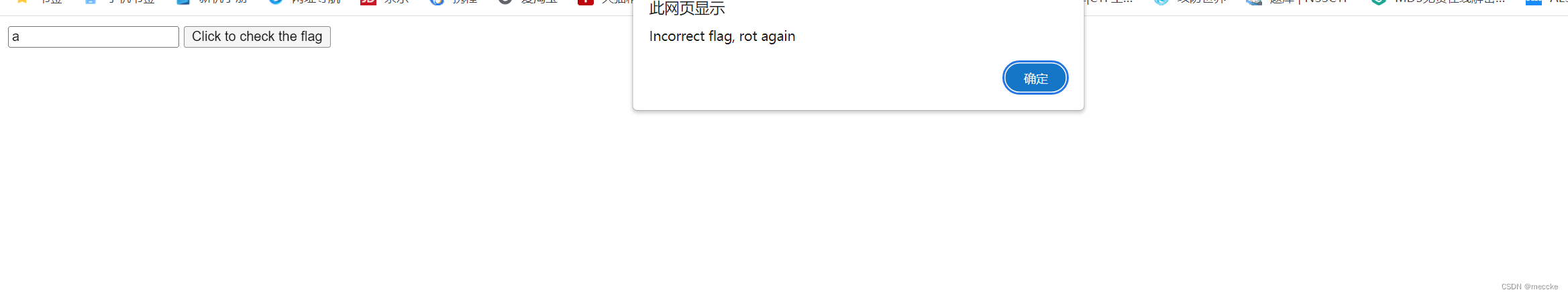
下载附件,打开是个网站
f12
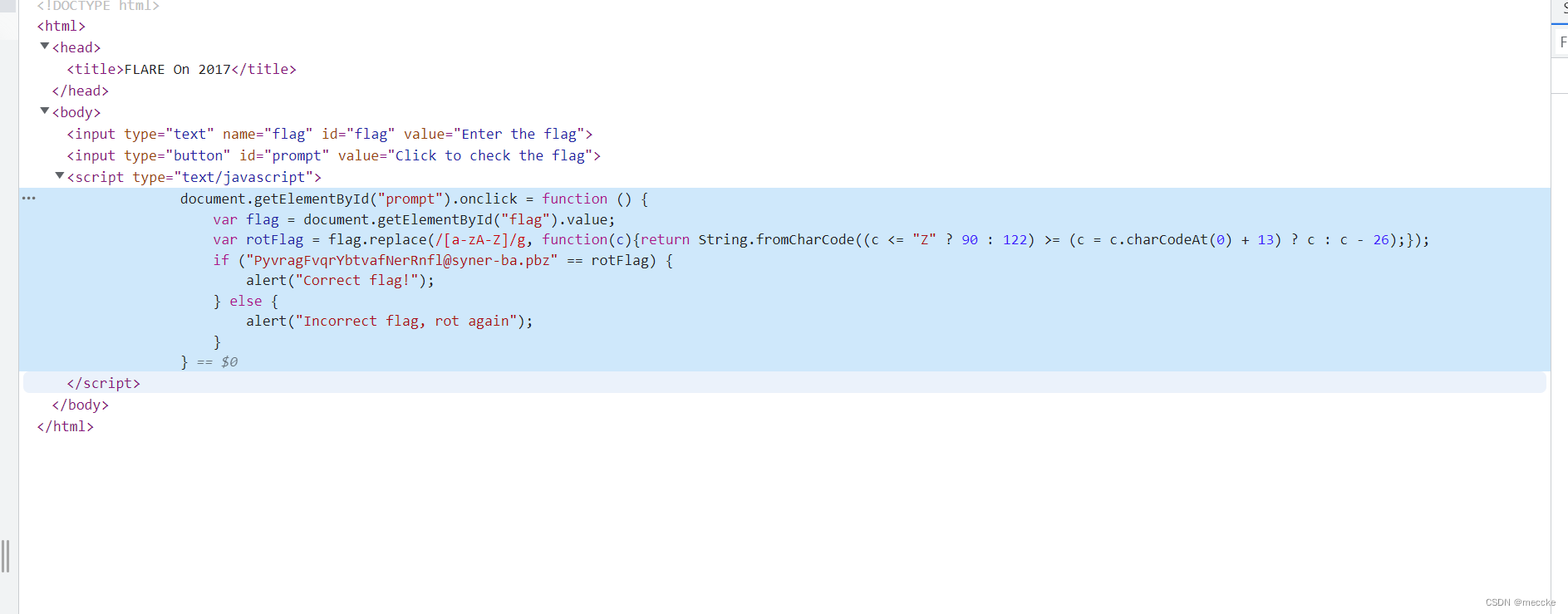
ROT13是一种简单的字母替换密码,它通过将字母表中的每个字母向后移动13个位置来加密文本。具体来说,它将A加密为N,B加密为O,依此类推,直到Z加密为M。然后,它将Y加密为A,Z加密为B,依此类推,直到M加密为Z。
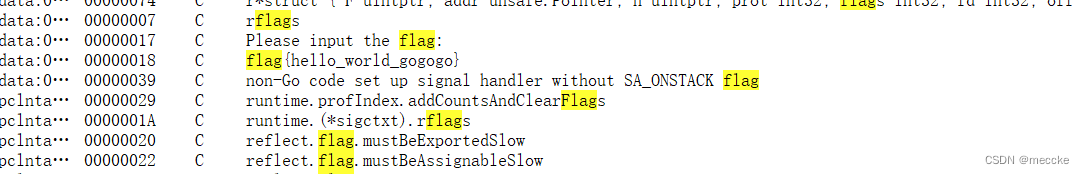
[ACTF新生赛2020]easyre
upx脱壳,拖进ida
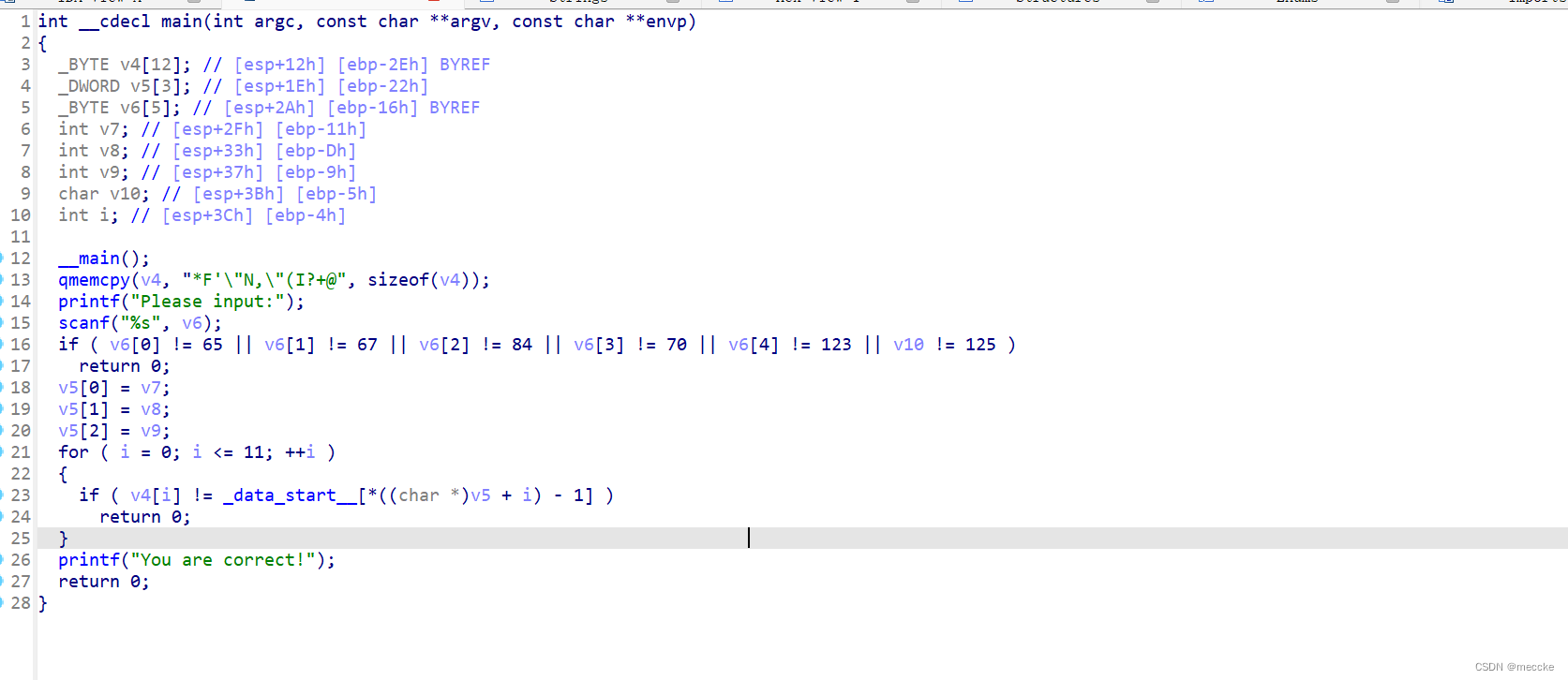
分析函数
将一堆字符串复制给v4
输入一个值,if条件判断前缀是不是actf
写代码
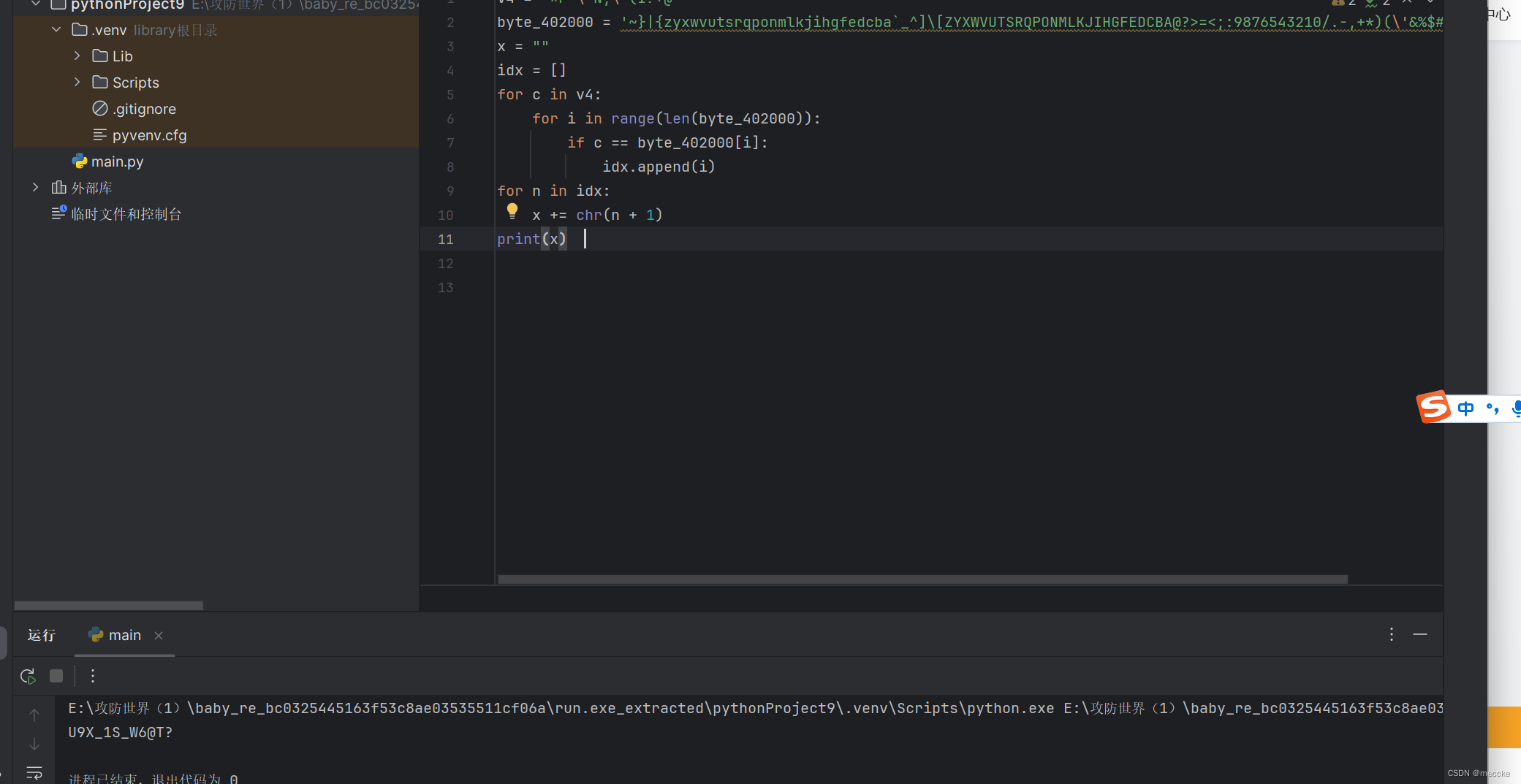
[MRCTF2020]hello_world_go
我还以为是go语言
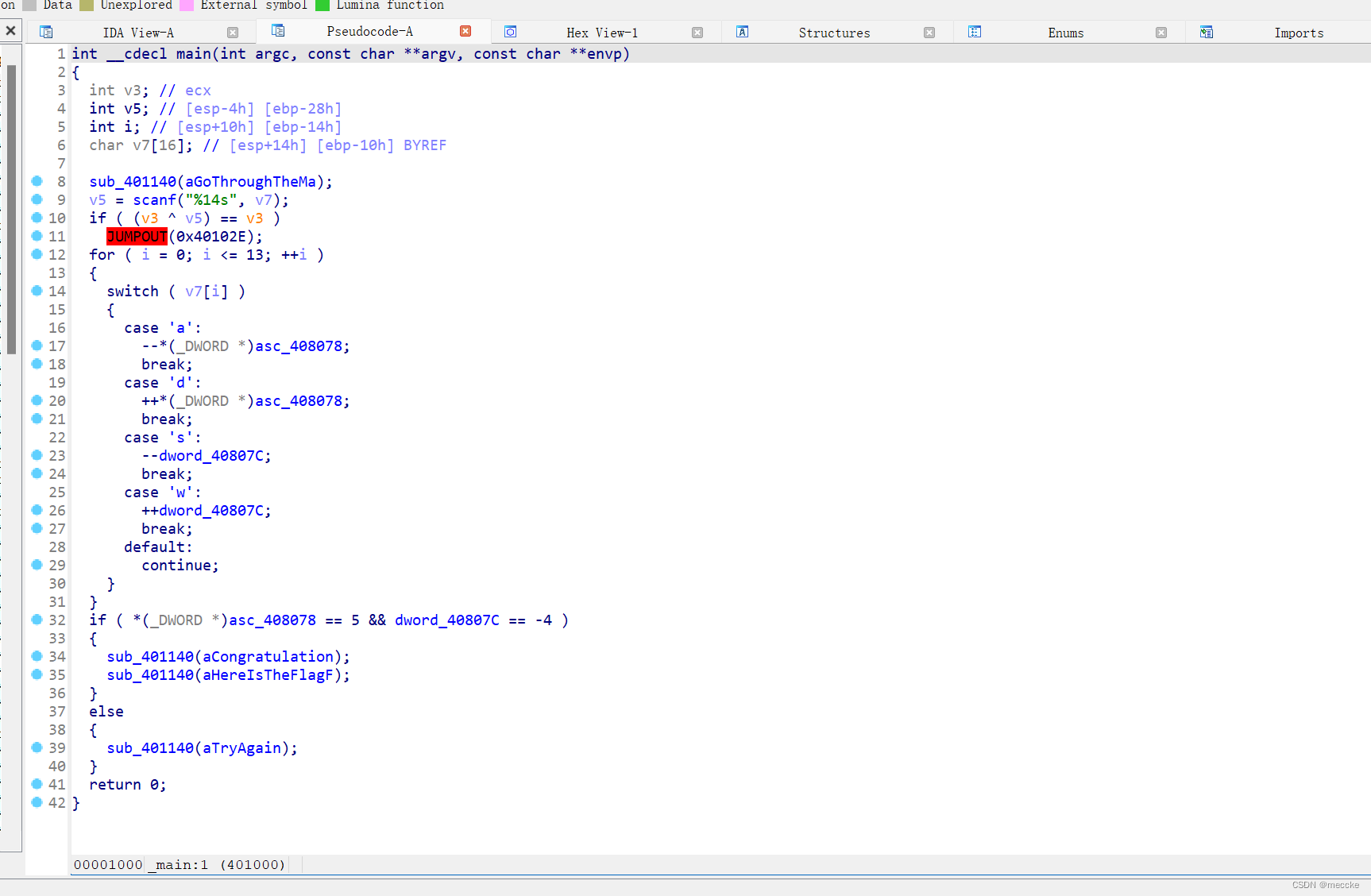
[HDCTF2019]Maze
脱壳
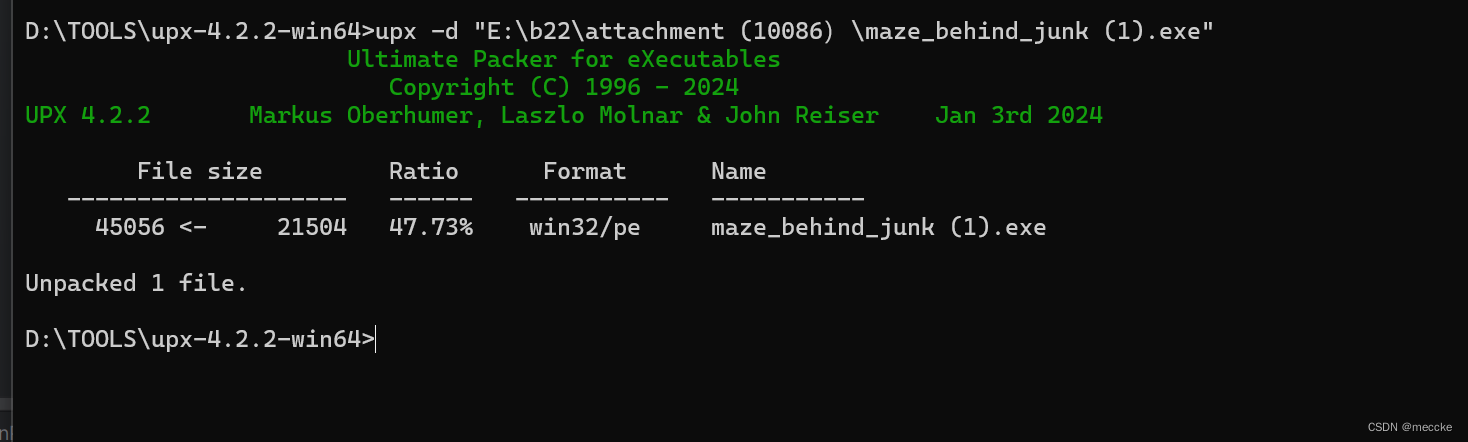
拖进ida
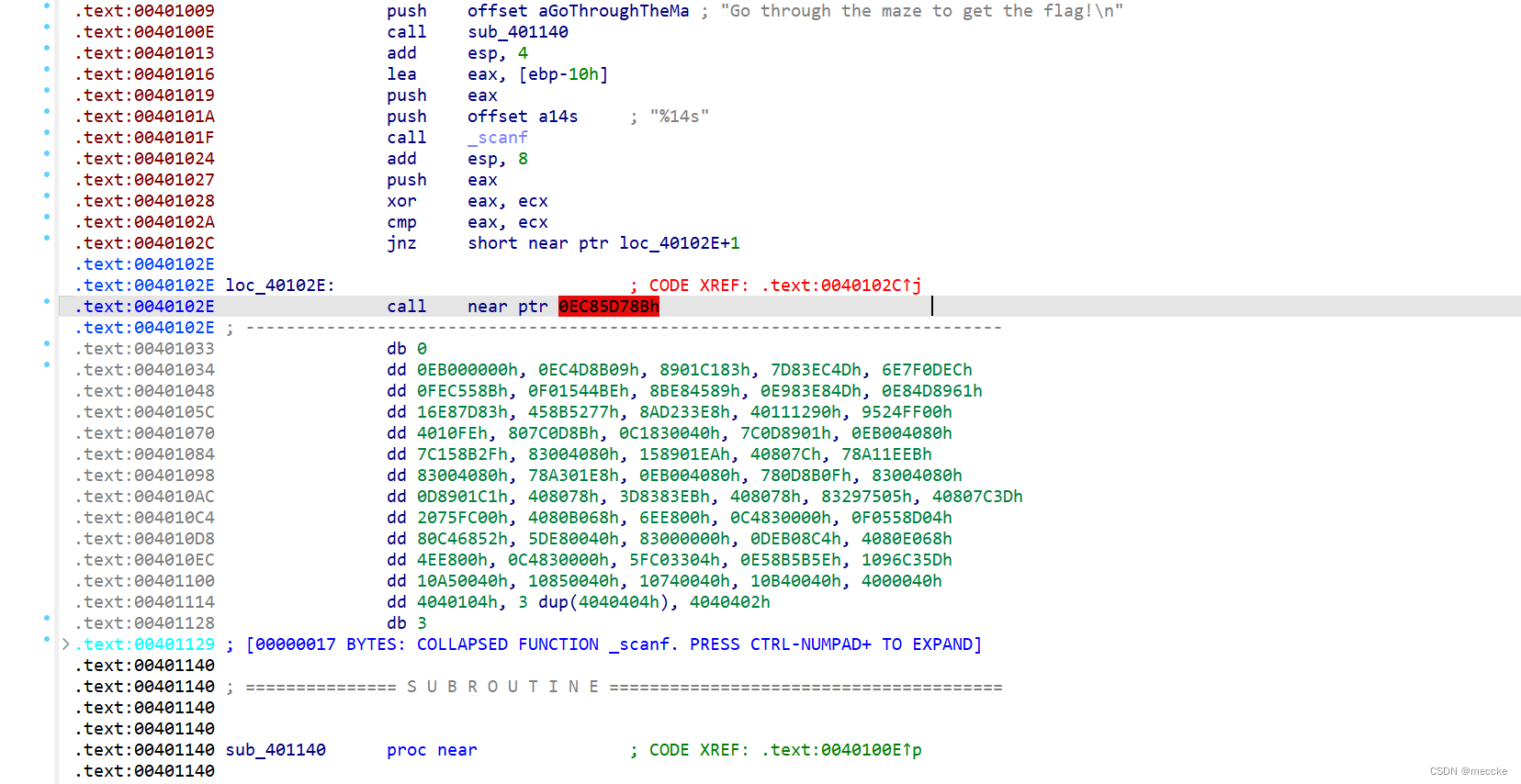
反编译不了
call处按u
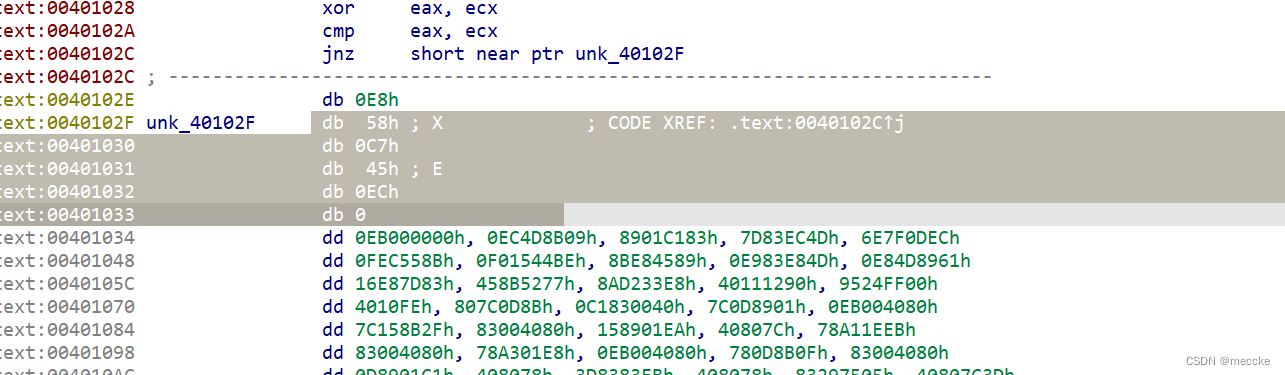
c 第一个选项
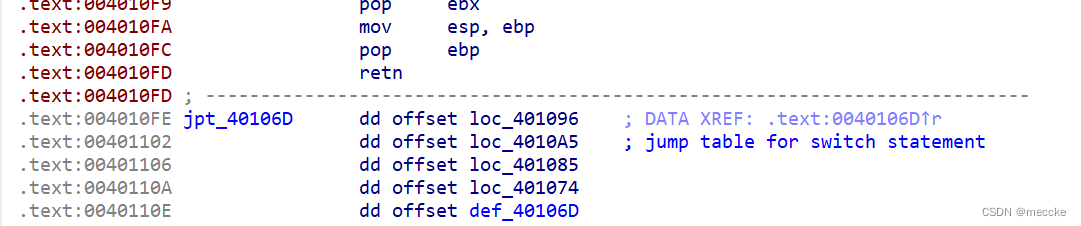
把红字之上的都选中 p(去脏字的过程)
反编译
![]()
7x7的迷宫
flag{ssaaasaassdddw}
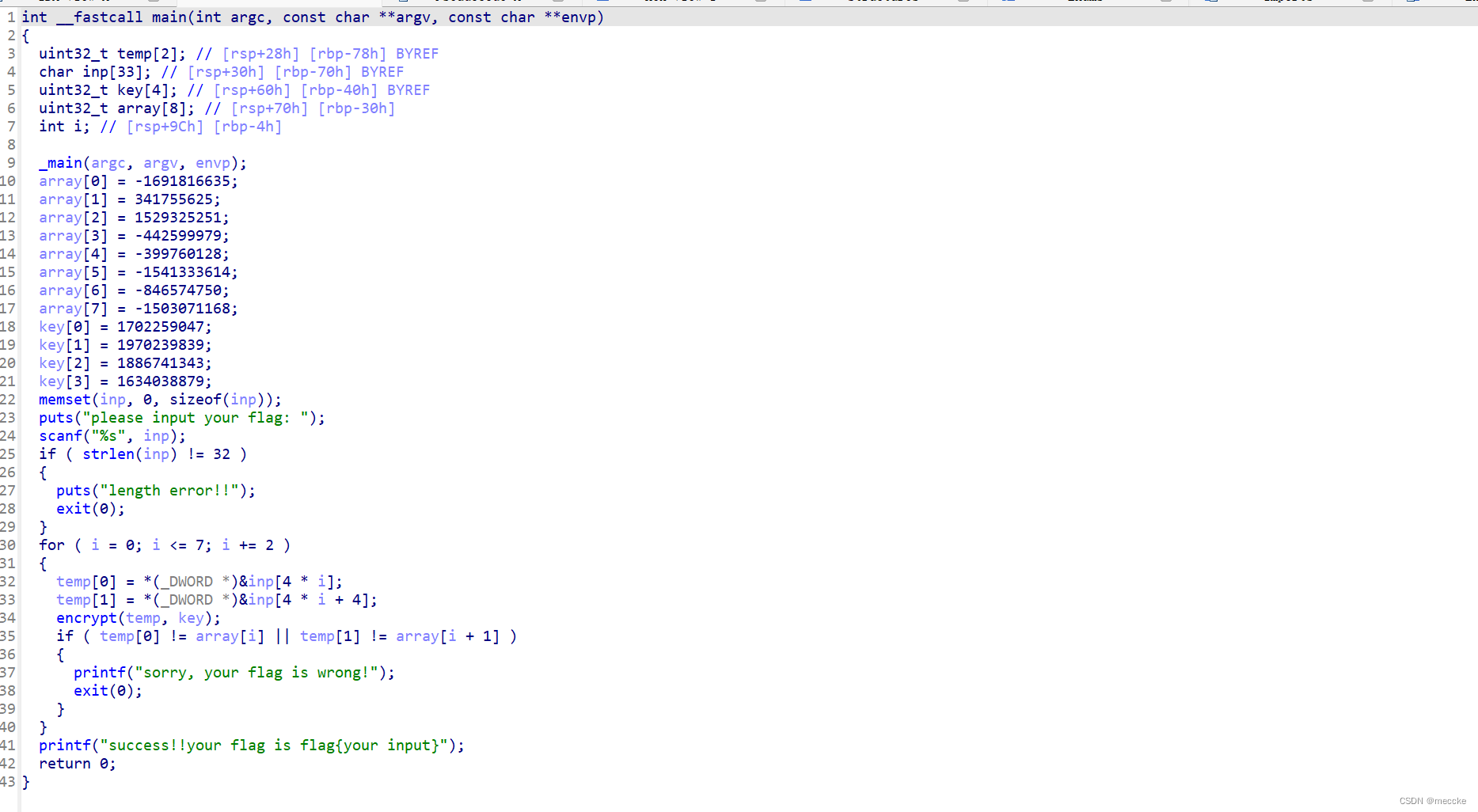
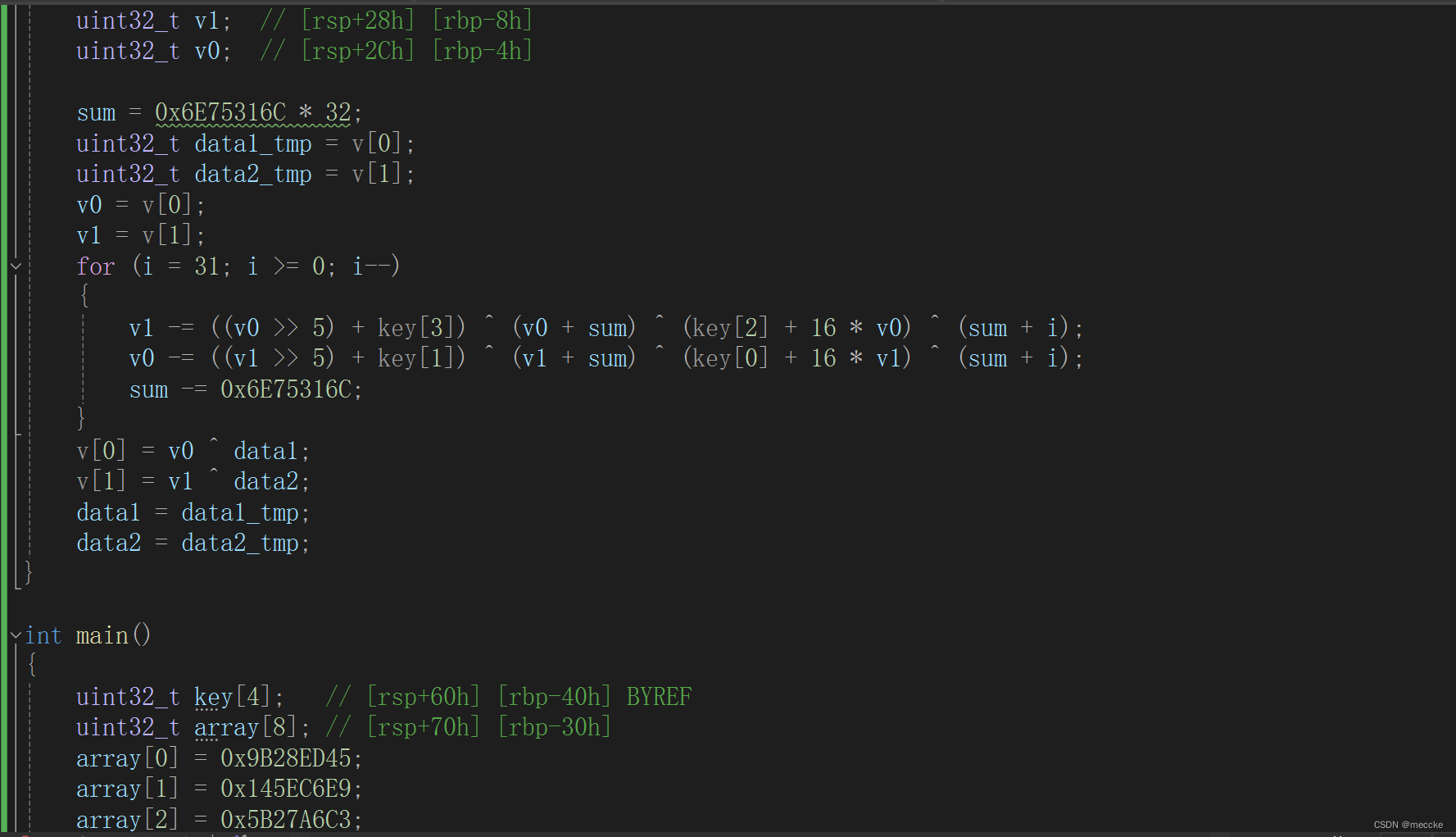
[GWCTF 2019]xxor
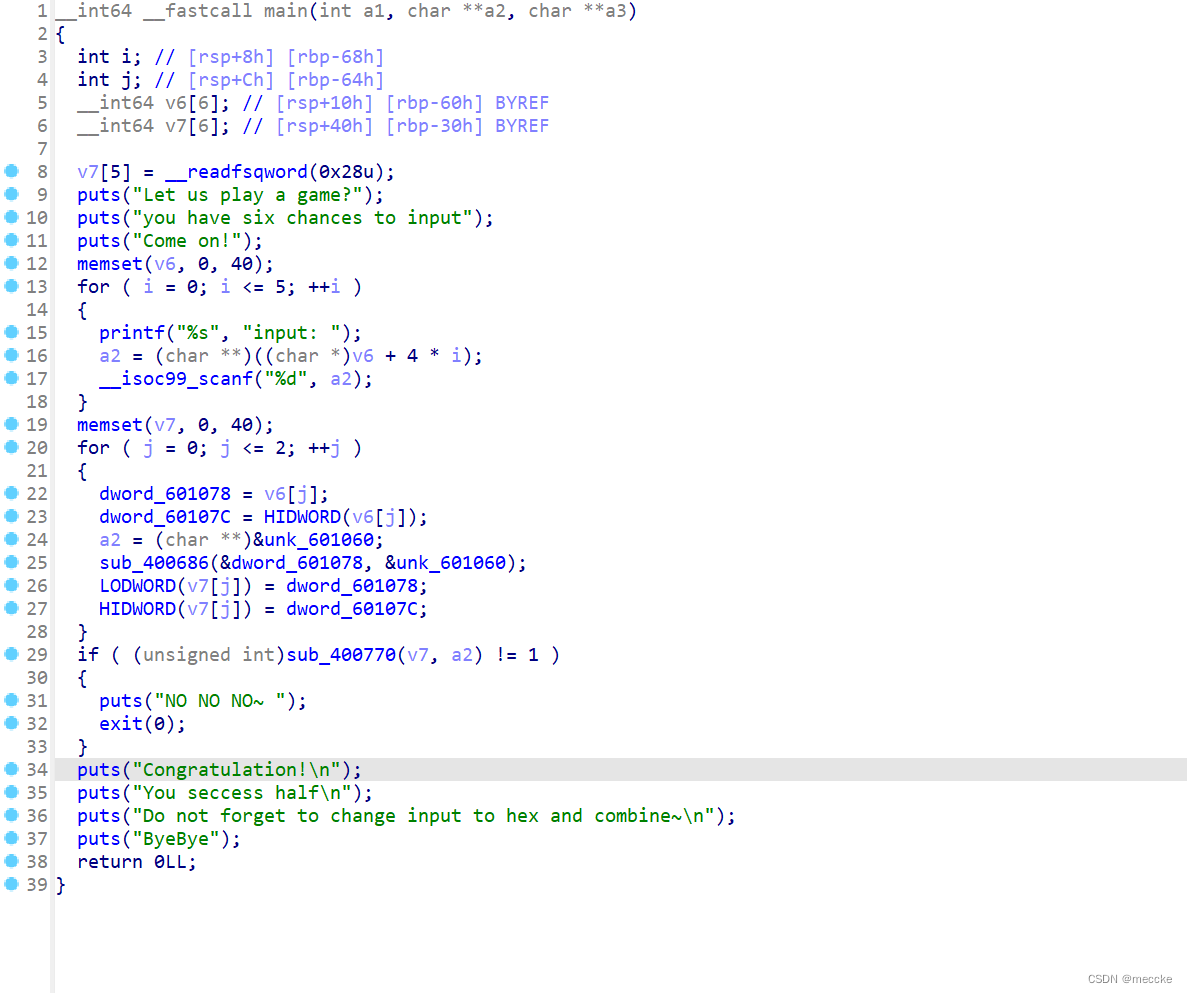
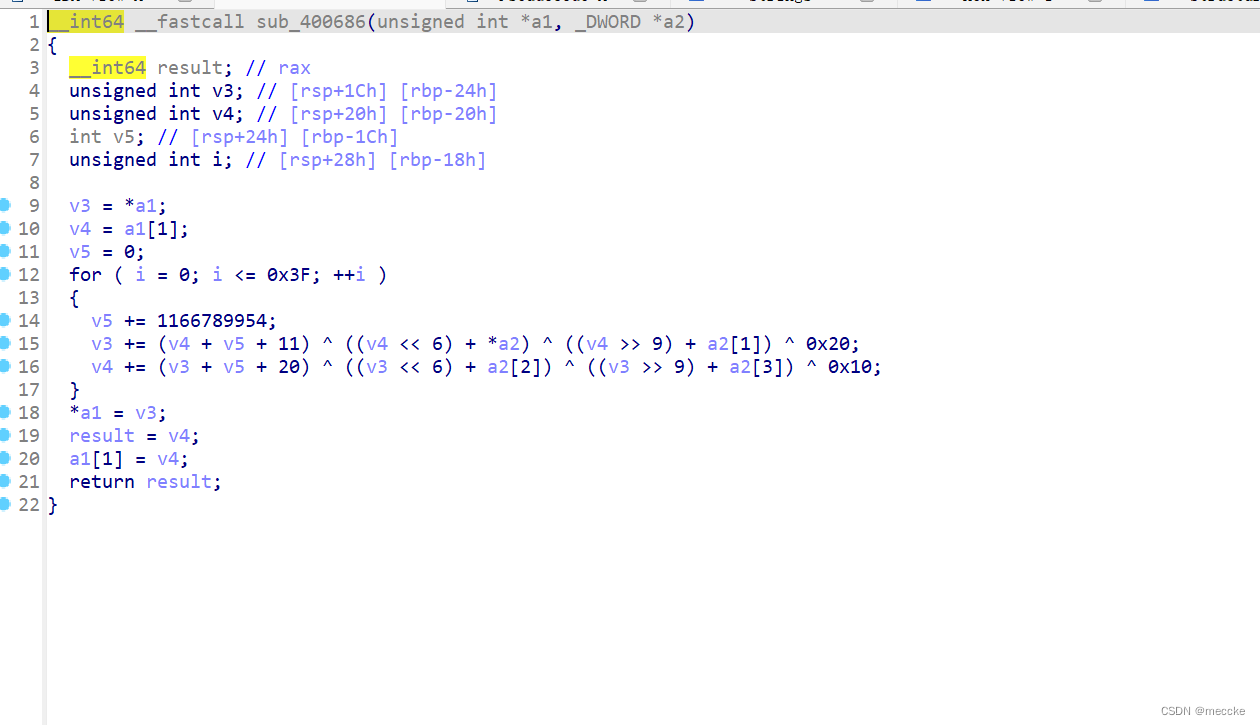
tea加密
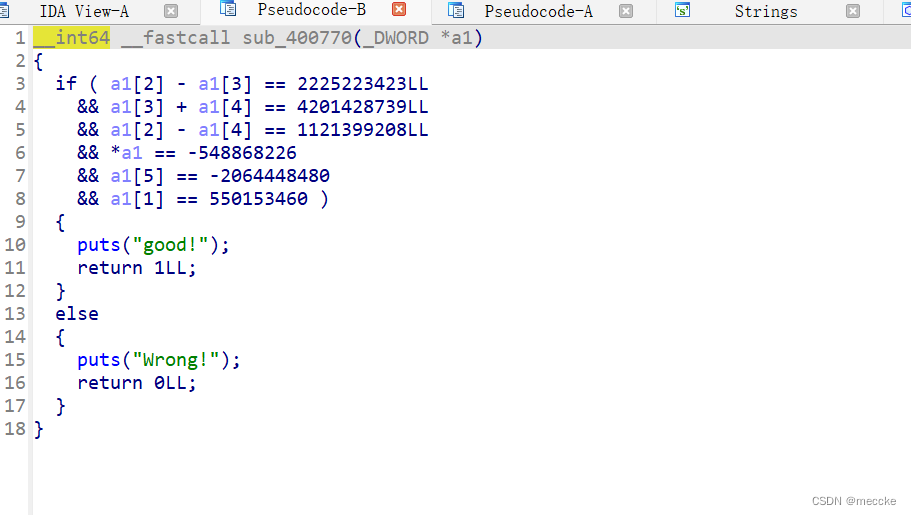
