1.说明
此处只做spring security 实现不同角色访问不同地址的简单示例代码,只为说明spring security的简单使用方法
基本的登录可查看---spring security入门--实现用户名密码登录简单示例一
地址:https://blog.csdn.net/qq_32224047/article/details/107921387
2.代码示例
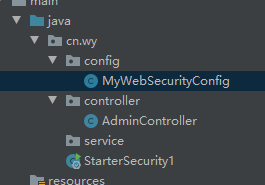
项目结构
AdminController 中的代码,做访问跳转测试用
import org.springframework.web.bind.annotation.RequestMapping;
import org.springframework.web.bind.annotation.RestController;
@RestController
public class AdminController {
@RequestMapping("/admin/write")
public String write() {
return "写入数据";
}
@RequestMapping("/admin/update")
public String update() {
return "更新数据";
}
@RequestMapping("/admin/delete")
public String delete() {
return "删除数据";
}
@RequestMapping("/user/read")
public String read() {
return "读取数据,不需要权限";
}
@RequestMapping("/ther")
public String other() {
return "其他权限";
}
}
Security配置类MyWebSecurityConfig 中的代码,第一次覆盖configure方法设置了用户密码、ROLE_guest,只赋予了user读read权限等,在第二次覆盖configure方法中,开启权限控制,通过ANT规范,自定义逻辑
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import org.springframework.security.config.annotation.authentication.builders.AuthenticationManagerBuilder;
import org.springframework.security.config.annotation.web.builders.HttpSecurity;
import org.springframework.security.config.annotation.web.configuration.EnableWebSecurity;
import org.springframework.security.config.annotation.web.configuration.WebSecurityConfigurerAdapter;
import org.springframework.security.config.annotation.web.configurers.ExpressionUrlAuthorizationConfigurer;
import org.springframework.security.core.userdetails.UserDetailsService;
import org.springframework.security.crypto.bcrypt.BCryptPasswordEncoder;
import org.springframework.security.crypto.password.NoOpPasswordEncoder;
import org.springframework.security.crypto.password.PasswordEncoder;
@Configuration
@EnableWebSecurity
public class MyWebSecurityConfig
extends WebSecurityConfigurerAdapter {
//明文加密器,只需要在内存中有这个管理对象,如果不添加,从前端登录时会抛出异常
@Bean
public PasswordEncoder passwordEncoder(){
return NoOpPasswordEncoder.getInstance();
}
@Override
protected void configure(AuthenticationManagerBuilder auth) throws Exception {
// auth.userDetailsService(myUserDetailsService());
//auth可以决定user对象的来源,可以是内存,也可以是
//自定义从数据库读取的数据
auth.inMemoryAuthentication()
.withUser("user")
.password("123456")
//.roles("guest")//底层ROLE_guest权限
.authorities("read");
//roles 和authorities本质底层都是设置的权限
//在内存用户定义时,同时存在,下面的方法值会覆盖上面的
auth.inMemoryAuthentication()
.withUser("admin")
.password("123456")
//.roles("administrator","guest")
.authorities("read","write","delete","update");
}
@Override
protected void configure(HttpSecurity http) throws Exception {
http.authorizeRequests()// 开启权限控制,通过ANT规范,自定义逻辑
//.antMatchers("/admin/**").hasRole("administrator")
//.antMatchers("/user/**").hasRole("guest")
//当访问/admin/write时必须有write权限
.antMatchers("/admin/write").hasAuthority("write")
.antMatchers("/admin/update").hasAuthority("update")
.antMatchers("/admin/delete").hasAuthority("delete")
.antMatchers("/user/read").hasAuthority("read")
.anyRequest()//任意请求
.authenticated();//必须经过认证 只要登陆就能访问
http.formLogin();//开启表单认证
http.httpBasic();//开启http 基本认证
}
}
运行程序
登录user 访问write,因为没有权限所以禁止访问

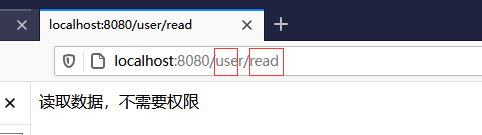
user 正常访问read
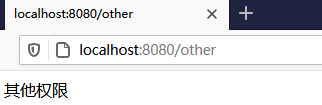
user访问其他权限
更换admin访问,都具有访问权限

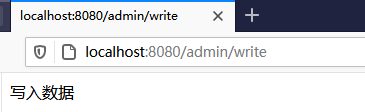
注意可以用admin用户登录直接访问 http://localhost:8080/user/read

























 1039
1039











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








