
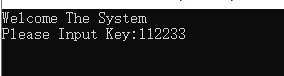



strlen(Buffer) <= 37, sub_401090第二个参数伪代码没有体现出来, 直接看汇编
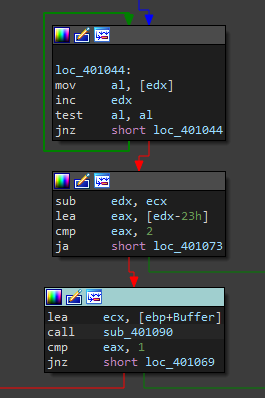
edx是第二个参数a2, 通过main函数的汇编得知edx保存strlen(&Buffer)
所以可以判断strlen(&Buffer) == 35, 然后就是通过sub_401090的检测.

数据处理

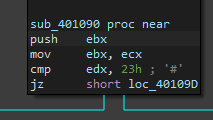
逆向sub_401090函数, 不是对称的加密, 所以采用爆破找到flag
byte_402150 = '2a49f69c38395cde96d6de96d6f4e025484954d6195448def6e2dad67786e21d5adae6'
byte_402151 = 'a49f69c38395cde96d6de96d6f4e025484954d6195448def6e2dad67786e21d5adae6'
data = [
0x63, 0x7C, 0x77, 0x7B, 0x0F2, 0x6B, 0x6F, 0x0C5, 0x30, 0x1, 0x67, 0x2B, 0x0FE,
0x0D7, 0x0AB, 0x76, 0x0CA, 0x82, 0x0C9, 0x7D, 0x0FA, 0x59, 0x47, 0x0F0, 0x0AD, 0x0D4,
0x0A2, 0x0AF, 0x9C, 0x0A4, 0x72, 0x0C0, 0x0B7, 0x0FD, 0x93, 0x26, 0x36, 0x3F, 0x0F7, 0x0CC,
0x34, 0x0A5, 0x0E5, 0x0F1, 0x71, 0x0D8, 0x31, 0x15, 0x4, 0x0C7, 0x23, 0x0C3, 0x18, 0x96, 0x5,
0x9A, 0x7, 0x12, 0x80, 0x0E2, 0x0EB, 0x27, 0x0B2, 0x75, 0x9, 0x83, 0x2C, 0x1A, 0x1B, 0x6E, 0x5A,
0x0A0, 0x52, 0x3B, 0x0D6, 0x0B3, 0x29, 0x0E3, 0x2F, 0x84, 0x53, 0x0D1, 0x0, 0x0ED, 0x20, 0x0FC,
0x0B1, 0x5B, 0x6A, 0x0CB, 0x0BE, 0x39, 0x4A, 0x4C, 0x58, 0x0CF, 0x0D0, 0x0EF, 0x0AA, 0x0FB, 0x43,
0x4D, 0x33, 0x85, 0x45, 0x0F9, 0x2, 0x7F, 0x50, 0x3C, 0x9F, 0x0A8, 0x51, 0x0A3, 0x40, 0x8F, 0x92,
0x9D, 0x38, 0x0F5, 0x0BC, 0x0B6, 0x0DA, 0x21, 0x10, 0x0FF, 0x0F3, 0x0D2, 0x0CD, 0x0C, 0x13, 0x0EC,
0x5F, 0x97, 0x44, 0x17, 0x0C4, 0x0A7, 0x7E, 0x3D, 0x64, 0x5D, 0x19, 0x73, 0x60, 0x81, 0x4F, 0x0DC,
0x22, 0x2A, 0x90, 0x88, 0x46, 0x0EE, 0x0B8, 0x14, 0x0DE, 0x5E, 0x0B, 0x0DB, 0x0E0, 0x32, 0x3A, 0x0A,
0x49, 0x6, 0x24, 0x5C, 0x0C2, 0x0D3, 0x0AC, 0x62, 0x91, 0x95, 0x0E4, 0x79, 0x0E7, 0x0C8, 0x37, 0x6D,
0x8D, 0x0D5, 0x4E, 0x0A9, 0x6C, 0x56, 0x0F4, 0x0EA, 0x65, 0x7A, 0x0AE, 0x8, 0x0BA, 0x78, 0x25, 0x2E,
0x1C, 0x0A6, 0x0B4, 0x0C6, 0x0E8, 0x0DD, 0x74, 0x1F, 0x4B, 0x0BD, 0x8B, 0x8A, 0x70, 0x3E, 0x0B5, 0x66,
0x48, 0x3, 0x0F6, 0x0E, 0x61, 0x35, 0x57, 0x0B9, 0x86, 0x0C1, 0x1D, 0x9E, 0x0E1, 0x0F8, 0x98, 0x11,
0x69, 0x0D9, 0x8E, 0x94, 0x9B, 0x1E, 0x87, 0x0E9, 0x0CE, 0x55, 0x28, 0x0DF, 0x8C, 0x0A1, 0x89, 0x0D,
0x0BF, 0x0E6, 0x42, 0x68, 0x41, 0x99, 0x2D, 0x0F, 0x0B0, 0x54, 0x0BB, 0x16
]
def brute():
flag = ""
for i in range(35):
v8 = ord(byte_402150[2 * i])
if v8 < 48 or v8 > 57: v9 = v8 - 87
else: v9 = v8 - 48
v10 = ord(byte_402151[2 * i])
v11 = 16 * v9
if v10 < 48 or v10 > 57: v12 = v10 - 87
else: v12 = v10 - 48
for j in range(16, 127):
v6 = (j >> 4) % 16 # 2 ^ 4 = 16
v7 = ((16 * j) >> 4) % 16
if data[16 * v6 + v7] == ((v11 + v12) ^ 0x19):
flag += chr(j)
print(flag)
brute()
flag{Th1s_1s_Simple_Rep1ac3_Enc0d3}






















 861
861











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