还有一个比较函数
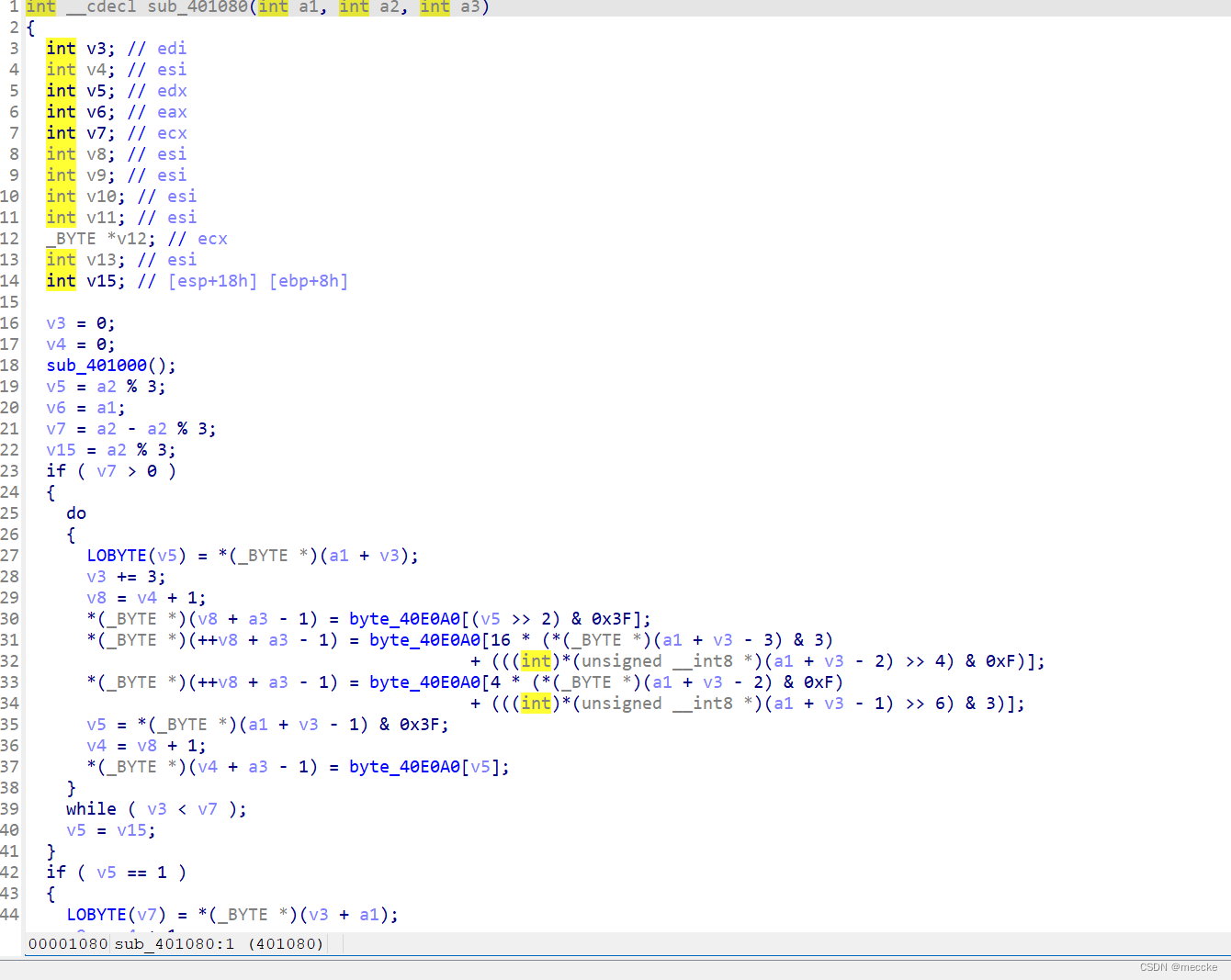
z3解一下
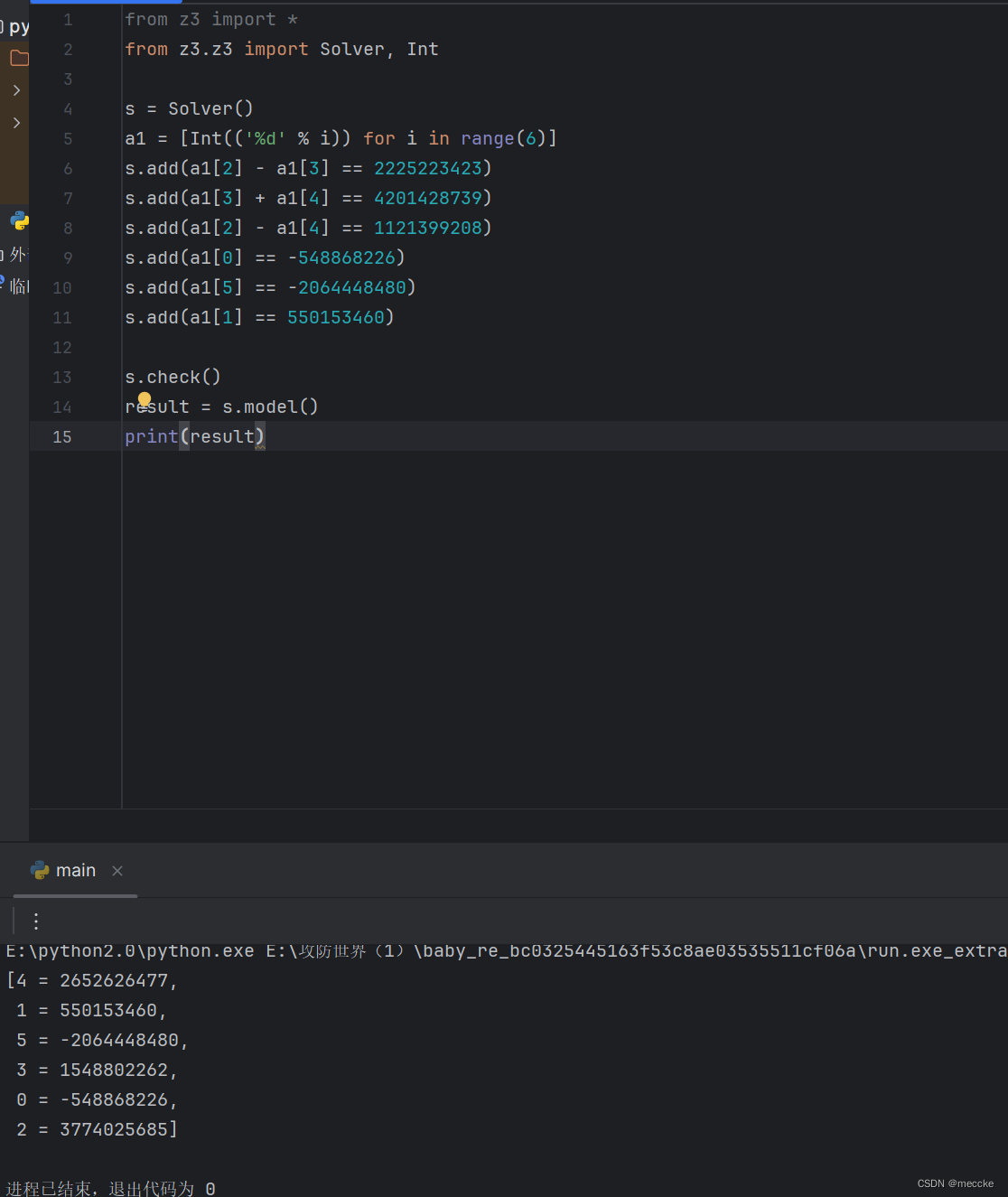
解密
#include <iostream>
using namespace std;
int main() {
int data[6] = { 3746099070,550153460,3774025685,1548802262,2652626477,2230518816 };
unsigned int tmp1, tmp2;
unsigned int v3, v4;
int key[4] = { 2,2,3,4 };
for (int i = 0; i < 5; i +=2) {
v3 = data[i];
v4 = data[i + 1];
int v5 = 1166789954 * 64;
for (int j = 0; j < 64; ++j)
{
v4 -= (v3 + v5 + 20) ^ ((v3 << 6) + key[2]) ^ ((v3 >> 9) + key[3]) ^ 0x10;
v3 -= (v4 + v5 + 11) ^ ((v4 << 6) + key[0]) ^ ((v4 >> 9) + key[1]) ^ 0x20;
v5 -= 1166789954;
}
data[i] = v3;
data[i + 1] = v4;
}
for (unsigned int i = 0; i < 6; i++)
printf("%c%c%c", *((char*)&data[i] + 2), *((char*)&data[i] + 1), *(char*)&data[i]);
}flag{re_is_great!}
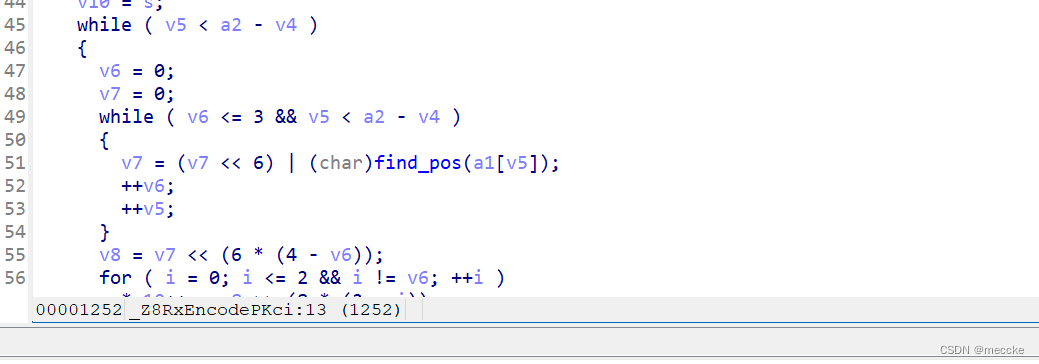
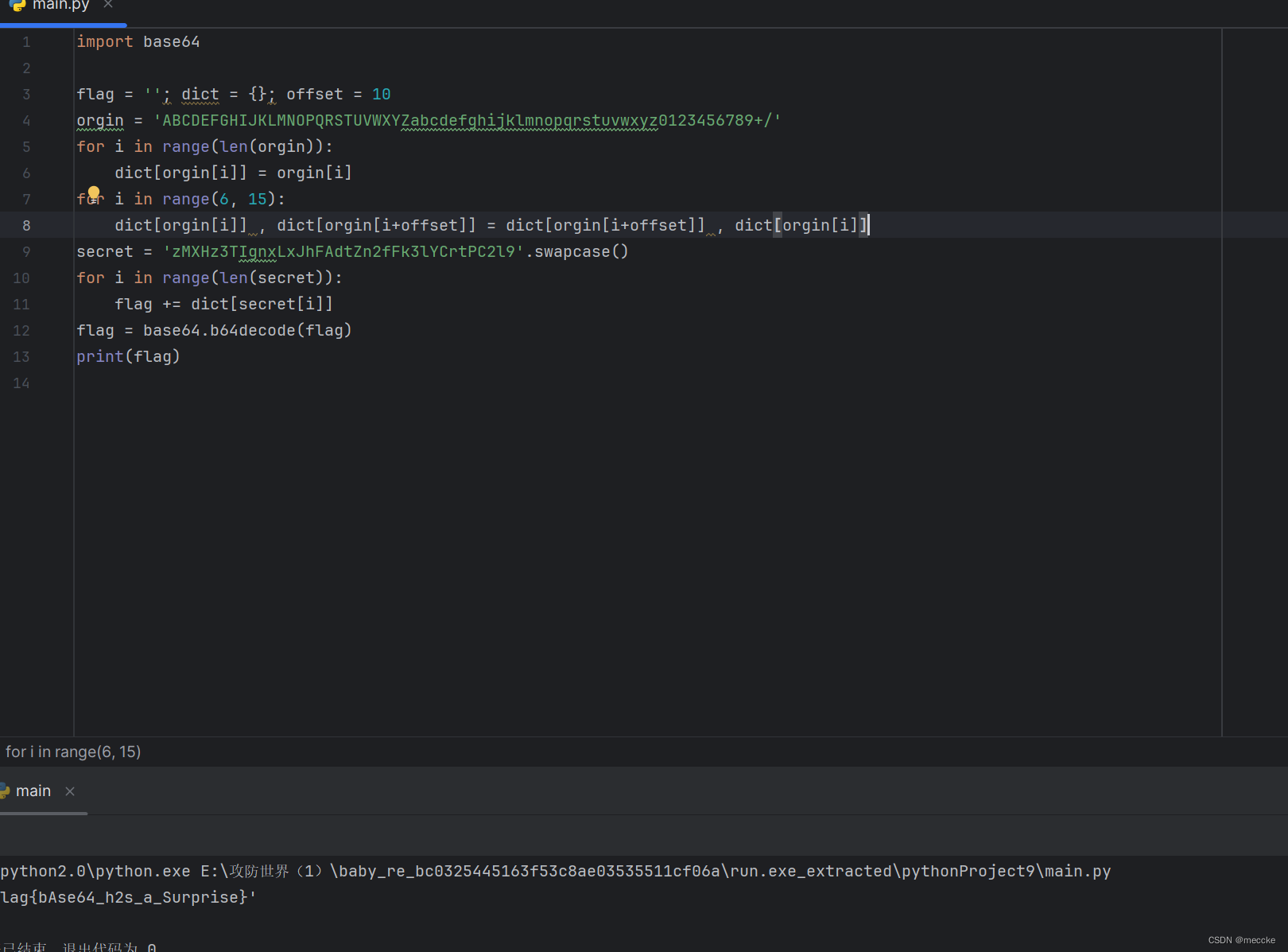
[ACTF新生赛2020]usualCrypt
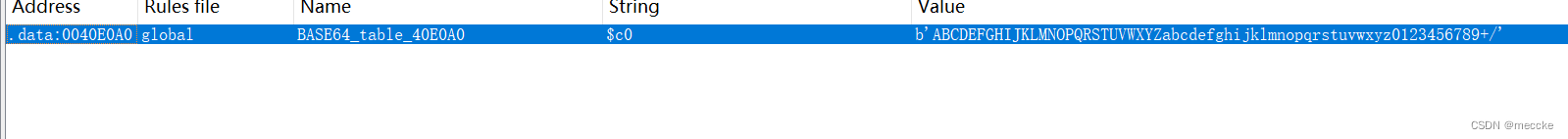
base64
找到变表内容(前面加个k)
