python使用3.8版本
系统:Windows 10 x64或者win7 x64
C:\Python38\Lib\site-packages\scapy\VERSION
2.5.0
scapy-2.5.0.tar.gz
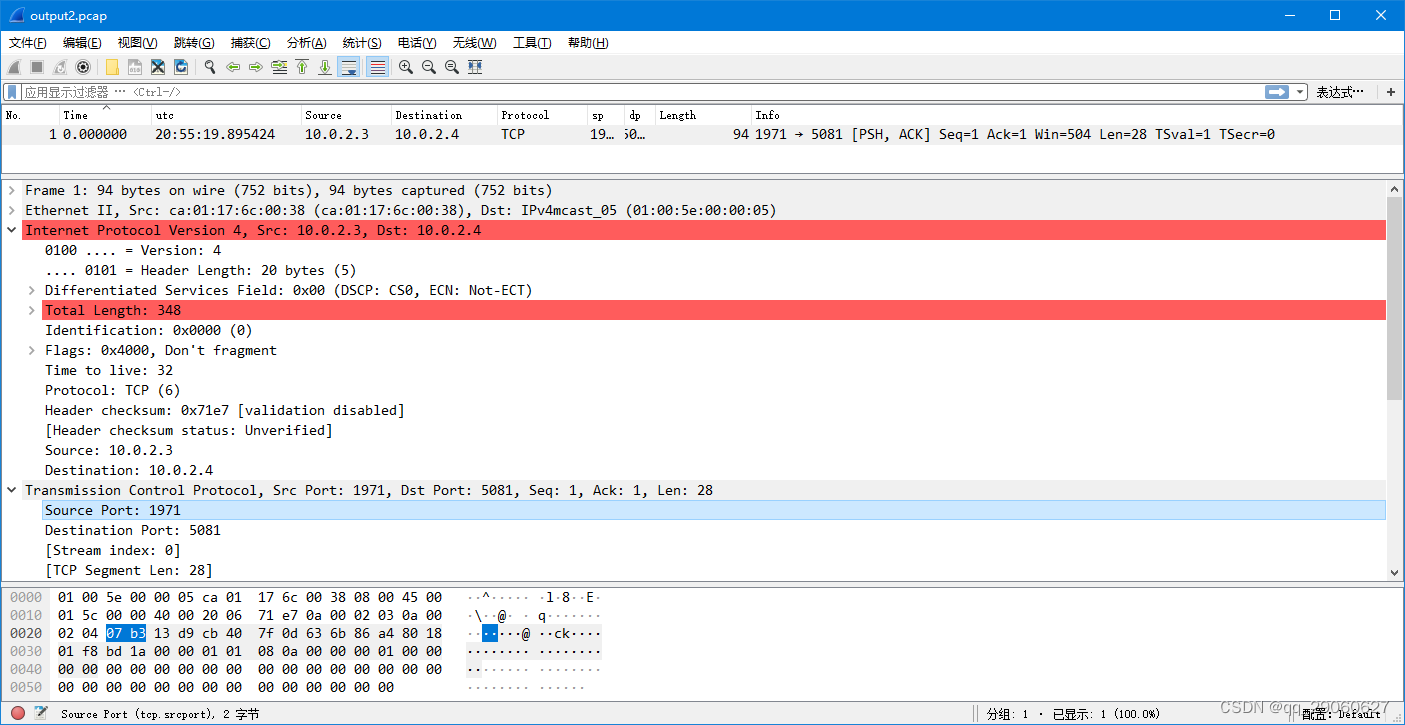
C:\Python38\python -m pip install scrpy 首先实现二层的payload替换:
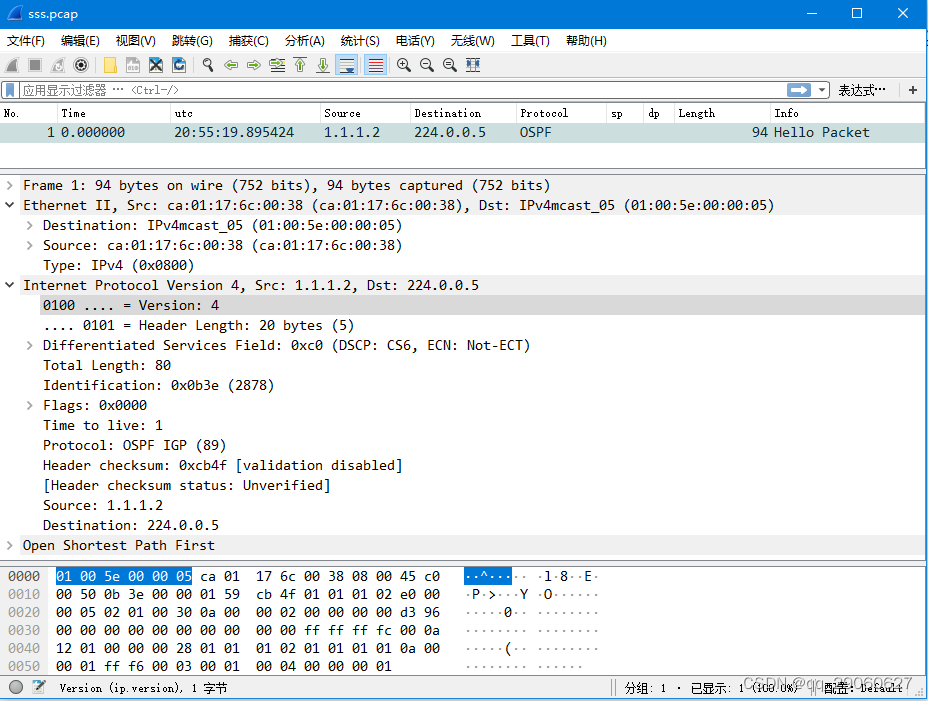
原始pcap文件,如下:
import scapy
from scapy.packet import *
from scapy.layers import *
from scapy.layers.l2 import Ether
from scapy.layers.inet import IP, TCP,UDP
from scapy.contrib.ospf import OSPF_Hdr, OSPF_Hello
from scapy.utils import rdpcap, wrpcap
import time, sys, binascii
aa2 = binascii.a2b_hex("4500015C00004000200671E70A0002030A00020407B313D9CB407F0D636B86A4801801F8BD1A00000101080A00000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001100000001000000040000004D595650020000000300000000000000000000000000000000000000")
