1.在企业级的证书管理中,会有crl证书吊销文件管理的需求
2.本文介绍如何给openldap中导入crl
1.安装openldap
1.1 ubuntu上安装openldap方法如下:
sudo apt-get install slapd ldap-utils
期间会让设置管理员账号两次,记住这个密码
打开'/etc/ldap/ldap.conf'文件按照以下内容配置修改:
BASE dc=ldap,dc=com
URI ldap://192.168.11.11
base dn和URI按需填写即可
如果已经安装了,可以通过以下命令进行配置:
sudo dpkg-reconfigure slapd
否:选择“NO”后按Enter继续
ldap.com:输入DNS domain 名称。例如ldap.com
aaa:输入组织名称,例如aaa
admin:输入LDAP管理员的密码,例如admin
admin:再次确认输入LDAP管理员密码,例如admin
1.2 测试LDAP服务
输入"ldapsearch -x",会看到类似以下输出:
root@array-virtual-machine:/etc/ldap# ldapsearch -x
# extended LDIF
#
# LDAPv3
# base <dc=ldap,dc=com> (default) with scope subtree
# filter: (objectclass=*)
# requesting: ALL
#
# ldap.com
dn: dc=ldap,dc=com
objectClass: top
objectClass: dcObject
objectClass: organization
o: array
dc: ldap
# admin, ldap.com
dn: cn=admin,dc=ldap,dc=com
objectClass: simpleSecurityObject
objectClass: organizationalRole
cn: admin
description: LDAP administrator
# search result
search: 2
result: 0 Success
# numResponses: 3
# numEntries: 2
root@array-virtual-machine:/etc/ldap#
2.导入crl
2.1 首先准备一个crl.ldif文件,内容如下:
dn: cn=crl1,dc=ldap,dc=com
objectClass: cRLDistributionPoint(这个class类必须要加)
cn: crl1
certificateRevocationList;binary::填写要导入的crl文件的base64编码
#关于ldap中每个类的作用,这里不做展开介绍
2.2 执行以下命令导入:
ldapadd -x -D cn=admin,dc=ldap,dc=com -h x.x.x.x -w xxx -f crl.ldif
-h和-w后面的参数是ip和密码,对应上文设置的URI和admin
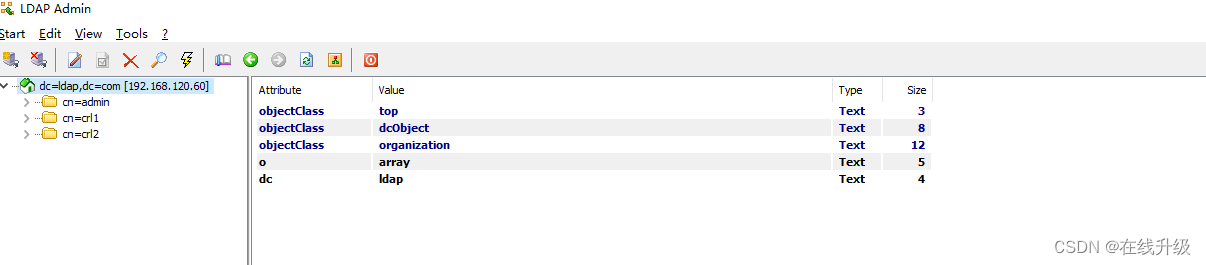