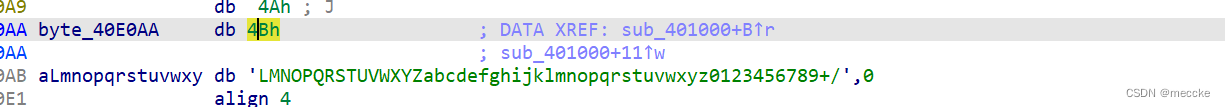
找到加密函数
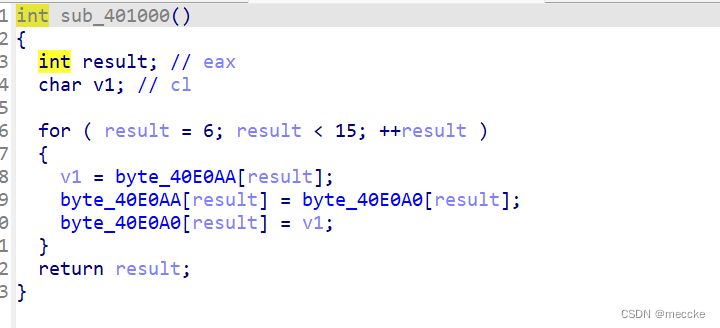
进行了变表加密
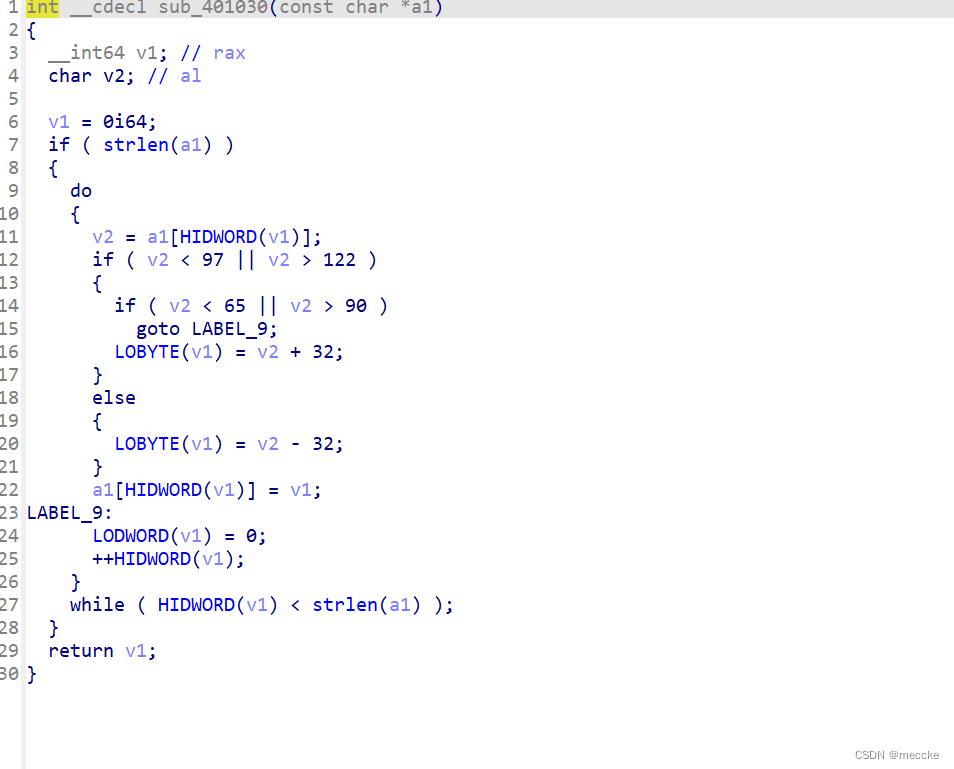
结尾处函数进行了大小写转换
根据逻辑写代码
[ACTF新生赛2020]Universe_final_answer
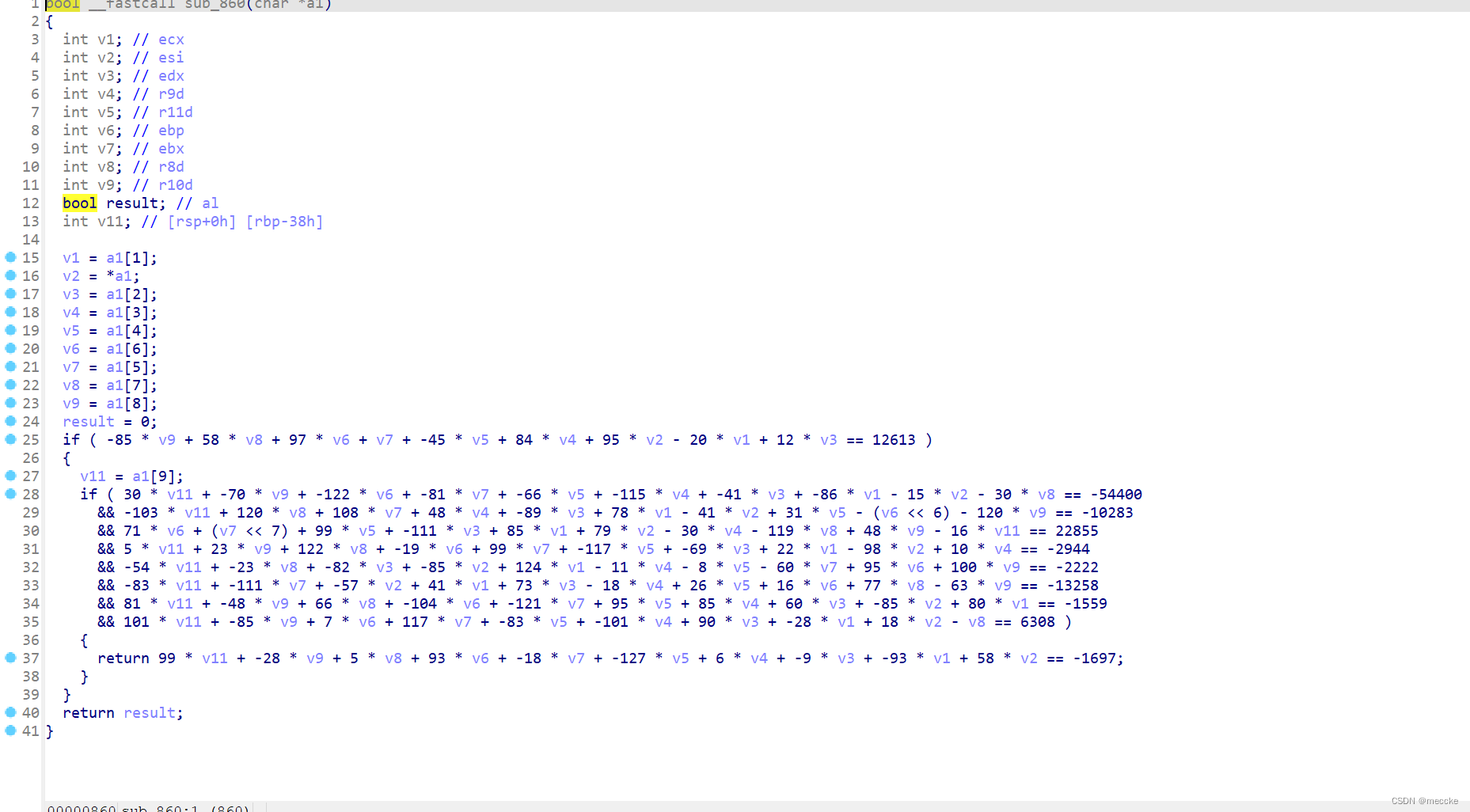
from z3.z3 import Solver, Int, Ints
v1,v2,v3,v4,v5,v6,v7,v8,v9,v11 = Ints('v1 v2 v3 v4 v5 v6 v7 v8 v9 v11')
s = Solver()
s.add(-85 * v9 + 58 * v8 + 97 * v6 + v7 + -45 * v5 + 84 * v4 + 95 * v2 - 20 * v1 + 12 * v3 == 12613)
s.add(30 * v11 + -70 * v9 + -122 * v6 + -81 * v7 + -66 * v5 + -115 * v4 + -41 * v3 + -86 * v1 - 15 * v2 - 30 * v8 == -54400)
s.add(-103 * v11 + 120 * v8 + 108 * v7 + 48 * v4 + -89 * v3 + 78 * v1 - 41 * v2 + 31 * v5 - (v6 * 64) - 120 * v9 == -10283)
s.add(71 * v6 + (v7 * 128) + 99 * v5 + -111 * v3 + 85 * v1 + 79 * v2 - 30 * v4 - 119 * v8 + 48 * v9 - 16 * v11 == 22855)
s.add(5 * v11 + 23 * v9 + 122 * v8 + -19 * v6 + 99 * v7 + -117 * v5 + -69 * v3 + 22 * v1 - 98 * v2 + 10 * v4 == -2944)