#45 == ( 4: ipv4 ,5: ip header length 20 bytes )
wp=Ether(dst='ff:ff:ff:ff:ff:ff',src="A8:64:F1:44:66:88", type=0x0800)/Raw(aa2)
#scapy.layers.l2.hexdump(wp);
packets = rdpcap('z:/sss.pcap') #read_pcap
for pkt in packets:
print(pkt.command());
scapy.layers.l2.hexdump(pkt) ;
pkt[Ether].payload = wp.payload;
wrpcap('z:/output2.pcap', packets) #write_pcap
再替换tcp协议的payload:
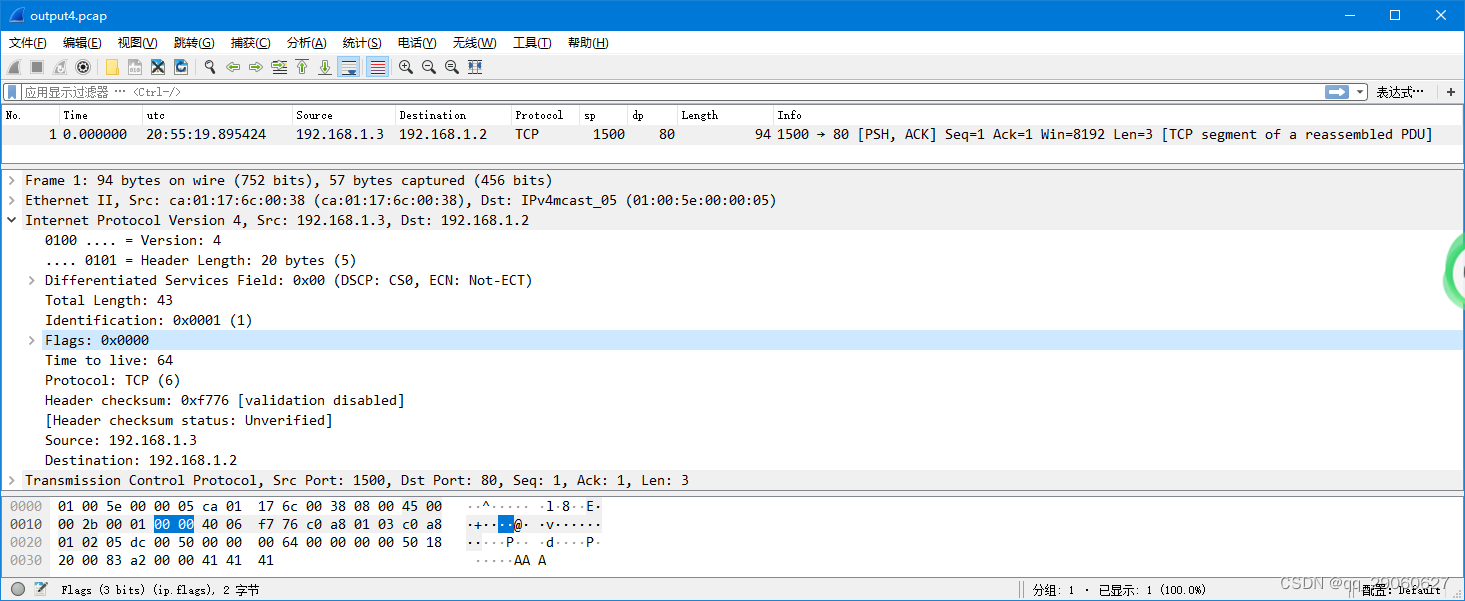
pcap文件(output4.pcap),如下:
import scapy
from scapy.packet import *
from scapy.layers import *
from scapy.layers.l2 import Ether
from scapy.layers.inet import IP, TCP, UDP
from scapy.contrib.ospf import OSPF_Hdr, OSPF_Hello
from scapy.utils import rdpcap, wrpcap
import time, sys, binascii
aa2 = binascii.a2b_hex("414141")
packets = rdpcap('z:/sss.pcap')