2.3 导入后查看:
root@array-virtual-machine:/etc/ldap# ldapadd -x -D cn=admin,dc=ldap,dc=com -h 192.168.120.60 -w click1 -f crl.ldif
adding new entry "cn=crl1,dc=ldap,dc=com"
root@array-virtual-machine:/etc/ldap# vi crl.ldif
root@array-virtual-machine:/etc/ldap# ldapadd -x -D cn=admin,dc=ldap,dc=com -h 192.168.120.60 -w click1 -f crl.ldif
adding new entry "cn=crl2,dc=ldap,dc=com"
root@array-virtual-machine:/etc/ldap# ldapsearch -x
# extended LDIF
#
# LDAPv3
# base <dc=ldap,dc=com> (default) with scope subtree
# filter: (objectclass=*)
# requesting: ALL
#
# ldap.com
dn: dc=ldap,dc=com
objectClass: top
objectClass: dcObject
objectClass: organization
o: array
dc: ldap
# admin, ldap.com
dn: cn=admin,dc=ldap,dc=com
objectClass: simpleSecurityObject
objectClass: organizationalRole
cn: admin
description: LDAP administrator
# crl1, ldap.com
dn: cn=crl1,dc=ldap,dc=com
objectClass: cRLDistributionPoint
cn: crl1
certificateRevocationList;binary:: MIIB2DCBwQIBATANBgkqhkiG9w0BAQsFADBVMQswCQY
DVQQGEwJXUTELMAkGA1UECAwCV1ExCzAJBgNVBAoMAldRMQswCQYDVQQLDAJXUTELMAkGA1UEAwwC
V1ExEjAQBgkqhkiG9w0BCQEWAzEyVxcNMjIwNDA3MDI0OTIxWhcNMjIwNTA3MDI0OTIxWjAoMBICA
QIXDTIyMDQwMjAxMjUwNFowEgIBAxcNMjIwNDA3MDI0ODUwWqAOMAwwCgYDVR0UBAMCAQIwDQYJKo
ZIhvcNAQELBQADggEBADzWEjs7tFLE2Tz9PHQ86wYc4PJEjTXRnWXMtykN94Yjfa+fpgiPxZoYmuq
avfGbtZdeClQkiZrMyXUaQYq6lGomD9STqf1l7ODBc7Xa/qxwxpzSe4aM2NUXrS9r7sfifYGgeWUw