s.add(-54 * v11 + -23 * v8 + -82 * v3 + -85 * v2 + 124 * v1 - 11 * v4 - 8 * v5 - 60 * v7 + 95 * v6 + 100 * v9 == -2222)
s.add(-83 * v11 + -111 * v7 + -57 * v2 + 41 * v1 + 73 * v3 - 18 * v4 + 26 * v5 + 16 * v6 + 77 * v8 - 63 * v9 == -13258)
s.add(81 * v11 + -48 * v9 + 66 * v8 + -104 * v6 + -121 * v7 + 95 * v5 + 85 * v4 + 60 * v3 + -85 * v2 + 80 * v1 == -1559)
s.add(101 * v11 + -85 * v9 + 7 * v6 + 117 * v7 + -83 * v5 + -101 * v4 + 90 * v3 + -28 * v1 + 18 * v2 - v8 == 6308)
s.add(99 * v11 + -28 * v9 + 5 * v8 + 93 * v6 + -18 * v7 + -127 * v5 + 6 * v4 + -9 * v3 + -93 * v1 + 58 * v2 == -1697)
check = s.check()
print(check)
model = s.model()
print(model)输入key
xyctf复现
聪明的信使
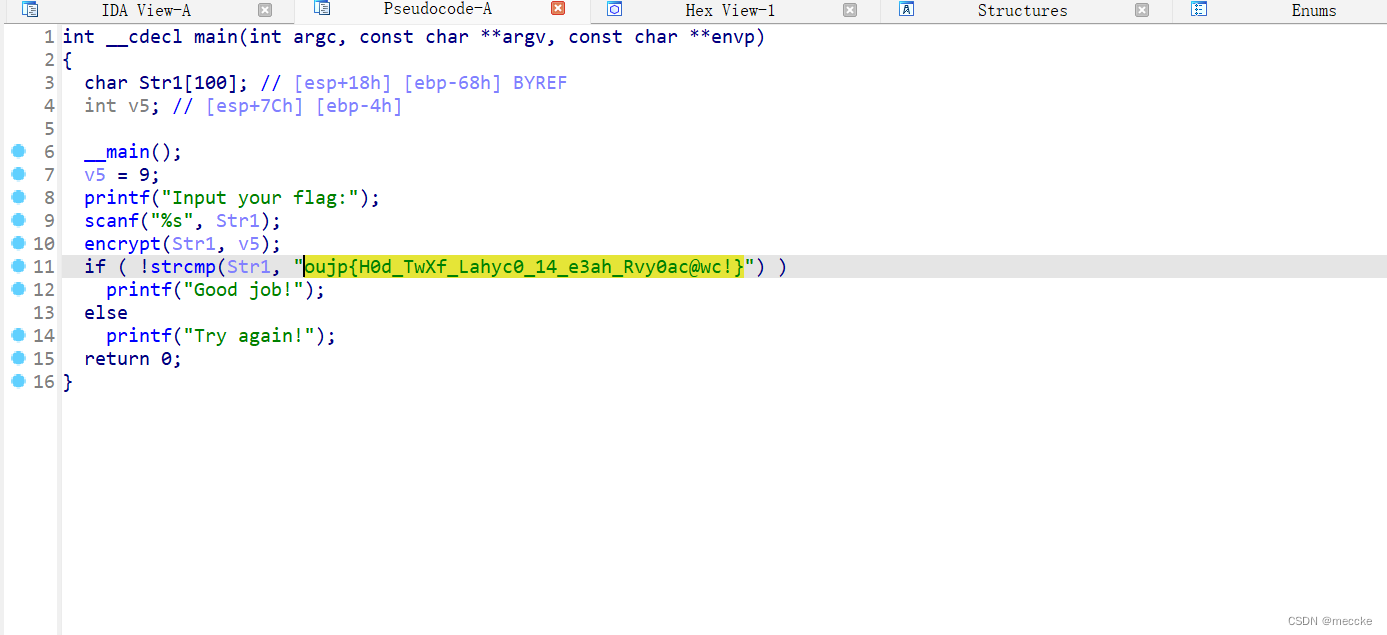
看着像凯撒加密
脚本爆破
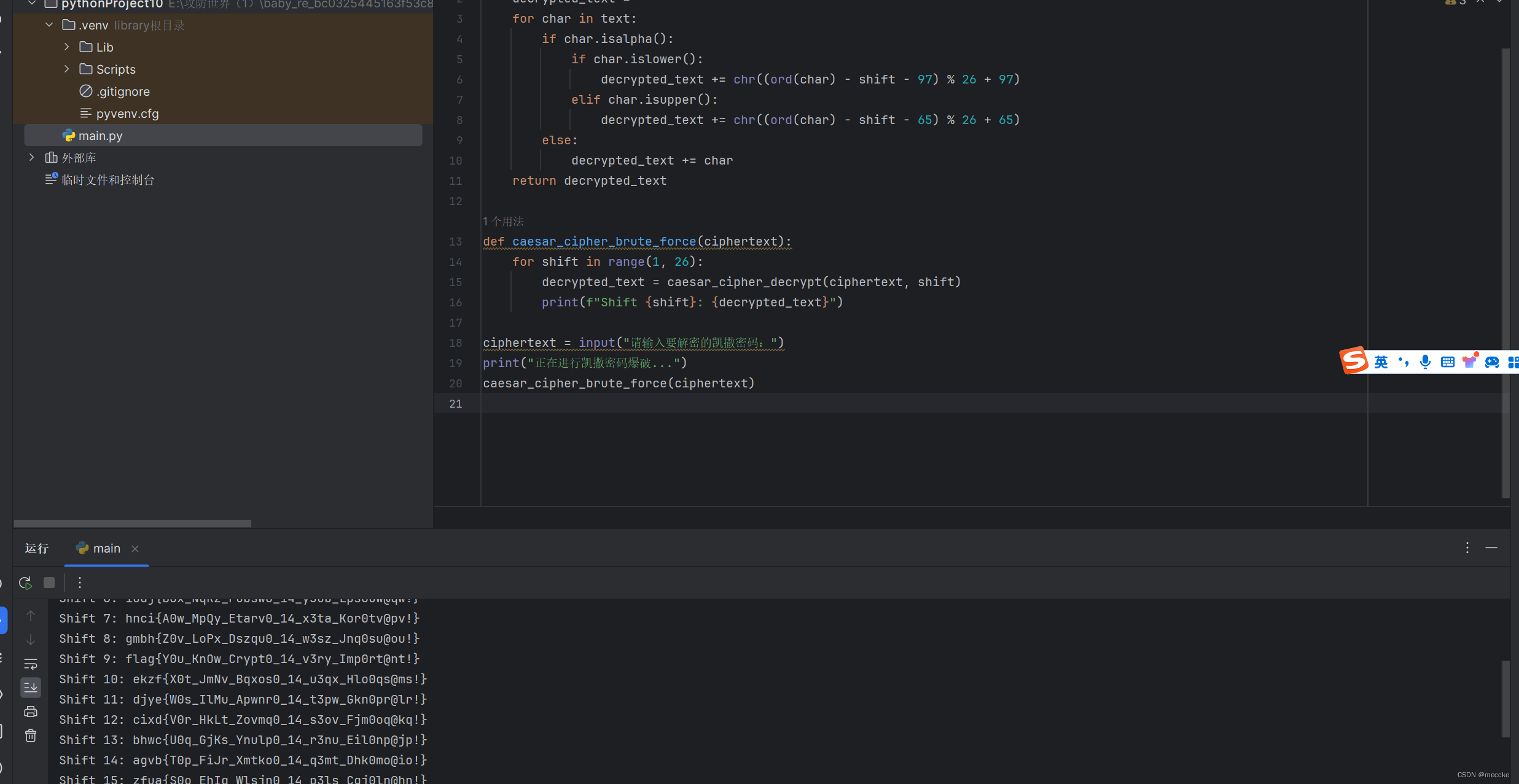
给阿姨倒一杯卡布奇诺
点进加密函数
tea加密,写脚本
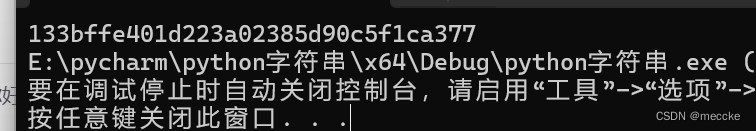
ezmath
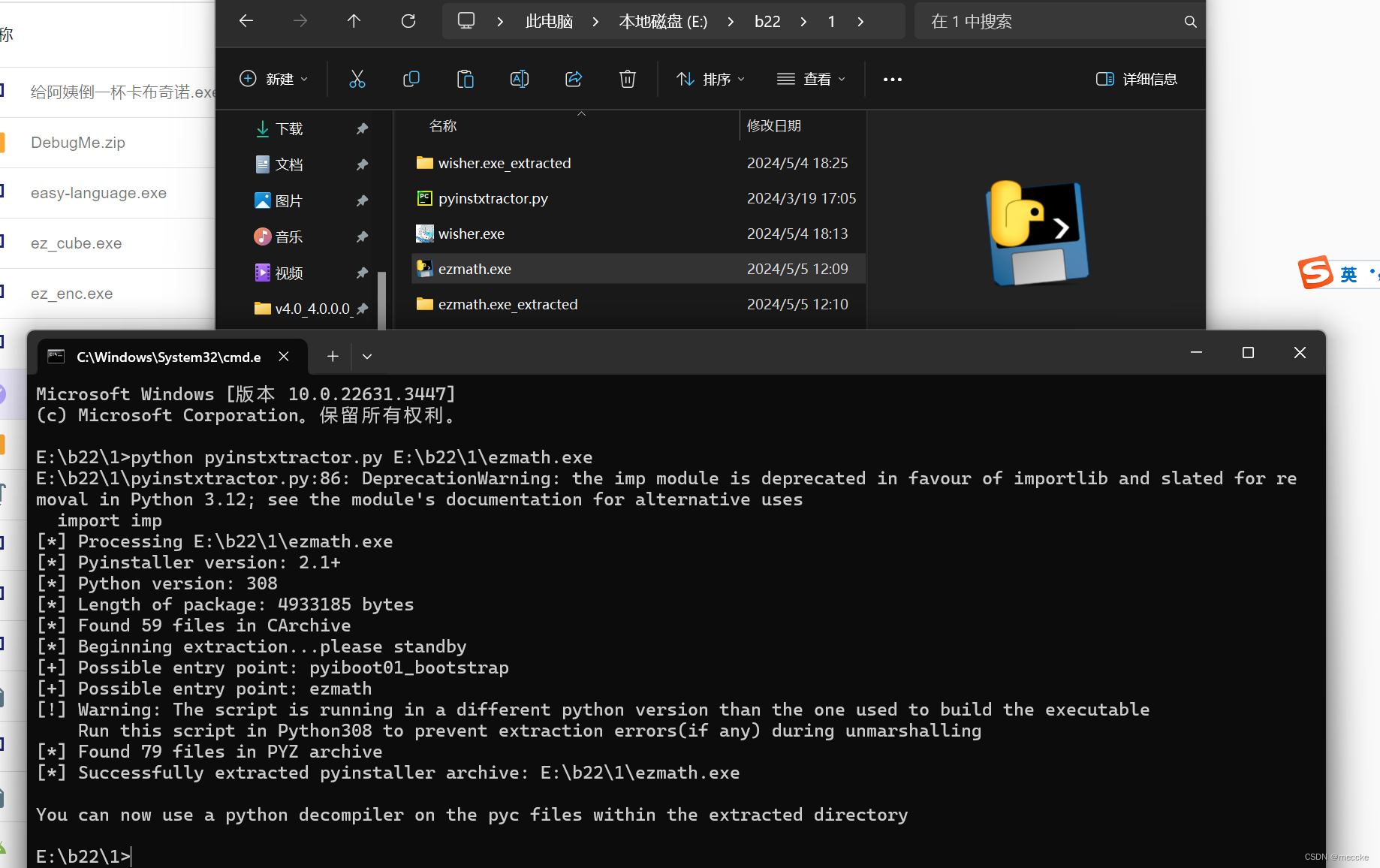
python解包
找到ezmath,改成pyc文件
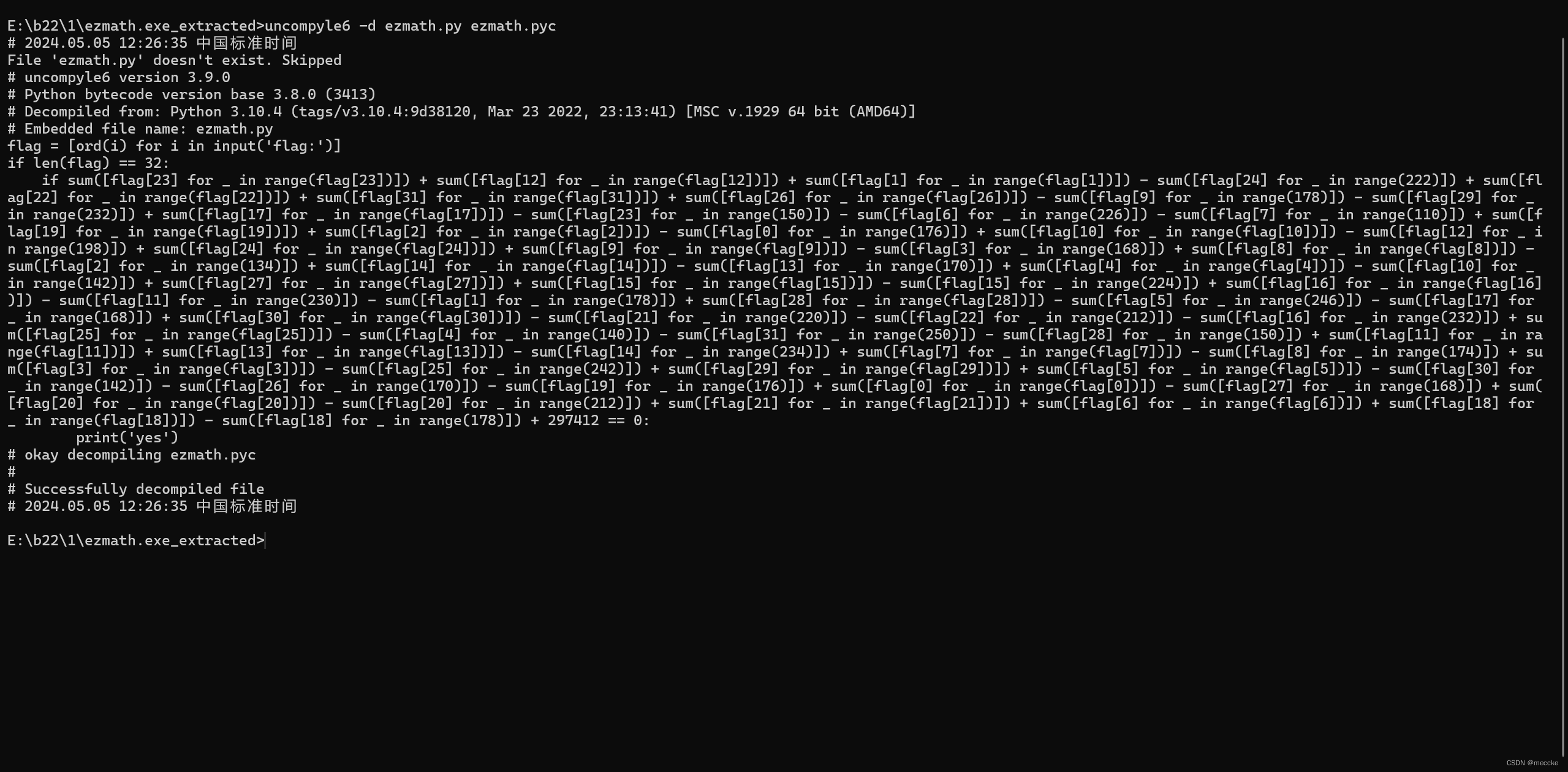
改成py文件
看不懂,上gpt!!!