eth2=Ether( dst='ff:ff:ff:ff:ff:ff', src="A8:64:F1:44:66:88", type=0x0800 )
ip2=IP(dst = "192.168.1.2",src ="192.168.1.3",proto = 6)
tcp2=TCP(sport=1500, dport=80, flags="PA", seq=100)
wp=eth2/ip2/tcp2/Raw(aa2)
#scapy.layers.l2.hexdump(wp);
for pkt in packets:
print(pkt.command());
scapy.layers.l2.hexdump(pkt);
pkt[Ether].payload =wp.payload
wrpcap('z:/output4.pcap',packets)
packets44 = rdpcap('z:/output4.pcap')
for pkt2 in packets44:
aa44=binascii.a2b_hex("444444")
wp44=TCP(sport=1514,dport=88)/Raw(aa44)
scapy.layers.l2.hexdump(wp44);
pkt2[TCP].payload =wp44.payload
wrpcap('z:/output8.pcap',packets44)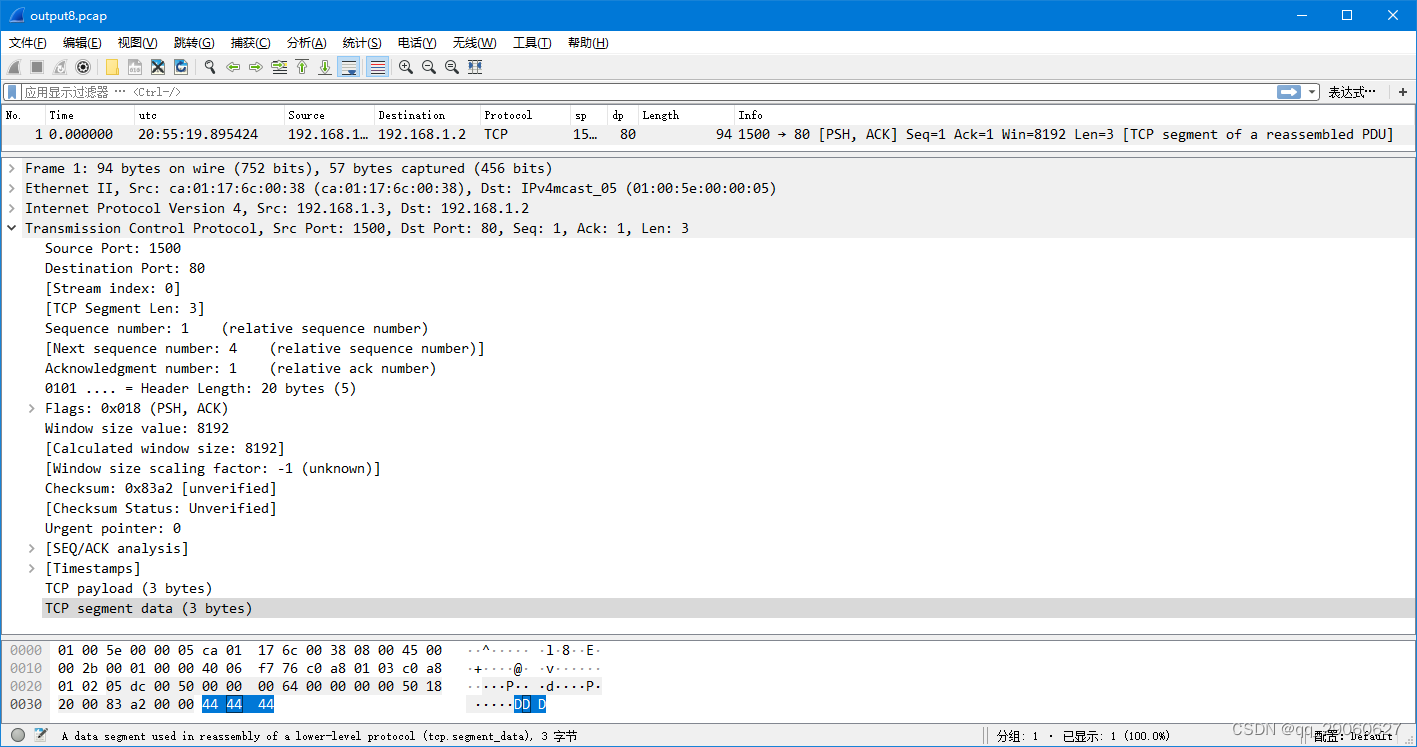






















 505
505











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