PhLkEHS1loftZjUlmfVLTPRGXAcsP9o6nlxmCX/Kxyjzr79aWc4ENKaMahQG6RZfyxfRUpBs1u+UT
GS2cdwrgG+Bfc5WdRbQBASttTfPYCDsBI3Kvvd5iciHOY760JmSGFUm7KjFV3QqFlM2q+zZerqW8O
2Rp6D2IfhcyeTGqVbM9eGelHMPrZPw2TjS2AY+0cZ8YL+pJJdtKE8=
# crl2, ldap.com
dn: cn=crl2,dc=ldap,dc=com
objectClass: cRLDistributionPoint
cn: crl2
certificateRevocationList;binary:: MIIB2DCBwQIBATANBgkqhkiG9w0BAQsFADBVMQswCQY
DVQQGEwJXUTELMAkGA1UECAwCV1ExCzAJBgNVBAoMAldRMQswCQYDVQQLDAJXUTELMAkGA1UEAwwC
V1ExEjAQBgkqhkiG9w0BCQEWAzEyVxcNMjIwNDA3MDI0OTIxWhcNMjIwNTA3MDI0OTIxWjAoMBICA
QIXDTIyMDQwMjAxMjUwNFowEgIBAxcNMjIwNDA3MDI0ODUwWqAOMAwwCgYDVR0UBAMCAQIwDQYJKo
ZIhvcNAQELBQADggEBADzWEjs7tFLE2Tz9PHQ86wYc4PJEjTXRnWXMtykN94Yjfa+fpgiPxZoYmuq
avfGbtZdeClQkiZrMyXUaQYq6lGomD9STqf1l7ODBc7Xa/qxwxpzSe4aM2NUXrS9r7sfifYGgeWUw
PhLkEHS1loftZjUlmfVLTPRGXAcsP9o6nlxmCX/Kxyjzr79aWc4ENKaMahQG6RZfyxfRUpBs1u+UT
GS2cdwrgG+Bfc5WdRbQBASttTfPYCDsBI3Kvvd5iciHOY760JmSGFUm7KjFV3QqFlM2q+zZerqW8O
2Rp6D2IfhcyeTGqVbM9eGelHMPrZPw2TjS2AY+0cZ8YL+pJJdtKE8=
# search result
search: 2
result: 0 Success
# numResponses: 5
# numEntries: 4
root@array-virtual-machine:/etc/ldap#
ldap可视化工具分享
这里介绍一个工具:LdapAdmin.exe
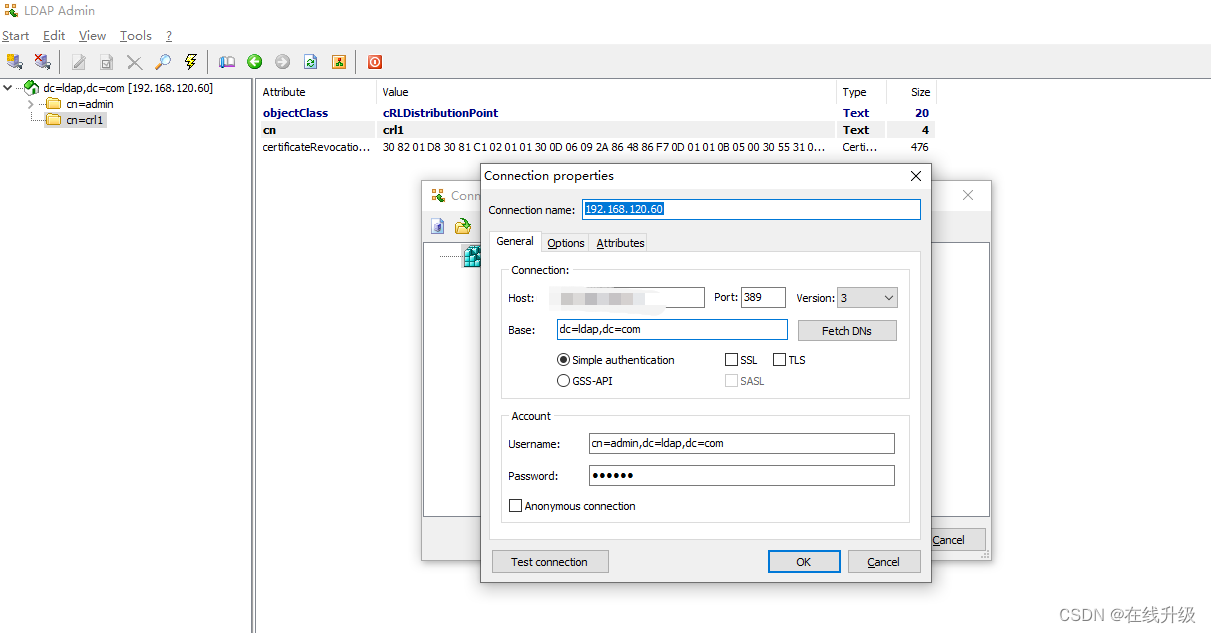
工具连接界面:host填写自己的URI,然后填写base以及管理员账户等信息,也可以选择匿名登陆,匿名连接只能查询:
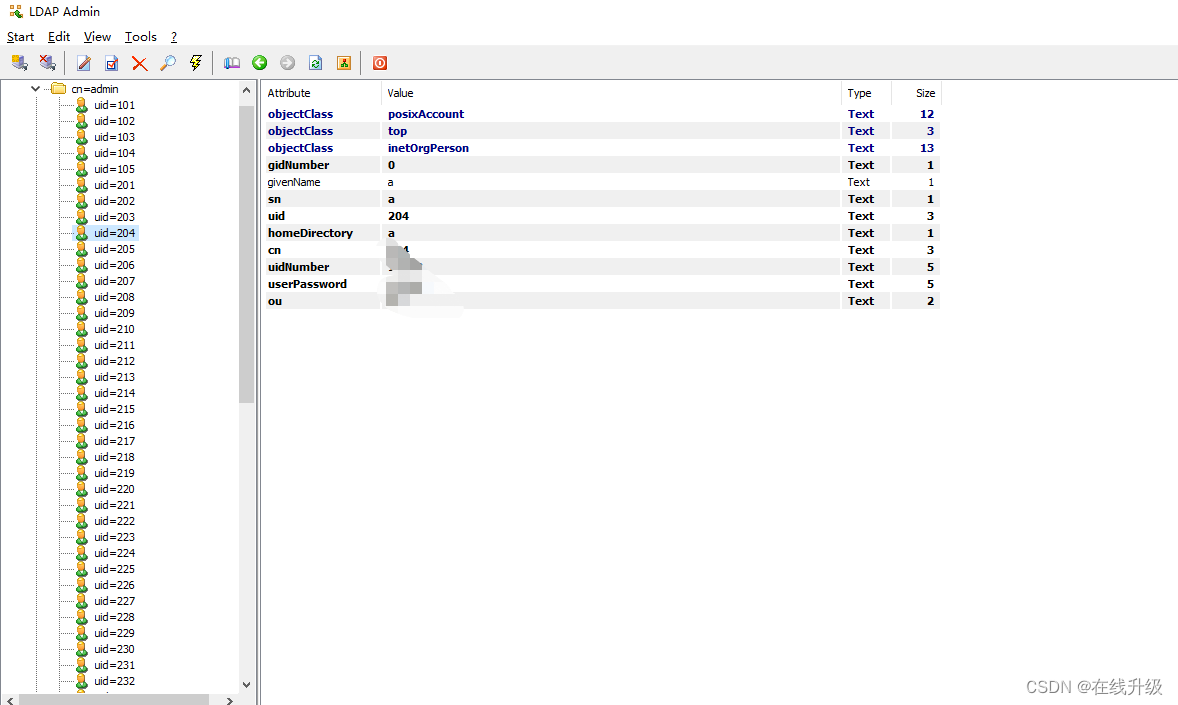
也可以添加、删除用户、修改用户密码:





















 6723
6723











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