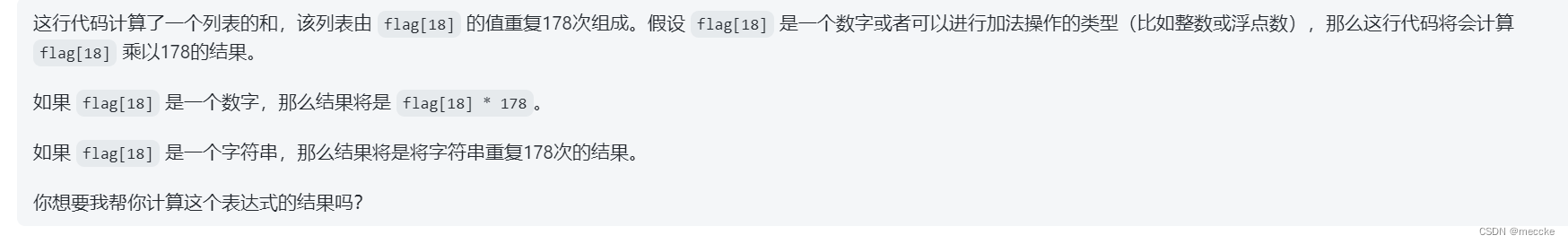
XYCTF{7WqYGcUputpTYXnjKoyUTKtG}
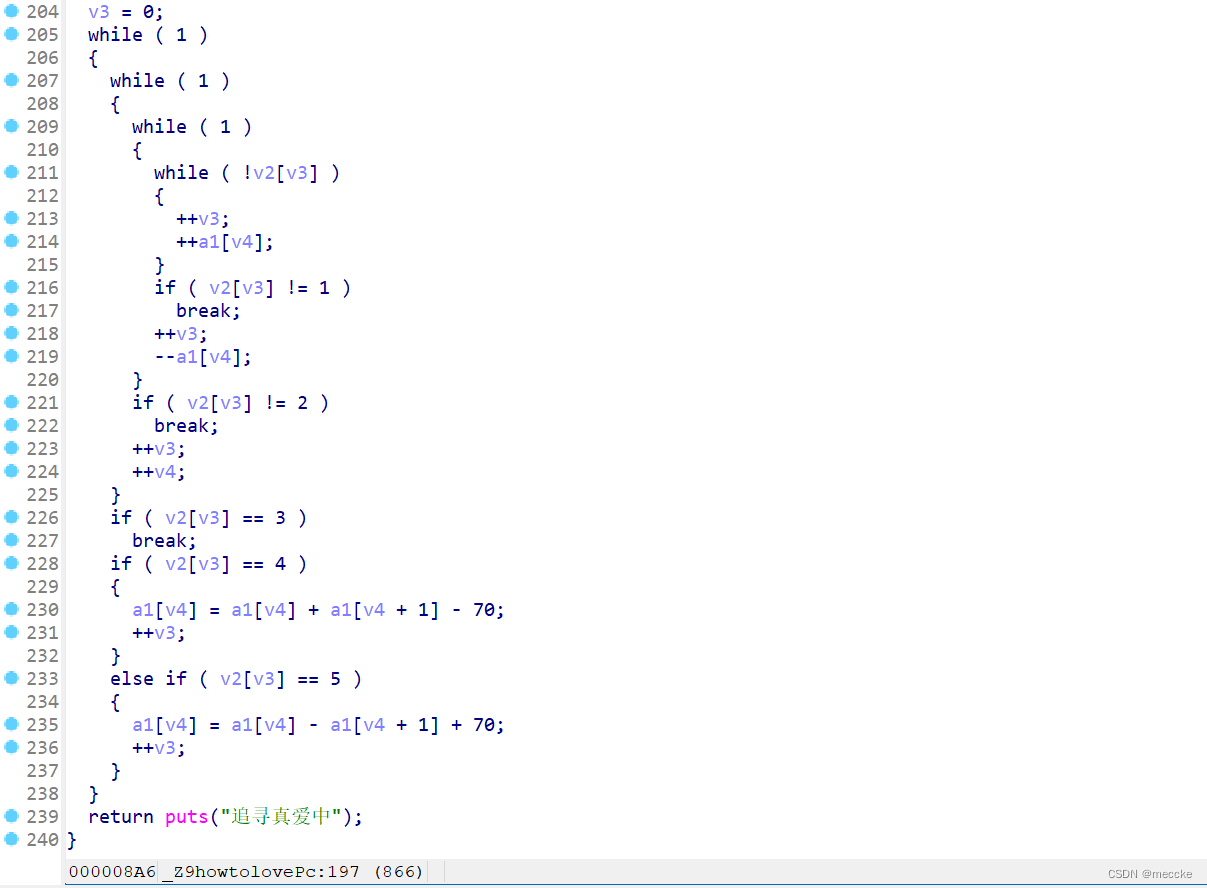
ez_enc
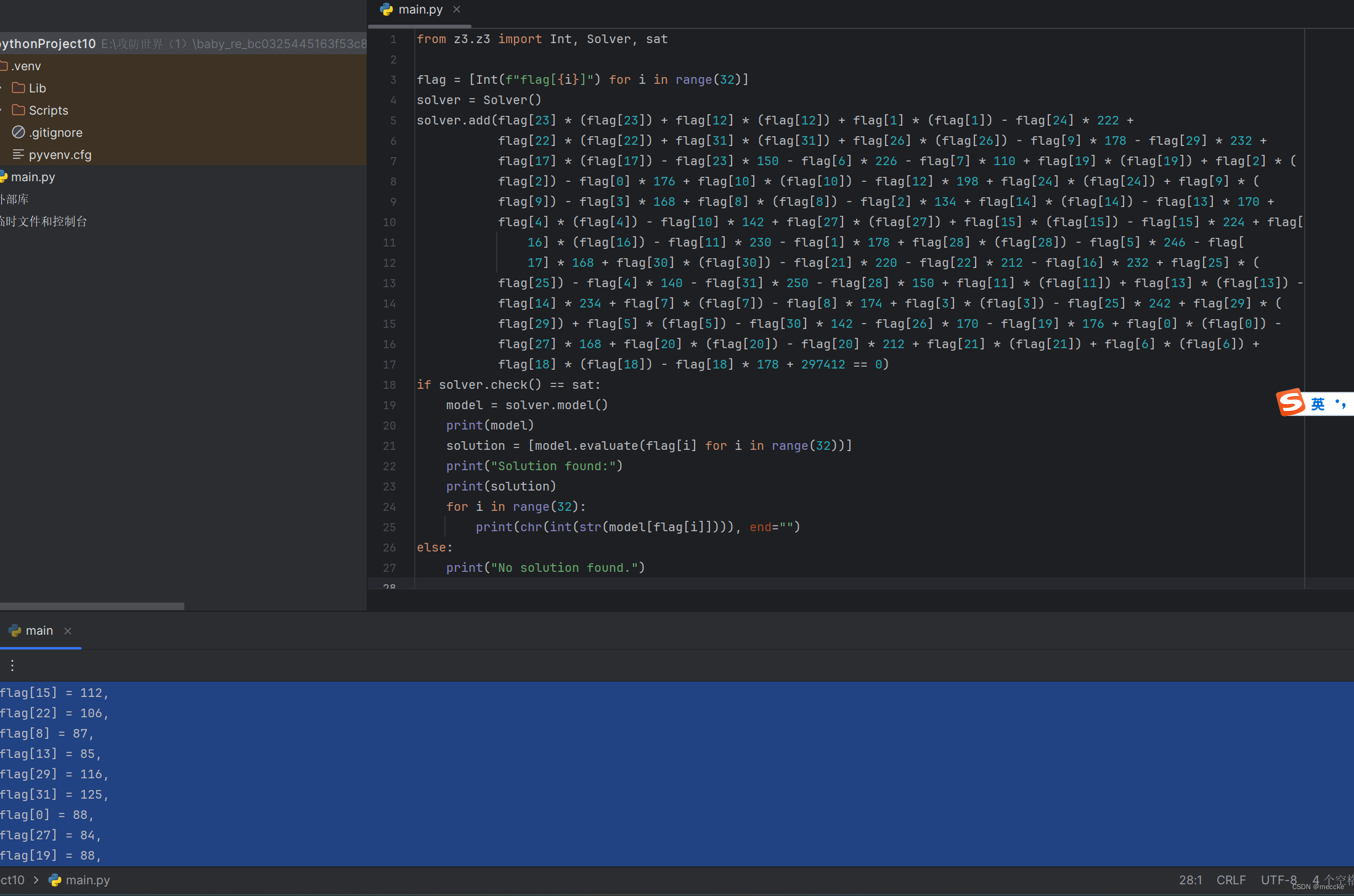
ida打开,根据字符串定位函数
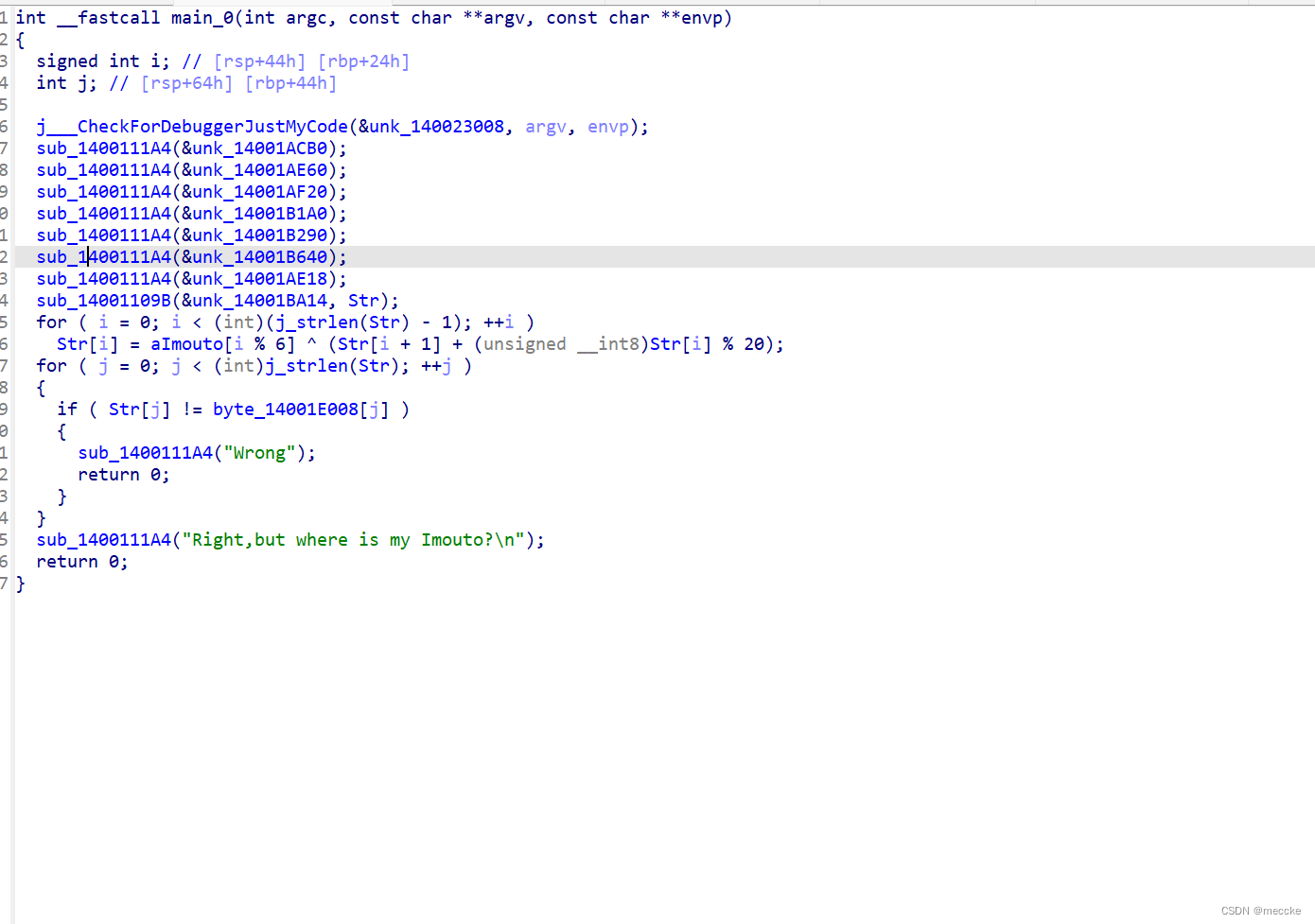
关键是第15行之后的内容
str进行加密后和byte_那一堆进行了比较,点进去可以看见内容
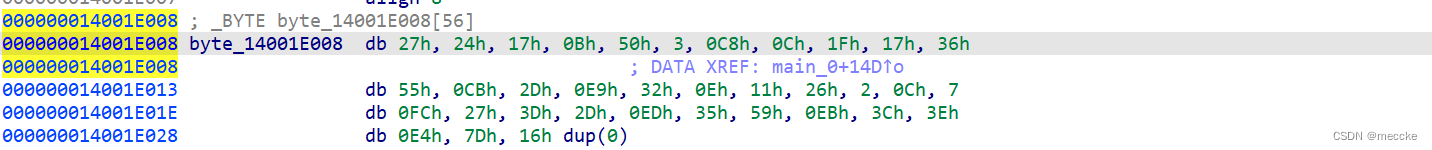
递归算法
猜一下开头直接爆破
据说也可以用z3解,回头试试
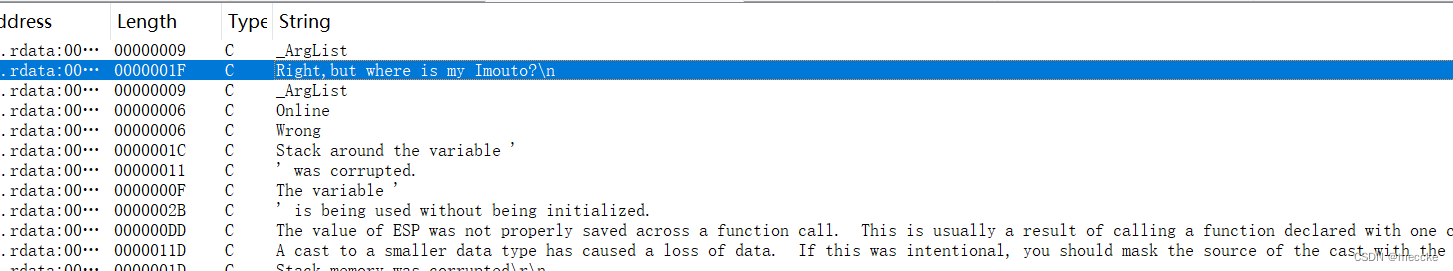
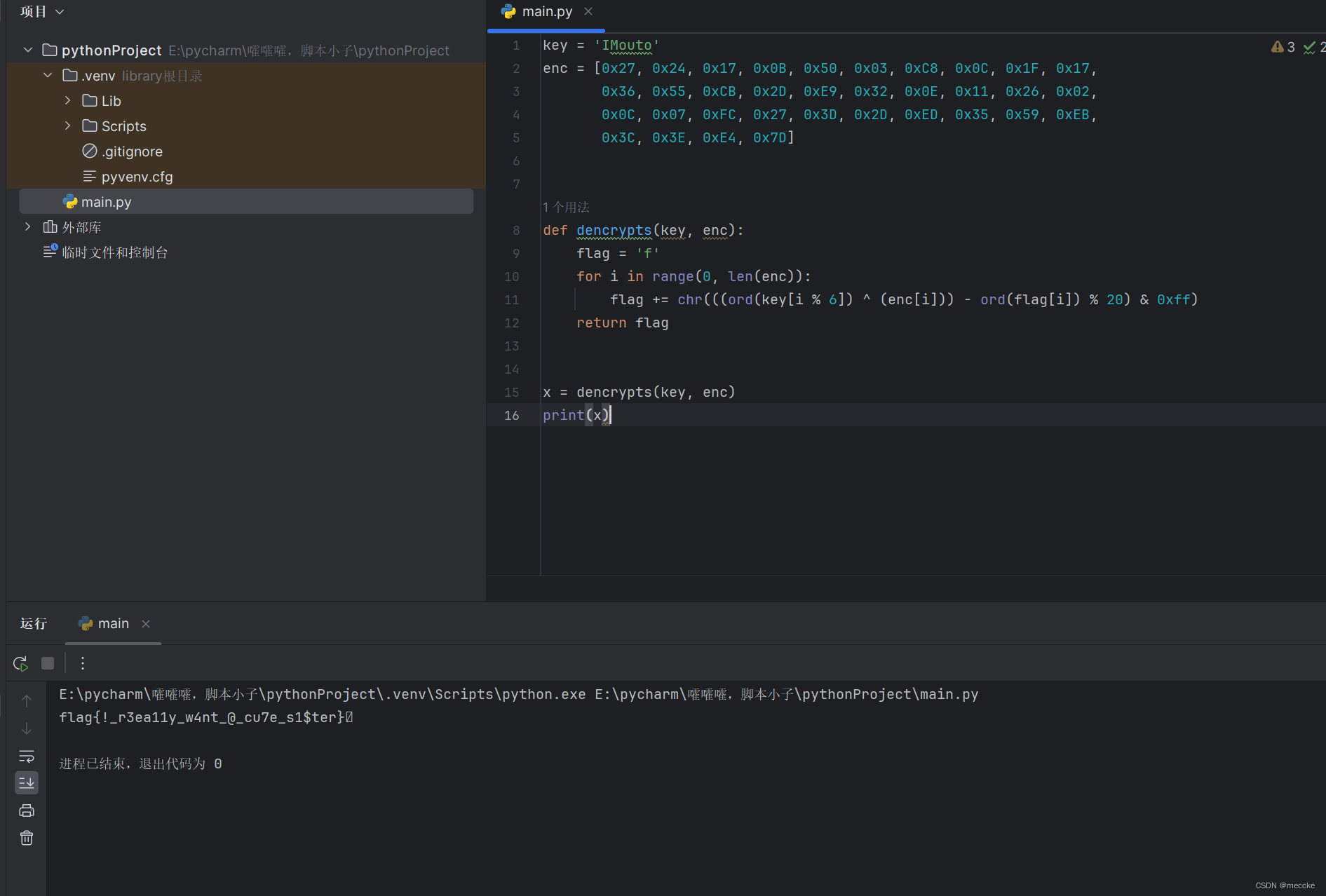
baby-unity
感觉是第一次做unity题,怪难的
下载附件,
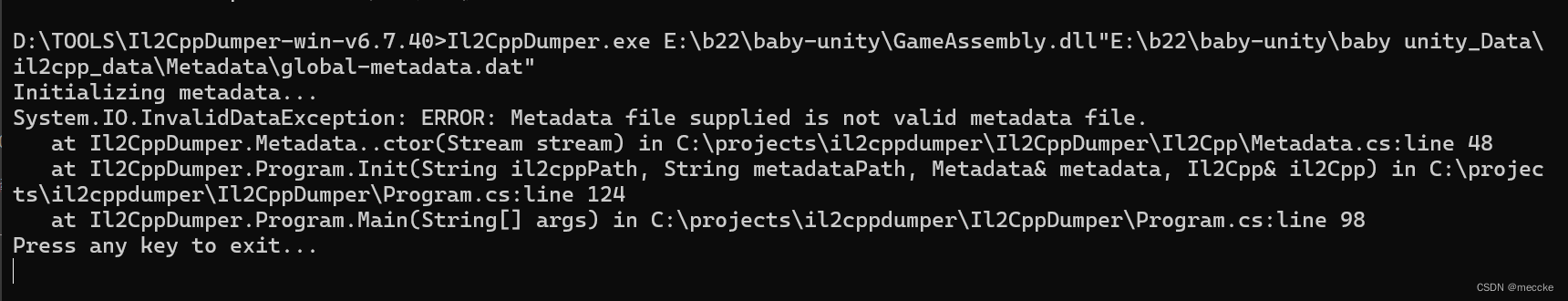
一开始il2cppdumper用不了,看了大佬wp是加了upx壳
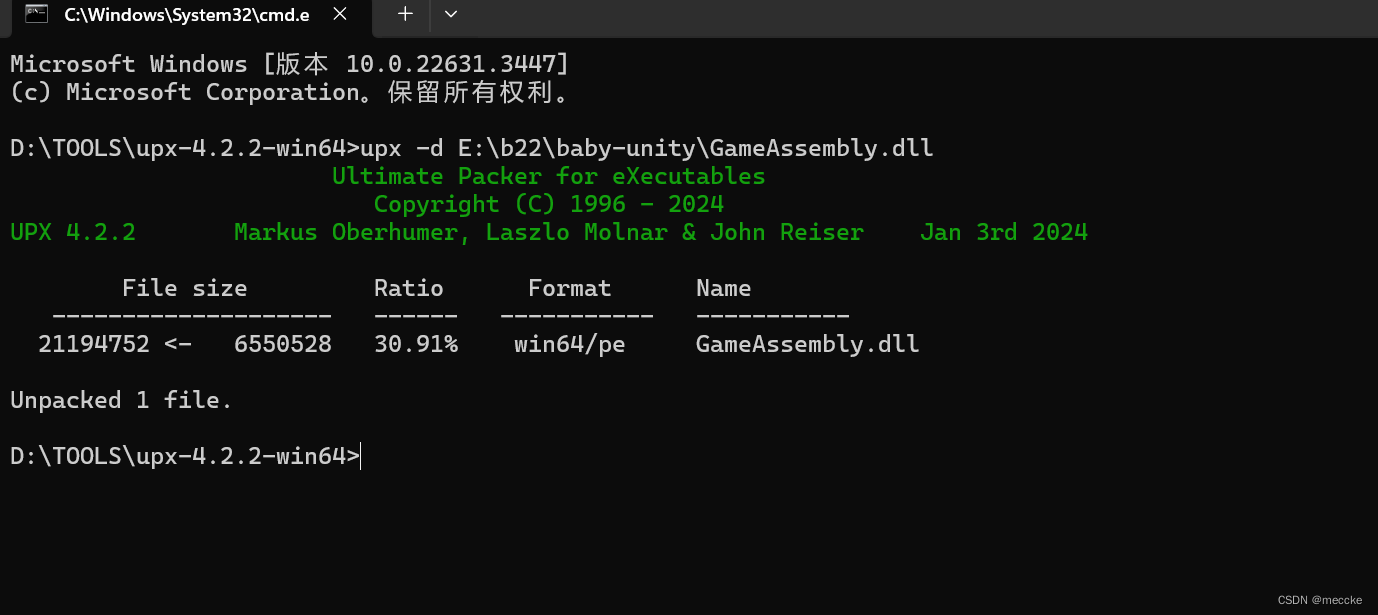
我脱

新建两个文件夹
将两个关键文件复制进input文件
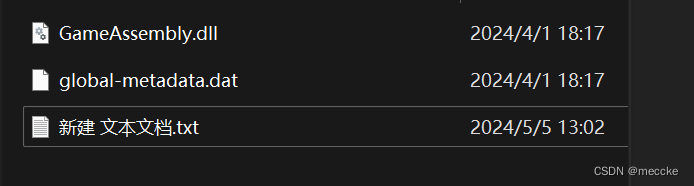
新建一个文档
..\Il2CppDumper.exe GameAssembly.dll global-metadata.dat ..\output
修改为bat文件
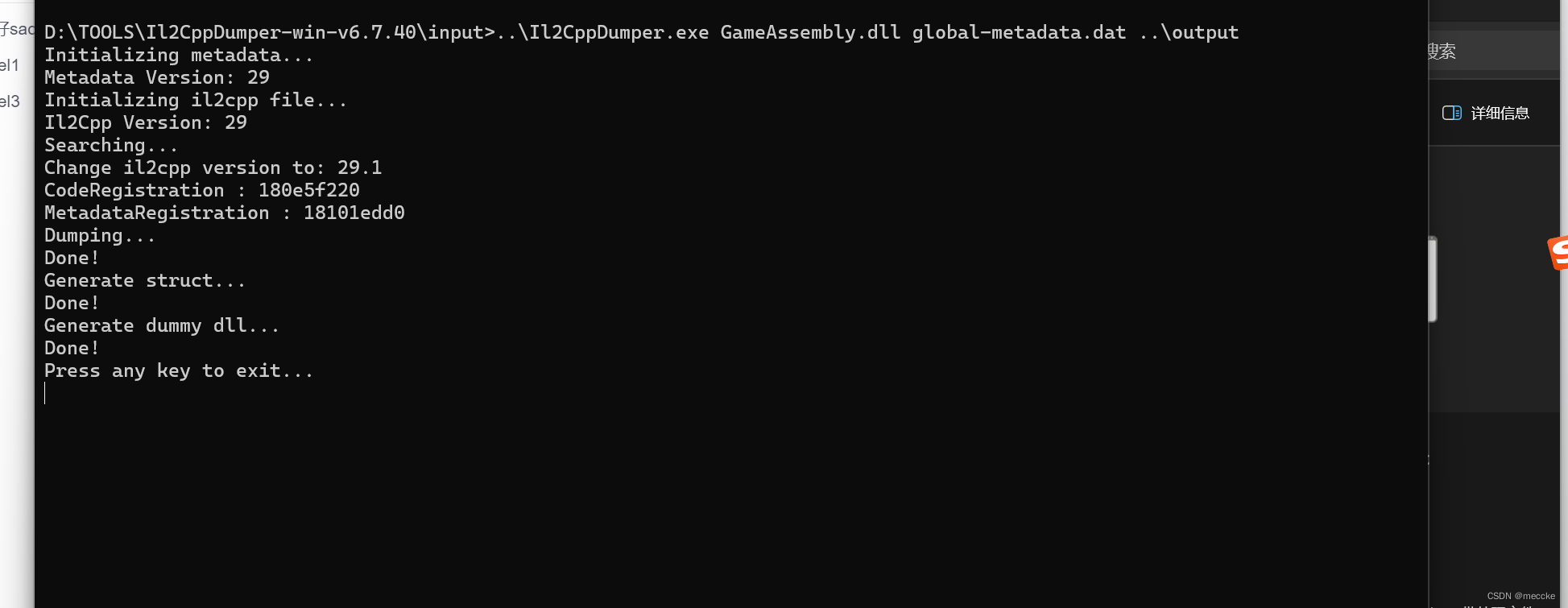
双击运行
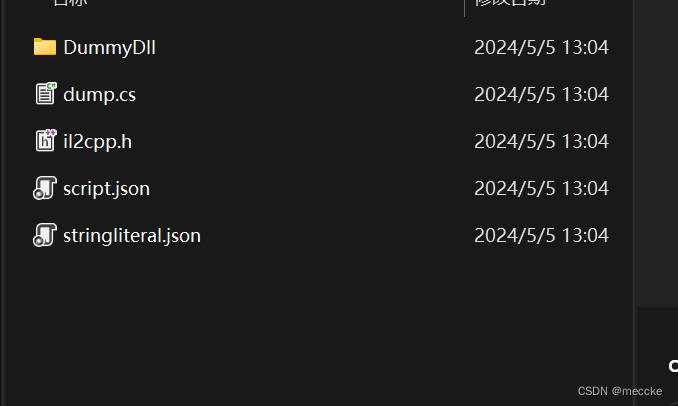
output里面就有东西了
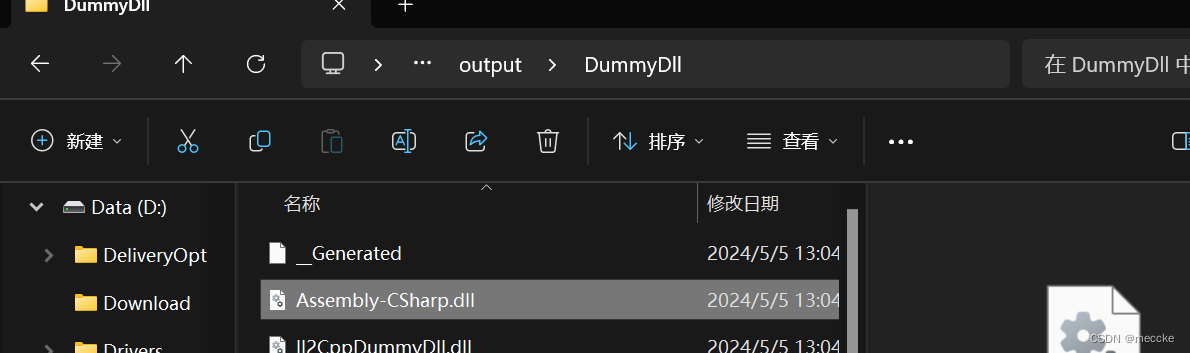
把这个拖进dnspy
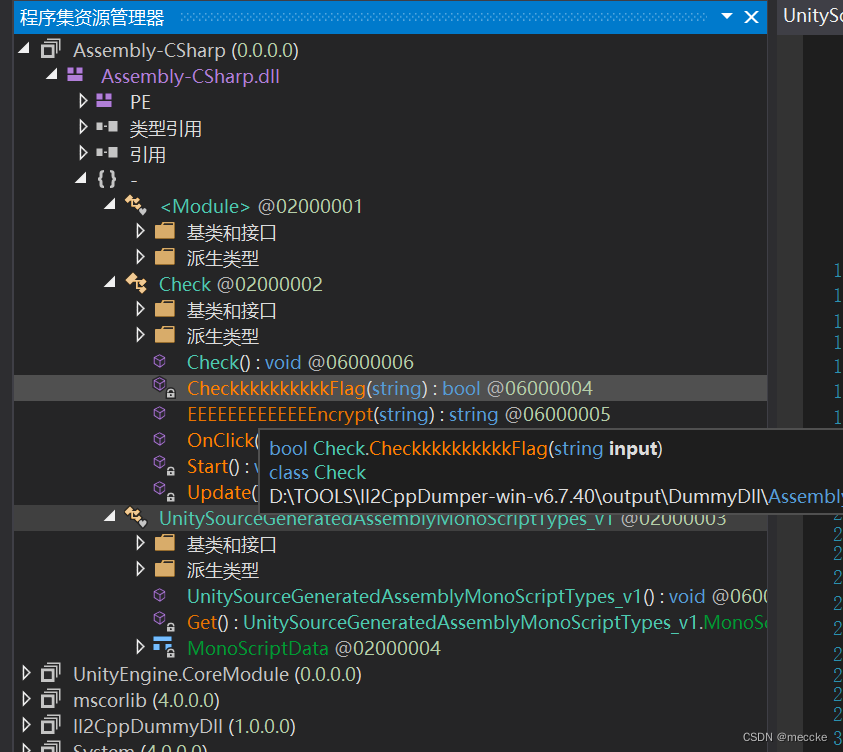
找到一个带flag的函数
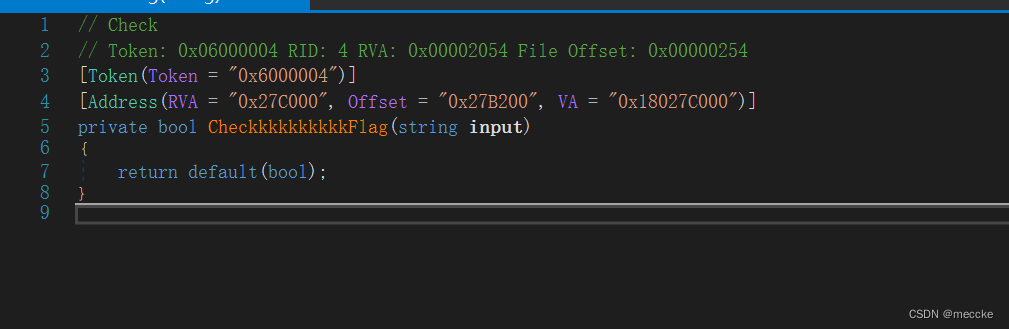
GameAssembly拖进ida
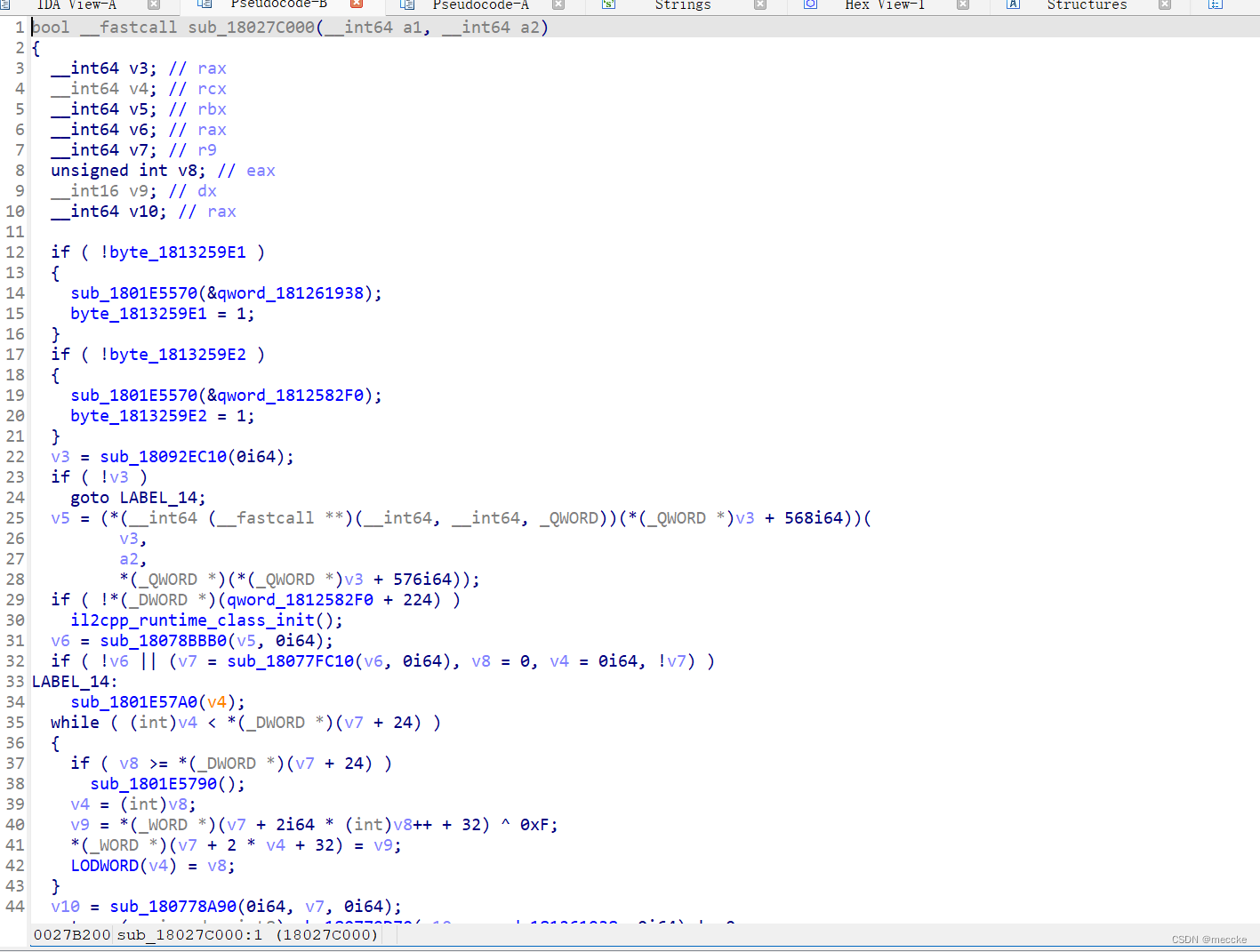
找到提到的函数
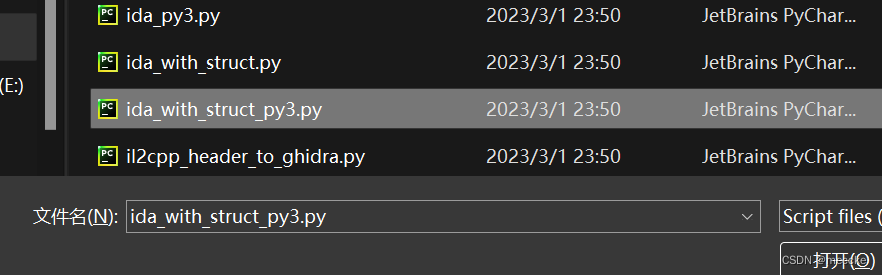
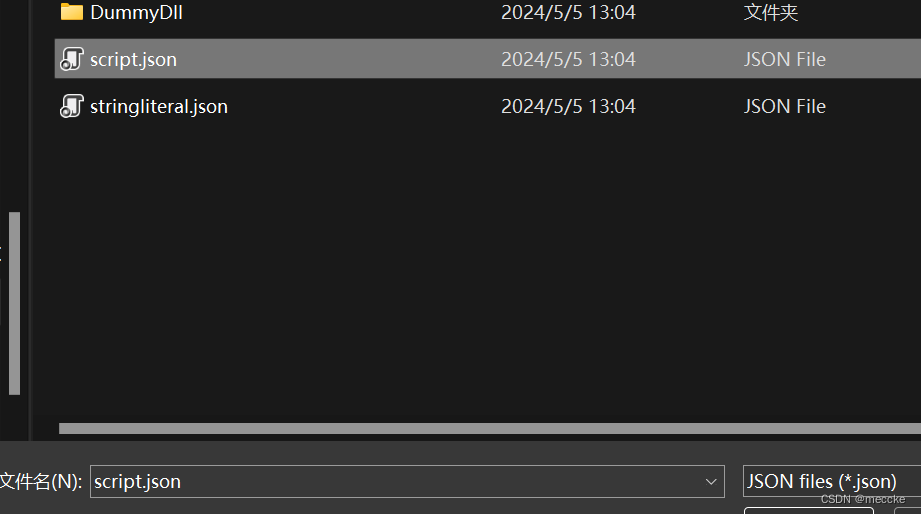
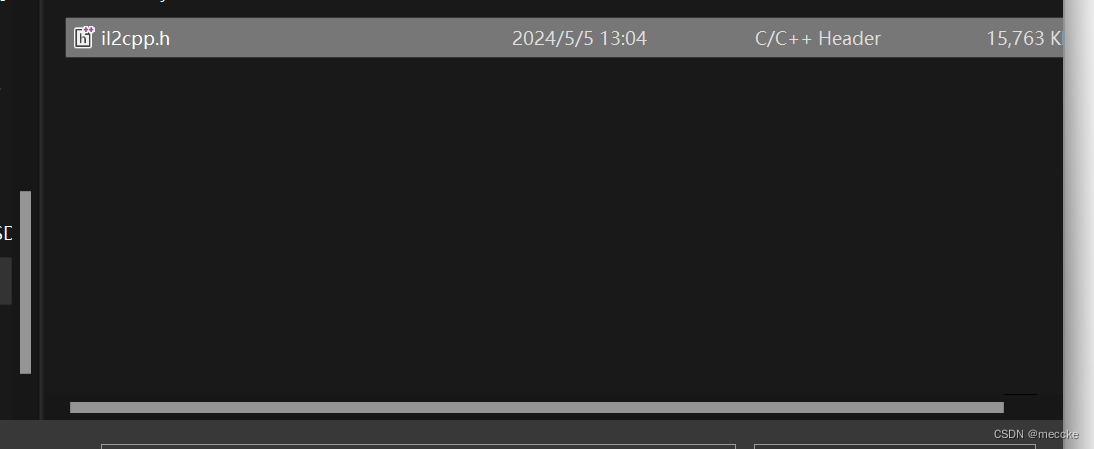
alt+f7依次导入上面三个文件
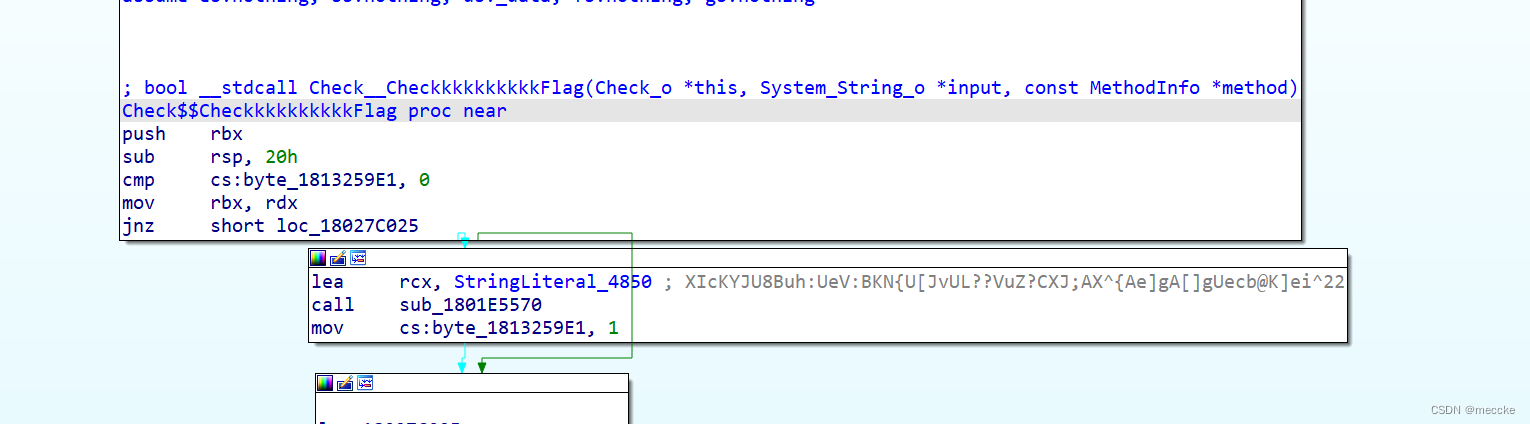
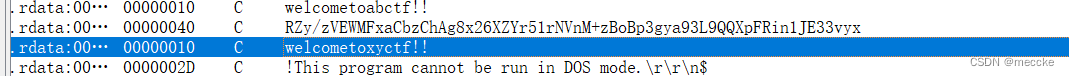
找到密文
扔给厨子让他用魔法
厨子是个好家伙XYCTF{389f6900-e12d-4c54-a85d-64a54af9f84c}
easy language
go语言还是不太会
定位字符串,aes-ecb加密
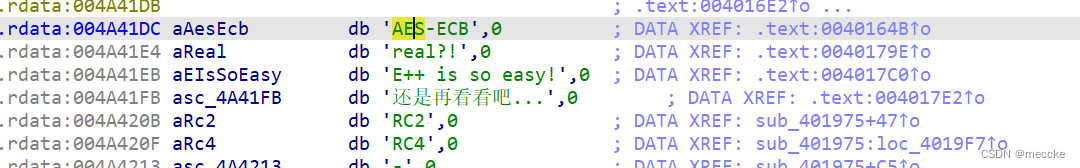
还有bse64
看wp找到密文和key
emmmm,迷迷糊糊
ez_cube
对魔方进行了初始化
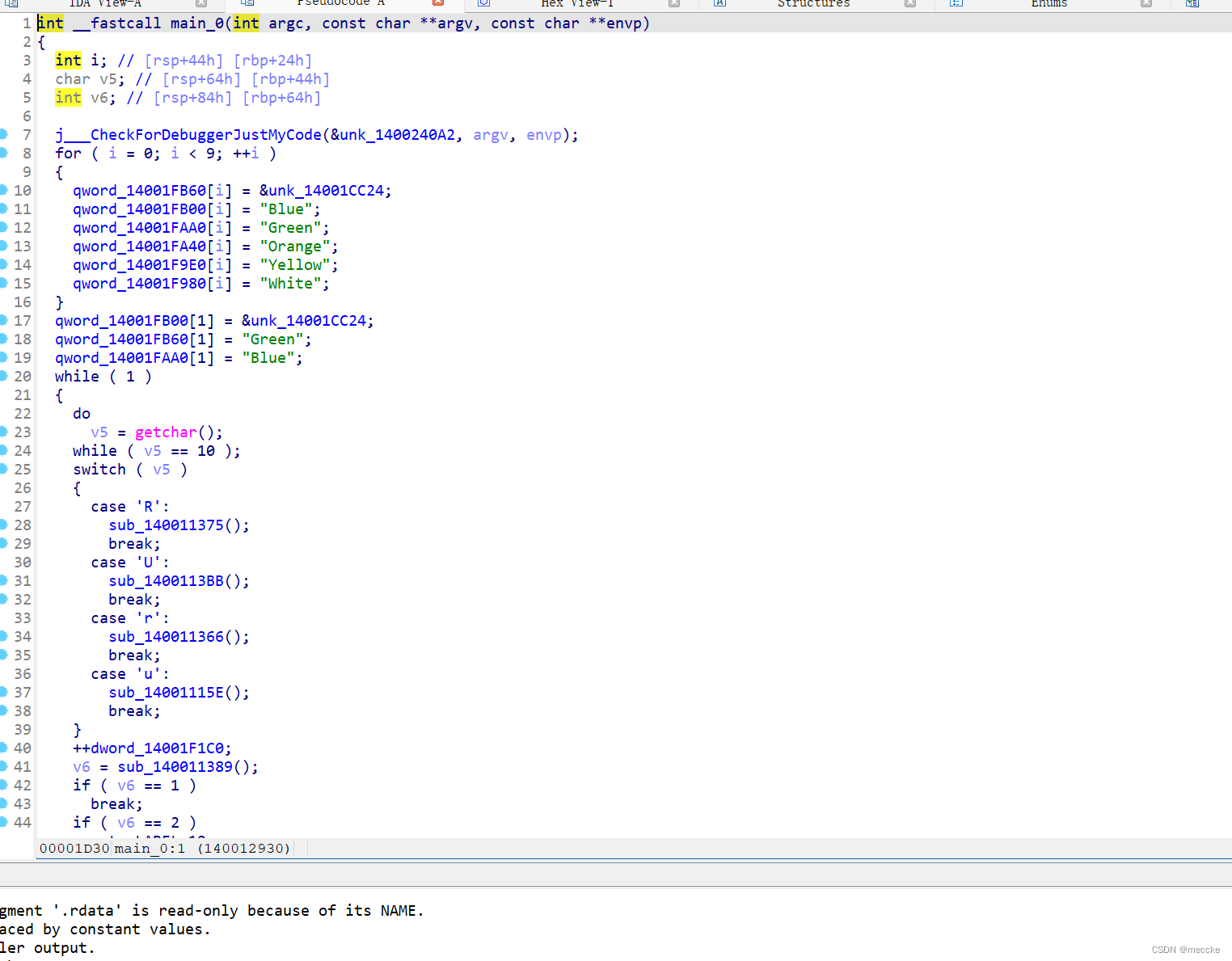
然后定义了四个函数,对魔方进行操作
import itertools
from tqdm import tqdm
def reset():
global pr, pb, pg, po, py, pw
pr = [0] * 9
pb = [1] * 9
pg = [2] * 9
po = [3] * 9
py = [4] * 9
pw = [5] * 9
pb[1] = 0
pr[1] = 2
pg[1] = 1
def R():
global pr, pb, pg, po, py, pw
v0 = pr[2];
v1 = pr[5];
v2 = pr[8];
pr[2] = pw[2];
pr[5] = pw[5];
pr[8] = pw[8];
pw[2] = po[6];
pw[5] = po[3];
pw[8] = po[0];
po[0] = py[8];
po[3] = py[5];
po[6] = py[2];
py[2] = v0;
py[5] = v1;
py[8] = v2;
v3 = pg[1];
pg[1] = pg[3];
pg[3] = pg[7];
pg[7] = pg[5];
pg[5] = v3;
v4 = pg[0];
pg[0] = pg[6];
pg[6] = pg[8];
pg[8] = pg[2];
pg[2] = v4;
def U():
global pr, pb, pg, po, py, pw
v0 = pr[0];
v1 = pr[1];
v2 = pr[2];
pr[0] = pg[0];
pr[1] = pg[1];
pr[2] = pg[2];
pg[0] = po[0];
pg[1] = po[1];
pg[2] = po[2];
po[0] = pb[0];
po[1] = pb[1];
po[2] = pb[2];
pb[0] = v0;
pb[1] = v1;
pb[2] = v2;
v3 = py[1];
py[1] = py[3];
py[3] = py[7];
py[7] = py[5];
py[5] = v3;
v4 = py[0];
py[0] = py[6];
py[6] = py[8];
py[8] = py[2];
py[2] = v4;
def r():
global pr, pb, pg, po, py, pw
v0 = pr[2];
v1 = pr[5];
v2 = pr[8];
pr[2] = py[2];
pr[5] = py[5];
pr[8] = py[8];
py[2] = po[6];
py[5] = po[3];
py[8] = po[0];
po[0] = pw[8];
po[3] = pw[5];
po[6] = pw[2];
pw[2] = v0;
pw[5] = v1;
pw[8] = v2;
v3 = pg[1];
pg[1] = pg[5];
pg[5] = pg[7];
pg[7] = pg[3];
pg[3] = v3;
v4 = pg[0];
pg[0] = pg[2];
pg[2] = pg[8];
pg[8] = pg[6];
pg[6] = v4;
def u():
global pr, pb, pg, po, py, pw
v0 = pr[0];
v1 = pr[1];
v2 = pr[2];
pr[0] = pb[0];
pr[1] = pb[1];
pr[2] = pb[2];
pb[0] = po[0];
pb[1] = po[1];
pb[2] = po[2];
po[0] = pg[0];
po[1] = pg[1];
po[2] = pg[2];
pg[0] = v0;
pg[1] = v1;
pg[2] = v2;
v3 = py[1];
py[1] = py[5];
py[5] = py[7];
py[7] = py[3];
py[3] = v3;
v4 = py[0];
py[0] = py[2];
py[2] = py[8];
py[8] = py[6];
py[6] = v4;
if __name__ == '__main__':
a = []
for l in range(2, 13):
a += itertools.product('RrUu', repeat=l)
for s in tqdm(a):
reset()
for c in s:
if c == 'R':
R()
elif c == 'r':
r()
elif c == 'U':
U()
elif c == 'u':
u()
if not all(all(x == t[0] for x in t) for t in [pr, pb, pg]):
continue
print(''.join(s))
借鉴一下大佬的脚本
![]()
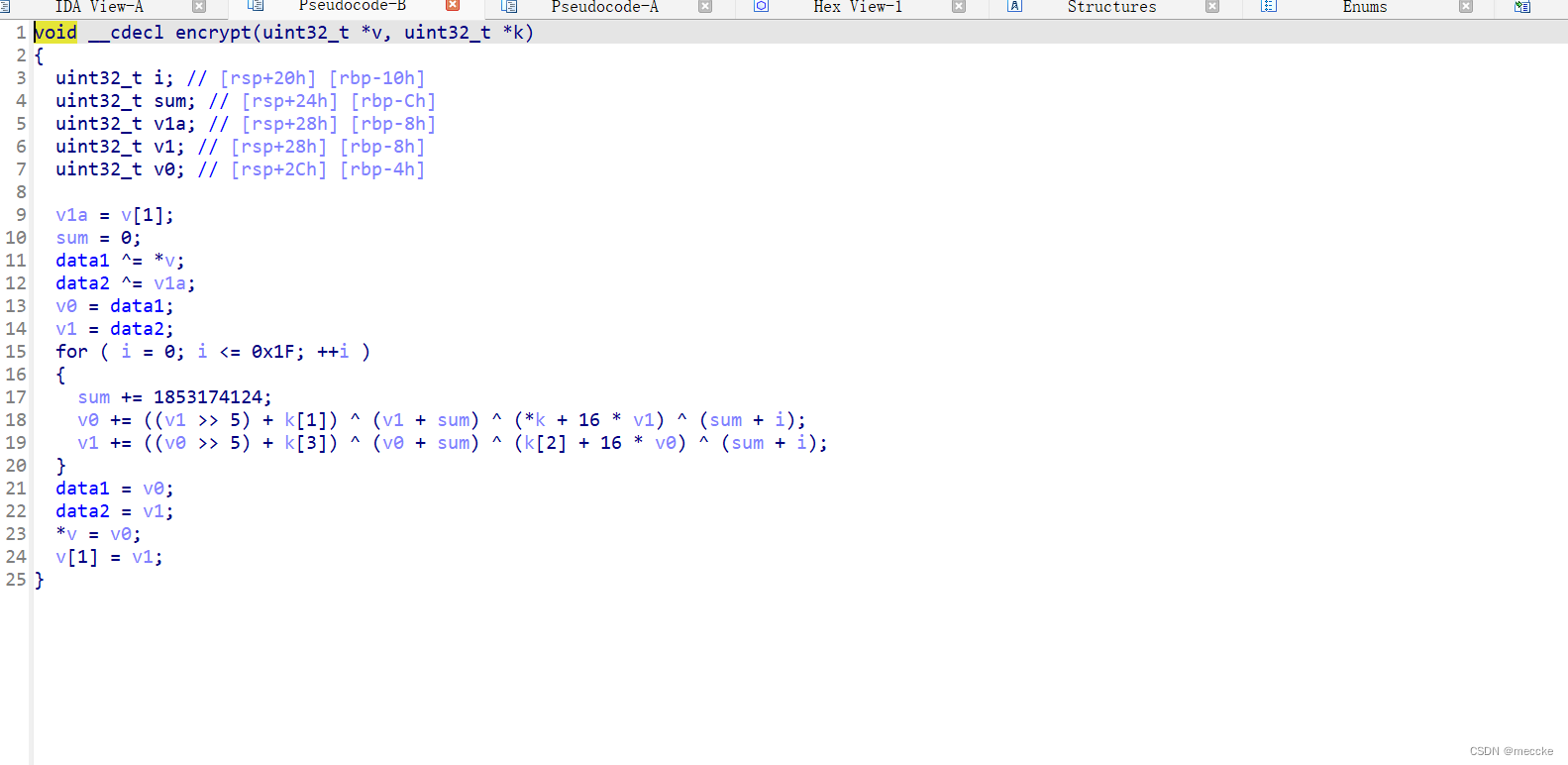
舔狗四部曲 -- 简爱
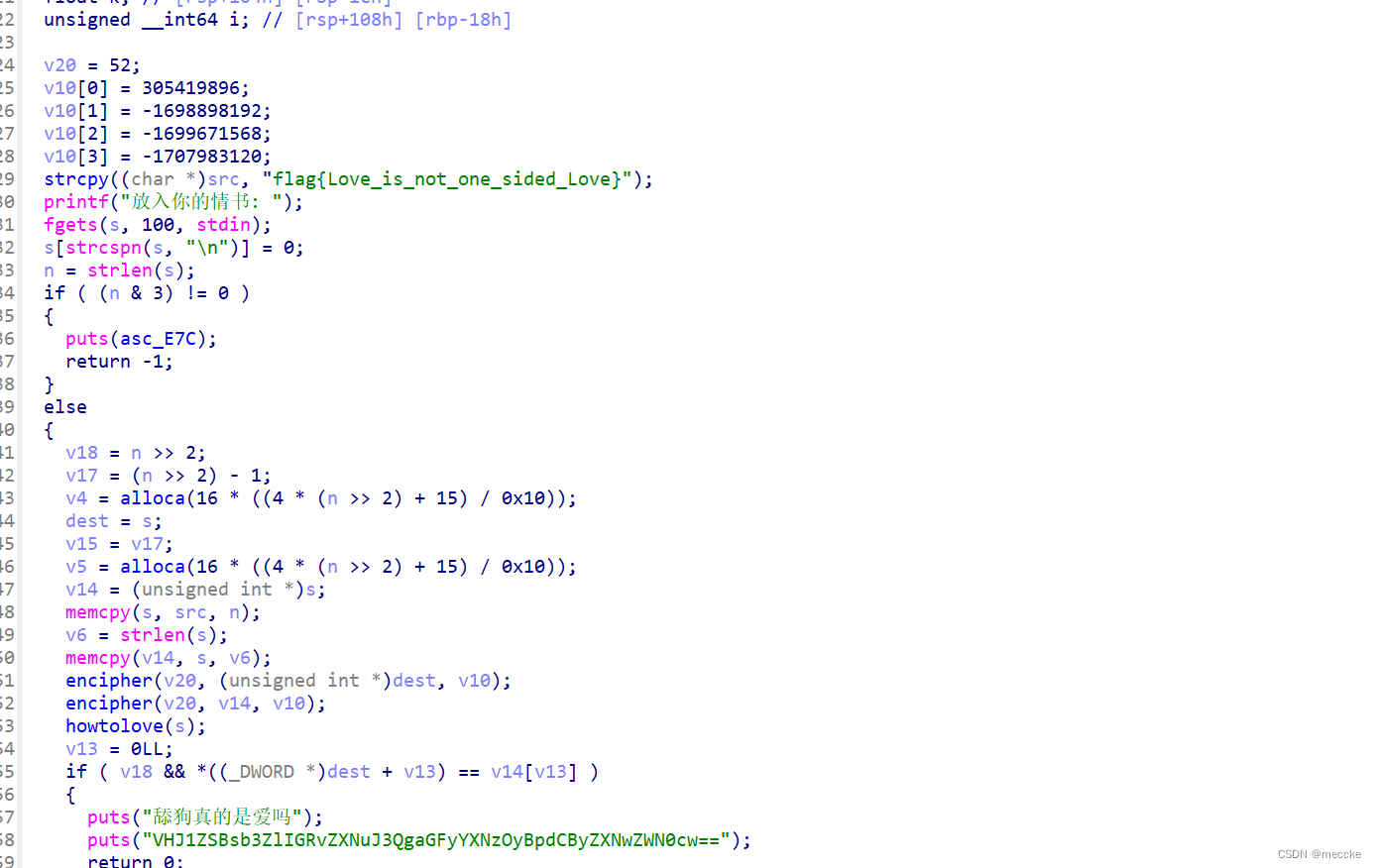
干扰信息挺多的
base64解密后是“爱是尊重不是打扰”和flag无关
重点在howtolove函数,脚本太长了直接复制了
from z3 import *
from z3.z3 import BitVec, Solver, sat
s = Solver()
temp = [BitVec(f'flag{i}', 8) for i in range(32)]
moyu_z3_vars = temp[:]
for i in range(32):
s.add(temp[i] >= 0x20, temp[i] <= 0x7e)
v2 = [0] * 0x1C20
v2[32] = 2;v2[65] = 2;
v2[66] = 4;
v2[98] = 2;
v2[99] = 5;
v2[185] = 2;
v2[186] = 2;
v2[187] = 1;
v2[188] = 1;
v2[189] = 1;
v2[190] = 1;
v2[191] = 1;
v2[192] = 1;
v2[193] = 1;
v2[194] = 1;
v2[195] = 1;
v2[196] = 1;
v2[197] = 1;
v2[198] = 1;
v2[199] = 1;
v2[200] = 1;
v2[201] = 1;
v2[202] = 1;
v2[203] = 1;
v2[204] = 1;
v2[205] = 1;
v2[206] = 1;
v2[207] = 1;
v2[208] = 1;
v2[209] = 1;
v2[210] = 1;
v2[211] = 1;
v2[212] = 1;
v2[213] = 1;
v2[214] = 1;
v2[215] = 1;
v2[216] = 1;
v2[217] = 1;
v2[218] = 1;
v2[219] = 1;
v2[220] = 1;
v2[221] = 1;
v2[222] = 1;
v2[223] = 1;
v2[224] = 1;
v2[225] = 1;
v2[226] = 1;
v2[227] = 1;
v2[228] = 1;
v2[229] = 2;
v2[232] = 2;
v2[256] = 2;
v2[257] = 5;
v2[303] = 1;
v2[304] = 1;
v2[305] = 1;
v2[306] = 1;
v2[307] = 2;
v2[308] = 5;
v2[328] = 1;
v2[329] = 1;
v2[330] = 1;
v2[331] = 1;
v2[332] = 1;
v2[333] = 1;
v2[334] = 1;
v2[335] = 1;
v2[336] = 1;
v2[337] = 1;
v2[338] = 1;
v2[339] = 1;
v2[340] = 1;
v2[341] = 1;
v2[342] = 2;
v2[353] = 2;
v2[354] = 5;
v2[430] = 2;
v2[431] = 2;
v2[432] = 5;
v2[523] = 2;
v2[524] = 5;
v2[564] = 2;
v2[565] = 5;
v2[627] = 2;
v2[628] = 1;
v2[629] = 1;
v2[630] = 1;
v2[631] = 1;
v2[632] = 1;
v2[633] = 1;
v2[634] = 1;
v2[635] = 1;
v2[636] = 1;
v2[637] = 1;
v2[638] = 1;
v2[639] = 1;
v2[640] = 1;
v2[641] = 1;
v2[642] = 1;
v2[643] = 1;
v2[644] = 1;
v2[645] = 1;
v2[646] = 1;
v2[647] = 2;
v2[648] = 4;
v2[649] = 1;
v2[650] = 1;
v2[651] = 1;
v2[652] = 1;
v2[653] = 2;
v2[680] = 2;
v2[687] = 2;
v2[688] = 4;
v2[698] = 2;
v2[766] = 2;
v2[767] = 5;
v2[818] = 2;
v2[819] = 1;
v2[820] = 2;
v2[827] = 2;
v2[828] = 5;
v2[846] = 2;
v2[847] = 5;
v2[890] = 2;
v2[891] = 1;
v2[892] = 1;
v2[893] = 1;
v2[894] = 1;
v2[895] = 1;
v2[896] = 1;
v2[897] = 1;
v2[898] = 1;
v2[899] = 1;
v2[900] = 1;
v2[901] = 1;
v2[902] = 1;
v2[903] = 1;
v2[904] = 1;
v2[905] = 1;
v2[906] = 1;
v2[907] = 1;
v2[908] = 1;
v2[909] = 1;
v2[910] = 1;
v2[911] = 1;
v2[912] = 1;
v2[913] = 1;
v2[914] = 1;
v2[915] = 1;
v2[916] = 1;
v2[917] = 1;
v2[918] = 1;
v2[919] = 1;
v2[920] = 1;
v2[921] = 1;
v2[922] = 1;
v2[923] = 1;
v2[924] = 1;
v2[925] = 1;
v2[926] = 1;
v2[927] = 1;
v2[928] = 1;
v2[929] = 1;
v2[930] = 1;
v2[931] = 1;
v2[932] = 1;
v2[933] = 2;
v2[934] = 5;
v2[989] = 2;
v2[994] = 2;
v2[995] = 1;
v2[996] = 1;
v2[997] = 1;
v2[998] = 1;
v2[999] = 1;
v2[1000] = 1;
v2[1001] = 1;
v2[1002] = 1;
v2[1003] = 1;
v2[1013] = 1;
v2[1014] = 1;
v2[1015] = 1;
v2[1016] = 1;
v2[1017] = 1;
v2[1018] = 1;
v2[1019] = 1;
v2[1020] = 1;
v2[1021] = 1;
v2[1022] = 1;
v2[1023] = 1;
v2[1024] = 1;
v2[1025] = 1;
v2[1026] = 1;
v2[1027] = 2;
v2[1028] = 3;
v4 = 0;
v3 = 0;
while ( 1 ):
while ( 1 ):
while ( 1 ):
while ( not v2[v3] ):
v3 += 1
temp[v4] += 1
if ( v2[v3] != 1 ):
break;
v3 += 1
temp[v4] -= 1
if ( v2[v3] != 2 ):
break;
v3 += 1
v4 += 1
if ( v2[v3] == 3 ):
break;
if ( v2[v3] == 4 ):
temp[v4] = temp[v4] + temp[v4 + 1] - 70;
v3 += 1
elif ( v2[v3] == 5 ):
temp[v4] = temp[v4] - temp[v4 + 1] + 70;
v3 += 1
for i in range(32):
s.add(temp[i] == ord('flag{Love_is_not_one_sided_Love}'[i]))
if s.check() == sat:
model = s.model()
print(''.join([chr(model[moyu_z3_vars[i]].as_long()) for i in range(32)]))
舔狗四部曲 -- 记忆的时光机
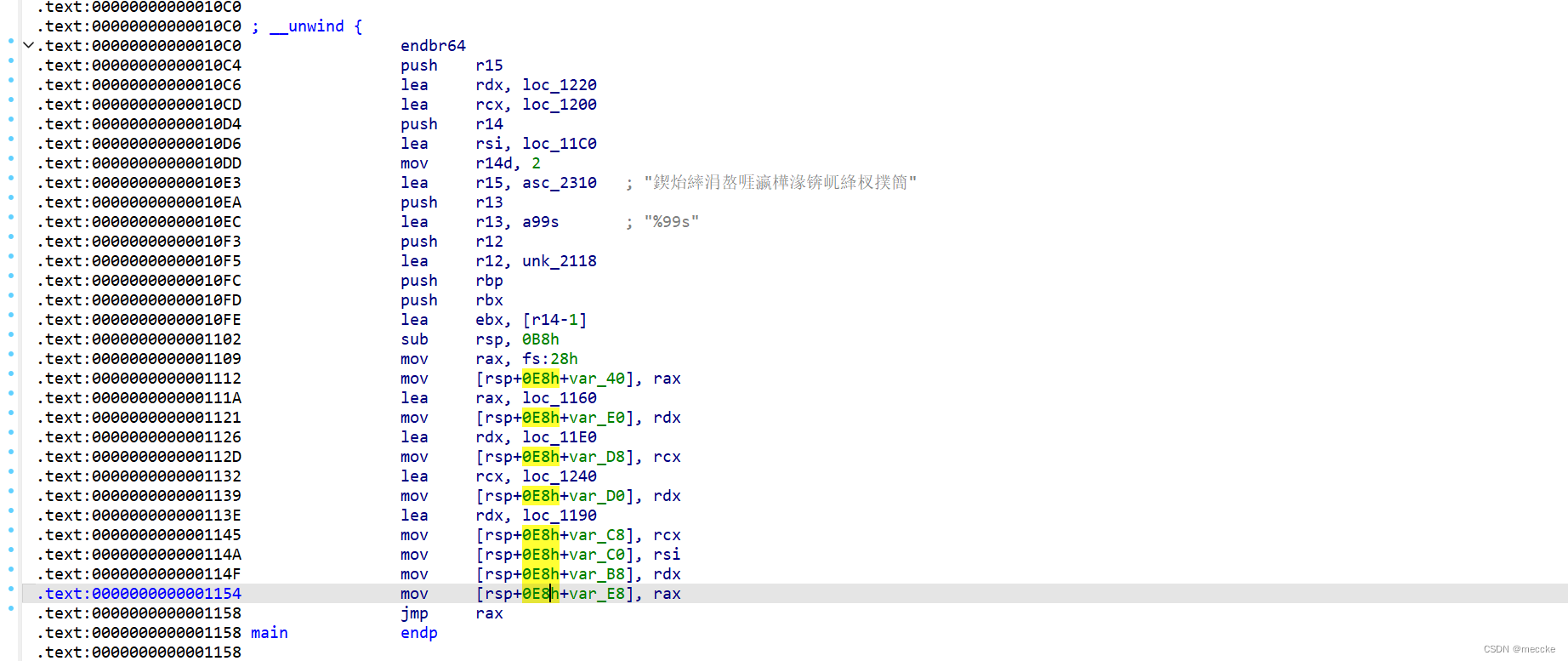
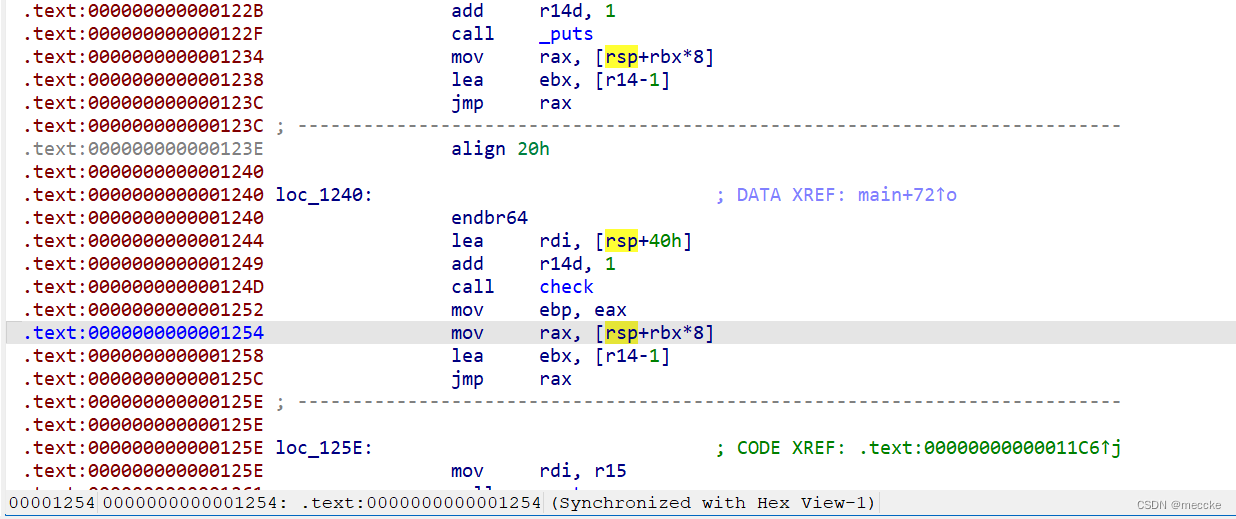
可以看到是通过函数地址的方式来跳转调用,所以导致ida不能正常识别。
一点点找吧,
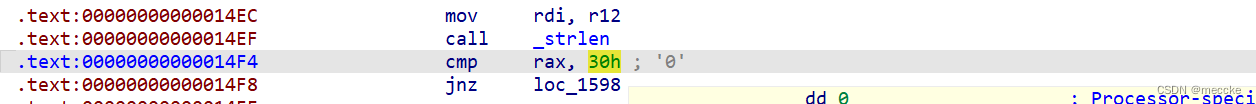
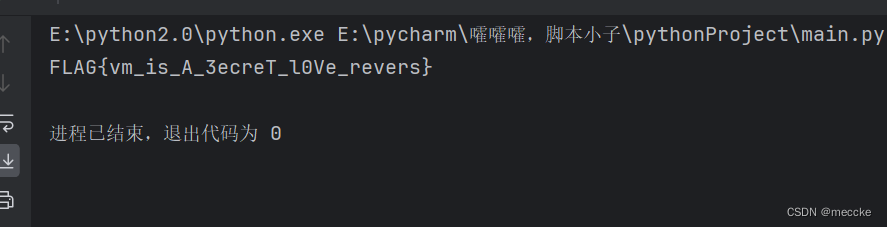
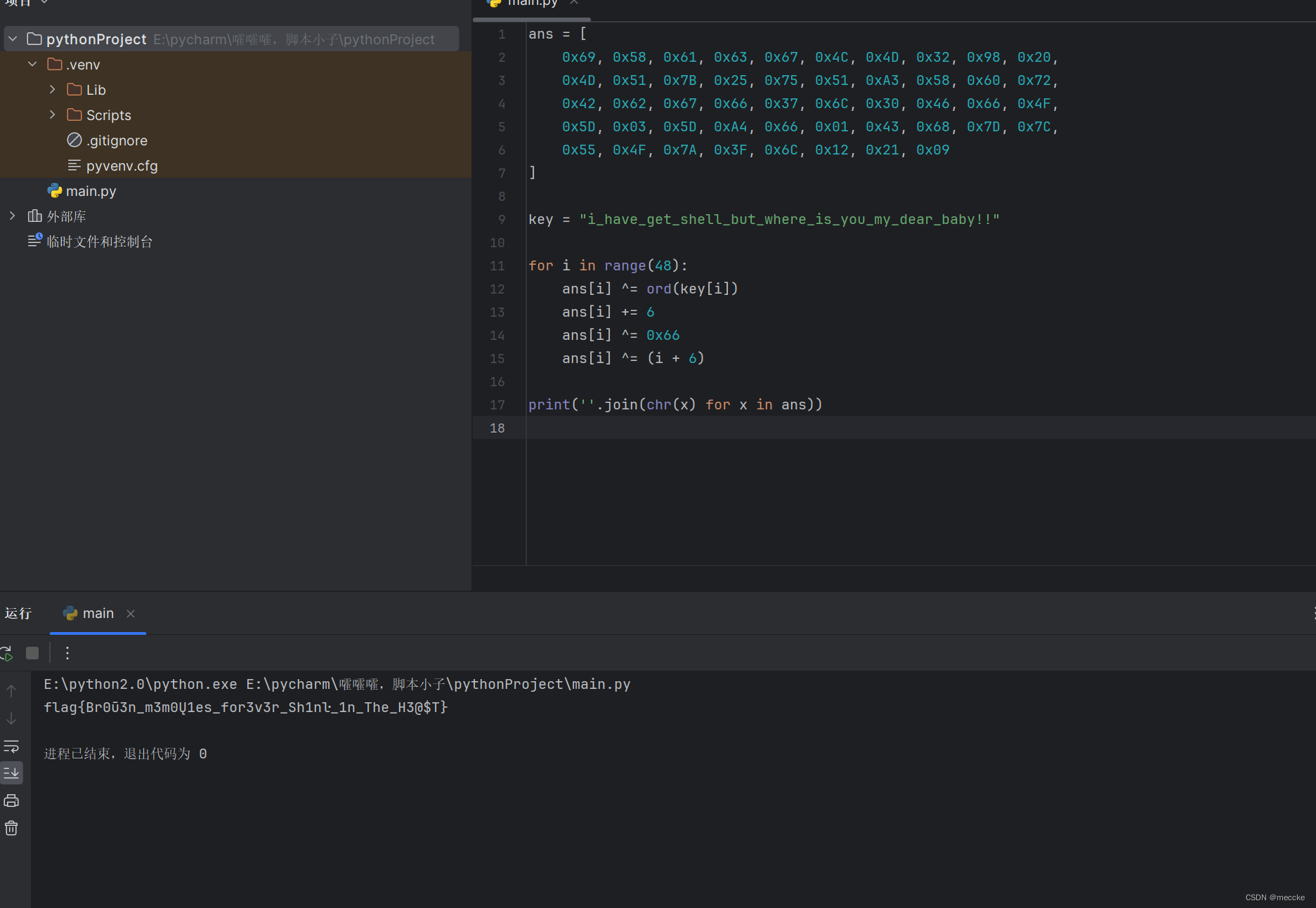
十六进制30等于48,flag长度是48
下一条跳转函数,
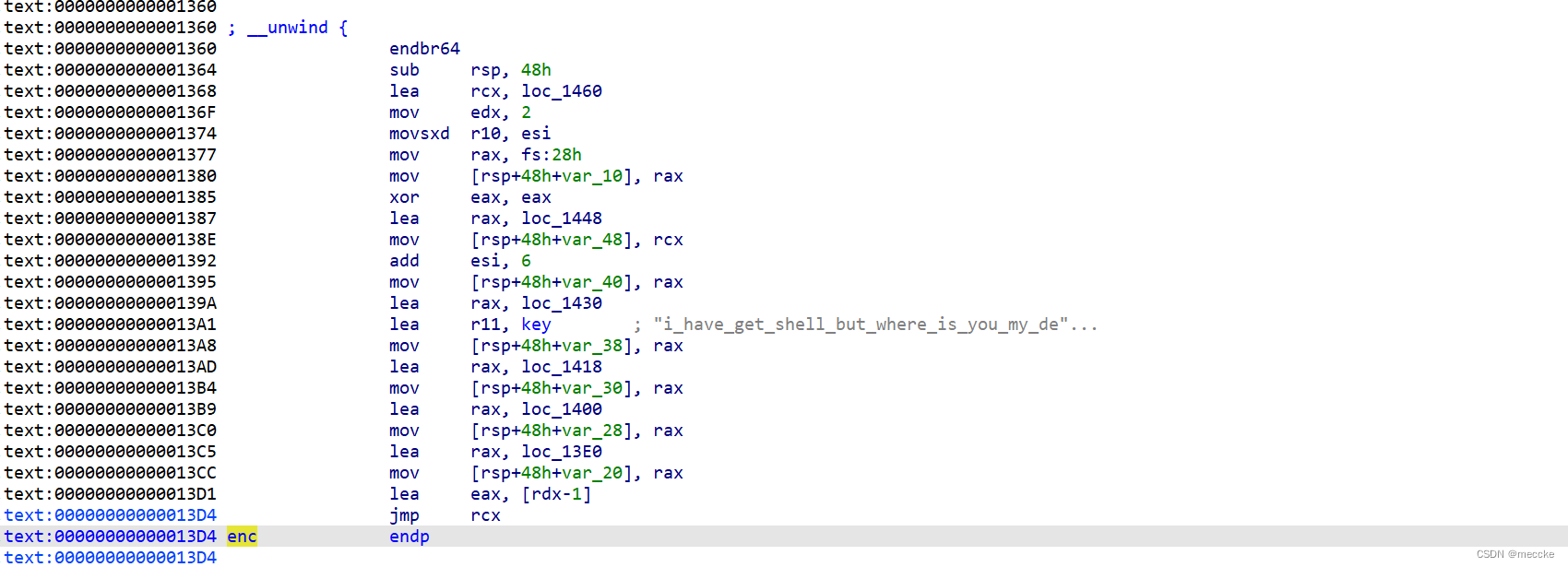
找到enc函数
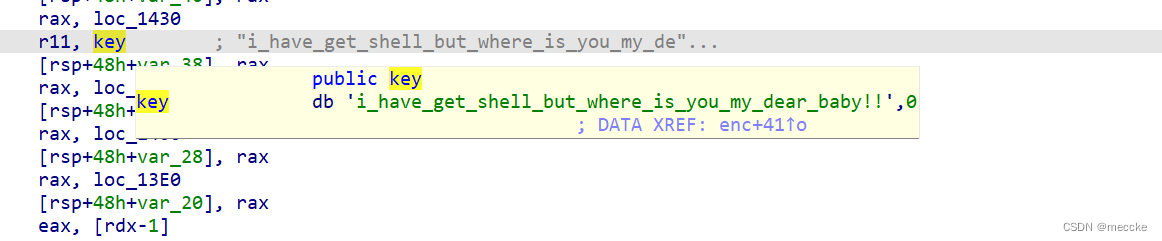
key已知
这个flag总感觉怪怪的





















 7348
7348











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








